Multi-Entity and Multi-Enrollment Key Agreement with Correlated Noise
A basic model for key agreement with a remote (or hidden) source is extended to a multi-user model with joint secrecy and privacy constraints over all entities that do not trust each other after key agreement. Multiple entities using different measur…
Authors: ** 정보가 제공되지 않음 (논문에 저자 명시가 없으므로 확인 필요) **
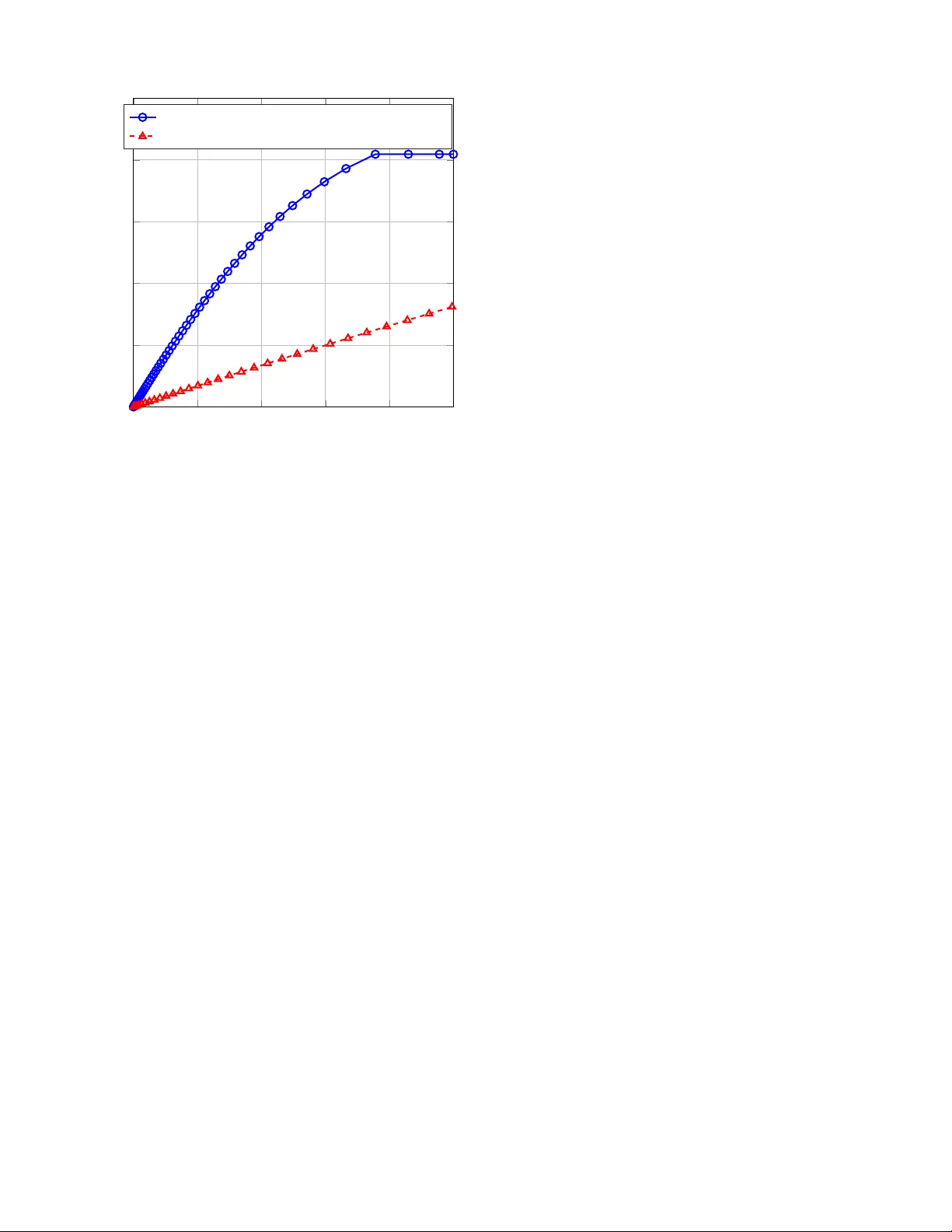
IEEE TRANSA CTIONS ON INFORMA TION FORENSICS AND SECURITY 1 Multi-Entity and Multi-Enrollment K ey Agreement with Correlated Noise Onur G ¨ unl ¨ u, Member , IEEE Abstract —A basic model f or key agr eement with a r emote (or hidden) source is extended to a multi-user model with joint secrecy and privacy constraints over all entities that do not trust each other after key agr eement. Multiple entities using different measurements of the same source through broadcast channels (BCs) to agree on mutually-independent local secret keys ar e consider ed. Our model is the proper multi-user extension of the basic model since the encoder and decoder pairs are not assumed to trust other pairs after key agreement, unlike assumed in the literature. Strong secrecy constraints imposed on all secret keys jointly , which is more stringent than separate secrecy leakage constraints for each secret key considered in the literature, are satisfied. Inner bounds for maximum key rate, and minimum privacy-leakage and database-storage rates are proposed for any finite number of entities. Inner and outer bounds for degraded and less-noisy BCs are given to illustrate cases with strong privacy . A multi-enrollment model that is used for common physical unclonable functions is also considered to establish inner and outer bounds f or key-leakage-storage regions that differ only in the Marko v chains imposed. For this special case, the encoder and decoder measur ement channels have the same channel transition matrix and secrecy leakage is measured for each secret key separately . W e illustrate cases f or which it is useful to have multiple enrollments as compar ed to a single enrollment and vice versa. Index T erms —Information theoretic privacy , multiple enroll- ments, multiple entities, physical unclonable functions. I . I N T R O D U C TI O N A natural source of randomness is biometric identifiers such as fingerprints that are generally transformed into a frequency domain and quantized to obtain bit sequences that are unique to an individual [1]. Similarly , physical identifiers such as fine variations of ring oscillator (RO) outputs or random start- up values of static random access memories (SRAMs) that are caused by uncontrollable manufacturing v ariations, are safer and cheaper alternativ es to ke y storage in a non-volatile memory [2]. Physical identifiers for digital devices such as Internet-of-Things (IoT) devices can be implemented using physical unclonable functions (PUFs) [2]. One can use PUFs in various coding schemes as a source of local randomness [3, Chapter 1], e.g., in the randomized encoder of the wiretap channel [4] and of the strong coordination problem [5], [6]. W e use the basic source model for ke y agreement from [7], [8] to find achiev able rate regions for key agreement Manuscript received April 30, 2020; revised August 19, 2020 and Septem- ber 15, 2020; accepted September 23, 2020. O. G ¨ unl ¨ u is supported by the German Federal Ministry of Education and Research (BMBF) within the national initiativ e for “Post Shannon Communication (Ne wCom)” under the Grant 16KIS1004. The associate editor coordinating the revie w of this manuscript and appro ving it for publication was Dr . Matthieu Bloch. O. G ¨ unl ¨ u is with the Information Theory and Applications Chair , T ech- nische Universit ¨ at Berlin, 10623 Berlin, German y (e-mail: guenlue@tu- berlin.de). with PUFs and biometric identifiers. In this classic model, an encoder observes a source output to generate a secret key and sends public side information, i.e., helper data , to a decoder , so the decoder can reliably reconstruct the same secret key by observing another source output and the helper data. The main constraints are that the information leak ed about the secret ke y , i.e., secr ecy leakage , is negligible and the information leaked about the identifier output, i.e., privacy leakage , is small [9], [10]. Furthermore, the amount of public storage should also be minimized to limit the hardware cost [11]. Suppose the encoder generates a key from a noisy measure- ment of a hidden (or remote) source output, and a decoder has access to another noisy measurement of the same source and the helper data to reconstruct the same key . W e call this model the gener ated-secr et (GS) model with a hidden source. This model is introduced in [12] as an extension of the visible (noiseless) source outputs observed by the encoder , considered in [9], [10]. Similarly , for the chosen-secr et (CS) model, an embedded (or chosen) ke y and noisy identifier measurements are combined by the encoder to generate the public helper data. W e consider both models to address different applications. A. Related W ork and Motivation The same identifier is used by multiple encoder and decoder pairs in [13], where the identifier outputs observed by different encoders are the same because the encoder measurements are assumed to be noiseless. Therefore, the multiple use of the same noiseless source output allows all encoders to know the secret key of the other encoders. This model does not fit well to the practical key agreement with identifier scenarios because there is noise in every identifier measurement. Multiple enrollments of a hidden source using noisy mea- surements are considered in [14], where weakly secure secret keys are generated without pri v acy leakage and storage con- straints. Furthermore, there is a causality assumption in [14] on the availability of the helper data, i.e., any decoder has access to all previously-generated helper data. This assumption is not necessarily realistic as a decoder of, e.g., an IoT device that embodies a PUF should be low complexity and the amount of data to process increases linearly with the number of enrollments. In addition, any manipulation in any of the helper data can cause the complete multi-enrollment system to fail. A classic method used for key agreement, i.e., the fuzzy commitment scheme (FCS) [15], is used in [16] in combina- tion with an SRAM PUF to enroll the noisy outputs of the same SRAM multiple times. The symmetry condition in [16, Eq. (16)] conditioned on a fixed SRAM cell state is entirely similar to the symmetry satisfied by binary-input symmetric 2 IEEE TRANSA CTIONS ON INFORMA TION FORENSICS AND SECURITY output (BISO) channels; see e.g., [17, p. 613], [12, Eq. (14)]. For SRAM outputs that satisfy this symmetry , the normalized (weak) secrecy leakage about each separate secret k ey is shown to be zero. It is discussed in [18, Section 3.4] that any uniformly-distributed hidden identifier output with BISO measurement channels satisfies the results in [16]. In [18, Theorem 1] the secret-key capacity of the two-enrollment key agreement problem is established for measurement channels with the same channel transition matrix. Ho we ver , these multi- enrollment models do not consider the priv ac y leakage and storage constraints, there is no constraint on the independence of the secret keys of different enrollments, and the secrecy leakage constraint is weak and is not applied jointly on all se- cret keys. Furthermore, optimal random linear code construc- tions that achieve the boundaries of the key-leakage-storage regions are gi ven in [19], where the classic code constructions FCS and code-offset fuzzy extractors [20] are sho wn to be strictly suboptimal. Therefore, the multi-enrollment models and constructions in the literature are strictly suboptimal and not necessarily realistic. W e therefore list stronger secrec y constraints jointly on all entities, which approximates the re- ality better in combination with storage rate and joint pri vac y- leakage rate constraints. These constraints define the multi- entity key agr eement problem, where the entities that use the same identifier do not hav e to trust other entities after key agreement. Therefore, the multi-entity key agreement problem is a proper multi-user extension of single-enrollment models. W e first consider the multi-entity ke y agreement problem and then analyze a special case of the multi-enrollment key agreement problem to illustrate scenarios for which a single enrollment can be more useful than multiple enrollments and vice versa. Every measurement of an identifier is considered to be noisy due to, e.g., local temperature and voltage changes in the hardware of the PUF circuit or a cut on the finger . Noise components at the encoder and decoder measurements of a hidden source can be also correlated due to, e.g., the surrounding logic in the hardware [21] or constant fingertip moisture. This correlation between the noise sequences is modeled in [22] as a broadcast channel (BC) [23] with an input that is the hidden source output and with outputs that are the noisy encoder and decoder measurements. W e use this model for multi-entity ke y agreement with identifiers, where each entity (i.e., each encoder and decoder pair) observes noisy identifier outputs of the same hidden source through different BCs. For the multi-entity key agreement problem, we allow the BCs to be different as honest entities generally use dif ferent hardware implementations of the encoder and decoder pairs, which results in different correlations between noise components. W e also consider physically-degraded (PD) and less-noisy (LN) BCs to give finer inner and outer bounds to the ke y- leakage-storage re gions for the GS and CS models of the multi-entity key agreement problem. For the considered PD and LN BCs, we prove that strong priv ac y can be achie ved. In [9], [10], [24], an extra common randomness that is av ailable to the encoder and decoder and that is hidden from the eav esdropper is required to obtain strong priv ac y . This assumption is not realistic since such a common randomness requires hardware protection against in vasi v e attacks, and if such a protection is feasible, then it is not necessary to use an identifier for ke y agreement. B. Models for Identifier Outputs W e study physical and biometric identifier outputs that are independent and identically distributed (i.i.d.) according to a giv en probability distribution. These models are reasonable if one uses transform-coding algorithms from [25] that occupy a small hardware area to extract almost i.i.d. bits from PUFs under varying environmental conditions. Similar transform- coding based algorithms ha ve been applied to biometric identifiers to obtain independent output symbols [26]. These transform-coding algorithms provide almost i.i.d. identifier outputs and noise sequences; howe v er , the correlation between the noise components on the encoder and decoder components are not remov ed using these methods. Furthermore, PUFs are used for on-demand key reconstruction and physical attacks on PUFs permanently change the identifier outputs [27], so we assume that the ea vesdropper cannot obtain information correlated with the PUF outputs, unlike biometric identifiers. C. Summary of Contributions W e extend the key-leakage-storage rate tuple analysis of the single-enrollment model for hidden identifier outputs mea- sured through general BCs in [22] to consider multi-entity and multi-enrollment key agreement with a set of stringent secrecy constraints. A summary of the main contributions is as follows. • W e derive achiev able key-leakage-storage rate tuples for the GS model with strong secrecy for any finite number of entities using the same identifier’ s measurements through different BCs for key agreement. Separate identifier mea- surements considered in [12], [28] correspond to a PD BC and the visible source model in [9], [10] corresponds to a semi-deterministic BC. • F or a set of PD and LN BCs, the pri v acy-leakage rates for the two-entity ke y agreement problem are calculated. These PD and LN BCs are shown to provide strong priv ac y without the need of a common randomness. An outer bound is giv en for the considered PD and LN BCs. • W e next consider a special case of the multi-enrollment key agreement problem, where all measurement channels are separate (i.e., PD BCs) and they have the same transition matrix. This is a common model used for SRAM PUFs. Using a less stringent secrecy leakage constraint that bounds the information leakage for each secret ke y separately and without the mutual indepen- dence constraint on the secret ke ys, we establish inner and outer bounds for the strong-secrecy ke y-leakage-storage region for this two-enrollment key agreement problem. The bounds differ only in the Markov chains imposed. This result is a significant improvement to the two- enrollment secret-key rate region (without storage and priv ac y-leakage rate constraints) established in [18] for weak secrecy , which is recovered by eliminating auxiliary random v ariables in the proposed rate regions. G ¨ UNL ¨ U: MUL TI-ENTITY AND MUL TI-ENR OLLMENT KEY AGREEMENT WITH CORRELA TED NOISE 3 • All inner and outer bounds for the GS model are extended to the CS model, which comprises secret-key binding methods that embed a chosen secret key to the encoder . • W e give two scenarios to compare single-enrollment and two-enrollment models and illustrate that for different assumptions on measurement channels, either of the two models can perform better in terms of the priv ac y-leakage vs. secret-ke y rate boundary tuples. D. Or ganization This paper is org anized as follows. In Section II, we describe the multi-entity ke y agreement problem with BC measure- ments. W e gi ve achiev able ke y-leakage-storage regions for the GS and CS models with strong secrecy and BC measurements for any finite number of entities in Section III in addition to inner and outer bounds for PD and LN BCs that satisfy strong priv ac y . The proposed inner bounds for the two-enrollment key agreement problem in Section IV are sho wn to dif fer from the outer bounds only in the Markov chains imposed for a special case with less stringent secrecy constraints. In Sections V and VI, proofs of the gi ven rate regions for the general multi-entity key agremeent problem and for the two- enrollment key agreement problem, respectiv ely , are giv en. Section VII concludes the paper . E. Notation Upper case letters represent random variables and lower case letters their realizations. A superscript denotes a string of variables, e.g., X n = X 1 , X 2 , . . . , X i , . . . , X n , and a subscript i denotes the position of a variable in a string. A random variable X has probability distribution P X . Calligraphic letters such as X denote sets, set sizes are written as |X | and their complements as X c . [1 : J ] denotes the set { 1 , 2 , . . . , J } for an integer J ≥ 1 and [1 : J ] \ { j } denotes the set { 1 , 2 , , . . . , j − 1 , j + 1 , . . . , J } for any j ∈ [1 : J ] . H b ( x ) = − x log x − (1 − x ) log (1 − x ) is the binary entropy function, where we tak e logarithms to the base 2 , and H − 1 b ( · ) denotes its in v erse with range [0 , 0 . 5] . X ∼ Bern ( α ) is a binary random variable with Pr[ X = 1] = α . A binary symmetric channel (BSC) with crosso ver probability p is denoted by BSC( p ). Q ( · ) is the Q -function that giv es the tail probability for the standard normal distribution. I I . M U LT I - E N T I T Y K E Y A G R E E M E N T M O D E L Consider hidden identifier outputs X n that are i.i.d. accord- ing to a probability distribution P X . The hidden (or remote) source with outputs X n is common to all honest entities that enroll the same identifier , but they observe different noisy measurements of the same hidden source. If there are a finite number J of honest entities that use the same identifer , the j -th encoder and decoder pair observes noisy source measurements that are outputs of a BC P e X j Y j | X , with abuse of notation, for all j ∈ [1 : J ] , where e X j , Y j , and X are finite sets. For the GS model illustrated in Fig. 1 ( a ) for J = 2 honest entities, the j -th encoder f GS ,j ( · ) generates helper data W j and a secret key S j from its observed sequence e X n j . All secret P X ( S 1 , W 1 ) ( a ) = f GS , 1 ( e X n 1 ) W 1 ( b ) = f CS , 1 ( e X n 1 , S 1 ) Ke y Database Public Database = ? P e X 1 Y 1 | X ˆ S 1 = g 1 ( Y n 1 , W 1 ) X n Y n 1 S 1 S 1 W 1 ˆ S 1 e X n 1 ( b ) ( a ) ( a ) ( b ) ( S 2 , W 2 ) ( a ) = f GS , 2 ( e X n 2 ) W 2 ( b ) = f CS , 2 ( e X n 2 , S 2 ) Ke y Database Public Database = ? P e X 2 Y 2 | X ˆ S 2 = g 2 ( Y n 2 , W 2 ) Y n 2 S 2 S 2 W 2 ˆ S 2 e X n 2 ( b ) ( a ) ( a ) ( b ) Fig. 1. Illustration of the multi-entity key agremeent problem for J = 2 entities with encoder and decoder measurements through BCs for ( a ) the GS model and ( b ) the CS model. keys are stored in a secure database, whereas helper data are stored in a public database so that an eavesdropper has access only to the helper data. Using the helper data W j and its observed sequence Y n j , the j -th decoder g j ( · , · ) generates the key estimate ˆ S j . Similar steps are applied for the CS model in Fig. 1 ( b ) also for J = 2 honest entities, except that each S j should be embedded into the j -th encoder f CS ,j ( · , · ) . Denote a set of secret keys as S K = { S j : j ∈ K} (1) and a set of helper data as W K = { W j : j ∈ K} (2) for any K ⊆ [1 : J ] . A (secret-key , priv ac y-leakage, storage), or key-leakage-storage, rate tuple is denoted as ( R s , R ` , R w ) . Similarly , we denote a set of secret-ke y rates, for any K ⊆ [1 : J ] , as R s , K = { R s ,j : j ∈ K} (3) and a set of storage rates as R w , K = { R w ,j : j ∈ K} . (4) W e next define the multi-entity key-leakage-storage regions. 4 IEEE TRANSA CTIONS ON INFORMA TION FORENSICS AND SECURITY Definition 1. A key-leakage-storage rate tuple ( R s , [1: J ] , R ` , R w , [1: J ] ) is achiev able for the multi-entity GS and CS models with j -th encoder and decoder measurements through a BC P e X j Y j | X if, given any δ > 0 , there is some n ≥ 1 , and J encoder and decoder pairs for which R s ,j = log |S j | n for all j ∈ [1 : J ] and Pr [ j ∈ [1: J ] { S j 6 = ˆ S j } ≤ δ (reliability) (5) 1 n H ( S j ) ≥ R s ,j − δ, ∀ j ∈ [1 : J ] (key uniformity) (6) I ( S K ; S K c ) ≤ δ, ∀K ⊆ [1 : J ] (strong ke y ind.) (7) 1 n I ( X n ; W [1: J ] ) ≤ R ` + δ (priv ac y) (8) I S [1: J ] ; W [1: J ] ≤ δ (strong secrecy) (9) 1 n log |W j | ≤ R w ,j + δ, ∀ j ∈ [1 : J ] (storage) . (10) The multi-entity ke y-leaka ge-stor age regions C gs for the GS model and C cs for the CS model are the closures of the set of all achie vable rate tuples ( R s , [1: J ] , R ` , R w , [1: J ] ) . Both secret-key uniformity (6) and storage rate (10) con- straints correspond to J separate constraints. Ho we ver , relia- bility (5), strong and mutual key independence (7), priv ac y- leakage rate (8), and secrecy leakage (9) constraints are joint constraints for all J honest entities. Suppose after a key gen- eration, an honest entity has access only to its corresponding secret key and it does not have access to other entities’ keys or sequences or ev en to the sequence it observed to generate its secret ke y . The mutual key independence constraint in (7) is not im- posed in the multi-enrollment key agreement problem consid- ered in [16]. Furthermore, a normalized (weak) version of this constraint is imposed in the multi-enrollment key agreement problem considered in [14], where the j -th decoder g j ( · , · ) is assumed to have access to the set of helper data W [1: j ] for all j ∈ [1 : J ] . The lack of the mutual key independence constraint and the assumption of av ailability of all previous helper data require that different encoder and decoder pairs should trust each other after key agreement. This can be the case, e.g., if all enrollments are made by the same entity . Therefore, the multi-entity ke y agreement problem imposes strictly more stringent constraints than the multi-enrollment key agreement problem. The unnormalized secrecy leakage constraint (9) provides strong secrecy , which is a stronger notion than the weak secrecy considered in [9], [10], [12], [14], [16], [28]. Further- more, (9) is more stringent than the set of individual secrecy leakage constraints I ( S j ; W [1: J ] ) imposed for all j ∈ [1 : J ] , considered in [16] for symmetric SRAM PUF outputs in combination with the suboptimal FCS. The unnormalized priv ac y leakage I ( X n ; W [1: J ] ) cannot be bounded by a finite number in general. W e illustrate special strong pri vac y cases in the next section. I I I . I N N E R B O U N D S W e are interested in characterizing the optimal trade-off among the secret-key , pri vac y-leakage, and storage rates with strong secrecy for BC measurements at the encoders and decoders of any finite number J of entities that use the same hidden identifier outputs for the multi-entity ke y agreement problem. W e give achiev able rate regions for the GS and CS models in Theorem 1. The proofs are given in Section V. Denote U K = { U j : j ∈ K} (11) and define a function max {· , ·} that giv es the maximum of the input v alues as its output. Theorem 1 (Inner Bounds for Multi-entity GS and CS Mod- els) . An achie vable rate re gion R gs for the multi-entity GS model with J entities is the union over all P U j | e X j for all j ∈ [1 : J ] of the rate tuples such that R s ,j ≥ 0 for all j ∈ [1 : J ] and R s ,j ≤ I ( U j ; Y j ) − I ( U j ; U [1: J ] \{ j } ) , ∀ j ∈ [1 : J ] (12) R ` ≥ J X j =1 max { 0 , I ( U j ; X ) − I ( U j ; Y j ) } , (13) R w ,j ≥ I ( U j ; e X j ) − I ( U j ; Y j ) , ∀ j ∈ [1 : J ] (14) R s ,j + R w ,j ≤ H ( U j | U [1: J ] \{ j } ) , ∀ j ∈ [1 : J ] . (15) An achie vable rate re gion R cs for the multi-entity CS model with J entities is the union over all P U j | e X j for all j ∈ [1 : J ] of the rate tuples such that R s ,j ≥ 0 for all j ∈ [1 : J ] , (12), (13), and R w ,j ≥ I ( U j ; e X j ) − I ( U j ; U [1: J ] \{ j } ) , ∀ j ∈ [1 : J ] (16) R w ,j ≤ H ( U j | U [1: J ] \{ j } ) , ∀ j ∈ [1 : J ] . (17) F or the achievable rate r e gions R gs and R cs , we have P U [1: J ] e X [1: J ] X Y [1: J ] = P X J Y j =1 P U j | e X j P e X j Y j | X . (18) Corollary 1. Suppose for all j ∈ [1 : J ] that • e X j − Y j − X form a Markov chain, i.e., X is a PD version of Y j with r espect to e X j , or • P X Y j | e X j is a LN BC with I ( U j ; Y j ) ≥ I ( U j ; X ) for all P U j | e X j . F or these cases, str ong privacy , i.e., R ` ≥ 0 (19) can be achieved for the multi-entity GS and CS models in combination with the other corr esponding bounds given in Theor em 1. The proof of Corollary 1 follows from Theorem 1 because I ( U j ; X ) − I ( U j ; Y j ) ≤ 0 for all j ∈ [1 : J ] for BCs considered in Corollary 1. Corollary 1 illustrates that it is possible to obtain strong priv ac y , i.e., negligible unnormalized priv acy leakage, without the requirement of a common randommness that is hidden from an eav esdropper assumed in [9], [10], [24]. This is the G ¨ UNL ¨ U: MUL TI-ENTITY AND MUL TI-ENR OLLMENT KEY AGREEMENT WITH CORRELA TED NOISE 5 case because the observ ation Y n j of each decoder is “better” than the observation e X n j of the corresponding encoder with respect to the hidden source X n for all entities. Remark 1. The rate regions for our problem depend on the joint conditional probability distributions P X Y j | e X j rather than only the mar ginal conditional distributions. Thus, the k ey- leakage-storage regions for the stochastically-degraded BCs are not necessarily equal to the regions for the corresponding PD BCs, unlike in the classic BC problem. Furthermore, since P e X [1: J ] X Y [1: J ] is fixed, the distinction between the LN BCs and essentially-less noisy BCs [29], is not necessary . W e next giv e simple outer bounds for the multi-entity key- leakage-storage regions C gs for the GS model and C cs for the CS model when the BCs P X Y j | e X j for all j ∈ [1 : J ] are PD BCs or LN BCs, as defined in Corollary 1. These simple outer bounds gi ve insights into the reason for dif ferent bounds on the secret-key rates. Based on these insights, we sho w a special multi-enrollment case in the next section with a less stringent secrecy constraint, for which the inner and outer bounds differ only in the Markov chains imposed and we illustrate that they match for simpler models. Lemma 1. Suppose one of the cases given in Cor ollary 1 is satisfied by the BCs P X Y j | e X j for all j ∈ [1 : J ] . An outer bound on the multi-entity ke y-leakag e-stora ge re gion C gs is the union over all P U j | e X j , wher e U j − e X j − ( X, Y j ) form a Markov chain, for all j ∈ [1 : J ] of the rate tuples such that R s ,j ≥ 0 for all j ∈ [1 : J ] , (14), (19), and R s ,j ≤ I ( U j ; Y j ) , ∀ j ∈ [1 : J ] . (20) An outer bound to the multi-entity key-leaka ge-stora ge r e gion C cs for the same BCs P X Y j | e X j is the union over all P U j | e X j , where U j − e X j − ( X, Y j ) form a Markov chain, for all j ∈ [1 : J ] of the rate tuples such that R s ,j ≥ 0 for all j ∈ [1 : J ] , (19), (20), and R w ,j ≥ I ( U j ; e X j ) , ∀ j ∈ [1 : J ] . (21) The proof of Lemma 1 follo ws straightforwadly by fol- lowing the steps in [12, Section VI], defining the auxiliary random variables U j,i = ( S j , W j , Y i − 1 j ) for all j ∈ [1 : J ] and i ∈ [1 : n ] , and by bounding I ( X n ; W [1: J ] ) ≥ 0 ; therefore, we omit the proof. The outer bounds do not include the inequalities in (15) and (17). Furthermore, the secret-key rate achiev ed by the inner bound in (12) is smaller than the outer bound given in (20), where the difference is the term − I ( U j ; U [1: J ] \{ j } ) . This term is a result of the constraint in (44) that is imposed to satisfy the strong and mutual key independence constraint given in (7). Therefore, we next consider a model without the constraint in (7) and use a secrecy-leakage constraint that is less stringent than the one in (9), i.e., replace (9) by I ( S j ; W [1: J ] ) ≤ δ, ∀ j ∈ [1 : J ] (22) which is also a strong secrecy metric. Due to the lack of a mutual ke y independence constraint, the model in the next section is not a multi-entity model but rather a multi- enrollment model. For a special case of this multi-enrollment key agreement problem, we establish inner and outer bounds for the ke y-leakage-storage re gions that comprise the same bounds but for different Markov chains. I V . B O U N D S F O R A M U LT I - E N RO L L M E N T M O D E L Consider next the multi-enrollment model, where the strong and mutual key independence constraint (7) of the multi-entity model is not imposed. Assume further J = 2 entities that measure noisy outputs of the same hidden source X n through separate channels that ha ve the same channel transition matri- ces, i.e., for all j ∈ [1 : 2] , ˜ x j ∈ e X , and y j ∈ e X we hav e P e X j Y j | X ( ˜ x j , y j | x ) = P e X | X ( ˜ x j | x ) P e X | X ( y j | x ) . (23) This model is common for SRAM PUFs, for which each measurement channel is modeled as a BSC with the same crossov er probability corresponding to a worst case scenario [30]. Using (23), we define a multi-enrollment model. Definition 2. A key-leakage-storage rate tuple ( s R s , 1 , s R s , 2 , s R ` , s R w , 1 , s R w , 2 ) is achie vable for the multi- enrollment GS and CS models with measurements through a BC P e X Y | X ( ˜ x, y | x ) as in (23) if, giv en any δ > 0 , there is some n ≥ 1 , and two encoder and decoder pairs for which s R s , 1 = log |S 1 | n , s R s , 2 = log |S 2 | n , s R w , 1 = H ( W 1 ) n , s R w , 2 = H ( W 2 ) n , and Pr h { S 1 6 = ˆ S 1 } [ { S 2 6 = ˆ S 2 } i ≤ δ (reliability) (24) 1 n H ( S j ) = s R s ,j − δ, j = 1 , 2 (key uniformity) (25) 1 n I ( X n ; W 1 , W 2 ) = s R ` + δ (priv ac y) (26) I ( S j ; W 1 , W 2 ) ≤ δ, j = 1 , 2 (strong secrecy) (27) 1 n log |W j | = s R w ,j + δ, j = 1 , 2 (storage) (28) I ( W 1 ; W 2 ) ≤ δ (storage ind.) . (29) The multi-enr ollment ke y-leakag e-storag e regions s C gs ,J =2 for the GS model and s C cs ,J =2 for the CS model are the closures of the set of all achiev able rate tuples ( s R s , 1 , s R s , 2 , s R ` , s R w , 1 , s R w , 2 ) . W e characterize in Theorem 2 inner and outer bounds for s C gs ,J =2 and s C cs ,J =2 . The proofs of Theorem 2 are given in Section VI, where the reason for the necessity of the secrecy-leakage constraint in (27) that is less stringent than the joint secrecy-leakage constraint in (9) is giv en in Remark 2. Similarly , the reason for the necessity of the strong helper data (storage) independence constraint in (29) is discussed in Remark 4. W e remark that the equalities in (25), (26), and (28) are required in the outer bounds in Theorem 2 to provide both upper and lo wer bounds on s R ` and s R w ,j in terms of Shannon entropy terms. Denote j 0 = 3 − j, j = 1 , 2 . (30) 6 IEEE TRANSA CTIONS ON INFORMA TION FORENSICS AND SECURITY Theorem 2. (Inner Bounds for Multi-enrollment GS and CS Models) : An achievable multi-enr ollment ke y-leakage-stor ag e r e gion Ď R gs ,J =2 is the union over all P U 1 | e X 1 and P U 2 | e X 2 of the rate tuples such that s R s ,j ≥ 0 for j = 1 , 2 and s R s ,j ≤ I ( U j ; Y j ) , j = 1 , 2 (31) s R ` ≥ 2 X j =1 I ( U j ; X ) − I ( U j ; Y j ) , (32) s R ` ≤ 2 X j =1 I ( U j ; X ) − I ( U j ; e X j ) + s R w ,j , (33) s R w ,j ≥ I ( U j ; e X j ) − I ( U j ; Y j ) , j = 1 , 2 (34) s R s ,j + s R w ,j ≤ H ( U j ) , j = 1 , 2 (35) s R s ,j + s R w ,j + s R w ,j 0 ≤ H ( U j , U j 0 ) , j = 1 , 2 . (36) An ac hievable multi-enr ollment ke y-leakage-stor ag e r egion Ď R cs ,J =2 is the union over all P U 1 | e X 1 and P U 2 | e X 2 of the rate tuples such that s R s ,j ≥ 0 for j = 1 , 2 , (31)-(33), and s R w ,j ≥ I ( U j ; e X j ) , j = 1 , 2 (37) s R w ,j ≤ H ( U j ) , j = 1 , 2 (38) s R w ,j + s R w ,j 0 ≤ H ( U j , U j 0 ) + s R s ,j 0 , j = 1 , 2 . (39) F or both ac hievable rate re gions Ď R gs ,J =2 and Ď R cs ,J =2 , we have P U 1 U 2 e X 1 e X 2 X Y 1 Y 2 ( u 1 , u 2 , e x 1 , e x 2 , x, y 1 , y 2 ) = P U 1 | e X 1 ( u 1 | ˜ x 1 ) P U 2 | e X 2 ( u 2 | ˜ x 2 ) P e X | X ( ˜ x 1 | x ) P e X | X ( ˜ x 2 | x ) × P e X | X ( y 1 | x ) P e X | X ( y 2 | x ) P X ( x ) . (40) (Outer Bounds for Multi-enrollment GS and CS Models) An outer bound for s C gs ,J =2 is the union over all P U 1 | e X 1 and P U 2 | e X 2 of the rate tuples such that s R s ,j ≥ 0 , (31) - (36), and U j − e X j − X − Y j form a Markov chain for j = 1 , 2 . An outer bound for s C cs ,J =2 is the union over all P U 1 | e X 1 and P U 2 | e X 2 of the rate tuples such that s R s ,j ≥ 0 , (31) - (33), (37) - (39), and U j − e X j − X − Y j form a Markov chain for j = 1 , 2 . The inner and outer bounds differ because the outer bounds define rate regions for the Markov chains U 1 − e X 1 − X − Y 1 and U 2 − e X 2 − X − Y 2 , which are larger than the rate regions defined by the inner bounds that satisfy (40). For instance, in the achiev ability proof of Theorem 2, we apply the properties of the Markov chain U 2 − e X 2 − U 1 in (86)(b), which does not form a Marko v chain for the choice of U 1 and U 2 in the outer bounds. Therefore, inner and outer bounds do not match in general. Corollary 2. Choosing U 1 = e X 1 and U 2 = e X 2 , it is straight- forwar d to show that inner and outer bounds in Theor em 2 match if we do not impose any storage or privacy constraints, i.e., impose only (24), (25), and (27). This result impr o ves on the secret-k e y capacity r e gion given in [18, Theorem 1] for a weak secr ecy constraint. Example 1. Consider the R O PUF model from [25, Section 4.1] wher e a transform-coding method is applied to conser- vatively model the measurement channels P Y | X = P e X | X 0 0 . 05 0 . 1 0 . 15 0 . 2 0 0 . 1 0 . 2 0 . 3 0 . 4 0 . 5 0 . 6 Priv ac y-leakage Rate s R ` (bits/symbol) Secret-key Rate s R s (bits/symbol) Single-enrollment T wo-enrollment Sum Rate Fig. 2. Priv acy-leakage vs. secret-key rate projection of the boundary tuples of the single- and two-enrollment R O PUF models with BSCs ( p A = 0 . 06) . as independent BSCs with the same cr ossover pr obability of p A and wher e the hidden sour ce output is Bern ( 1 2 ) . W e ther efor e can apply the achievability r esults fr om Theor em 2 to this R O PUF model. Using [12, Theor em 3] to evaluate the boundary tuples of Ď R gs ,J =2 , it suffices to consider pr obability distributions P U j | e X j for j = 1 , 2 such that P e X j | U j ar e BSCs with cr osso ver pr obabilities ˜ x j = H − 1 b ( H ( X | U j )) − p A 1 − 2 p A . (41) Consider the pr ojection of the boundary tuples of Ď R gs ,J =2 onto ke y-leakag e plane, i.e., (31) and (32). W e plot in F ig. 2 single- enr ollment r esults wher e the privacy-leakage rate is measur ed with respect to single helper data and two-enr ollment results for the sum rate of the two keys, both for p A = 0 . 06 [25]. T o achieve a total secr et-ke y rate of I ( e X 1 ; Y 1 ) = I ( e X 2 ; Y 2 ) , the privacy-leakage rate for the two-enr ollment model is appr oximately 13 . 5% less than the privacy-leakage rate for the single-enr ollment model for RO PUFs. The reason for this gain is the information bottleneck pr oblem that arises fr om (31) and (32) to find the boundary tuples. Example 2. Consider uniform binary antipodal measur ements over an additive white Gaussian noise (A WGN) channel. Define the signal power as P S and the noise power as P N , so we have a signal-to-noise ratio (SNR) of S N R = P S P N . If a matched filter , which maximizes the S N R at the sampling instant for the A WGN channel, is applied at the encoder and decoder , the bit err or pr obability P b is given by [31, pp. 96] P b = Q √ S N R . (42) The channel between input binary symbols and outputs of the matched filter is a BISO channel. Using [12, Theor em 3], we G ¨ UNL ¨ U: MUL TI-ENTITY AND MUL TI-ENR OLLMENT KEY AGREEMENT WITH CORRELA TED NOISE 7 0 0 . 02 0 . 04 0 . 06 0 . 08 0 . 1 0 0 . 2 0 . 4 0 . 6 0 . 8 1 Priv ac y-leakage Rate s R ` (bits/symbol) Secret-key Rate s R s (bits/symbol) Single-enrollment @ S N R = 6 . 84 dB. T wo-enrollment Sum Rate @ S N R = 3 . 83 dB Fig. 3. Priv acy-leakage vs. secret-key rate projection of the boundary tuples of the single- and two-enrollment R O PUF models with different SNRs. have that P e X j | U j for j = 1 , 2 that are BSCs with cr ossover pr obabilities given in (41) by r eplacing p A with P b , suffice to obtain the boundary tuples of Ď R gs ,J =2 . W e r emark that p A = 0 . 06 used in Example 1 corr esponds to an SNR of appr oximately 3 . 83 dB. In F ig. 3, the privacy-leakage r ate vs. secr et-ke y rate bound- ary tuples ar e depicted for two cases. F ir st, a two-enr ollment model at S N R = 3 . 83 dB with a sum rate for two secr et keys is depicted, where each enr ollment has a signal power of P s . F or comparison, we plot a single-enr ollment model with the signal power of 2 P s , i.e., we have an SNR of appr oximately 6 . 84 dB. F ig . 3 shows for the two cases with the same total signal power of 2 P s , unlike in Example 1, that the single enrollment boundary tuple can r esult in a gain of appr oximately 228 . 55% at its top left corner point in terms of the secret-k e y rates achie ved for a given privacy-leakage rate . F or such an A WGN channel with a fixed total signal power; therefor e, the single- enr ollment model can r esult in significant gains in terms of achie ved secret-k e y rates as compared to the two-enr ollment model for small s R ` values. V . P R O O F O F T H E O R E M 1 W e provide a proof that follows from the output statistics of random binning (OSRB) method, proposed in [32] and further extended in [33], by applying the steps in [34, Section 1.6]. A. Pr oof for the GS Model Pr oof Sketch: Fix P U 1 | e X 1 , P U 2 | e X 2 , . . . , P U J | e X J . Let ( U n [1: J ] , e X n [1: J ] , X n , Y n [1: J ] ) be i.i.d. according to (18). Assign three random bin indices ( S j , W j , C j ) to each realization u n j for all j ∈ [1 : J ] , where S j represents the secret key , W j the helper data, and C j a public index referring to a random encoder-decoder pair fixed below . Assume S j ∈ [1 : 2 nR s ,j ] , W j ∈ [1 : 2 nR w ,j ] , and C j ∈ [1 : 2 nR c ,j ] such that R s ,j , R w ,j , R c ,j ≥ 0 for all j ∈ [1 : J ] . Apply the union bound to the reliability constraint in (5) to obtain the sum of J error probabilities. This sum v anishes for any finite number J when n → ∞ by using a Slepian-W olf (SW) [35] decoder to estimate U n j from ( C j , W j , Y n j ) if [32, Lemma 1] R c ,j + R w ,j > H ( U j | Y j ) , ∀ j ∈ [1 : J ] . (43) The ke y uniformity (6), mutual and strong key independence (7), and strong secrec y (9) constraints are satisfied if [32, Theorem 1] R s ,j + R w ,j + R c ,j < H ( U j | U [1: J ] \{ j } ) , ∀ j ∈ [1 : J ] (44) since (44) ensures that the three random indices ( S j , W j , C j ) are almost mutually independent and uniformly distrib uted, and they are almost independent of U [1: J ] \{ j } . Therefore, ( S j , W j , C j ) are almost independent of S [1: J ] \{ j } , W [1: J ] \{ j } , C [1: J ] \{ j } because U n k determines ( S k , W k , C k ) for all k ∈ [1 : J ] . Similarly , the public randomness C j is almost independent of e X n j , so it is almost independent of ( e X n [1: J ] , X n , Y n [1: J ] ) , if we hav e [32, Theorem 1] R c ,j < H ( U j | e X j ) , ∀ j ∈ [1 : J ] . (45) Thus, the public indices C [1: J ] can be fixed and shared with all parties by generating them uniformly at random. The j -th encoder can generate U n j according to P U n j | e X n j C j ob- tained from the binning scheme above to compute the bins ( S j , W j ) from U n j for all j ∈ [1 : J ] . This procedure induces a joint probability distribution that is almost equal to P U [1: J ] e X [1: J ] X Y [1: J ] fixed in (18) [34, Section 1.6]. Applying the Fourier Motzkin elimination [36] using the software av ailable in [37] to (43)-(45) for each j ∈ [1 : J ] separately , we obtain the inequalities R w ,j > I ( U j ; e X j ) − I ( U j ; Y j ) (46) R s ,j < I ( U j ; Y j ) − I ( U j ; U [1: J ] \{ j } ) (47) R w ,j + R s ,j < H ( U j |U [1: J ] \{ j } ) (48) for all j ∈ [1 : J ] . T o satisfy the constraints (46)-(48), we can fix the rates to R s ,j = I ( U j ; Y j ) − I ( U j ; U [1: J ] \{ j } ) − 2 , ∀ j ∈ [1 : J ] (49) R w ,j = I ( U j ; e X j ) − I ( U j ; Y j ) + 2 , ∀ j ∈ [1 : J ] (50) R c ,j = H ( U j | e X j ) − , ∀ j ∈ [1 : J ] (51) for some > 0 such that → 0 when n → ∞ . Consider the priv acy leakage. Since C [1: J ] are public, we 8 IEEE TRANSA CTIONS ON INFORMA TION FORENSICS AND SECURITY can bound the priv acy leakage as follows. I ( X n ; W [1: J ] , C [1: J ] ) ≤ H ( W [1: J ] ) − H ( W [1: J ] , C [1: J ] | X n ) + H ( C [1: J ] ) ( a ) = H ( W [1: J ] ) − J X j =1 H ( W j , C j | X n ) + H ( C [1: J ] ) ≤ J X j =1 H ( W j ) + H ( C j ) − H ( W j , C j | X n ) (52) where ( a ) follows because ( W j , C j ) − X n − ( W [1: j − 1] , C [1: j − 1] ) form a Markov chain for all j ∈ [2 : J ] . Consider two cases for the priv ac y leakage analysis. Case 1: Suppose for any j ∈ [1 : J ] that we have R c ,j + R w ,j < H ( U j | X ) (53) i.e., H ( U j | X ) > H ( U j | Y j ) , so ( W j , C j , X n ) are almost mutually independent [32, Theorem 1]. Therefore, we have H ( W j ) + H ( C j ) − H ( W j , C j | X n ) ≤ H ( W j ) + H ( C j ) − ( H ( W j ) + H ( C j ) − 0 n ) = 0 n (54) for some 0 n > 0 such that 0 n → 0 when n → ∞ . Combining (52) and (54) proves strong priv acy . Case 2: Suppose for any j ∈ [1 : J ] that we have R c ,j + R w ,j ≥ H ( U j | X ) (55) i.e., H ( U j | X ) ≤ H ( U j | Y j ) , so ( W j , C j , X n ) can reliably estimate U n j [32, Lemma 1]. Therefore, we have H ( W j ) + H ( C j ) − H ( W j , C j | X n ) ( a ) ≤ H ( W j ) + H ( C j ) − nH ( U j | X ) + n 00 n ( b ) ≤ n ( I ( U j ; X ) − I ( U j ; Y j ) + + 00 n ) (56) where ( a ) follows because U n j determines ( W j , C j ) , ( W j , C j , X n ) can realiably estimate U n for some 00 n > 0 such that 00 n → 0 when n → ∞ , and ( U n j , X n ) are i.i.d., and ( b ) follo ws by (50) and (51). Combining (52) and (56), we obtain I ( X n ; W [1: J ] , C [1: J ] ) ≤ J X j =1 j : H ( U j | X ) ≤ H ( U j | Y j ) n ( I ( U j ; X ) − I ( U j ; Y j ) + + 00 n ) . (57) Using the selection lemma [38, Lemma 2.2], these prove the achie vability of the rate region R gs . B. Pr oof for the CS Model W e use the achievability proof for the GS model. Suppose the key S 0 j , generated as in the GS model together with the helper data W 0 j and public index C 0 j , have the same cardinality as the corresponding embedded secret key S j , i.e., |S 0 j | = |S j | for all j ∈ [1 : J ] . The chosen key S j is uniformly distributed and independent of ( X n , e X n [1: J ] , Y n [1: J ] , S [1: J ] \{ j } ) for all j ∈ [1 : J ] . Consider the j -th encoder f cs ,j ( · , · ) with inputs ( e X n j , S j ) and output W j = ( S 0 j + S j , W 0 j ) , and the j -th decoder g j ( · , · ) with inputs ( Y n j , W j ) and output ˆ S j = S 0 j + S j − ˆ S 0 j . All addition and subtraction operations are modulo- |S j | for all j ∈ [1 : J ] . The j -th decoder of the GS model is used to obtain ˆ S 0 j for all j ∈ [1 : J ] . W e hav e the error probability Pr [ j ∈ [1: J ] { S j 6 = ˆ S j } = Pr [ j ∈ [1: J ] { S 0 j 6 = ˆ S 0 j } (58) which is small due to the proof of achiev ability for the GS model. Using (49) and (50), and from the one-time padding oper- ation applied abov e, we can achieve a storage rate of R w ,j ≥ I ( U j ; e X j ) − I ( U j ; U [1: J ] \{ j } ) , ∀ j ∈ [1 : J ] (59) for the CS model. W e hav e the secrecy leakage of I ( S [1: J ] ; W [1: J ] , C 0 [1: J ] ) ( a ) = I ( S [1: J ] ; W [1: J ] |C 0 [1: J ] ) = I ( S [1: J ] ; W 0 [1: J ] |C 0 [1: J ] ) + I ( S [1: J ] ; ( S 0 + S ) [1: J ] |W 0 [1: J ] , C 0 [1: J ] ) ( b ) = H (( S 0 + S ) [1: J ] |W 0 [1: J ] , C 0 [1: J ] ) − H ( S 0 [1: J ] |W 0 [1: J ] , C 0 [1: J ] ) ( c ) ≤ n J X j =1 R s ,j − H ( S 0 [1: J ] |C 0 [1: J ] ) + I ( S 0 [1: J ] ; W 0 [1: J ] |C 0 [1: J ] ) ( d ) ≤ n J X j =1 R s ,j − n J X j =1 R s ,j − 000 n + I ( S 0 [1: J ] ; W 0 [1: J ] |C 0 [1: J ] ) ( e ) ≤ 000 n + (4) n (60) where ( a ) follows since S [1: J ] are chosen independently of the public indices C [1: J ] , ( b ) follows because S [1: J ] are chosen independently of ( W 0 [1: J ] , C 0 [1: J ] , S 0 [1: J ] ) , ( c ) follows because |S 0 j | = |S j | for all j ∈ [1 : J ] , ( d ) follows because S 0 [1: J ] and C 0 [1: J ] are almost mutually independent and each S 0 j is almost uniformly distributed due to (44) for some 000 n > 0 such that 000 n → 0 when n → ∞ , and ( e ) follows because the GS model satisfies the strong secrecy constraint (9) due to (44) for some (4) n > 0 such that (4) n → 0 when n → ∞ . Consider the pri v acy leakage: I ( X n ; W [1: J ] , C 0 [1: J ] ) ≤ I ( X n ; W 0 [1: J ] , C 0 [1: J ] ) + H (( S + S 0 ) [1: J ] |W 0 [1: J ] , C 0 [1: J ] ) − H (( S + S 0 ) [1: J ] | X n , W 0 [1: J ] , C 0 [1: J ] , S 0 [1: J ] ) ( a ) ≤ I ( X n ; W 0 [1: J ] , C 0 [1: J ] ) + J X j =1 log( |S j | ) − H ( S [1: J ] ) ( b ) = I ( X n ; W 0 [1: J ] , C 0 [1: J ] ) (61) where ( a ) follows because S [1: J ] are chosen independently of ( X n , W 0 [1: J ] , S 0 [1: J ] , C 0 [1: J ] ) and |S 0 j | = |S j | for all j ∈ [1 : J ] and ( b ) follo ws from the uniformity and mutual independence of S [1: J ] . Using the selection lemma, these prove the achiev ability of the rate region R cs . G ¨ UNL ¨ U: MUL TI-ENTITY AND MUL TI-ENR OLLMENT KEY AGREEMENT WITH CORRELA TED NOISE 9 V I . P R O O F O F T H O R E M 2 W e use the OSRB method steps in [34, Section 1.6]. A. Achievability Pr oof for the GS Model Fix P U 1 | e X 1 = P U 2 | e X 2 = P U | e X . (62) Let ( U n 1 , U n 2 , e X n 1 , e X n 2 , X n , Y n 1 , Y n 2 ) be i.i.d. according to (40). Assign three random bin indices ( S j , W j , C j ) to each realization u n j for all j = 1 , 2 . Assume S j ∈ [1 : 2 n Ď R s ,j ] , W j ∈ [1 : 2 n Ď R w ,j ] , and C j ∈ [1 : 2 n Ď R c ,j ] such that s R s ,j , s R w ,j , s R c ,j ≥ 0 for j = 1 , 2 . Apply the union bound to the reliability constraint in (24), which v anishes when n → ∞ by using an SW decoder to estimate U n j from ( C j , W j , Y n j ) if [32, Lemma 1] s R c ,j + s R w ,j > H ( U j | Y j ) , j = 1 , 2 . (63) The key uniformity (25) constraint is satisfied if [32, The- orem 1] s R s ,j + s R w ,j + s R c ,j < H ( U j ) , j = 1 , 2 (64) since (64) ensures that the three random indices ( S j , W j , C j ) are almost mutually independent and uniformly distributed. Suppose a virtual joint encoder assigns six indices ( S 1 , W 1 , C 1 , S 2 , W 2 , C 2 ) to each realization pair ( u n 1 , u n 2 ) . This virtual encoder is an operational dual of the virtual decoder used in the proof of [18, Theorem 1]. Using the virtual joint encoder , the strong secrecy constraint in (27) and the strong helper data independence constraint in (29) are satisfied if [32, Theorem 1] s R s , 1 + s R w , 1 + s R c , 1 + s R w , 2 + s R c , 2 < H ( U 1 , U 2 ) (65) and s R s , 2 + s R w , 2 + s R c , 2 + s R w , 1 + s R c , 1 < H ( U 1 , U 2 ) (66) because (65) ensures that ( S 1 , W 1 , C 1 , W 2 , C 2 ) are al- most mutually independent; whereas, (66) ensures that ( S 2 , W 2 , C 2 , W 1 , C 1 ) are almost mutually independent. Remark 2. The set of equations considered in (64)-(66) cannot be imposed for the joint secrecy-leakage constraint in (9) for general probability distributions P e X 1 e X 2 X Y 1 Y 2 , since to impose (9) one would replace (65) and (66) with s R s , 1 + s R w , 1 + s R c , 1 + s R s , 2 + s R w , 2 + s R c , 2 < H ( U 1 , U 2 ) (67) which would also imply the mutual independence of secret keys in (7). Howe ver , the inequalities in (64) and (67) cannot be satisfied simultaneously in general as H ( U 1 ) + H ( U 2 ) ≥ H ( U 1 , U 2 ) . This problem is avoided in the proof of Theorem 1 by imposing the inequality in (44) rather than (64). The public randomness C j is almost independent of e X n j , so it is almost independent of ( e X n 1 , e X n 2 , X n , Y n 1 , Y n 2 ) , if we hav e [32, Theorem 1] s R c ,j < H ( U j | e X j ) , j = 1 , 2 . (68) Thus, the public indices ( C 1 , C 2 ) can be fixed and shared publicly by generating them uniformly at random. U n j can be generated according to P U n j | e X n j C j for j = 1 , 2 obtained from the binning scheme abov e to compute the bins ( S j , W j ) from U n j for j = 1 , 2 . This procedure induces a joint probability distribution that is almost equal to P U 1 U 2 e X 1 e X 2 X Y 1 Y 2 that is fixed in (40) [34, Section 1.6]. Applying the Fourier Motzkin elimination to (63)-(66) and (68), we obtain the inequalities s R w , 1 > H ( U 1 | Y 1 ) − H ( U 1 | e X 1 ) (69) s R w , 2 > H ( U 2 | Y 2 ) − H ( U 2 | e X 2 ) (70) s R s , 1 < I ( U 1 ; Y 1 ) (71) s R s , 2 < I ( U 2 ; Y 2 ) (72) s R s , 1 < − H ( U 1 | Y 1 ) − H ( U 2 | Y 2 ) + H ( U 1 , U 2 ) (73) s R s , 2 < − H ( U 1 | Y 1 ) − H ( U 2 | Y 2 ) + H ( U 1 , U 2 ) (74) s R s , 1 + s R w , 2 < − H ( U 1 | Y 1 ) + H ( U 1 , U 2 ) (75) s R s , 1 + s R w , 1 < H ( U 1 ) (76) s R s , 1 + s R w , 1 < − H ( U 2 | Y 2 ) + H ( U 1 , U 2 ) (77) s R s , 1 + s R w , 1 + s R w , 2 < H ( U 1 , U 2 ) (78) s R s , 2 + s R w , 2 < − H ( U 1 | Y 1 ) + H ( U 1 , U 2 ) (79) s R s , 2 + s R w , 2 < H ( U 2 ) (80) s R s , 2 + s R w , 1 < − H ( U 2 | Y 2 ) + H ( U 1 , U 2 ) (81) s R s , 2 + s R w , 2 + s R w , 1 < H ( U 1 , U 2 ) . (82) Observe that we hav e H ( U 1 | e X 2 ) = H ( U 1 | Y 1 ) = H ( U 2 | e X 1 ) = H ( U 2 | Y 2 ) (83) H ( U 1 | e X 1 ) = H ( U 2 | e X 2 ) (84) H ( U 1 ) = H ( U 2 ) (85) due to (23) and (62). W e therefore obtain H ( U 1 , U 2 ) − H ( U 1 | Y 1 ) ( a ) = H ( U 2 ) + H ( U 1 | U 2 ) − H ( U 1 | e X 2 ) ( b ) ≥ H ( U 2 ) (86) where ( a ) follows by (83) and ( b ) follo ws from the Marko v chain U 2 − e X 2 − U 1 . A similar result can be shown by swaping the indices. Therefore, the constraints in (77) and (79) are inactiv e due to the constraints, respectiv ely , in (76) and (80). Similarly , the constraints in (73) and (74) are inactive due to the constraints, respecti vely , in (71) and (72). Replace the inequalities in (75) and (81), respectiv ely , with 2 s R s , 1 + s R w , 1 + s R w , 2 < I ( U 1 ; Y 1 ) + H ( U 1 , U 2 ) (87) 2 s R s , 2 + s R w , 2 + s R w , 1 < I ( U 2 ; Y 2 ) + H ( U 1 , U 2 ) . (88) Then, (87) is inactiv e because (71) and (78) imply (87), and (88) is inacti ve because (72) and (82) imply (88). W e remark that the rate region represented by (69)-(82) is the same as the region represented by replacing (75) and (81) with (87) and (88) because the corner points (i.e., the points that asymptotically achiev e equalities in the given inequalities for fixed P U 1 | e X 1 = P U 2 | e X 2 ) of the two rate regions are the same. Therefore, the inequalities in (75) and (81) are inacti ve. 10 IEEE TRANSA CTIONS ON INFORMA TION FORENSICS AND SECURITY T o satisfy the constraints (69)-(82), we can fix the rates to s R s ,j = I ( U j ; Y j ) − 5 , j = 1 , 2 (89) s R w ,j = I ( U j ; e X j ) − I ( U j ; Y j ) + 2 , j = 1 , 2 (90) s R c ,j = H ( U j | e X j ) − , j = 1 , 2 (91) for some > 0 such that → 0 when n → ∞ due to (83)-(86). Since C 1 and C 2 are public, we can bound the priv acy leakage as follo ws. I ( X n ; W 1 , W 2 , C 1 , C 2 ) ( a ) ≤ H ( W 1 , W 2 ) − H ( W 1 , C 1 | X n ) − H ( W 2 , C 2 | X n ) + H ( C 1 , C 2 ) ( b ) ≤ H ( W 1 ) + H ( W 2 ) − H ( U n 1 | X n ) − H ( U n 2 | X n ) + 2 n 00 n + H ( C 1 ) + H ( C 2 ) (92) ( c ) ≤ n ( I ( U 1 ; X ) − I ( U 1 ; Y 1 ) + I ( U 2 ; X ) − I ( U 2 ; Y 2 )) + 2 n 00 n + 2 n (93) where ( a ) follows because ( W 1 , C 1 ) − X n − ( W 2 , C 2 ) form a Markov chain, ( b ) follows for some 00 n > 0 such that 00 n → 0 when n → ∞ because for the two-enrollment model considered, (55) is satisfied due to the Markov chain U j − X − Y j for j = 1 , 2 , and ( c ) follows by (90) and (91), and because ( U n 1 , U n 2 , X n ) are i.i.d. Using (92) for general rate tuples that satisfy the constraints (69)-(82), i.e., not only (89)-(91), we can bound the priv ac y leakage alternati vely as I ( X n ; W 1 , W 2 , C 1 , C 2 ) ( a ) ≤ n s R w , 1 + n s R w , 2 + nI ( U 1 ; X ) − nI ( U 1 ; e X 1 ) + nI ( U 2 ; X ) − nI ( U 2 ; e X 2 ) + 2 n 00 n (94) where ( a ) follo ws by (91) and because ( U n 1 , U n 2 , X n ) are i.i.d. Using the selection lemma, these prove the achiev ability of the ke y-leakage-storage region Ď R gs ,J =2 . B. Achievability Pr oof for the CS Model The achiev ability proof for the CS model follows by apply- ing the one-time padding step used in Section V -B. C. Outer Bound Pr oofs for the Multi-enr ollment Models Suppose for some δ n > 0 and n , there is a pair of encoders and decoders such that (24)-(29) are satisfied by some key- leakage-storage tuple ( s R s , 1 , s R s , 2 , s R ` , s R w , 1 , s R w , 2 ) . Using (24) and Fano’ s inequality , we obtain H ( S j | W j , Y n j ) ( a ) ≤ H ( S j | ˆ S j ) ≤ n n , j = 1 , 2 (95) where ( a ) permits randomized decoding, n = δ n max { s R s , 1 , s R s , 2 } + H b ( δ n ) /n such that n → 0 if δ n → 0 . Let U j,i , ( S j , W j , X i − 1 ) , which satisfies the Markov chain U j,i − e X j,i − X i − Y j,i for all i ∈ [1 : n ] and j = 1 , 2 . Remark 3. F or the choice of U j,i = ( S j , W j , X i − 1 ) (and similarly for U j,i = ( S j , W j , Y i − 1 j ) ) for j = 1 , 2 , U 1 ,i − e X 1 ,i − U 2 ,i do not form a Markov chain for all i ∈ [1 : n ] although for the inner bound we use this Markov chain. This is the r eason why inner and outer bounds do not match in general. Pr oof for (31) : W e obtain for the multi-enrollment GS and CS models for j = 1 , 2 that n ( s R s ,j − δ n ) ( a ) ≤ H ( S j ) − H ( S j | W j , Y n j ) + n n ( b ) ≤ I ( S j ; Y n j | W j ) + n n + δ n ≤ n X i =1 h I ( S j , W j , Y i − 1 j ; Y j,i ) + n + δ n n i ( c ) ≤ n X i =1 h I ( S j , W j , X i − 1 ; Y j,i ) + n + δ n n i ( d ) = n X i =1 h I ( U j,i ; Y j,i ) + n + δ n n i (96) ( a ) follows by (25) and (95), ( b ) follo ws by (27), ( c ) follows by applying the data-processing inequality to the Markov chain Y i − 1 j − ( W j , S j , X i − 1 ) − Y j,i , j = 1 , 2 , ∀ i ∈ [1 : n ] (97) and ( d ) follo ws from the definition of U j,i . Pr oof for (32) : Observ e for the multi-enrollment models that n ( s R ` + δ n ) ( a ) = H ( W 1 , W 2 ) − H ( W 1 | X n ) − H ( W 2 | X n ) ( b ) = H ( W 1 | Y n 1 ) − H ( W 1 | X n ) + H ( W 2 | Y n 2 ) − H ( W 2 | X n ) + I ( W 1 ; e X n 2 ) + I ( W 2 ; Y n 2 ) − I ( W 1 ; W 2 ) ( c ) ≥ 2 X j =1 h H ( W j | Y n j ) − H ( W j | X n ) i ≥ 2 X j =1 h H ( S j , W j , Y n j ) − H ( S j | W j , Y n j ) − H ( Y n j ) − H ( S j , W j | X n ) i ( d ) ≥ 2 X j =1 h I ( S j , W j ; X n ) − I ( S j , W j ; Y n j ) − n n i ( e ) ≥ 2 X j =1 n X i =1 h I ( S j , W j , X i − 1 ; X i ) − I ( S j , W j , X i − 1 ; Y j,i ) − n i ( f ) = 2 X j =1 n X i =1 h I ( U j,i ; X i ) − I ( U j,i ; Y j,i ) − n i (98) where ( a ) follo ws by (26) and from the Markov chain W 1 − X n − W 2 , ( b ) follows because I ( W 1 ; Y n 1 ) = I ( W 1 ; e X n 2 ) due to (23), ( c ) follows from the Markov chain W 1 − e X n 2 − W 2 , ( d ) follows by (95), ( e ) follows because the channel and source are memoryless and from the Marko v chain in (97), and ( f ) follows from the definition of U j,i . Pr oof for (33) : Observ e for the multi-enrollment models that n ( s R ` + δ n ) ( a ) ≤ H ( W 1 ) + H ( W 2 ) − H ( W 1 | X n ) − H ( W 2 | X n ) ( b ) ≤ 2 X j =1 h n s R w ,j + H ( S j , W j | e X n j ) − H ( S j , W j | X n ) + n n i G ¨ UNL ¨ U: MUL TI-ENTITY AND MUL TI-ENR OLLMENT KEY AGREEMENT WITH CORRELA TED NOISE 11 ( c ) = 2 X j =1 h n s R w ,j + n X i =1 I ( S j , W j , X i − 1 ; X i ) − n X i =1 I ( S j , W j , e X i − 1 j ; e X j,i ) + n n i ( d ) ≤ 2 X j =1 h n s R w ,j + n X i =1 I ( S j , W j , X i − 1 ; X i ) − n X i =1 I ( S j , W j , X i − 1 ; e X j,i ) + n n i ( e ) ≤ 2 X j =1 h n s R w ,j + n X i =1 ( I ( U j,i ; X i ) − I ( U j,i ; e X j,i )) + n n i (99) where ( a ) follo ws by (26) and from the Markov chain W 1 − X n − W 2 , ( b ) follows by (95) and from the Markov chain S j − ( W j , X n ) − Y n for j = 1 , 2 , ( c ) follows because the channel and source are memoryless, ( d ) follows from the Marko v chain X i − 1 − ( W j , S j , e X i − 1 j ) − e X j,i , j = 1 , 2 , ∀ i ∈ [1 : n ] (100) and ( e ) follo ws from the definition of U j,i . Pr oof for (34) : Observe for the multi-enrollment GS model for j = 1 , 2 that n ( s R w ,j + δ n ) ( a ) ≥ H ( W j | Y n j ) + I ( W j ; Y n j ) ( b ) ≥ H ( S j , W j , Y n j ) − H ( Y n j ) − H ( S j | W j , Y n j ) − H ( S j , W j | e X n j ) + I ( W j ; Y n j ) ( c ) ≥ I ( S j , W j ; e X n j ) − I ( S j , W j ; Y n j ) − n n ( d ) = n X i =1 [ I ( S j , W j , e X i − 1 j ; e X j,i ) − I ( S j , W j , Y i − 1 j ; Y j,i ) − n n ] ( e ) ≥ n X i =1 [ I ( S j , W j , X i − 1 ; e X j,i ) − I ( S j , W j , X i − 1 ; Y j,i ) − n n ] ( f ) = n X i =1 [ I ( U j,i ; e X j,i ) − I ( U j,i ; Y j,i ) − n n ] (101) where ( a ) follo ws by (28), ( b ) follo ws from the encoding steps, ( c ) follows by (95), ( d ) follo ws because the source and channel are memoryless, ( e ) follo ws from the data-processing inequality applied to the Markov chains in (97) and (100), and ( f ) follows from the definition of U j,i . Pr oof for (37) : Observe for the multi-enrollment CS model for j = 1 , 2 that n ( s R w ,j + δ n ) ( a ) ≥ I ( S j , W j ; e X n j ) − H ( S j | W j ) + H ( S j , W j | e X n j ) ( b ) ≥ I ( S j , W j ; e X n j ) + I ( S j ; W j ) ( c ) ≥ n X i =1 I ( S j , W j , e X i − 1 j ; e X j,i ) ( d ) ≥ n X i =1 I ( S j , W j , X i − 1 ; e X j,i ) ( e ) = n X i =1 I ( U j,i ; e X j,i ) (102) where ( a ) follows by (28), ( b ) follows because e X n is indepen- dent of S j and from the encoding step, ( c ) follows because the source and channel are memoryless, ( d ) follows by applying the data-processing inequality to the Marko v chain in (100), and ( e ) follo ws from the definition of U j,i . Pr oof for (35) : W e have for the multi-enrollment GS model for j = 1 , 2 that n ( s R s ,j + s R w ,j ) ( a ) = H ( S j , W j ) + I ( S j ; W j ) + nδ n ( b ) ≤ n X i =1 H ( S j , W j , X i − 1 ) + δ n n + δ n ( c ) = n X i =1 H ( U j,i ) + δ n n + δ n (103) where ( a ) follows by (25), ( b ) follo ws by (27), and ( c ) follo ws from the definition of U j,i . Pr oof for (38) : Similarly , we hav e for the multi-enrollment CS model for j = 1 , 2 that n s R w ,j ≤ n X i =1 H ( S j , W j , X i − 1 ) ( a ) = n X i =1 H ( U j,i ) (104) where ( a ) follo ws from the definition of U j,i . Pr oof for (36) : W e obtain for the multi-enrollment GS model for j = 1 , 2 and j 0 as defined in (30) that n ( s R s ,j + s R w ,j + s R w ,j 0 ) ( a ) = H ( S j , W j , W j 0 ) + I ( S j ; W j , W j 0 ) + I ( W j ; W j 0 ) + nδ n ( b ) ≤ n X i =1 h H ( S j , W j , W j 0 , S j 0 , X i − 1 ) + 2 δ n n + δ n i (105) ( c ) = n X i =1 h H ( U j,i , U j 0 ,i ) + 2 δ n n + δ n i (106) where ( a ) follows by (25), ( b ) follo ws by (27) and (29), and ( c ) follo ws from the definitions of U j,i and U j 0 ,i . Pr oof for (39) : W e hav e for the multi-enrollment CS model for j = 1 , 2 and j 0 as defined in (30) that n ( s R w ,j + s R w ,j 0 ) ≤ n X i =1 H ( W j , W j 0 , S j , S j 0 , X i − 1 ) + I ( W j ; W j 0 ) + n s R s ,j 0 ( a ) ≤ n X i =1 h H ( W j , W j 0 , S j , S j 0 , X i − 1 ) + δ n n + s R s ,j 0 i (107) ( b ) = n X i =1 h H ( U j,i , U j 0 ,i ) + δ n n + s R s ,j 0 i (108) where ( a ) follo ws by (29) and ( b ) follows from the definitions of U j,i and U j 0 ,i . Remark 4. (105) and (107) are the only places we use the constraint in (29) and it does not seem straightforw ard to obtain the inequalities in (105) and (107) without (29). Introduce a uniformly distributed time-sharing random vari- able Q ∼ Unif [1 : n ] independent of other random variables. Define X = X Q , e X j = e X j,Q , Y j = Y j,Q , and U j = ( U j,Q ,Q ) so that U j − e X j − X − Y j form a Markov chain for j = 1 , 2 . The outer bound for the GS model follows by using the introduced random variables in (96), (98), (99), (101), (103), and (106), 12 IEEE TRANSA CTIONS ON INFORMA TION FORENSICS AND SECURITY and letting δ n → 0 . Similarly , the outer bound for the CS model follo ws by using the introduced random v ariables in (96), (98), (99), (102), (104), and (108), and letting δ n → 0 . V I I . C O N C L U S I O N W e deriv ed inner bounds for the multi-entity ke y-leakage- storage regions for GS and CS models with strong secrecy , a hidden identifier source, and correlated noise components at the encoder and decoder measurements that are modeled as BCs. The inner bounds are v alid for any finite number of entities that use the same hidden source to agree on a secret ke y . W e ar gued that the mutual key independence constraint we impose makes the proposed multi-entity ke y agreement problem a proper multi-user extension of the classic single-enrollment key agreement problem, unlike the multi- enrollment key agreement problem considered in the literature. A set of degraded and less-noisy BCs was shown to provide strong priv ac y without a need for a common randomness. W e also established inner and outer bounds for the key-lekage- storage regions for a two-enrollment model with measurement channels that are valid for SRAM and R O PUFs. Inner and outer bounds were shown to differ only in the Markov chains imposed and they match if the storage and pri v acy-leakage rate constraints are remov ed. T wo examples illustrated that depending on the constraints of the practical scenario, a single or multiple enrollments might perform better in terms of the secret-key vs. priv acy-leakage rate ratio. In future work, we will find a set of symmetric probability distributions for which the strong helper data independence constraint in the two- enrollment model can be eliminated. A C K N O W L E D G M E N T O. G ¨ unl ¨ u thanks Rafael F . Schaefer for fruitful discussions. R E F E R E N C E S [1] P . Campisi, Security and Privacy in Biometrics . London, U.K.: Springer-Verlag, 2013. [2] B. Gassend, “Physical random functions, ” Master’ s thesis, M.I.T ., Cam- bridge, MA, Jan. 2003. [3] O. G ¨ unl ¨ u, “Ke y agreement with physical unclonable functions and biometric identifiers, ” Ph.D. dissertation, TU Munich, Germany , Nov . 2018, published by Dr. Hut V erlag in Feb. 2019. [4] A. D. W yner , “The wire-tap channel, ” Bell Labs T ech. J. , vol. 54, no. 8, pp. 1355–1387, Oct. 1975. [5] P . W . Cuff, H. H. Permuter, and T . M. Cover , “Coordination capacity , ” IEEE T r ans. Inf . Theory , v ol. 56, no. 9, pp. 4181–4206, Sep. 2010. [6] G. Cervia, L. Luzzi, M. L. T reust, and M. R. Bloch, “Strong coordi- nation of signals and actions over noisy channels with two-sided state information, ” Mar . 2018, [Online]. A v ailable: arxiv .org/abs/1801.10543. [7] R. Ahlswede and I. Csisz ´ ar , “Common randomness in information theory and cryptography - Part I: Secret sharing, ” IEEE T r ans. Inf. Theory , vol. 39, no. 4, pp. 1121–1132, July 1993. [8] U. M. Maurer , “Secret ke y agreement by public discussion from common information, ” IEEE T rans. Inf. Theory , vol. 39, no. 3, pp. 2733–2742, May 1993. [9] T . Ignatenko and F . M. J. W illems, “Biometric systems: Pri vac y and secrecy aspects, ” IEEE Tr ans. Inf . F or ensics Security , vol. 4, no. 4, pp. 956–973, Dec. 2009. [10] L. Lai, S.-W . Ho, and H. V . Poor, “Priv acy-security trade-offs in biometric security systems - Part I: Single use case, ” IEEE T r ans. Inf. F or ensics Security , vol. 6, no. 1, pp. 122–139, Mar . 2011. [11] I. Csisz ´ ar and P . Narayan, “Common randomness and secret key generation with a helper, ” IEEE T rans. Inf. Theory , vol. 46, no. 2, pp. 344–366, Mar . 2000. [12] O. G ¨ unl ¨ u and G. Kramer, “Priv acy , secrecy , and storage with multiple noisy measurements of identifiers, ” IEEE T r ans. Inf. F or ensics Security , vol. 13, no. 11, pp. 2872–2883, Nov . 2018. [13] L. Lai, S. Ho, and H. V . Poor , “Priv acy–security trade-of fs in biometric security systems - Part II: Multiple use case, ” IEEE Tr ans. Inf. F orensics Security , vol. 6, no. 1, pp. 140–151, Mar . 2011. [14] L. Kusters and F . M. J. Willems, “Secret-key capacity regions for multiple enrollments with an SRAM-PUF, ” IEEE T r ans. Inf. F or ensics Security , vol. 14, no. 9, pp. 2276–2287, Sep. 2019. [15] A. Juels and M. W attenberg, “ A fuzzy commitment scheme, ” in ACM Conf. Comp. Commun. Security , New Y ork, NY , Nov . 1999, pp. 28–36. [16] L. Kusters, T . Ignatenko, F . M. J. Willems, R. Maes, E. van der Sluis, and G. Selimis, “Security of helper data schemes for SRAM-PUF in multiple enrollment scenarios, ” in IEEE Int. Symp. Inf. Theory , Aachen, Germany , June 2017, pp. 1803–1807. [17] I. Land, S. Huettinger, P . A. Hoeher, and J. B. Huber , “Bounds on information combining, ” IEEE Tr ans. Inf. Theory , vol. 51, no. 2, pp. 612–619, Feb . 2005. [18] L. Kusters, O. G ¨ unl ¨ u, and F . M. W illems, “Zero secrecy leakage for multiple enrollments of physical unclonable functions, ” in Symp. Inf. Theory Sign. Pr ocess. Benelux , T wente, The Netherlands, May-June 2018, pp. 119–127. [19] O. G ¨ unl ¨ u, O. Iscan, V . Sidorenko, and G. Kramer, “Code constructions for physical unclonable functions and biometric secrecy systems, ” IEEE T r ans. Inf. F or ensics Security , vol. 14, no. 11, pp. 2848–2858, Nov . 2019. [20] Y . Dodis, R. Ostrovsk y , L. Reyzin, and A. Smith, “Fuzzy extractors: How to generate strong keys from biometrics and other noisy data, ” SIAM J . Comput. , v ol. 38, no. 1, pp. 97–139, Jan. 2008. [21] D. Merli, F . Stumpf, and C. Eckert, “Improving the quality of ring oscillator PUFs on FPGAs, ” in ACM W orkshop Embedded Sys. Security , New Y ork, NY , Oct. 2010, pp. 9:1–9:9. [22] O. G ¨ unl ¨ u, R. F . Schaefer , and G. Kramer , “Priv ate authentication with physical identifiers through broadcast channel measurements, ” in IEEE Inf. Theory W orkshop , V isby , Sweden, Aug. 2019, pp. 1–5. [23] T . M. Cover and J. A. Thomas, Elements of Information Theory , 2nd ed. Hoboken, NJ: John Wiley & Sons, 2012. [24] R. A. Chou, M. R. Bloch, and E. Abbe, “Polar coding for secret-key generation, ” IEEE T rans. Inf. Theory , vol. 61, no. 11, pp. 6213–6237, Nov . 2015. [25] O. G ¨ unl ¨ u, T . Kernetzk y , O. ˙ Is ¸can, V . Sidorenko, G. Kramer , and R. F . Schaefer , “Secure and reliable key agreement with physical unclonable functions, ” Entropy , vol. 20, no. 5, May 2018. [26] J. W ayman, A. Jain, D. Maltoni, and D. M. (Eds), Biometric Systems: T echnology , Design and P erformance Evaluation . London, U.K.: Springer-Verlag, 2005. [27] R. Pappu, “Physical one-way functions, ” Ph.D. dissertation, M.I.T ., Cambridge, MA, Oct. 2001. [28] O. G ¨ unl ¨ u, K. Kittichokechai, R. F . Schaefer, and G. Caire, “Controllable identifier measurements for private authentication with secret keys, ” IEEE T rans. Inf . F orensics Security , vol. 13, no. 8, pp. 1945–1959, Aug. 2018. [29] C. Nair , “Capacity re gions of tw o ne w classes of two-receiver broadcast channels, ” IEEE T r ans. Inf. Theory , vol. 56, no. 9, pp. 4207–4214, Sep. 2010. [30] R. Maes, P . T uyls, and I. V erbauwhede, “ A soft decision helper data algorithm for SRAM PUFs, ” in IEEE Int. Symp. Inf. Theory , Seoul, South K orea, June 2009, pp. 2101–2105. [31] J. Hagenauer , “Lecture Notes in Digital Communications 1, ” G. Kramer and O. G ¨ unl ¨ u, Eds. Singapore: TU Munich Asia, Feb . 2019. [32] M. H. Y assaee, M. R. Aref, and A. Gohari, “ Achievability proof via output statistics of random binning, ” IEEE Tr ans. Inf. Theory , vol. 60, no. 11, pp. 6760–6786, Nov . 2014. [33] M. Nafea and A. Y ener, “ A new wiretap channel model and its strong secrecy capacity , ” IEEE Tr ans. Inf. Theory , vol. 64, no. 3, pp. 2077– 2092, Mar . 2018. [34] M. Bloch, Lectur e Notes in Information-Theoretic Security . Atlanta, GA: Georgia Inst. T echnol., July 2018. [35] D. Slepian and J. W olf, “Noiseless coding of correlated information sources, ” IEEE Tr ans. Inf. Theory , vol. 19, no. 4, pp. 471–480, July 1973. [36] A. Schrijver , Theory of Linear and Inte ger Pr o gramming . Chichester , England: John W ile y & Sons, June 1998. [37] I. B. Gattegno, Z. Goldfeld, and H. H. Permuter, “Fourier-Motzkin elimination software for information theoretic inequalities, ” 2016. [38] M. Bloch and J. Barros, Physical-layer Security . Cambridge, U.K.: Cambridge Uni. Press, 2011. G ¨ UNL ¨ U: MUL TI-ENTITY AND MUL TI-ENR OLLMENT KEY AGREEMENT WITH CORRELA TED NOISE 13 Onur G ¨ unl ¨ u (S’10–M’18) receiv ed the B.Sc. de gree (with high distinction) in Electrical and Electronics Engineering from the Bilkent Univ ersity , T urkey in 2011; M.Sc. (with high distinction) and Dr .- Ing. (Ph.D. equiv alent) degrees in Communication Engineering both from the T echnical University of Munich (TUM), German y in October 2013 and November 2018, respectively . He was a W orking Student in the Communication Systems division of Intel Mobile Communications (IMC) during No vem- ber 2012 - March 2013. He worked as a Research and T eaching Assistant at TUM between February 2014 - May 2019. He was a V isiting Researcher at the Information and Communication Theory (ICT) Lab of TU Eindhoven, The Netherlands during February 2018 - March 2018. He has been a Research Associate and Dozent at TU Berlin, Germany since June 2019 and a Brain City Berlin Ambassador since June 2020. His research interests include information theoretic privac y and security , coding theory , statistical signal processing for biometrics and physical unclonable functions (PUFs), federated learning (FL) with differential privac y (DP) guarantees, and doubly-exponential secure identification. Among his publications is the recent book Ke y Agreement with Physical Unclonable Functions and Biometric Identifiers (Dr . Hut V erlag, 2019). He is currently a Guest Editor of the I E EE J O U RN A L O N S E L E CT E D A R E A S I N I N F O RM ATI O N T H E O RY and is a Reviewer Board Member of the M D P I E N TR OP Y , C O M P UT E R S , and I N FO R M A TI O N journals.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment