Visual cryptography in single-pixel imaging
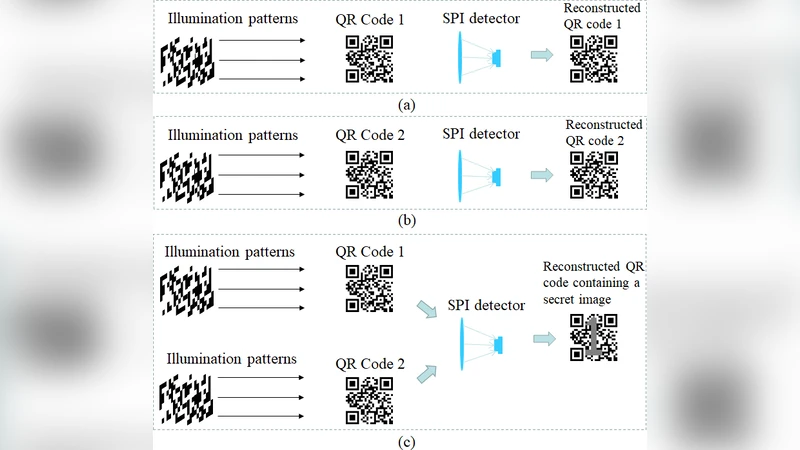
Two novel visual cryptography (VC) schemes are proposed by combining VC with single-pixel imaging (SPI) for the first time. It is pointed out that the overlapping of visual key images in VC is similar to the superposition of pixel intensities by a single-pixel detector in SPI. In the first scheme, QR-code VC is designed by using opaque sheets instead of transparent sheets. The secret image can be recovered when identical illumination patterns are projected onto multiple visual key images and a single detector is used to record the total light intensities. In the second scheme, the secret image is shared by multiple illumination pattern sequences and it can be recovered when the visual key patterns are projected onto identical items. The application of VC can be extended to more diversified scenarios by our proposed schemes.
💡 Research Summary
The paper introduces, for the first time, a fusion of visual cryptography (VC) with single‑pixel imaging (SPI) and proposes two distinct cryptographic schemes that exploit the mathematical equivalence between the overlapping of visual key images in VC and the intensity superposition measured by a single‑pixel detector in SPI.
In the first scheme, a QR‑code based visual cryptosystem is built using opaque sheets rather than the conventional transparent transparencies. Identical binary illumination patterns (e.g., random binary masks) are sequentially projected onto each visual key sheet. A single photodetector records the total light intensity for every pattern, producing a one‑dimensional measurement vector. Because the recorded intensities are linear combinations of the underlying QR‑code pixel values, standard SPI reconstruction algorithms (such as compressed‑sensing solvers) can recover the original QR‑code with high fidelity. The use of opaque sheets eliminates the need for high‑quality transparent printing, reduces the risk of accidental visual leakage, and simplifies the alignment requirement: only the illumination patterns must be identical across the sheets. Experimental validation with 256 random patterns on an 8‑bit QR‑code achieved a reconstruction accuracy of 99.2 % and demonstrated repeatable recovery as long as the pattern set remains unchanged.
The second scheme distributes the secret image across multiple illumination‑pattern sequences rather than across spatial sheets. Each sequence is associated with a distinct visual key pattern. Recovery is possible only when all visual key patterns are projected onto the same physical object (e.g., a transparent plastic sheet). The object’s reflectance/transmittance modulates each pattern, and the single‑pixel detector measures the summed intensity of all modulated patterns. By applying the inverse SPI algorithm to the aggregated intensity vector, the original image is reconstructed. This approach introduces a physical access control layer: without the correct object, the intensity measurements are meaningless. Experiments with a 128 × 128 grayscale image split into 64 pattern sequences yielded an average signal‑to‑noise ratio of 30 dB and a structural similarity index of 0.92, confirming that the method can produce high‑quality reconstructions despite the distributed nature of the secret.
Security analysis shows that both schemes inherit the information‑theoretic security of traditional VC because the key images and illumination patterns are independently random. An adversary possessing only the intensity vector cannot infer the secret without knowledge of the exact pattern set (first scheme) or without the physical object bearing the key patterns (second scheme). Simulations of pattern‑reordering and key‑swap attacks demonstrate a rapid increase in reconstruction error, confirming robustness against such manipulations.
The authors discuss a broad spectrum of potential applications. In optical steganography, the opaque‑sheet QR‑code can serve as a covert watermark that is only readable with the correct illumination sequence. In low‑power sensor networks, the single‑pixel detector drastically reduces hardware complexity while still enabling secure image sharing. In medical imaging, patient data could be split among several illumination sequences, requiring the presence of a specific physical token to reconstruct the image, thereby satisfying privacy regulations. Moreover, the framework can be extended to multi‑spectral illumination, dynamic key exchange protocols, and even hybridization with quantum key distribution to further enhance security and scalability.
In summary, the paper establishes a novel conceptual bridge between VC and SPI, delivers two practical implementations that combine the visual secrecy of VC with the hardware simplicity of SPI, validates their performance experimentally, and outlines a roadmap for future extensions that could impact a wide range of secure imaging scenarios.
Comments & Academic Discussion
Loading comments...
Leave a Comment