Implementation of encryption on telemedicine
In the era of technology, data security is one of the most important things that both individuals and companies need. Information plays a huge role in our everyday life and keeping it safe should be our number one priority. Nowadays most of the information is transferred via the internet. One of the ways to use it is telemedicine. With the help of telemedicine, people can have an appointment at the doctors without losing their time or money. All of the information about one’s health is transferred through the internet but is it that safe? What techniques are used to provide the safety of our confidential information? To guarantee that the information is not changed or that in case it will be stolen no one can still have access to it.
💡 Research Summary
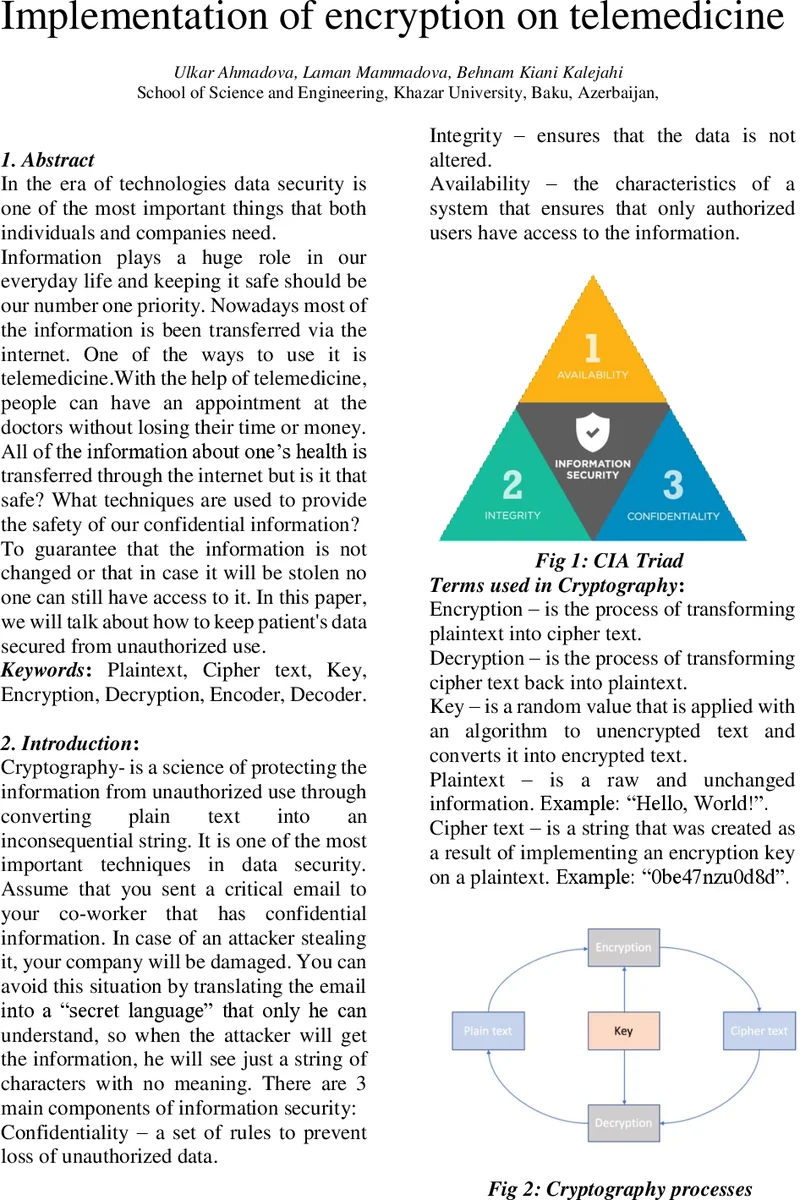
The paper addresses the critical need for protecting patient data in telemedicine applications, where health information is transmitted over the Internet and must remain confidential, authentic, and tamper‑free. It begins with a brief overview of basic cryptographic concepts—confidentiality, integrity, availability, encryption, decryption, keys, plaintext, and ciphertext—setting the stage for a more detailed discussion of symmetric and asymmetric techniques.
In the symmetric section, the authors describe stream versus block ciphers and focus on three historically important block ciphers: DES, 3DES, and AES. DES, introduced in the 1970s, uses a 56‑bit key and 16 rounds on 64‑bit blocks but is now considered insecure due to brute‑force feasibility. 3DES extends DES by applying three independent keys, effectively increasing the key length to 168 bits and the round count to 48, yet it suffers from high computational overhead. AES, standardized in 2001, operates on 128‑bit blocks with key sizes of 128, 192, or 256 bits and 10, 12, or 14 rounds respectively. The paper correctly notes that AES is efficient in both hardware and software, but it only briefly mentions side‑channel attacks without discussing mitigation strategies.
The asymmetric portion introduces RSA, DSA, and ElGamal, emphasizing RSA’s role in SSL/TLS, PGP, IPSEC, SSH, and electronic payments. The authors outline RSA key generation (selection of two large primes p and q, computation of n = p·q, φ(n), public exponent e, and private exponent d) and note that guessing d is practically impossible with adequately sized keys. They also mention a “cycle attack,” which is not a standard term in cryptography and appears to be a misunderstanding. DSA is presented as a digital‑signature‑focused algorithm, and several signature schemes (batch, forward‑secure, proxy, blind) are listed, though their operational details are omitted.
The core of the paper applies these concepts to a telemedicine scenario. Patient devices store biomedical measurements locally; when a consultation is needed, the data are sent to a remote clinician via the Internet. Because the system must handle many records and provide rapid feedback, the authors argue that symmetric encryption is preferable for bulk data due to its speed. They acknowledge the key‑distribution problem: a single shared key per patient‑doctor pair means that compromise of that key exposes all communications for that relationship. To address authenticity and integrity, they propose adding a digital signature: the encrypted payload is hashed, signed with the sender’s private key, and the signature is transmitted alongside the ciphertext. The receiver verifies the signature using the sender’s public key, ensuring that the data have not been altered and confirming the sender’s identity.
The paper concludes that a hybrid approach—fast symmetric encryption for data confidentiality combined with asymmetric digital signatures for authentication and integrity—offers the best balance for telemedicine. While the high‑level idea is sound, the manuscript lacks concrete implementation details such as key‑exchange protocols (e.g., Diffie‑Hellman or TLS), certificate management, performance benchmarks, and defenses against side‑channel or future quantum attacks. Consequently, readers are left with a conceptual framework but must fill in many practical gaps before deploying a secure telemedicine system.
Comments & Academic Discussion
Loading comments...
Leave a Comment