Gelato: Feedback-driven and Guided Security Analysis of Client-side Web Applications
💡 Research Summary
The paper addresses the growing difficulty of analyzing modern client‑side web applications that heavily rely on complex JavaScript frameworks such as React, Angular, and Vue. Existing dynamic analysis tools either focus on improving crawling coverage or on taint‑based vulnerability detection, but none combine both aspects in a way that scales to today’s single‑page applications (SPAs). To fill this gap, the authors introduce Gelato, a feedback‑driven and guided security analysis platform that tightly couples a state‑aware crawler with a lightweight dynamic taint analysis.
Gelato’s architecture consists of four main components: (1) a client‑state‑aware and server‑state‑aware crawler, (2) a call‑graph‑based guidance engine, (3) a staged taint inference engine, and (4) an input‑generation module that can bypass validation guards. The crawler explores the UI by interacting with DOM elements, generating both event sequences and data inputs. Unlike prior crawlers (Crawljax, j̈Ak, FEEDEX, WATeg), Gelato does not aim merely for generic coverage; it uses static call‑graph information refined at runtime to compute a “distance” from the current execution point to security‑sensitive sinks (e.g., innerHTML, document.write). This distance drives a prioritization scheme that steers the crawler toward locations where a security analysis is most valuable.
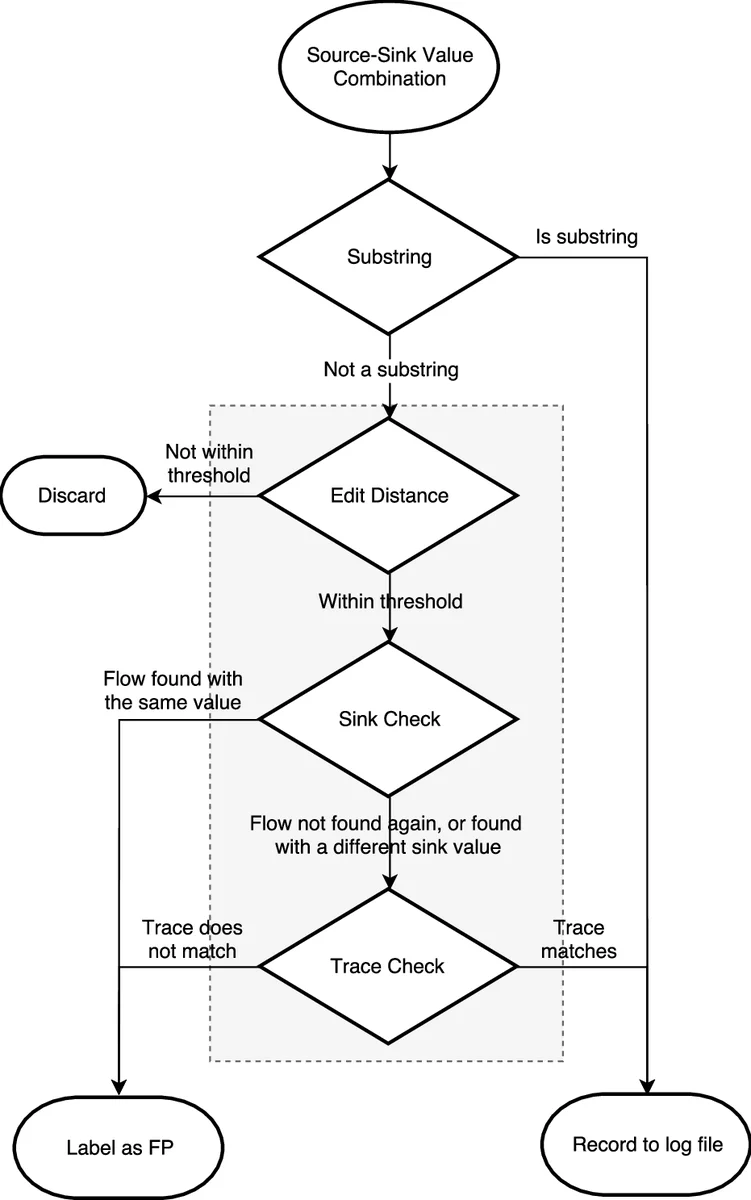
The staged taint inference analysis is the second novelty. Instead of instrumenting the JavaScript engine (which hurts portability) or performing heavyweight source‑code rewriting, Gelato injects a minimal set of instrumentation statements at the source level. The first stage quickly identifies direct flows from user‑controlled inputs to DOM sinks. The second stage follows asynchronous callbacks, promises, and event bubbling to capture indirect flows that static analysis typically misses. By combining dynamic trace collection with on‑the‑fly refinement of the call graph, Gelato reduces false positives and improves recall compared with state‑of‑the‑art dynamic taint tools such as FlowDroid‑JS, JSAI, and others.
To evaluate Gelato, the authors selected 30 real‑world SPAs from the Alexa Top 1 000 list and compared Gelato against a suite of existing tools (Crawljax, j̈Ak, FEEDEX, WATeg, and several dynamic taint systems). The results show that Gelato discovers on average 22 % more DOM‑based XSS and reflected XSS vulnerabilities, while requiring only a modest 1.3× increase in total analysis time. Importantly, Gelato uncovers vulnerabilities located deep inside the application logic—such as hidden REST endpoints and dynamically generated event handlers—that other tools miss because they either stop after the first page or cannot reach the required state due to exponential state‑space explosion.
The paper also discusses several practical contributions: (i) a feedback loop that continuously refines the static call graph using runtime information, thereby mitigating the “search‑space explosion” problem; (ii) a lightweight input generator that leverages taint inference to produce values capable of bypassing string‑based validation guards; (iii) support for modern libraries without the need for manually crafted models, thanks to the dynamic call‑graph approach; and (iv) a design that works with unmodified browsers, facilitating adoption in industry pipelines.
In summary, Gelato represents a significant step forward in client‑side security analysis. By unifying guided crawling with staged dynamic taint inference, it achieves higher vulnerability detection rates on complex JavaScript applications while maintaining reasonable performance and portability. The authors suggest that the same feedback‑driven paradigm could be extended to other client‑side security concerns such as CSP bypasses, memory‑leak detection, or even automated generation of security test suites for emerging web technologies.
Comments & Academic Discussion
Loading comments...
Leave a Comment