Dynamic Resilient Network Games with Applications to Multi-Agent Consensus
A cyber security problem in a networked system formulated as a resilient graph problem based on a game-theoretic approach is considered. The connectivity of the underlying graph of the network system is reduced by an attacker who removes some of the edges whereas the defender attempts to recover them. Both players are subject to energy constraints so that their actions are restricted and cannot be performed continuously. For this two-stage game, which is played repeatedly over time, we characterize the optimal strategies for the attacker and the defender in terms of edge connectivity and the number of connected components of the graph. The resilient graph game is then applied to a multi-agent consensus problem. We study how the attacks and the recovery on the edges affect the consensus process. Finally, we also provide numerical simulation to illustrate the results.
💡 Research Summary
The paper addresses a cyber‑security problem in networked multi‑agent systems by formulating a dynamic, energy‑constrained two‑player game between an attacker and a defender. The underlying communication network is modeled as an undirected graph G = (V,E). The attacker can jam (remove) a subset of edges, while the defender can recover (reinstate) some of the jammed edges. Both players have limited energy budgets, which restrict the total duration and the number of edges they can act upon in each round.
A novel metric, called generalized edge connectivity bλ(G′), is introduced to capture the state of the graph in a unified way: for a connected graph it equals the classical edge‑connectivity λ(G′) (the size of a minimum cut), and for a disconnected graph it equals the negative of the minimum number of edges required to reconnect the graph (−eλ(G′)). This metric allows the authors to define the attacker’s utility as the negative of the accumulated bλ over the attack interval plus a linear energy cost β_A m_A δ_A, and the defender’s utility as the accumulated bλ (positive) over the same horizon minus a similar recovery cost β_D m_D δ_D.
The game proceeds in repeated two‑stage intervals. After a fixed dwell time γ_A, the attacker initiates an attack at τ_A, selecting m_A edges and maintaining the jam for a duration δ_A. After another dwell time γ_D, the defender may start a recovery at τ_D, selecting up to m_D ≤ m_A edges and maintaining recovery for δ_D. The interval ends when the attacker stops jamming (or when no attack occurs, in which case the interval lasts γ_A + γ_D). Energy constraints are modeled by an inequality that limits cumulative energy consumption to an initial reserve κ_p plus a linear recharge term ρ_p t.
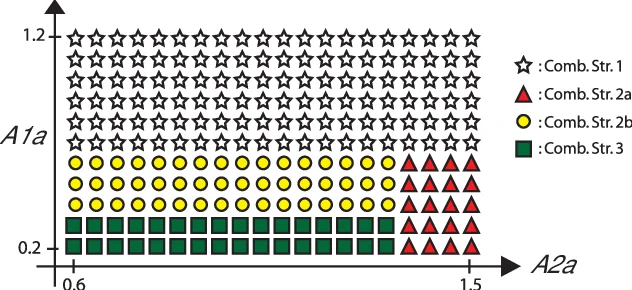
The core analytical contribution is the derivation of subgame‑perfect equilibria (SPE) for each stage using backward induction. First, given a fixed attack (m_A, δ_A), the defender’s optimal recovery (m_D^, δ_D^) is obtained by maximizing bλ while accounting for the recovery cost. Then, anticipating this best response, the attacker chooses (m_A^, δ_A^) to minimize bλ (i.e., to fragment the graph as much as possible) subject to its own energy budget. The optimal attack corresponds to solving a minimum‑cut problem on the original graph, while the optimal recovery corresponds to a minimum‑addition (k‑cut) problem on the attacked graph. The authors encapsulate the outcomes in a matrix bλ_G of size (|E|+1) × (|E|+1), where entry (i,j) gives the generalized connectivity after i−1 attacks and j−1 recoveries. This matrix is generally non‑Toeplitz, reflecting the non‑linear relationship between the number of edges acted upon and the resulting connectivity.
To demonstrate practical relevance, the game framework is applied to a consensus problem. Agents follow a standard Laplacian‑based consensus protocol; when the graph remains connected, the states converge exponentially to a common value. If the attacker disconnects the graph, each connected component reaches its own consensus, and the overall convergence time T_c is prolonged. By expressing T_c as a function of bλ, the energy parameters (β_A, β_D, κ_p, ρ_p), and the optimal strategies, the authors quantify how aggressive attacks increase T_c and how timely recovery can mitigate this effect.
Numerical simulations on random 10‑node graphs and on a 4‑node complete graph validate the theoretical predictions. Varying β_A and β_D shows that low recovery cost and high recharge rate (ρ_D) dramatically improve resilience, whereas high attacker energy (κ_A) can overwhelm the defender if recovery resources are limited. The simulations also illustrate that the optimal set of edges to attack or recover is not simply the most numerous ones; rather, it depends on the graph’s cut structure, confirming the importance of the bλ‑based analysis.
In summary, the paper makes three key contributions: (1) a unified utility formulation based on generalized edge connectivity that captures both fragmentation and reconnection effects; (2) a rigorous SPE analysis for an energy‑constrained attacker‑defender game, revealing that optimal actions solve classic graph‑cut problems; and (3) an application to multi‑agent consensus that links game outcomes to convergence performance. The framework offers actionable insights for designing resilient network topologies and defense policies in cyber‑physical systems where energy resources are limited and attacks are strategic.
Comments & Academic Discussion
Loading comments...
Leave a Comment