Energy and Social Cost Minimization for Data Dissemination in Wireless Networks: Centralized and Decentralized Approaches
We study multi-hop data-dissemination in a wireless network from one source to multiple nodes where some of the nodes of the network act as re-transmitting nodes and help the source in data dissemination. In this network, we study two scenarios; i) t…
Authors: Mahdi Mousavi, Anja Klein
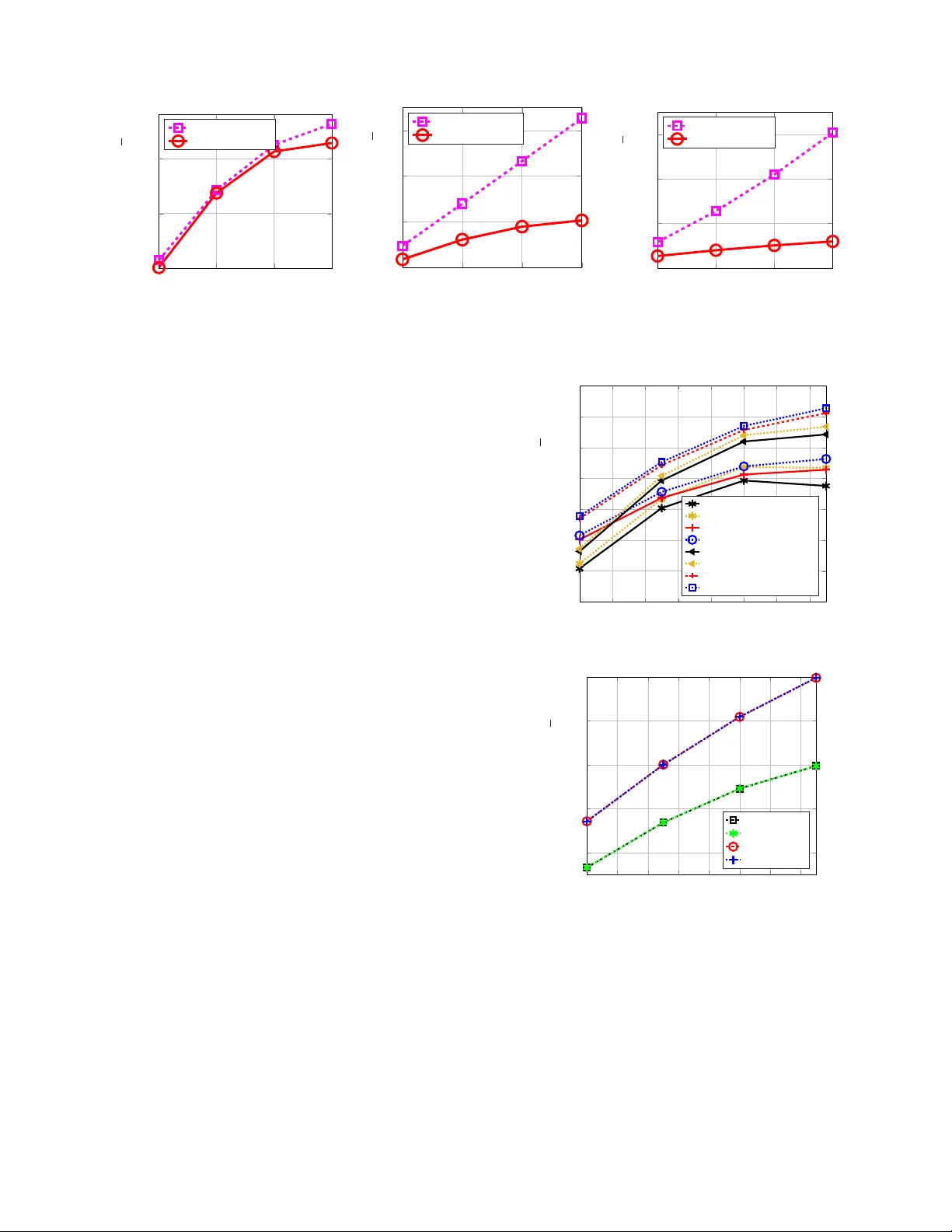
1 Ener gy and Social Cost Minimization for Data Dissemination in W ireless Networks: Centralized and Decentralized Approaches Mahdi Mousavi and Anja Klein, Member , IEEE Abstract —W e study multi-hop data-dissemination in a wir eless network from one source to multiple nodes where some of the nodes of the network act as r e-transmitting nodes and help the source in data dissemination. In this network, we study two scenarios; i) the transmitting nodes do not need an incentive for transmission and ii) they do need an incentive and are paid by their corresponding r eceiving nodes by virtual tokens. W e in vestigate two problems; P1) network power minimization for the first scenario and P2) social cost minimization for the second scenario, defined as the total cost paid by the nodes of the network for recei ving data. In this paper , to address P1 and P2, we propose centralized and decentralized approaches that determine which of the nodes of the network should act as transmitting nodes, find their transmit powers and their corresponding receiving nodes. For the sake of energy efficiency , in our model, we employ maximal-ratio combining (MRC) at the receivers so that a receiver can be ser ved by multiple transmitters. The proposed decentralized approach is based on a non-cooperative cost-sharing game (CSG). In our proposed game, every recei ving node chooses its respective transmitting nodes and consequently , a cost is assigned to it according to the power imposed on its chosen transmitting nodes. W e discuss how the network is formed in a decentralized way , find the action of the nodes in the game and show that, despite being decentralized, the proposed game con verges to a stable solution. T o find the centralized global optimum, which is a benchmark to our decentralized approach, we use a mixed-integer-liner -program (MILP). Simulation results show that our proposed decentralized approach outperforms the con ventional algorithms in terms of energy efficiency and social cost while it can address the need f or an incentive for collaboration. I . I N T RO D U C T I O N W ith the growing integration of communication networks, the Internet of things (IoT) and sensor networks under the umbrella of 5G, there is a need for increasing the capacity of future dense wireless networks [2]. Multi-hop communications is an efficient technique that can increase the capacity of wire- less networks and improve the reliability of communications. This paper specifically studies multi-hop broadcast where one source disseminates its data to multiple receivers. The data here could be a file, a software update, a video stream, etc. In this multi-hop netw ork, in order to decrease the transmit power required at the source for serving all the receiving nodes or to increase the coverage area, some of the nodes Copyright (c) 2015 IEEE. Personal use of this material is permitted. Howe ver , permission to use this material for any other purposes must be obtained from the IEEE by sending a request to pubs-permissions@ieee.org. The authors are with Communications Engineering Lab, T echnische Univ er- sit ¨ at Darmstadt, Germany . E-mail: { m.mousavi, a.klein } @nt.tu-darmstadt.de. Part of this paper has been published in [1]. may need to re-transmit the source’ s data. W e in vestigate two scenarios in this network. In the first scenario , we assume that the re-transmitting nodes are willing to collaborate with the source in data dissemination. Such a scenario may apply to IoT and sensor networks. In the first scenario, the objectiv e is to minimize the power required in the network for data dissemination. In the second scenario , ho wev er, we assume that the transmitting nodes require an incentiv e from their corresponding receiving nodes in exchange for transmitting the data to them. Such an assumption is vital for situations in which human users play an active role in data dissemination. Hence, in the second scenario, we aim at minimizing the social cost, defined as the summation of the costs that the nodes pay in exchange for recei ving the source’ s data [3]. The payment in this scenario is via virtual tokens, assumed to be available at the nodes. Due to the broadcast nature of the wireless medium, serving multiple nodes by multicast transmission is more energy- efficient than employing unicast transmission where ev ery receiving node requires a separate transmission. Multicast transmission can improve energy efficienc y and the capacity of the future generation of wireless networks, for instance, in machine-to machine-transmissions [4] and video streaming [5]. Since there may exist multiple transmitting nodes in our network, a recei ving node is able to recei ve multiple copies of the disseminated message. The recei ver in this case, instead of relying on one transmitter, can combine the receiv ed copies in order to decode the message. This helps in network energy-ef ficiency . Further , in a wireless device, two types of modules are inv olved in message transmission; passiv e and activ e modules. The passi ve modules such as digital-to-analog con verter , mixer , etc., require a fix po wer for proper operation [6]. W e refer to the po wer required for these modules as the circuitry po wer . In contrast, the power required at the activ e module, that is, the amplifier , is not fixed and varies depending on the channel gain between a transmitter and a receiver . This power is referred to as the radio link power . Despite the fact that the circuitry po wer is not negligible compared to the radio link po wer [6], it is often ignored for multi-hop communications and merely the radio link power is considered for optimization. F or the sake of energy-ef ficiency , in the present work, i) we consider multicast transmission so that multiple receiving nodes can be served by a common transmitter , ii) we let ev ery receiving node be served by multiple transmitting nodes and in this case, maximal ratio combining (MRC) is used to combine the 2 copies of the message receiv ed at a receiv er and iii) besides the radio link power , we take into account the circuitry power for multi-hop broadcast and show that our model leads to form a network that requires a lower power for data dissemination compared to the circuitry power -agnostic approaches. In order to design a decentralized mechanism, for both the first and the second scenarios, we use game theory . A non- cooperativ e cost sharing game (CSG) is proposed in which ev ery receiving node chooses one or more than one node among the nodes of the network as its respective transmitting node. In addition, the receiving node determines the transmit power of each of its chosen transmitting nodes such that the receiving node receives the message with a required minimum signal to noise ratio (SNR). As the consequence of the receiv er’ s decision, a cost is assigned to it. By using a CSG, in a multicast transmission where a transmitting node has multiple receiv ers, the cost paid to the transmitter is shared among its receivers by a so-called cost sharing scheme. The cost in the first scenario is an artificial cost, used as a tool by which a node merely finds the best transmitting nodes for itself in order to minimize the network power , whereas, in the second scenario, the cost of the node determines the cost, i.e., the number of tokens, that needs to be paid by the receiv er to each of its chosen transmitters. In both scenarios, the cost of a recei ving node is defined as a function of the total transmit power of its chosen transmitting nodes, including the radio link and the circuitry powers. Such a design is clear to be beneficial for the first scenario as we aim at network power minimization. The reason for taking such an approach for the second scenario is the importance of battery-life for the end-users. Studies show that energy consumption is one of the main concerns of the users when it comes to collaborativ e transmission [7]. Hence, in the second scenario, the transmitting nodes are also paid by their respectiv e recei ving nodes based on the po wer the y use for serving their receivers. The fundamental difference between the CSG proposed for each of the scenarios is the employed cost sharing scheme. In the first scenario, we use the marginal contribution (MC) cost sharing scheme as it is suitable for network power minimization [8]. In the second scenario where ev ery recei ver pays a price in exchange for recei ving the message, having a fair cost allocation is critical, especially when multiple receiving nodes are served by a common transmitting node via multicast. In this scenario, we employ the Shapley value (SV) which is known as the fairest cost allocation scheme [3]. Our proposed game is iterativ e where the nodes take their action one after another until the con vergence of the game to a point at which none of the nodes can reduce its cost given the actions of the others, called the Nash equilibrium (NE) point. The proposed game is sho wn to be a potential game for which the existence of at least one NE is guaranteed. In addition to the decentralized approach, we find the centralized optimum network configuration by a mixed-integer linear program (MILP). The optimum centralized solution serves as the benchmark for our proposed decentralized ap- proach. The centralized MILP formulation that we provide can be used for both scenarios by a minor change. The rest of the paper is or ganized as follows. Section II presents the related work and our main contributions. Section III describes the network model and formulates the problem. The proposed decentralized algorithm and details of the game are explained in Section IV. Section V provides the global optimum via an MILP . Performance analysis is presented in Section VI and finally , Section VII concludes the paper . I I . S T A T E O F T H E A RT A N D M A I N C O N T R I B U T I O N S Energy efficiency is one of the main challenges in multi- hop communications. Broadly speaking, the algorithms for multi-hop data dissemination are either centralized [9], [10] or decentralized [11], [12]. One of the well-known centralized heuristics for minimum-power multi-hop broadcast is proposed by the authors in [9], called the broadcast incremental po wer (BIP) [9]. The BIP is a greedy algorithm, starts from the source and adds the nodes one by one to the network. Being centralized is the main drawback of the BIP . The dependency of the centralized approaches on a central entity makes them difficult to implement and vulnerable against the failure of the connection between the nodes and the central entity . Hence, decentralized approaches are more suitable for such applications. While numerous centralized algorithms have been proposed by researchers for minimum-po wer multi-hop broadcast, there does not exist much work on decentralized approaches. Recently , decentralized solutions based on blind [11] and probabilistic [13] approaches are proposed where in the former case, the nodes are unaware of the presence of each other , and in the latter one, the reception of the data is not guaranteed. Since the transmissions by such approaches are unreliable, they cannot be used for streaming applications or payment-dependent transmissions. The authors of [10] propose a greedy centralized heuristic that exploits MRC in multi-hop broadcast and we refer to it as GreedyMRC. Like the BIP , it starts from the source and in ev ery iteration, it finds the node which is the best transmitter in the network in terms of the energy required for transmission of the message to others. Every transmitting node uses a separate time-slot for transmission and the nodes of the network recei ve the message o ver multiple time-slots and combine them via MRC until they accumulate the minimum SNR required for decoding the message. Although GreedyMRC exploits MRC, it is centralized, does not address the incentive issue and ignores the circuitry power . One of the main drawbacks of the existing algorithms for multi-hop broadcast is that they usually consider the nodes as passiv e and ready-to-collaborate entities. In practice, and more specifically in the future generation of wireless networks, the users play an active role in data dissemination and require a proper incentiv e for collaboration [14]. In the past decade, many works hav e in vestigated v arious wireless communica- tions and networking scenarios from a game-theoretic perspec- tiv e, ho wev er , fewer works ha ve studied incenti ve mechanisms. Incentiv e mechanisms can be employed for sharing an already- cached data [14] [15], in store-carry-forward applications [16], base-station-assisted device-to-de vice communications [17], distributed big data processing [18], and network utility 3 maximization [19]. For instance, in [19], the authors study network utility maximization in a network where a central entity has its o wn objectiv e. They propose mechanisms to motiv ate truthful reporting from the users to the central entity , about their personal preferences, so that proper incentiv es can be provided for the users to adopt the solution that the central entity prefers. In [17], an incenti ve mechanism is proposed within the frame work of an auction for selecting relay nodes in a cellular network who help the base station in transmitting data to other nodes. The social cost, which we aim at minimizing in the second scenario, can be seen as a network utility . In comparison to most of the existing works on network utility maximization, e.g., [17] and [19], our proposed algorithm is fully decentral- ized. It addresses the incenti ve design issue while at the same time it controls the network power . Moreover , to minimize the social cost, we not only employ the fairest cost allocation scheme, that is, the SV , but also we show that the con vergence of our designed decentralized algorithm with the SV is always guaranteed. One of the open issues of the existing works is that they do not address how the incentiv es need to be calculated for each individual user . A variety of rewarding schemes hav e been proposed by researchers, to be used as incentiv es, which rely either on a tit-for -tat strategy or reputation mechanism [20] or virtual currency [21]. W ith the growing popularity of cryptocurrencies in recent years, the latter strategy , that is, the use of virtual currency , is attracting significant attention [20], [22]. For instance, recently , the authors in [20] proposed a virtual currency to be used for computation offloading in ad- hoc networks in which the users offload their tasks to other remote entities. A virtual currency similar to the one proposed in [20] can be employed in our netw ork, howe ver , in the present work, our focus is on the network formation rather than a token or a virtual currency design. Due to the importance of user collaboration in the future generation of communication networks, it is vital to find a more comprehensiv e algorithm, capable of addressing both the energy efficiency and incenti ve issue for multi-hop broadcast. This, to the best of our knowledge, has not been addressed in the literature. Game theory , as a powerful mathematical tool, has been widely used for decentralized optimization of multi-user networks [23–25]. For instance, the authors of [23] use game theory in a content caching scenario where they aim to select important users and allocate content files to the storage of these selected users. In [25], we studied energy-minimization in multi-hop broadcast using a cost- sharing game. In [26], we sho wed that using MRC at the receiv ers improves the performance of the network, howe ver , the proposed algorithm for decision making at the nodes is a heuristic algorithm which does not necessarily find the optimum decision of the nodes. W e later showed in [1] that the decision-making problem at the nodes can be solved optimally by a linear program in contrast to the heuristic approach of [26]. In comparison to [1], in the present work, we improve our work in [1], where a decentralized approach merely for social cost minimization was proposed. Here, we propose a general framew ork for data dissemination which can be emplo yed for both network power and social cost minimization. W e will sho w that in both cases, the cost function of the nodes can be modeled by a piece-wise linear function and the decision-making problem at a node can be solved via an MILP . Moreover , in comparison to [1], the power model that we consider for the nodes in the present w ork includes the circuitry power for both transmission and reception which makes the network po wer model much more realistic. W e show that the circuitry power needed for signal reception, in particular , has a significant impact on the optimization problem. W e also, in the present work, discuss how the nodes can use a shared channel for transmission and exploit the MRC technique. Finally , to complete the work, we provide an MILP that finds the centralized global optimum configuration for both scenarios. Briefly , the main contributions of this paper are as follo ws: • For multi-hop broadcast we study network power min- imization when the transmitting nodes do not need an incentiv e for transmission and social cost minimization when having an incentiv e for the transmitting nodes is mandatory . When an incentiv e is required, we also address the fairness in cost allocation. • Our algorithm supports multicast transmission and fur- ther , exploits the MRC technique by which the receiving nodes can be served by multiple nodes, instead of relying on one transmitting node for data reception. • Besides the radio link power , our model considers the circuitry power of the nodes for both transmission and reception of the message. By such a model, the results obtained for the network po wer and the social cost are much more realistic compared to the existing works on multi-hop broadcast. • In comparison to [1] that provides a decentralized ap- proach for social cost minimization in multi-hop broad- cast, here, we propose both centralized and decentralized solutions which can be employed for minimization of the network power as well as the social cost. • W e provide an MILP formulation that finds the global optimum configuration for both scenarios as a benchmark. I I I . N E T WO R K M O D E L A N D A S S U M P T I O N S A. T ransmission and power models W e consider a network composed of N + 1 wireless nodes with random locations in a two-dimensional plane; a source S and a set P of N receiving nodes. The nodes in P are interested in recei ving the source’ s message. W e denote the set of all the nodes of the network by Q = P ∪ { S } . Every node j ∈ Q is equipped with an omnidirectional antenna and has an amplifier po wer constraint p max j for transmission ov er a radio link, and hence, its cov erage area is limited. For the sake of simplicity , we omit the efficienc y coefficient of the amplifier of the transmitters. In a transmission from a transmitting node j ∈ Q to a recei ving node i ∈ P \{ j } , nodes j and i are called the parent node (PN) and the child node (CN), respectively . The PNs transmit either by unicast or multicast if they have one or more than one intended receiv ers, respectiv ely . The transmission flow from the source to other nodes of the network forms a directed acyclic graph (D AG), 4 a graph in which there is at least one directed path from the source to all the nodes without any cycle, see Fig. 1. Every node i ∈ P chooses its PNs as well as the radio-link power of each of its chosen PNs. By combining the signals receiv ed from its chosen PNs, a CN can successfully decode the message if the accumulated SNR is at least equal to a threshold value γ th . The radio link po wer used by PN j to serve CN i , requested by the CN, is denoted by p req i,j . W e define the action of a node as the set of tuples composed of the PNs that the node chooses along with the corresponding requested po wers as a i = ( j, p req i,j ) | j ∈ A i , p req i,j ∈ [0 , p max j ] , (1) in which A i is the action set of the CN i from which it chooses its PNs. The set of actions of all the nodes is defined as a := { a i | i ∈ P } . (2) Giv en the transmit power of a transmitter , the SNR at a receiving node depends on the channel attenuation between the transmitter and the receiver as well as the noise power . The SNR at recei ving node i in a unicast transmission is defined as γ i,j ( p req i,j ) = p req i,j g i,j σ 2 . (3) in which g i,j and σ 2 are the channel gain between nodes i and j and the noise power , respectively . W e assume that the transmitting nodes in the this netw ork have their own channel for transmission and intra-network interference can be neglected [8]. Further, we assume that the statistical properties of the channel remain unchanged during the data dissemination and the channel gains of the links between a giv en node and its neighboring nodes are known at the node. The set N i of the neighboring nodes of node i ∈ P is defined as the nodes which can pro vide the minimum SNR required for decoding the message at node i via unicast considering their maximum radio-link po wer . More precisely , N i = { j | j ∈ Q i , γ i,j ( p max j ) ≥ γ th } (4) in which γ i,j ( p max j ) is defined in (3). Although with MRC a CN is able to accumulate the signals transmitted from the PNs which are not in its neighboring area, we restrict the action set of a CN to the nodes in its neighboring area. This is because overhead information needs to be transmitted in practice between a PN and a CN in order to find the multicast receiving group, the cost of the CNs, etc., and this implies that the PN must be in the neighboring area of the CN. The action set of node i in this section is defined as the set of neighboring nodes of node i whose distance from the source, in terms of the number of hops, is not larger than that for node i . More precisely , it is defined as A i = { j | j ∈ N i , h j ≤ h i , h j 6 = ∞} (5) in which h j is called the hop-rank of node j ∈ Q , representing the number of hops from the source to node j . Denoting by W i ⊆ A i the set of PNs of CN i , the hop-rank of CN i is obtained by h i = ( max j ∈W i { h j } + 1 , if W i 6 = ∅ ∞ , if W i = ∅ , ∀ i ∈ P , (6) which indicates that the hop-rank of a node depends on the maximum of the hop-ranks of its PNs if W i is not an empty S . . . . . . . . . Fig. 1: A sample network. In this network, node i decides to be served by more than one PN, that is, nodes l and j . set. Initially , we set h S = 0 and h j = ∞ for all j ∈ P . Note that, h j 6 = ∞ in (5) indicates that only a node that is already connected to the network and its hop-rank is not ∞ can be selected as a PN of a CN. In fact, the first receiving node, say node 1 , can only choose the source node as its PN since the hop-rank of all the nodes except the source is ∞ . The next node, say node 2 , now has two potential PNs; the source node with h S = 0 and node 2 with h 1 = 1 . This process continues until all the nodes join the network, howe ver , they can later change their decision. Based on the definition of the action of a node in (1), we observe that each action contains two sub-actions. W e call them the PN set and the po wer request set of node i and define them as W i = j | p req i,j > 0 , j ∈ A i (7) and p req i = p req i,j | p req i,j > 0 , j ∈ A i , (8) respectiv ely . The number of PNs chosen by CN i is denoted by W i = |W i | and W max is the maximum number of allowed PNs. In Fig. 1, W i = { l, j } . From the perspecti ve of a transmitting node j ∈ Q , we define the set of its CNs as M j = i p req i,j > 0 , ∀ i ∈ N j . (9) W e also denote the set of radio-link power requests r e- ceived by node j from its neighboring nodes as p rcv j = p req i,j | i ∈ M j and p rcv − i,j := p rcv j \ p req i,j represents p rcv j without p req i,j . The radio-link power of PN j in a multicast transmission is given by p Tx j ( p rcv j ) = max i ∈M j p req i,j . (10) As mentioned in Sec. I, the hardware of a wireless trans- mitter consists of se veral passiv e modules which all require a po wer for proper operation. W e refer to this power as the cir cuitry power of a node and denote the circuitry power of a node for transmission and reception by p ct j and p cr j for all j ∈ Q , respectiv ely . The circuitry power of a transmitter can be assumed as a fixed value. Hence, the sum transmit power of a PN j is obtained by P Tx j ( a ) := P Tx j ( p rcv j ) = 1 j ( M j ) p ct j + max i ∈M j p req i,j , (11) in which 1 j ( M j ) indicates if node j acts as a transmitting node, i.e., 1 j ( M j ) = 1 if M j 6 = ∅ and 1 j ( M j ) = 0 , otherwise. Using MRC, the aggregated SNR experienced by 5 Time-slots Transmit Receive Idle Nodes 1 2 3 S 1 2 3 4 Fig. 2: Transmission and reception in dif ferent time-slots in the scheduled section of the channel access. CN i is calculated by γ i | MRC ( p req i ) := X j ∈W i p req i,j g i,j σ 2 . (12) The channel access scheme employed in this network is composed of two sections. The first section is a random-access channel (RACH) used by the nodes for sending requests to their chosen PNs and the second section is a scheduled section in which e very PN has its own time-slot for transmission. In MRC-based multi-hop broadcast, when a CN chooses multiple PNs, each of the selected PNs, if not having a CN already , needs to reserve a time-slot for its transmission in the scheduled section. Moreover , each PN needs to inform its neighboring nodes about the new CN that joined it. Since in MRC a node needs to receive the messages from its PNs in multiple time-slots, depending on the number of PNs that a CN chooses, the reception power and consequently the energy it requires to consume ov er multiple time-slots changes. This issue is further illustrated in Fig. 2 in which transmissions over the scheduled section of the channel access is shown. In this Figure, for instance, node 1 recei ves its message from the source in time-slot 1 and acts as a PN in the next time-slot. Node 2 , in order to receiv e the message, accumulates the signals transmitted by nodes 1 and 3 in time-slots 2 and 3 , respectively . In this example, nodes 2 and 4 receiv e the message in two time-slots and the circuitry power they require for message reception is more than that required by nodes 1 and 3 that use only one time-slot. Since e very transmitting node in this network has its o wn time- slot for transmission and the receiving nodes merely receiv e the message during the time-slots that their respectiv e PNs transmit, intra-network interference will be pre vented in the network. The nodes in this network need to be synchronized in time domain so that they access the channel at the correct point in time. For clock synchronization, the clock of the source can be considered as the reference clock [27]. Since the MRC at a CN is carried out over multiple time-slots, no phase synchronization is required among the PNs of the CN. Note that collisions may occur during the network set-up in which the CNs find their respective PNs. In case of a collision, the nodes may back-off and access the channel at a later point in time 1 . The reception power of a CN i is calculated by P Rx i ( a ) = W i p cr i . (13) Hence, the total power of node j for both message transmis- sion and reception is given by P tot j ( a ) = P Rx j ( a ) + P Tx j ( a ) (14) B. Pr oblem formulation Since the transmission time-slots have equal length, by omitting the duration of the time-slots, the ener gy consumption of a node for transmission/reception can be represented by the power required for transmission/reception. Before defining the problems formally , we define the following terms. Definition 1: (Network power): The network po wer is defined as the sum of the total power of the nodes as P tot net ( a ) := X j ∈Q P tot j ( a ) , (15) in which P tot j ( a ) is defined in (14). W e further define the network transmit power by P Tx net ( a ) = P j ∈Q P Tx j ( a ) . Definition 2: (Node’ s Cost): W e define by C i ( p req i ) the total cost that a node i pays to its chosen PNs as C f i ( a ) = X j ∈W i c f j,i ( a ) , (16) in which c f j,i ( p req i,j ) is the cost paid fr om node i to its PN j under the cost sharing scheme f . Definition 3: (Social cost): The social cost of a network formed by the nodes in P is defined as [3] SC ( a ) := X i ∈P C f i ( a ) , (17) in which C i ( a ) is defined in (16). Definition 4: (Budget-balanced cost sharing scheme): A cost sharing scheme f is budget balanced if X i ∈M j c f j,i ( a ) = P Tx j ( a ) . (18) In other words, a cost sharing scheme is budget-balanced if the summation of the costs assigned to the CNs of a PN is equal to the sum transmit power of the PN. As discussed earlier , we consider two different scenarios in this network with the following objectiv es. Scenario 1 (Energy minimization) The objecti ve in this scenario is formally defined as P1: minimize { a i } i ∈P P tot net { a i } i ∈P (19a) subject to: γ i | MRC ( p req i ) ≥ γ th (19b) i ∈ P , j ∈ A i . (19c) According to the definition of A i in (5) and based on the definition of h i in (6), it is straightforward to see that having the condition j ∈ A i in (19c) is enough to ensure that the outcome of P1 is a DA G. Scenario 2 (Social cost minimization) In this scenario, we aim to find the minimum cost required to be paid by the receiving nodes of the network for obtaining the message. In this scenario, we focus on the class of budget-balanced cost 1 Please refer to [28] for further discussion on the channel access scheme. 6 T ABLE I: K ey notations used in this paper . Notation Definition N Number of receiving nodes P The set of all the nodes of the network except the source Q The set of all the nodes of the network W i The set of PNs chosen by CN i M j The set of CNs of PN j M j Number of CNs of PN j W i Number of PNs of node i W max Maximum number of PNs allowed to be chosen by a CN h i Hop-rank of node i γ i SNR of the signal received at CN i γ th Minimum SNR required at a CN for decoding the signal p ct j , p cr j Circuitry power of node j for transmission, reception. p Tx j Radio-link power of node j P Tx j Sum transmit power of node j : p ct j + p Tx j P Rx j Reception power of node j : W j p cr j P tot j T otal power of node j : P Rx j + P Tx j P Tx net Network transmit power: P j ∈Q P Tx j P tot net Network power: P j ∈Q P tot j p req i V ector of power requests of CN i from its chosen PNs p rcv j Power request vector received by PN j p rcv − i,j Power request vector recei ved by PN j excluding the request of CN i a i Action of node i a Set of actions of all the nodes of the network a − i Set of actions of all the nodes of the network except node i c f j,i Cost paid by CN i to PN j under the sharing function f C f i T otal cost paid by CN i to all its PNs sharing schemes, cf. Definition 4. The network objectiv e for the second scenario is defined as: P2: minimize { a i } i ∈P SC { a i } i ∈P (20a) subject to: (18) , (19b) , (19c) . (20b) T able I lists key notations used in this paper . In the next section, we propose decentralized approaches for problems P1 and P2 . I V . M R C - BA S E D D E C E N T R A L I Z E D M U LT I - H O P B RO A D C A S T A. Game-theoretic model W e design our decentralized approach via a non-cooperative CSG with the following properties: • Players: The finite number of nodes in P . • Action: Defined in (1) as a set of tuples that determines the PN set and (radio-link) power request set of the node, defied in (7) and (8), respectiv ely . For the PN set of CN i we have W i ∈ 2 A i \{ ∅ } and the joint PN set of the game is giv en by W = × i ∈P W i , in which 2 A i and × represent the po wer-set of A i and the Cartesian product, respectiv ely . W e further define the joint request set of the game as P req = × i ∈P p req i . • Cost function: Assigns a real-valued cost to ev ery node i ∈ P as C i ( a ) : ( W , P req ) → R + . The cost function is defined in (16). Remark 1: W e employ the MC cost sharing scheme for the first scenario. W e showed in [8] that the MC is simple and performs fairly well for network power minimization in multi- hop broadcast. Definition 5: (Marginal contribution (MC)) The cost of node i , based on the MC, is defined as the power imposed by CN i on the network, including the sum transmit power of the chosen PNs and its own circuitry power , as C MC i ( a ) = P Rx i ( a ) + X j ∈W i c MC j,i ( p rcv j ) (21) = W i p cr i + X j ∈W i P Tx j ( p rcv j ) − P Tx j ( p rcv − i,j ) . with P Tx j ( p rcv j ) defined in (11). Remark 2: In the second scenario where the CNs need to pay a price for receiving data, there are two points that have to be considered in defining a cost sharing function. Firstly , the cost sharing function must be budget-balanced. W ith a budget-balanced scheme, as shown in (18), a PN is paid by its CNs according to its sum transmit power . Secondly , the cost sharing function must be fair . Given a multicast by a PN, according to (10), each CN imposes a different level of radio-link power on the PN and thus, the cost that they need to pay to the PN must be shared among them in a fair manner . For this scenario, we employ Shapley value (SV) which is budget-balanced and known as the fairest cost sharing scheme [3]. Definition 6: (Shapley value (SV)) The SV of CN i ∈ M j is defined by [29] c SV j,i ( a ) = X S ⊆M j \{ i } |S | ! ( |M j | − |S | − 1)! |M j | ! ( P Tx j ( S ∪{ i } ) − P Tx j ( S )) . (22) Remark 3: While the cost function of a node in the first scenario, defined in (21), contains the reception power of a CN, the one used for the second scenario is merely defined according to the sum transmit powers of the PNs. The reason is that the goal in the first scenario is to minimize the network power and as far as the power of the network as a whole is concerned, the reception power needs to be also included in the cost function of the node. In contrast, in the second scenario we aim at minimizing the paid cost. In this case, we assume that a CN is not concerned about its reception power and merely aims at minimizing the cost it pays to its PNs. Definition 7: (Exact potential game) A game G is an e xact potential game [30] if there exists a function Φ : ( W , P req ) → R , called the potential function, such that ∀ i ∈ P , a , a 0 ∈ ( W , P req ) C i ( a 0 ) − C i ( a ) = Φ( a 0 ) − Φ( a ) . (23) Lemma 1: The game G without employing MRC, where ev ery node is allowed to choose only one PN, is a potential game for which at least one pure NE e xists [8]. The NE is reachable by using the best response dynamics in which every node iteratively chooses its PNs in a way to minimize its cost giv en the decision of other nodes. Theor em 1: The game G with MRC possesses an NE. Pr oof: Using Lemma 1 and the definition of an exact potential game in Definition 7, we show that our proposed game is also an an exact potential game. Let ∆ i ( j ) c i and ∆ i ( j ) Φ denote the change in the cost of node i and the potential function when i changes its request from PN j . Being a potential game in case of having only one PN implies that 7 c MC j,i ( a ) = p ct j + p req i,j , if 1 j ( M j \{ i } ) = 0 p req i,j − p Tx j ( p rcv − i,j ) , if 1 j ( M j \{ i } ) = 1 , p req i,j = max h ∈M j { p req h,j } 0 if 1 j ( M j \{ i } ) = 1 , p req i,j 6 = max h ∈M j { p req h,j } . (26) argmin p req i , t i , w i X j ∈A i w i,j p cr i + t i,j , ∀ i ∈ P (27a) subject to w i,j p min j ≤ p req i,j ≤ w i,j p max j , ∀ j ∈ A i (27b) X j ∈W i p req i,j g i,j σ 2 = γ th ∀ j ∈ A i (27c) p req i,j − p Tx j ( p rcv − i,j ) + (1 − 1 j ( M j \{ i } )) w i,j p ct j ≤ t i,j ∀ j ∈ A i (27d) X j ∈A i w i,j ≤ W max ∀ j ∈ A i (27e) p req i,j , t i,j ∈ R , s i,j , w i,j ∈ { 0 , 1 } ∀ j ∈ A i (27f) ∆ i ( j ) c i = ∆ i ( j ) Φ . Let W i and W 0 i be the sets of old and new PNs of CN i and ∆ i W i →W 0 i C i be the change in the cost of node i when it changes its PNs from W i to W 0 i . According to (16), the change in the cost of node i can be written as ∆ i W i →W 0 i C i = ∆ i W i →W 0 i X j ∈W i ∪W 0 i c j,i (24) Since the cost function in G , defined in (16), is linearly separable with respect to the cost paid by a CN to each of its chosen PNs, we can write the right side of (24) as ∆ i W i →W 0 i X j ∈W i ∪W 0 i c j,i = X j ∈W i ∪W 0 i ∆ i ( j ) c i = X j ∈W i ∪W 0 i ∆ i ( j ) Φ = ∆ i ( j ) X j ∈W i ∪W 0 i Φ = ∆Φ 0 , (25) which shows that the game is still an exact potential game. Hence, at least one NE exists for the game which can be obtained using the best response dynamics. Remark 4: Although reaching an NE in a finite number of iterations is guaranteed by using the best response dynamics, the con vergence time is exponential in the worst case. It has been shown in [31] that the av erage conv ergence time of the best response dynamics is e ζ N + O ( N ) in which e and ζ are the Euler’ s number and the Euler’ s constant, respectiv ely . Such a con ver gence time is acceptable for practical scenarios. B. Scenario 1: Minimum-power data dissemination In this section, we propose an MILP for the problem in (19a) using the MC, aiming at network power minimization. According to (21), c MC j,i ( a ) can be broken down as (26). As can be seen from (26), when 1 j ( M j { i } ) = 1 , the cost function c MC j,i ( a ) is a piece-wise linear function. Giv en the piece-wise linearity of the cost function, we propose the MILP problem shown in (27) for decision making at e very node i ∈ P . In the MILP , giv en in (27), w i is a binary vector of length |A i | defined as w i = [ w i,j | j ∈ A i ] where w i,j = 1 if node i chooses node j ∈ A j as its PN. W e define t i,j as an auxiliary variable which is used in both (27a) and (27d). w i,j p cr i in (27a) represents the power imposed on the network by node i due to its signal reception po wer . Moreov er , t i,j captures the sum transmit power of node i via (27a) and (27d). In (27b), p min j is the minimum radio-link power of a transmitter in transmit mode. (27c) represents the minimum-SNR condition for signal reception. Finally , (27e) can restrict the number of PNs that a CN can choose if the system designer sets such a restriction. C. Scenario 2: Minimum-cost data dissemination Despite the complexity of the SV in (22), we will sho w that it can be represented by a piece-wise linear function. Lemma 2: c SV j,i ( a ) in (22) can be written as c SV j,i ( a ) = p ct j M j + i X n =1 p req n,j − p req n − 1 ,j M j + 1 − n . (28) Pr oof: Using (11), the sum transmit power of a PN j is composed of two parts; p ct j as the fixed circuitry power and the the radio link power , i.e., p Tx j . Since these two parts are independent and since the SV satisfies the additivity axiom [3, Ch. 12], the cost of a node i ∈ M j can be separated as c SV j,i ( a ) = c SV j,i ( p ct j + p rcv j ) = c SV j,i ( p ct j )+ c SV j,i ( p req i,j , p rcv − i,j ) (29) in which the cost related to the circutiry po wer is equally shared among the CNs as c SV j,i ( p ct j ) = p ct j / M j [8]. Moreover , the cost share regarding the requests of the CNs by assuming that they can be sorted as 0 = p req 0 ,j ≤ p req 1 ,j ≤ · · · ≤ p req n,j ≤ p req i,j ≤ p req n +2 ,j ≤ · · · ≤ p req M j ,j (30) is gi ven by [32] [33] c SV j,i ( p req i,j , p rcv − i,j ) = i X k =1 p req k,j − p req k − 1 ,j M j + 1 − k . (31) Lemma 3: Suppose that the requests receiv ed by PN j can be sorted as (30). c SV j,i ( p req i,j , p rcv − i,j ) in (29) can be modeled by 8 argmin p req i , t i , s i , w i X j ∈A i t i,j , ∀ i ∈ P (36a) subject to: w i,j p min j ≤ p req i,j ≤ w i,j p max j , ∀ j ∈ A i (36b) X j ∈W i p req i,j g i,j σ 2 = γ th ∀ j ∈ A i (36c) m i ( n ) p req i,j + y i ( n, p rcv − i,j ) ≤ t i,j ∀ j ∈ A i , 0 ≤ n ≤ M j (36d) X j ∈A i w i,j ≤ W max ∀ j ∈ A i (36e) p req i,j , t i,j ∈ R , s i,j , w i,j ∈ { 0 , 1 } ∀ j ∈ A i (36f) a piece wise-linear, increasing function as c SV j,i ( p req i,j , p rcv − i,j ) = p req i,j M j − n + n ≥ 1 X k =1 − p req k,j ( M j − k )( M j − k + 1) ! . (32) Pr oof: See Appendix A. Theor em 2: Let M j \ i := M j \{ i } be the set of CNs of PN j without node i with the number M j \ i of CNs. Let p req i,j be the ( n + 1) -th smallest request among the CNs of PN j as (30). Then, the cost of a node i in (29) if it joins PN j according to the SV is obtained by c SV j,i ( a ) = m i ( n ) p req i,j + y i ( n, p rcv − i,j ) (33) in which m i ( n ) = 1 M j \ i + 1 − n (34) and y i ( n, p rcv − i,j ) = p ct j M j \ i + 1 + n ≥ 1 X k =1 − p req k,j ( M j \ i − k + 1)( M j \ i − k + 2) ! . (35) Pr oof: It follows directly from Lemma 2 and Lemma 3. Cor ollary 1: The optimum request vector of node i , i.e., p req i can be obtained by solving an MILP . The optimal decision of node i can be obtained by the MILP shown in (36). Notice that the parameters used in the MILP of (36) are like the ones used for the MC scheme in (27). V . M R C - BA S E D C E N T R A L I Z E D A P P R OAC H W I T H M I L P In the previous section, we discussed decision-making with the MC and the SV schemes. In this section, we find the global optimum for both the network power and the social cost minimization problems. Theor em 3: Let { ∗ a i } PTx i ∈P and { ∗ a i } SC i ∈P be the set of opti- mum action profiles corresponding to the network’ s minimum transmit power (see T able I) and the minimum social cost (with a budget-balanced cost sharing scheme), respectively . W e always have { ∗ a i } PTx i ∈P = { ∗ a i } SC i ∈P . Pr oof: Theorem 3 states that any action profile that minimizes the network’ s transmit power , minimizes the social cost as well. Using the definition of a budget-balanced cost sharing scheme, for every PN j ∈ N we hav e X i ∈M j c BB j,i ( a ) = P Tx j ( a ) . (37) By taking a summation o ver all the nodes of the network which can act as PNs, we get X j ∈Q X i ∈M j c BB j,i ( a ) = X j ∈Q P Tx j ( a ) . (38) Note that the payment received by a PN is equal to the cost paid by its CNs. Therefore, we can replace the left side of (38), which is the total payment receiv ed by the PNs in the network, with the total cost paid by the CNs. Hence, the left side of (38), using (16), is equiv alent to X j ∈Q X i ∈M j c BB j,i ( a ) = X i ∈P X j ∈W i c BB j,i ( a ) = X i ∈P C i ( a ) = SC( a ) (39) By comparing (38) and (39), we find that with a b udget- balanced cost sharing scheme, the action profile that minimizes the social cost also minimizes the network transmit power . Cor ollary 2: The MILP that finds the optimum configura- tion for P1 in (19) can also be used for P2 in (20) if p cr j = 0 . Before providing the MILP , we define the following. • ˜ S : The maximum number of time-slots used for message dissemination in the network. T o av oid notational confu- sion, between the source and the time-slot, we show the source node in this formulation by S and ( s ) represents time-slot s such that 1 ≤ s ≤ ˜ S . • P Tx (radio-link power matrix): A ( N + 1) × ˜ S ma- trix with P = [ p Tx (1) , . . . , p Tx ( ˜ S ) ] in which p ( s ) = [ p Tx S , ( s ) , p Tx 1 , ( s ) , . . . , p Tx N , ( s ) ] | is a column vector and p Tx j, ( s ) shows the radio-link po wer of node j in time-slot s . • T (transmission matrix): A ( N + 1) × ˜ S binary ma- trix with T = [ t S , t 1 , . . . , t N ] | in which t j = [ t j, (1) , t j, (2) , . . . , t j, ( ˜ S ) ] is a ro w vector of size 1 × ˜ S and t j, ( s ) = 1 if node j transmits in time-slot s . • R (reception matrix): A N × ˜ S binary matrix with R = [ r 1 , . . . , r N ] | in which r j = [ r i, (1) , r i, (2) , . . . , r i, ( ˜ S ) ] is a row vector of size 1 × ˜ S and r i,s = 1 if node i receives the message from a transmitting node that transmits in time-slot s . • G (channel gain matrix): A N × ( N + 1) matrix with 9 G := [ g | 1 , . . . , g | N ] | in which g i = [ g i, S , g i, 1 . . . , g i,N ] is a 1 × N + 1 ro w vector and g i,j is the channel gain between transmitter j and receiv er i . W e set g i,j = 0 if j / ∈ A i . • Γ (SNR matrix): A N × ˜ S matrix with Γ := [ γ 1 , . . . , γ N ] | in which γ i = [ γ i, S , γ i, 1 . . . , γ i,N ] is a 1 × ˜ S ro w vector and γ i, ( s ) is the SNR recei ved by node i in time-slot s . • 1 N : An all 1 vector of size N × 1 . • I N ( i ) : A binary vector of size N × 1 with all its elements equal to 1 except the i -th element. Before presenting the optimization problem, we provide the following lemma. Lemma 4: (Big M method) : Let v 1 , v 2 ∈ R ≥ 0 and b ∈ { 0 , 1 } all be the v ariables of an optimization problem. The following non-linear constraint v 1 = v 2 b (40) can be linearized by the following set of constraints v 1 ≤ v 2 (41) v 1 ≤ M b (42) v 1 ≥ v 2 − M (1 − b ) (43) v 1 ≥ 0 (44) in which M is a sufficiently large number such that v 2 ≤ M . Remark 5: According to Lemma 4, when b = 1 , based on the constraints (41) and (43), v 2 limits v 1 from both upper and lower sides as v 2 ≤ v 1 ≤ v 2 . Hence, v 1 = v 2 if b = 1 . Like wise, one can observe that when b = 0 , according to (42) and (43) we have v 2 − M ≤ v 1 ≤ 0 . Further , based on the constraint (44) together with (42) and (43) we finally get 0 ≤ v 1 ≤ 0 which results in v 1 = 0 . The MILP for the MRC-based multi-hop broadcast is pre- sented in (45). Recall that, when the network objecti ve is social cost minimization, we set p cr j = 0 in formulation (45a). The constraint in (45b) indicates the radio-link po wer con- straint. Based on our assumption, ev ery node can transmit in one time-slot. This property has been captured by (45c). The condition in (45e) indicates that there exists at most one transmission per time-slot. Further , ev ery node receiv es the message at least in one time slot as shown in (45d). The constraint in (45f) is due to the fact that a reception occurs in a time-slot if there is at least one transmission. The constraint (45g) indicates that a node i ∈ P does not receive the message if it has already transmitted it. In fact, r i, ( s ) = 0 if node i transmits the messages in one of the previous slots 1 ≤ s 0 ≤ s . The expression in (45h), in which shows the element-wise product, calculates the normalized SNR of the signal received at user i in time-slot s . More precisely , given the radio- link powers of the users at time-slot s in p s , the expression p s I N +1( i ) g | i giv es a vector whose elements are the SNR of the signal receiv ed by node i from each of the transmitters j ∈ Q in time-slot s . Recall that I N +1( i ) is an all-one column vector of length N + 1 with the i -th element equal to zero. This helps us to eliminate the SNR received by node i due to its own transmission. In (45h), 1 | N +1 p ( s ) I N +1( i ) g | i giv es the SNR receiv ed by node i which we normalize it to γ th σ 2 and represent it by ˆ γ i, ( s ) with ˆ γ i, ( s ) ≤ 1 . T ABLE II: Main parameters used for simulation Notation value Number N of nodes 10, 15, 20, 25 Network size 250m × 250m Circuitry power , p c 1, 10, 100 mW Channel model Path-loss Path-loss coefficient, α 3 Noise power , σ 2 -90 dBm Signal wave-length, λ 0.125 m Although (45h) determines the SNR av ailable at node i in time-slot s , the actual SNR receiv ed by node i depends on whether node i recei ves the message in this time-slot. Node i uses the signals transmitted in time-slot s if r i, ( s ) = 1 . The constraints in (45i), (45j) and (45k) are used based on the big M method, discussed in Lemma 4. They hav e been employed here to find out if node i should receive the message in time- slot s . More precisely , they linearize the follo wing constraint γ i, ( s ) = r i, ( s ) ˆ γ i, ( s ) (46) in which ˆ γ i, ( s ) is a function of the continuous variable p Tx i, ( s ) that makes the right side of (46) non-linear . The constraint in (45l) indicates that the aggregated SNR obtained by ev ery node i ∈ P must be higher than the minimum SNR. Every node i ∈ P can transmit the message in time-slot s if and only if it recei ves the message with minimum SNR over the previous time-slots. The only e xception is the source for which we always hav e t S , 1 = 1 . V I . P E R F O R M A N C E A N A L Y S I S A. Simulation setup An area of size 250m × 250m is considered in which the nodes are randomly distrib uted. The simulation results are based on the Monte-Carlo method and in each simulation run, one of the nodes in the network is randomly chosen as the source. The total number of nodes varies between 10 and 25. W e assume that the transmit and receive circuitry powers of the nodes in the network are equal, i.e., p cr j = p ct j = p c [6] and consider three values for circuitry powers, p c ∈ { 1 , 10 , 100 } mW. The low circuitry po wer case is suitable for low-po wer IoT applications while the high circuitry power can model con ventional wireless transmitters [34], [35]. The noise power , represented by σ 2 in (3), is set to -90 dBm. The channel is based on the path-loss model. Let l i,j and l 0 be the distance between nodes i and j and a reference distance, respectiv ely . Then, by considering α as the path loss exponent and λ as the signal wav elength, the power gain of the channel between nodes i and j is defined as g i,j = λ 4 π l 0 2 l 0 l i,j α . (47) For simulation, we set λ = 0 . 125 m, l 0 = 1 m and α = 3 . The results are normalized to the v alue v = ˜ p Tx + ˜ p c in which ˜ p Tx and ˜ p c represent normalization reference values for the radio-link power and the circuitry power , respectively . More precisely , the normalized network power and the nor- malized social cost are defined as P tot net ( a ) = P j ∈Q P tot j ( a ) v , SC( a ) = P i ∈P C i ( a ) v , (48) 10 min P , T , R , Γ ˜ S X s =1 X j ∈Q p Tx j, ( s ) + p ct j t j, ( s ) + X i ∈P p cr j r i, ( s ) , (45a) s. t.: t j, ( s ) p min j ≤ p Tx j, ( s ) ≤ t j, ( s ) p max j , ∀ j ∈ Q , 1 ≤ s ≤ ˜ S (45b) t j 1 ˜ S ≤ 1 , ∀ j ∈ Q (45c) r i 1 ˜ S ≥ 1 , ∀ i ∈ P (45d) X j ∈Q t j, ( s ) ≤ 1 , ∀ j ∈ Q , 1 ≤ s ≤ ˜ S (45e) r i, ( s ) ≤ X j ∈Q t j, ( s ) , ∀ i ∈ P , j ∈ Q , 1 ≤ s ≤ ˜ S (45f) r i, ( s ) ≤ 1 − s X s 0 =1 t i, ( s 0 ) , ∀ j ∈ Q , 1 ≤ s ≤ ˜ S (45g) ˆ γ i, ( s ) = 1 | N +1 p ( s ) I N +1( i ) g | i /γ th σ 2 , ∀ j ∈ Q , 1 ≤ s ≤ ˜ S (45h) γ i, ( s ) ≤ ˆ γ i, ( s ) , ∀ i ∈ P , 1 ≤ s ≤ ˜ S (45i) γ i, ( s ) ≥ ˆ γ i, ( s ) − M (1 − r i, ( s ) ) , ∀ i ∈ P , 1 ≤ s ≤ ˜ S (45j) γ i, ( s ) ≤ M r i, ( s ) , ∀ i ∈ P , 1 ≤ s ≤ ˜ S (45k) γ i 1 ˜ S ≥ 1 , ∀ j ∈ P (45l) t j, ( s ) ≤ s − 1 X s 0 =1 γ j, ( s 0 ) , ∀ j ∈ P , 2 ≤ s ≤ ˜ S (45m) t S , 1 = 1 (45n) p Tx j, ( s ) , γ i, ( s ) ∈ R ≥ 0 , t j, ( s ) , r i, ( s ) ∈ { 0 , 1 } , ∀ i ∈ P , j ∈ Q , 1 ≤ s ≤ ˜ S (45o) respectiv ely , where ¯ P tot net ( a ) is defined in (14) and C i ( a ) = P j ∈W i c SV j,i in which c SV j,i is defined in (28). W e set ˜ p Tx = 200 mW and ˜ p c = 10 mW . Moreover , we do not set any limitation on the number of PNs that a CN is allo wed to select. The simulation has been carried out in MA TLAB and the proposed MILPs are solved using CVX [36] and Gurobi 2 . T able II summarizes the main parameters used for simulation. The algorithms that we consider in this section for ev alua- tion are as follows. • GreedyMRC: The centralized MRC-based greedy algo- rithm proposed in [10] introduced in Section II. Despite being centralized, due to lack of a more rele vant work, we use it as our main benchmark. • MC-MRC, SV -MRC: Our proposed MRC-based algo- rithm with the MC and the SV schemes, respectiv ely . • MC-OPN, SV -OPN: Special case of MC-MRC and SV - MRC in which the nodes can choose only one PN. • MILP-MRC, MILP-OPN: The MILP-based optimum solution obtained by solving (45) with and without ex- ploiting MRC, respectively . B. Simulation r esults W e first show the importance of taking the circuitry power into account for message dissemination. W e compare our proposed algorithm with GreedyMRC proposed in [10] which is centralized, ignores the circuitry power required at the nodes 2 https://www .gurobi.com/ and merely considers the power required for the radio link in network optimization. Figures 3a, 3b and 3c, correspond to low , medium and high circuitry powers, respectively . First, we observe that by increasing the number N of nodes, the netw ork power increases. This is because the circuitry powers required at the nodes for message reception and transmission impose additional power on the network which is not negligible. Second, we observe in Fig. 3a that by increasing the number of nodes, the po wers required by both algorithms tend to saturate. When the netw ork becomes denser, the number of PNs required for cov ering the network and serving all the receiving nodes does not necessarily increase. Hence, by increasing the number of nodes, at some point, the total radio link power required in the network for message dissemination remains unchanged. Howe ver , the circuitry po wer required at the nodes makes the network power continue to increase. The value of the circuitry power in Fig. 3c is higher than that for the other tw o cases. Thus, in Fig. 3c, e ven if the total radio-link power of the network does not change significantly , the high value of the circuitry po wer dominates the radio-link po wer required in the network. This results in a constant increase of the network power in Fig. 3c. Our proposed algorithm outperforms GreedyMRC in all the three cases shown in Fig. 3. When the circuitry power of the nodes is high, the performance of our game-theoretic algorithm becomes significantly better than the benchmark algorithm, see Fig. 3c. The main reason is that with our approach the nodes take the circuitry power into account in 11 10 15 20 25 2 2 . 5 3 No. N of Nodes Normalized network power P tot net ( a ) GreedyMRC - [10] MC-MRC (a) p c = 1 mW 10 15 20 25 2 4 6 8 No. N of Nodes Normalized network power P tot net ( a ) GreedyMRC - [10] MC-MRC (b) p c = 10 mW 10 15 20 25 0 20 40 60 No. N of Nodes Normalized network power P tot net ( a ) GreedyMRC - [10] MC-MRC (c) p c = 100 mW Fig. 3: Network power for different numbers N of nodes in the network and different values p c of circuitry power . choosing their PNs. In contrast, with [10], the message is always transmitted o ver large number of hops in order to minimize the total radio link power of the network. Since each transmission requires circuitry power besides the radio-link power , the actual network power required by [10] for message dissemination, after adding the circuitry power of the nodes to the outcome of the algorithm, becomes significantly high. This is more pronounced with high values of the circuitry power . In Fig. 4 we ev aluate the effect of employing the MRC in message dissemination. W e depict the network power obtained via the MC and the MILP approaches for different numbers of the nodes and different v alues of the circuitry power . First, we observe that with MRC, the message can be disseminated with a lower network power compared to the case of one PN (OPN). Second, we find in Fig. 4a that, when the circuitry power is low ( p c = 1 mW), employing the MRC technique results in a higher gain compared to the case in which the circuitry power is high. In fact, when the radio-link power dominates the circuitry power , it is beneficial for the nodes to combine the signals from multiple PNs. Conv ersely in Fig. 4b, where the circuitry power is high, i.e., 100 mW , the nodes do not exploit the MRC as it requires reception circuitry power ov er multiple time-slots. In other words, as shown in Fig. 4b, ev en if the nodes are allowed to choose multiple PNs, they only select one PN and hence, the performance of the MPN and OPN approaches are almost the same. Figure 5 ev aluates the effect of employing MRC on the social cost. As mentioned earlier , when the social cost mini- mization is the objectiv e, the nodes do not consider their own reception circuitry power . In fact, the goal of the nodes in this case is to minimize the power imposed on their chosen PNs and consequently to minimize the cost they pay . Similar to the MC-based game in Fig. 4, here, SV -MRC performs better that SV -OPN in terms of the social cost. In other words, the total cost paid by the receiving nodes in order to receive the message reduces when they are allowed to recei ve the message from more than one PN. By comparing Fig. 4a and Fig. 5a, we find that employing the MRC has a slightly higher gain on the SV -based game than the MC-based game. The reason is that in the SV -based game, the reception circuitry power is not considered in the cost function of a CN. Hence, recei ving via the MRC over multiple time-slots imposes a lower cost 10 12 14 16 18 20 22 24 1 1 . 5 2 2 . 5 3 3 . 5 4 4 . 5 No. N of Nodes Normalized network po wer P tot net ( a ) MILP-MRC - p c = 1 mW MILP-OPN - p c = 1 mW MC-MRC - p c = 1 mW MC-OPN - p c = 1 mW MILP-MRC - p c = 10 mW MILP-OPN - p c = 10 mW MC-MRC - p c = 10 mW MC-OPN - p c = 10 mW (a) The network power with p c ∈ { 1 mW , 10 mW } . 10 12 14 16 18 20 22 24 4 6 8 10 12 No. N of Nodes Normalized network po wer P tot net ( a ) MILP-MRC MILP-OPN MC-MRC MC-OPN (b) The network power with p c = 100 mW . Fig. 4: The normalized network power for different numbers N of nodes in the network and different v alues p c of circuitry power . on the recei ving nodes compared to the MC-based game in which the cost of reception is also included. In order to find the ef fect of the MRC technique on nodes’ decision, in Fig. 6 we sho w the av erage number of PNs per CN with two v alues for the circuitry power , 1 mW and 10 mW . Considering the MC-MRC and the SV -MRC for low circuitry power , i.e., p c = 1 mW , we observe that the average number 12 10 12 14 16 18 20 22 24 2 2 . 2 2 . 4 2 . 6 2 . 8 3 3 . 2 3 . 4 3 . 6 3 . 8 No. N of Nodes Normalized social cost SC( a ) SV -OPN - p c = 1 mW SV -MRC - p c = 1 mW SV -OPN - p c = 10 mW SV -MRC - p c = 10 mW (a) The social cost with p c ∈ { 1 mW , 10 mW } . Fig. 5: The normalized social cost for different numbers N of nodes and different v alues p c of circuitry power . of PNs per CN for the MC-based game is higher than that for the SV -based game. The reason is that, since the objective is network power minimization and since the circuitry power in this case is low , the nodes exploit the MRC technique to a higher extent than the SV -based game in order to reduce their costs as well as the network power . In addition, we observe that, in general, when the circuitry power increases, the a verage number of PNs per CN reduces for both the MC-based and the SV -based games. This reduc- tion is more significant for the MC-based game. Recall that, with the MC-based game, the cost of a CN with respect to the cir cuitry power of its PN is either zero (in multicast) or p c (in unicast), see (26). Moreover , according to (28), with the SV -based game, the circuitry po wer of transmission at the PN is equally shared among the CNs. In short, the impact of the transmission circuitry po wer on the cost function of a node is not as significant as the impact of the reception circuitry power which is only captured in the MC-based game. Therefore, as the circuitry po wer increases from p c = 1 mW to p c = 10 mW , the nodes in the MC-based game react by choosing a lower number of PNs, while in contrast, such an increase of the circuitry power has a lower impact on the decision of the nodes in the SV -based game. For instance, when there are 20 nodes in the network, by increasing the circuitry power from p c = 1 mW to p c = 10 mW , the av erage number of PN per CN with the MC-based game reduces from 1.26 to 1.11 PNs per CN. These numbers for the SV -based game are 1.18 and 1.16 PNs per CN, respectively . Finally , Fig. 7 shows how efficient the resources are used in this network for different algorithms. W e plot the network power versus the number of time-slots used in the network for message dissemination. The optimum MILP-based approach and the MC-based game are considered with two different values of circuitry power , that is, p c = 10 mW and p c = 100 mW . Further , the performance of the GreedyMRC is also shown for the case of p c = 10 mW . Since the network power obtained by the GreedyMRC for p c = 100 mW is much higher than for the other algorithms, we omit the GreedyMRC for p c = 100 mW . In Fig. 7, the closer the points are to the 10 15 20 25 1 . 1 1 . 2 1 . 3 No. N of Nodes A vg. no. of PNs per CN SV - p c = 1 mW SV - p c = 10 mW MC - p c = 1 mW MC - p c = 10 mW Fig. 6: The average number of PNs per CN for dif ferent numbers N of nodes in the network. 4 6 8 10 12 14 16 18 0 2 4 6 8 10 12 Fig. 7: Normalized network power P tot net ( a ) versus the number ˜ S of time-slots used for message dissemination. origin, the better the resources are used. As can be seen, when the circuitry po wer increases, the number of time-slots required for message dissemination in the network decreases. In other words, transmissions over a large number of hops impose additional transmission and reception circuitry powers on the nodes. Hence, cost minimization at the nodes results in a message dissemination strategy that requires a lower number of time-slots. Considering both Fig. 7 and Fig. 6, it can be inferred that by increasing the circuitry po wer , the nodes tend to receiv e the message from one PN and the multicast receiving groups are formed by a lar ger number of CNs so that both the average number of PNs per CN as well as the av erage number of required time-slots reduce. V I I . S U M M A RY W e studied multi-hop broadcast in a network with one source and multiple receiv ers. The nodes are able to exploit the MRC technique and combine the messages receiv ed from multiple transmitting nodes in order to reduce the network power required for message dissemination. W e studied two scenarios depending on the need for an incenti ve for the transmitting nodes. A decentralized approach using a non- cooperativ e CSG is proposed in which the nodes employ the MC and the SV cost sharing schemes for minimization of net- work power in incentiv e-independent networks and social cost 13 in incenti ve-mandatory networks, respecti vely . W e showed that our proposed game is a potential game that possesses an NE. Simulation results sho wed that our proposed algorithm outperforms the existing heuristic algorithm concerning the required power for message dissemination while it is also able to address the incentiv e and fairness issues. Further , since our algorithm captures the impact of the circuitry power on the network power , the higher the circuitry power of the nodes, the higher gain is obtained by our algorithm compared to the benchmarks. W e also presented the centralized global optimum via an MILP that can be used for both scenarios. A P P E N D I X A P RO O F O F L E M M A 3 Assume that p req i,j is the ( n + 1) th lowest request from PN j as shown in (30) such that p req i,j = p req n +1 ,j . Based on (31) by considering i = n + 1 , c SV j,i ( p req i,j , p rcv − i,j ) can be written as a function of n as c SV j,i ( p req i,j , p rcv − i,j ) = p req i,j − p req n,j M j + 1 − ( n + 1) + n X k =1 p req k,j − p req k − 1 ,j M j + 1 − k . (49) Expanding the right side of (49) leads to c SV j,i ( p req i,j , p rcv − i,j ) = p req i,j M j − n − p req n,j M j − n + p req n,j M j − n + 1 + · · · − p req 1 ,j M j − 1 + p req 1 ,j M j . (50) Eq. (50) is equiv alent to c SV j,i ( p req i,j , p rcv − i,j ) = p req i,j M j − n + n ≥ 1 X k =1 − p req k,j ( M j − k )( M j − k + 1) ! . (51) It can be deriv ed from (51) that the cost of node i is obtained by a linear function whose slope and y-intercept depend on the interval that p req i,j falls in. Eq. (51) sho ws that if p req i,j increases and falls inside an interval with a higher n , the slope of the function c j,i in (51) increases accordingly . Besides, the y-intercept of c j,i decreases. Hence, c j,i forms a piece-wise linear function that increases in the interval [0 , p max j ] . R E F E R E N C E S [1] M. Mousa vi, S. M ¨ uller , H. Al-Shatri, B. Freisleben, and A. Klein, “Multi-hop data dissemination with selfish nodes: Optimal decision and fair cost allocation based on the shapley value, ” in Pr oc. IEEE International Conference on Communications (ICC) , May 2016. [2] “Ericsson consumerlab report, TV and media, ” 2018, [Online]. A vail- able: https://www .ericsson.com/assets/local/mobility- report/documents/ 2018/ericsson- mobility- report- november - 2018.pdf. [3] Y . Shoham and K. Leyton-Brown, Multiagent Systems: Algorithmic, Game-Theor etic, and Lo gical F oundations . New Y ork, NY , USA: Cambridge University Press, 2008. [4] M. Condoluci, G. Araniti, T . Mahmoodi, and M. Dohler, “Enabling the IoT Machine Age With 5G: Machine-T ype Multicast Services for Innov ative Real-Time Applications, ” IEEE Access , vol. 4, pp. 5555– 5569, Sept. 2016. [5] A. Argyriou, K. Poularakis, G. Iosifidis, and L. T assiulas, “V ideo Deliv ery in Dense 5G Cellular Networks, ” IEEE Network , vol. 31, no. 4, pp. 28–34, July 2017. [6] S. Cui, A. J. Goldsmith, and A. Bahai, “Energy-constrained modulation optimization, ” IEEE T ransactions on W ireless Communications , vol. 4, no. 5, pp. 2349–2360, September 2005. [7] H. Al-Shatri, K. Keller, F . Jacobfeuerborn, O. Hinz, and A. Klein, “Eliciting and considering underlay user preferences for data-forwarding in multihop wireless networks, ” IEEE Access , vol. 7, pp. 40 052–40 067, 2019. [8] M. Mousavi, H. Al-Shatri, and A. Klein, “Cost sharing games for energy- efficient multi-hop broadcast in wireless networks, ” IEEE T ransactions on W ireless Communications , October 2019. [9] J. E. Wieselthier , G. D. Nguyen, and A. Ephremides, “Energy-efficient broadcast and multicast trees in wireless networks, ” Mobile Networks and Applications , vol. 7, no. 6, pp. 481–492, December 2002. [10] I. Maric and R. Y ates, “Cooperativ e multihop broadcast for wireless networks, ” IEEE Journal on Selected Ar eas in Communications , v ol. 22, no. 6, pp. 1080–1088, Aug. 2004. [11] A. Bader and M. Alouini, “Localized power control for multihop large- scale internet of things, ” IEEE Internet of Things Journal , vol. 3, no. 4, pp. 503–510, Aug 2016. [12] A. Kuehne, H. Q. Le, M. Mousavi, M. Wichtlhuber , D. Hausheer, and A. Klein, “Power control in wireless broadcast networks using game theory , ” in Proc. ITG Conference on Systems, Communications and Coding , February 2015, pp. 1–5. [13] X. Zeng, M. Y u, and D. W ang, “ A new probabilistic multi-hop broad- cast protocol for vehicular networks, ” IEEE T ransactions on V ehicular T echnology , vol. 67, no. 12, pp. 12 165–12 176, Dec 2018. [14] L. W ang, H. W u, Z. Han, P . Zhang, and H. V . Poor, “Multi-hop coop- erativ e caching in social iot using matching theory , ” IEEE T ransactions on W ireless Communications , vol. 17, no. 4, pp. 2127–2145, April 2018. [15] M. Mousavi and A. Klein, “Decentralized video streaming in multi-hop wireless networks: Incentiv e mechanism and energy efficiency , ” IEEE Access , vol. 7, pp. 51 329–51 345, December 2019. [16] Y . Cai, Y . Fan, and D. W en, “ An incentiv e-compatible routing protocol for two-hop delay-tolerant networks, ” IEEE Tr ansactions on V ehicular T echnology , vol. 65, no. 1, pp. 266–277, Jan 2016. [17] A. MVS, H. Pancholi, P . Priyanka, and G. S. Kasbekar, “Beyond the VCG mechanism: Truthful reverse auctions for relay selection with high data rates, high base station utility and low interference in D2D networks, ” CoRR , vol. abs/1906.00379, 2019. [Online]. A vailable: http://arxiv .org/abs/1906.00379 [18] Z. Zheng, L. Song, and Z. Han, “Bridge the Gap Between ADMM and Stackelberg Game: Incentive Mechanism Design for Big Data Networks, ” IEEE Signal Pr ocessing Letters , vol. 24, no. 2, pp. 191– 195, Feb 2017. [19] J. Gao, L. Zhao, and X. Shen, “Network utility maximization based on an incentiv e mechanism for truthful reporting of local information, ” IEEE T ransactions on V ehicular T echnology , vol. 67, no. 8, pp. 7523–7537, Aug 2018. [20] D. Chatzopoulos, M. Ahmadi, S. Kosta, and P . Hui, “Flopcoin: A cryp- tocurrency for computation offloading, ” IEEE T ransactions on Mobile Computing , vol. 17, no. 5, pp. 1062–1075, May 2018. [21] G. Iosifidis, L. Gao, J. Huang, and L. T assiulas, “Efficient and f air collab- orativ e mobile internet access, ” IEEE/A CM Tr ansactions on Networking , vol. 25, no. 3, pp. 1386–1400, June 2017. [22] D. Chatzopoulos, S. Gujar, B. Faltings, and P . Hui, “Localcoin: An ad- hoc payment scheme for areas with high connectivity , ” November 2017, [Online]. A vailable: https://arxiv .org/abs/1708.08086. [23] J. Li, M. Liu, J. Lu, F . Shu, Y . Zhang, S. Bayat, and D. N. K. Jayakody, “On Social-A ware Content Caching for D2D-Enabled Cellular Networks W ith Matching Theory, ” IEEE Internet of Things Journal , vol. 6, no. 1, pp. 297–310, Feb 2019. [24] J. R. Marden and A. W ierman, “Distributed welfare games, ” Operations Resear ch , vol. 61, no. 1, pp. 155–168, 2013. [25] M. Mousavi, H. Al-Shatri, M. Wichtlhuber , D. Hausheer, and A. Klein, “Energy-Ef ficient Data Dissemination in Ad Hoc Networks: Mechanism Design with Potential Game, ” in Proc. IEEE 12th International Sympo- sium on Wir eless Communication Systems (ISWCS) , Aug. 2015. [26] M. Mousavi, H. Al-Shatri, H. Q. Le, A. Kuehne, M. W ichtlhuber, D. Hausheer , and A. Klein, “Game-based multi-hop broadcast including power control and MRC in wireless networks, ” in Proc. IEEE 26th International Symposium on P ersonal, Indoor and Mobile Radio Com- munications (PIMRC) , Aug. 2015, pp. 1611–1616. [27] Y . C. W u, Q. Chaudhari, and E. Serpedin, “Clock synchronization of wireless sensor networks, ” IEEE Signal Processing Magazine , vol. 28, no. 1, pp. 124–138, January 2011. [28] Seyed Mahdi Mousavi T oroujeni, “Game theory for multi-hop broadcast in wireless networks, ” Ph.D. dissertation, T echnische Univ ersit ¨ at Darmstadt, Darmstadt, Germany , 2020. [Online]. A vailable: http://tuprints.ulb .tu- darmstadt.de/9284/ 14 [29] L. S. Shapley , A V alue for n-person Games , ser . In Contributions to the Theory of Games. Princeton University Press, 1953, vol. 28, pp. 307–317. [30] D. Monderer and L. S. Shaple y , “Potential g ames, ” Games and Economic Behavior , vol. 14, no. 1, pp. 124 – 143, 1996. [31] S. Durand and B. Gaujal, “Complexity and optimality of the best response algorithm in random potential games, ” in Algorithmic Game Theory , M. Gairing and R. Sav ani, Eds. Springer Berlin Heidelberg, 2016, pp. 40–51. [32] S. Littlechild and G. Owen, “ A simple expression for the shapley value in a special case, ” Management Science , vol. 20, no. 3, November 1973. [33] C. Singh and E. Altman, “The wireless multicast coalition game and the non-cooperativ e association problem, ” in Pr oc. IEEE Conference on Computer Communications (INFOCOM) , April 2011, pp. 2705–2713. [34] W . R. Heinzelman, A. Chandrakasan, and H. Balakrishnan, “Energy- efficient communication protocol for wireless microsensor networks, ” in Proceedings of the 33rd Annual Hawaii International Conference on System Sciences , vol. 2, January 2000, p. 10. [35] Q. W ang, M. Hempstead, and W . Y ang, “ A realistic power consumption model for wireless sensor network de vices, ” in in pr oc. 3rd Annual IEEE Communications Society on Sensor and Ad Hoc Communications and Networks (SECON) , vol. 1, September 2006, pp. 286–295. [36] M. Grant and S. Boyd, “CVX: Matlab Software for Disciplined Con vex Programming, version 2.1, ” http://cvxr .com/cvx, March 2014.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment