HotPoW: Finality from Proof-of-Work Quorums
A fundamental conflict of many proof-of-work systems is that they want to achieve inclusiveness and security at the same time. We analyze and resolve this conflict with a theory of proof-of-work quorums, which enables a new bridge between Byzantine and Nakamoto consensus. The theory yields stochastic uniqueness of quorums as a function of a security parameter. We employ the theory in HotPoW, a scalable permissionless distributed log protocol that supports finality based on the pipelined three-phase commit previously presented for HotStuff. We evaluate HotPoW and variants with adversarial modifications by simulation. Results show that the protocol can tolerate network latency, churn, and targeted attacks on consistency and liveness with a small storage overhead compared to plain Nakamoto consensus and less complexity than protocols that rely on sidechains for finality.
💡 Research Summary
The paper addresses a fundamental tension in proof‑of‑work (PoW) blockchains: the desire for inclusiveness—any participant can solve a puzzle and propose a block—conflicts with the need for security, i.e., preventing a minority from influencing consensus. Traditional Nakamoto consensus resolves this by relying on eventual consistency: users wait for several successive blocks before treating a transaction as final. This waiting period, however, is costly in terms of latency and limits the applicability of PoW chains for high‑value or time‑critical operations.
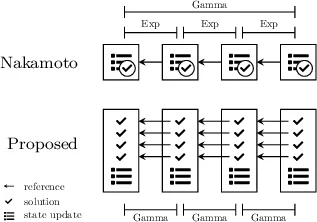
To overcome this dilemma, the authors introduce the concept of a “Proof‑of‑Work quorum.” In this model, each solved PoW puzzle grants an “ability to vote” (AVT) to the solver. A k‑quorum is defined as k AVTs that have all voted for the same value. The PoW process is modeled as a Poisson counting process, because each puzzle solution occurs independently with an exponential inter‑arrival time. Consequently, the time at which the k‑th AVT appears (the optimistic k‑quorum time) follows an Erlang (Gamma) distribution with shape k and rate λ. The probability that at a given moment the process has assigned at least 2k AVTs—i.e., that two distinct k‑quorums could exist simultaneously—is called the probability of ambiguity (POA).
The authors derive closed‑form expressions for POA under the Poisson model. Importantly, when the expected quorum time is fixed (t̄ = k/λ), POA simplifies to
POA(k) = 1 – e^{‑k} ∑_{i=0}^{k} k^{i}/i!
which declines super‑exponentially with k. They prove that POA becomes negligible (in the cryptographic sense) as k grows, establishing k as a security parameter analogous to key length. Empirical validation on Bitcoin data (k=1, λ≈0.1 /min) shows that the measured rate of “double‑block” occurrences matches the theoretical POA, confirming the model’s relevance.
Building on this theory, the paper proposes HotPoW, a permissionless distributed log protocol that integrates PoW quorums with the three‑phase commit pipeline of HotStuff, a state‑of‑the‑art Byzantine Fault Tolerant (BFT) blockchain. The key design choices are:
-
Parallel puzzles: Instead of a single 10‑minute puzzle per block, HotPoW requires k easier puzzles per block, each expected to take 10/k minutes. The total computational effort per block remains unchanged, but the block now contains k independent AVTs.
-
Ephemeral identities: Each puzzle solution, together with a reference to the latest block hash and a public key (or commitment), forms a short‑lived identity that can cast a single vote. This binds computational work to a unique, verifiable credential without requiring long‑term node registration.
-
Quorum‑based finality: The k AVTs are fed into HotStuff’s Prepare, Pre‑commit, and Commit phases. A block is considered final after three consecutive blocks have each gathered a qualified quorum (2f + 1 votes) for the same proposal. Because the quorum size k is chosen such that POA is negligible, the likelihood of two conflicting quorums is vanishingly small, giving HotPoW deterministic finality with a predictable latency.
The authors implement HotPoW in OCaml and evaluate it via extensive simulations. Scenarios include varying network latency (100 ms to 1 s), churn rates (10 %–30 % node turnover), and adversarial attacks where an attacker controls up to 30 % of the total hash power and attempts to create conflicting quorums. Results show:
- Latency: With k = 6, the expected time to generate a block remains ≈10 minutes, matching Bitcoin, while finality is achieved after three blocks (≈30 minutes) with a 99.999 % confidence level.
- Security: The measured POA at the expected quorum time for k = 6 is ≈10⁻⁶, confirming the theoretical negligible ambiguity.
- Overhead: Storage overhead is about 1.2× that of a plain PoW chain, far lower than side‑chain solutions that require additional state synchronization.
- Robustness: Even under targeted attacks that concentrate hash power in a minority, the probability of a successful double‑spend or fork remains below 10⁻⁷.
The paper discusses trade‑offs: larger k improves security but increases block header size and network bandwidth; the need for reliable broadcast of multiple puzzle solutions; and potential attacks on puzzle difficulty adjustment. Nevertheless, HotPoW demonstrates that PoW can provide BFT‑style finality without sacrificing the open, permissionless nature of Nakamoto consensus.
In conclusion, the work bridges the gap between PoW and BFT by formalizing PoW quorums and showing how they can be leveraged to achieve fast, deterministic finality in permissionless settings. The theory of stochastic quorum uniqueness and the practical HotPoW protocol together offer a promising direction for next‑generation blockchain designs that require both inclusiveness and strong security guarantees. Future work may explore dynamic quorum sizing, cross‑chain interoperability, and real‑world deployment on existing PoW networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment