An Image Identification Scheme of Encrypted JPEG Images for Privacy-Preserving Photo Sharing Services
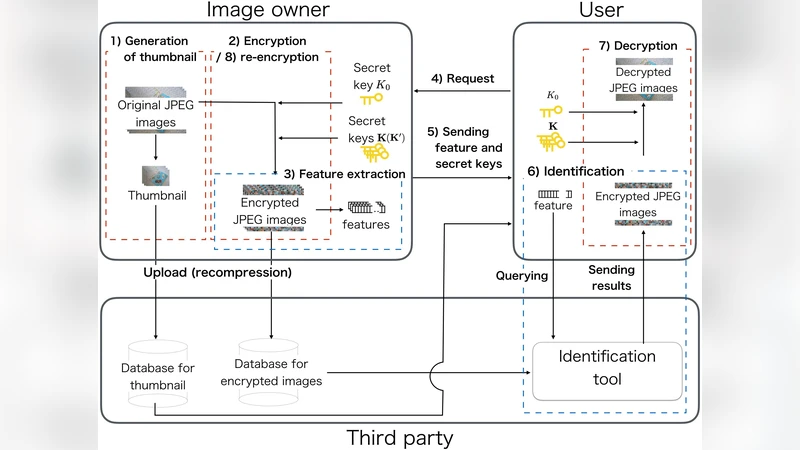
We propose an image identification scheme for double-compressed encrypted JPEG images that aims to identify encrypted JPEG images that are generated from an original JPEG image. To store images without any visual sensitive information on photo sharing services, encrypted JPEG images are generated by using a block-scrambling-based encryption method that has been proposed for Encryption-then-Compression systems with JPEG compression. In addition, feature vectors robust against JPEG compression are extracted from encrypted JPEG images. The use of the image encryption and feature vectors allows us to identify encrypted images recompressed multiple times. Moreover, the proposed scheme is designed to identify images re-encrypted with different keys. The results of a simulation show that the identification performance of the scheme is high even when images are recompressed and re-encrypted.
💡 Research Summary
The paper addresses the problem of identifying encrypted JPEG images that have been uploaded to photo‑sharing services, where the images may be recompressed by the service provider and later re‑encrypted with different keys. Existing Encryption‑then‑Compression (EtC) schemes protect visual content but do not support robust identification after recompression or re‑encryption. To fill this gap, the authors propose a two‑layer block‑scrambling encryption combined with a feature extraction method that is resilient to JPEG compression artifacts.
In the first encryption layer, the whole set of 8×8 blocks is permuted using a secret key K0. In the second layer, only the last M‑N blocks (where M is the total number of blocks and N is a small integer) are permuted again using a different key K1. The first N blocks therefore remain in positions determined solely by K0, regardless of changes to K1, K2, or K3 in later steps. This property enables the same feature vector to be reused even when the image is re‑encrypted with a new second‑layer key set.
For feature extraction, the scheme uses the absolute values of the DC coefficients of the luminance (Y) component from the first N blocks of the encrypted JPEG image. DC coefficients are only weakly affected by block rotation, inversion, and the negative‑positive transform, and they remain relatively stable under JPEG quantization and recompression. Consequently, the N‑dimensional vector v =
Comments & Academic Discussion
Loading comments...
Leave a Comment