Medusa: Blockchain Powered Log Storage System
Blockchain is one of the most heavily invested technologies in recent years. Due to its tamper-proof and decentralization properties, blockchain has become an ideal utility for data storage that is applicable in many real world industrial scenarios. One important scenario is web log, which is treated as sources of technical significance and commercial revenues in major internet companies. In this paper, we illustrate our design of a web log storage system based on HyperLedger. HyperLedger yields higher throughput and lower latency compared with other blockchain systems. Alongside its efficiency advantages, HyperLeger is a permissioned blockchain, which is an ideal fit for enterprise software design scenario.
💡 Research Summary
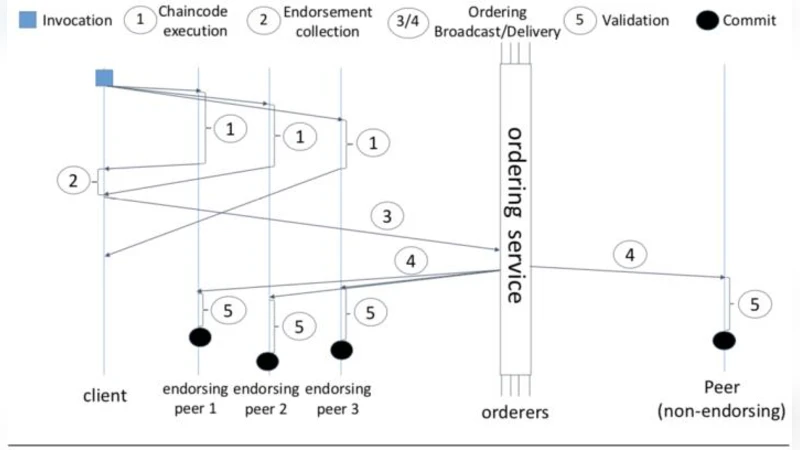
The paper presents “Medusa,” a prototype audit‑log storage system built on the permissioned blockchain platform HyperLedger Fabric. Recognizing that public blockchains such as Bitcoin and Ethereum suffer from high latency and low throughput—making them unsuitable for high‑frequency web‑server logs—the authors focus on low‑frequency, high‑value logs that require strong tamper‑proof guarantees. HyperLedger Fabric’s execute‑order‑validate architecture, which separates transaction execution, ordering, and validation, allows parallel processing and eliminates the costly proof‑of‑work step, thereby achieving thousands of transactions per second and millisecond‑level latency.
The system model is deliberately minimal. There is a single participant type, “DataSource,” representing any entity that produces or consumes audit logs. Each DataSource is identified by a datasourceId and holds connection credentials (IP, port, username, password, URL). The only asset type is “WebLogData,” a simplified representation of a web‑server log entry containing fields such as IP, URL, referer, return code, user‑agent, and timestamp. Log insertion is performed via a “DataAppend” transaction; a chaincode trigger (onDataAppend) writes the payload to the ledger, ensuring immutability. Querying is supported through a selectWebLogData function that can filter by any of the stored attributes, leveraging Fabric’s built‑in query capabilities.
Implementation details note that the chaincode was authored with HyperLedger Composer and deployed on a Fabric network running in Docker containers. The authors emphasize that, because the blockchain enforces immutability, only two operations—append and query—are needed, simplifying the design compared with traditional log storage solutions (e.g., ElasticSearch, HDFS) that must handle updates, deletions, and complex indexing.
Related work discusses the evolution of consensus protocols, the distinction between permissionless and permissioned ledgers, and prior attempts to use blockchain for log integrity (e.g., “Log chain”). The authors argue that Medusa’s contribution lies in applying HyperLedger’s permissioned model to audit‑log storage, exploiting its higher throughput and native access‑control features.
The conclusion acknowledges that while HyperLedger improves performance relative to public chains, it still lags behind mature centralized log platforms in raw speed and scalability. The paper therefore positions Medusa as a proof‑of‑concept for secure, tamper‑evident log archiving, with future work aimed at achieving ElasticSearch‑level throughput, implementing compression or archiving strategies, and extending the system to handle high‑frequency web‑server logs.
Overall, the paper offers a clear architectural description of a blockchain‑backed log storage system, highlights the suitability of permissioned ledgers for audit scenarios, but falls short on empirical performance evaluation and scalability analysis. It serves as an initial step toward integrating blockchain immutability guarantees into enterprise log management workflows.
Comments & Academic Discussion
Loading comments...
Leave a Comment