Blockchain access control Ecosystem for Big Data security
In recent years, the advancement in modern technologies has experienced an explosion of huge data sets being captured and recorded in different fields, but also given rise to concerns the security and protection of data storage, transmission, processing, and access to data. The blockchain is a distributed ledger that records transactions in a secure, flexible, verifiable and permanent way. Transactions in a blockchain can be an exchange of an asset, the execution of the terms of a smart contract, or an update to a record. In this paper, we have developed a blockchain access control ecosystem that gives asset owners the sovereign right to effectively manage access control of large data sets and protect against data breaches. The Linux Foundation’s Hyperledger Fabric blockchain is used to run the business network while the Hyperledger composer tool is used to implement the smart contracts or transaction processing functions that run on the blockchain network.
💡 Research Summary
The paper addresses the growing security and privacy challenges associated with big‑data storage, transmission, processing, and access in cloud environments. Using the Plant Phenotyping and Imaging Research Centre (P2IRC) project as a motivating example, the authors illustrate how multiple research groups must share heterogeneous datasets (genomic sequences, phenotypic images, etc.) while preserving data ownership and confidentiality.
After outlining five major security concerns—privacy preservation, authentication and authorization, identity and access management, data ownership, and policy management—the authors propose a blockchain‑based access‑control ecosystem built on Hyperledger Fabric and Hyperledger Composer. Fabric provides a permissioned ledger with Membership Service Provider (MSP) based identity management, channel isolation, and chaincode execution. Composer is used to model the business network, defining participants (persons, organizations), assets (data), and six transaction types (request, grant, revoke, verify, view, plus the implicit historian).
Two complementary access‑control models are implemented:
-
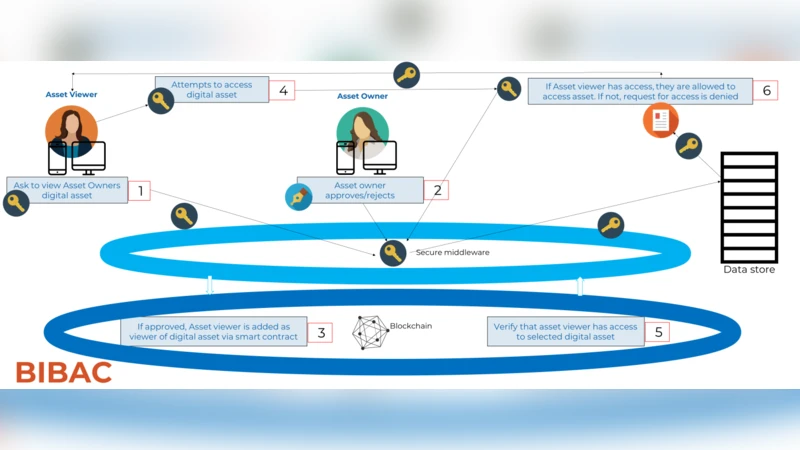
Identity‑Based Access Control (IBAC, called BIBAC) – Each user possesses a digital certificate. When a user requests access to a data asset, the asset owner issues a “grant” transaction; the owner can later issue a “revoke” transaction. Verification and view operations are performed by submitting signed transactions that the chaincode validates against the ledger’s immutable history. All actions are recorded in the Fabric historian, providing transparent audit trails.
-
Role‑Based Access Control (RBAC, called BRBAC) – Organizations define roles and associate each role with specific data assets. Role assignments are managed by the organization’s key. When a user attempts to view an asset, a smart contract checks whether the user’s role is permitted for that asset and either grants or denies access. This model scales better for large user bases and aligns with traditional enterprise RBAC practices.
Crucially, the actual big‑data payload is not stored on the blockchain; it remains in an existing Apache Cassandra cluster. The blockchain functions solely as a trusted verification layer and audit log, dramatically reducing storage costs and avoiding the performance penalties of on‑chain data replication.
The authors evaluate two architectural alternatives: (a) storing data directly on the blockchain, which would require costly migration and parallel operation with legacy stores, and (b) using the blockchain only as an access‑control verifier, which they adopt. The second approach offers a low entry barrier for organizations, preserves existing data infrastructures, and still delivers the benefits of immutability, decentralised trust, and tamper‑evident logging.
Discussion highlights the trade‑offs of a permissioned network: while MSP‑based identity management and channel isolation enhance security, they also introduce complexity in membership onboarding and network governance. Transaction throughput is lower than public blockchains, but sufficient for typical access‑control workloads.
In conclusion, the paper demonstrates that a Hyperledger‑Fabric‑backed ecosystem can provide robust, auditable, and flexible access control for big‑data environments, safeguarding data ownership and privacy without sacrificing scalability. Future work includes performance optimisation, cross‑chain interoperability, and integration of advanced privacy‑preserving techniques such as zero‑knowledge proofs.
Comments & Academic Discussion
Loading comments...
Leave a Comment