Temporal Logic Verification of Stochastic Systems Using Barrier Certificates
This paper presents a methodology for temporal logic verification of discrete-time stochastic systems. Our goal is to find a lower bound on the probability that a complex temporal property is satisfied by finite traces of the system. Desired temporal…
Authors: Pushpak Jagtap, Sadegh Soudjani, Majid Zamani
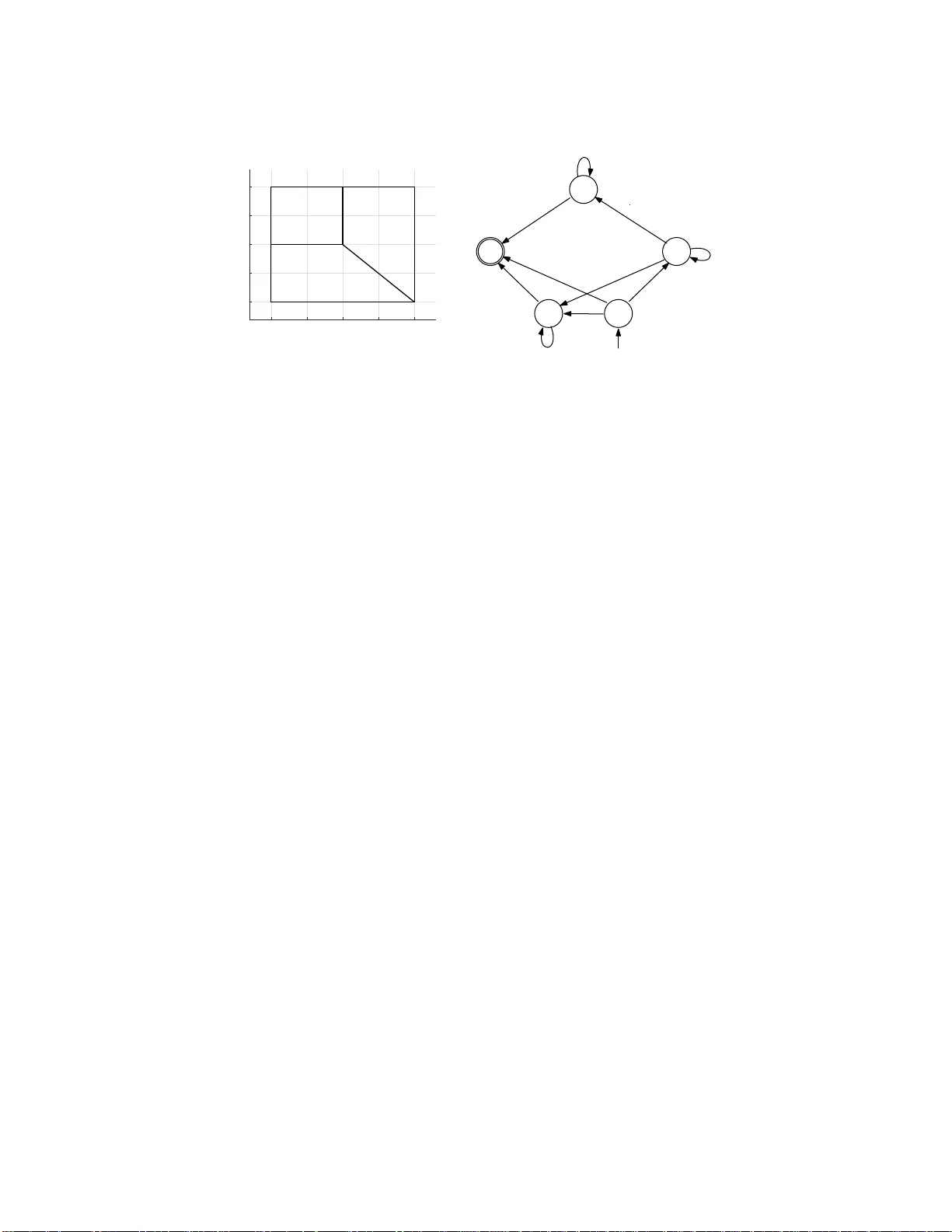
T emp oral Logic V erification of S to c hastic Systems Using Barrier Certificates ⋆ Pushpak Jagtap 1 , Sadegh Soudjani 2 , and Ma jid Zamani 1 1 T ec hnical Universit y of Munich, Germany { pushpak. jagtap,zam ani } @tum.de 2 New castle Universit y , United Kingdom Sadegh.Sou djani@ncl .ac.uk Abstract. T his pap er presents a m eth odology for t emp oral logic verification of discrete-time stochastic systems. Our goal is to find a lo w er b ound on th e probabilit y that a complex temp oral prop ert y is satisfied by finite traces of the sy stem. Desired temp ora l prop erties of th e sy stem are exp ressed u si ng a fragmen t of linear temp oral logic, ca lled safe L TL over fini te tr ac es . W e propose to use barrier certificates for com- putations of such lo w er b ounds, whic h is computationally muc h more efficient than the existing discretization-based approaches. The new approac h is discretization-free and do es not suff er from the curse of dimensionalit y caused by discretizing state sets. The prop osed approach relies on d ecomp osing the negation of t he specification into a union of sequentia l reachabilities and then u si ng barrier certificates to comput e upp er b ounds for these reachabilit y probabilities. W e demonstrate the effective ness of the prop ose d approach on case studies with linear and p olynomial dynamics. 1 In tro duction V erification of dynamical systems against co mplex sp ecifications has gained s ignifican t at- ten tion in la st few decades [3,29]. The verification task is challenging for contin uous-space dynamical systems under uncertainties and is har d to b e per formed exa ctly . Ther e hav e been several results in the liter ature utilizing approximate finite models (a.k.a. abstractions ) for verification of sto c hastic dynamical sy s tems. Examples include re sults on verification of discrete-time sto c hastic hybrid systems against pr obabilistic in v ar iance [25,23] and linear tempo ral logic sp ecifications [1,30] using Markov chain abstr actions. V erification o f discre te- time sto c hastic switch ed systems ag ainst probabilistic computationa l tree logic formulae is discussed in [14] using int erv al Marko v chains as abstract models. How ev er, these abstraction techn iques ar e based on s tate set discr e tization and face the issue of discrete state explos ion. This sca labilit y issue is only partly mitiga ted in [24,15] bas ed on comp ositional abstr action of sto c hastic sy stems. On the other hand, a discr etization-free appro ac h, based on b arrier c ert ific ates , has been used for verifying sto chastic systems against simple temp oral pr o perties such a s s afet y and reachabilit y . Employing barrier certifica tes for sa fet y verification of sto chastic sy s tems is initially prop osed in [19]. Similar r esults are rep orted in [32] for switched diffusion pro cesses ⋆ This w ork w as supp orted in p art by the German Research F ound atio n (DFG) through the grant ZA 873/1-1 and th e TUM I n ternational Graduate School of Science and Engineering ( IGSSE). and pie c ewise-deterministic Markov pr ocesses . The res ults in [9] prop ose a probabilistic bar- rier certifica te to co mput e b ounds on the proba bilit y that a s tochastic h ybrid system reaches unsafe regio n. Howev er, in or de r to provide infinite time hor izon guara n tees, all of these r e- sults requir e an as sumption that the bar r ier c ertificates exhibit su p ermartingale prop ert y which in turns pre suppose sto c hastic stability and v anishing noise at the equilibrium p oin t of the s ystem. In this work, we consider the problem of verifying discrete-time sto chastic sys tems a gainst complex specifica tions o v er finite time ho rizons without requiring any ass umpt ion on the sta- bilit y of the system. This is achiev ed by relaxing sup ermartingale condition to c -martingale as also utilized in [27]. C o rrespo ndingly , instead of infinite-horizon specifica tions, we consider finite-horizon temp oral sp ecifications, w hich are mor e practica l in the r eal life a pplications including motion planning problems [22,16,2]. In spirit, this work extends the idea of combin- ing automa ta r epresen tation of the sp ecification a nd bar rier certificates , which is prop osed in [33] for non-sto c hastic dynamics, in or der to verify sto chastic s ystems agains t sp ecifica- tions ex pressed as a fra gmen t of L TL for m ulae, na mely , safe L TL on finite traces. Our work also has the s a me flavour as [6], but in a co mpletely different s ettin g, in combining barr ier certificates to gua ran tee s atisfaction of tempor al sp ecifications. T o the b est of our knowledge, this pap er is the first one to use bar rier certificates for alg o- rithmic verification of sto c hastic sys tems aga inst a wide cla ss of temp oral prop erties. Our main co n tribution is to provide a s ystematic approach for computing low er b ounds o n the probability that the discrete-time sto chastic system satisfies given safe L TL s pecification ov er a finite time horizon. This is achiev ed by fir st dec o mposing sp ecification into a s e- quence of simpler verification task s based on the structure o f the automaton a ssocia ted with the negation of the sp ecification. Next, we use barrier cer tificates for computing probabil- it y bounds for simpler verification tas k s whic h a re further combined to get a (p oten tially conserv ativ e) low er b ound on the pr obabilit y of satisfying the orig inal sp ecification. The ef- fectiveness of the pr oposed approa c h is demonstrated using several ca se studies with linear and p olynomial dynamics. 2 Preliminaries 2.1 Notations W e denote the set of no nnegativ e integers by N 0 := { 0 , 1 , 2 , . . . } and the set of p ositiv e int egers by N := { 1 , 2 , 3 , . . . } . The symbols R , R + , and R + 0 denote the set of r eal, p ositive, a nd nonnegative r eal n um ber s, r espectively . W e use R n × m to deno te the space of real ma trices with n r o ws a nd m columns. W e c o nsider a pro babilit y space ( Ω , F Ω , P Ω ) where Ω is the sample space, F Ω is a sigma- algebra on Ω compr ising the subset o f Ω as even ts, and P Ω is a probability mea s ure that assigns probabilities to event s. W e assume tha t ra ndom v ariables intro duce d in this a rticle are measura ble functions o f the form X : ( Ω , F Ω ) → ( S X , F X ) as P rob { A } = P Ω { X − 1 ( A ) } for any A ∈ F X . W e often directly discuss the pro babilit y measur e on ( S X , F X ) without explicitly ment ioning the underly ing probability space a nd the function X itself. 2.2 Discrete-time s to c hastic systems In this work, we consider discrete-time sto c hastic systems g iv en b y a tuple S = ( X , V w , w , f ), where X and V w are Bore l spaces representing state a nd uncer tain t y space s of the sy stem. W e denote by ( X , B ( X )) the measur able spa ce with B ( X ) be ing the Bor el sig ma-algebra on the state s pace. Notation w denotes a sequence of indep endent and identically distributed (i.i.d.) ra ndo m v ariables on the set V w as w := { w ( k ) : Ω → V w , k ∈ N 0 } . The ma p f : X × V w → X is a measura ble function characterizing the state evolution of the s ystem. F or a given initial state x (0) ∈ X , the s tate evolution can b e written as x ( k + 1) = f ( x ( k ) , w ( k )) , k ∈ N 0 . (1) W e deno te the solution pr o c ess genera ted ov er N time steps by x N = x (0) , x (1) , . . . , x ( N − 1). The sequence w together with the measura ble function f induce a unique pro babilit y measure on the sequence s x N . W e are interested in computing a lo w er bo und on the proba bilit y that s ystem S = ( X , V w , w , f ) satisfies a sp ecification expr essed as a temp oral logic prop ert y . W e provide syntax and se- mantics o f the class of sp ecifications dea lt with in this pap er in the next s ubsection. 2.3 Linear tem poral lo gic ov er finite traces In this subsection, we introduce linear temp oral log ic over finite traces, referred to a s L TL F [4]. L TL F uses the s ame syntax of L TL over infinite tra ces given in [3]. The L TL F formulas ov er a set Π of atomic prop ositions ar e obtained as follows: ϕ ::= true | p | ¬ ϕ | ϕ 1 ∧ ϕ 2 | ϕ 1 ∨ ϕ 2 | ϕ | ♦ ϕ | ϕ | ϕ 1 U ϕ 2 , where p ∈ Π , is the next op erator, ♦ is even tually , is alwa ys, a nd U is un til. The semantics of L TL F is given in terms of fin ite tr ac es , i.e. , finite words σ , denoting a finite non-empty sequence of consecutive steps over Π . W e use | σ | to repr esen t the length o f σ a nd σ i as a prop ositional interpretation at i th po sition in the tra ce, whe r e 0 ≤ i < | σ | . Giv en a finite tra ce σ and an L TL F formula ϕ , we inductively define when an L TL F formula ϕ is true a t the i th step (0 ≤ i < | σ | ), deno ted by σ, i | = ϕ , a s fo llo ws: – σ, i | = true; – σ, i | = p , for p ∈ Π iff p ∈ σ i ; – σ, i | = ¬ ϕ iff σ , i 6| = ϕ ; – σ, i | = ϕ 1 ∧ ϕ 2 iff σ , i | = ϕ 1 and σ, i | = ϕ 2 ; – σ, i | = ϕ 1 ∨ ϕ 2 iff σ , i | = ϕ 1 or σ , i | = ϕ 2 ; – σ, i | = ϕ iff i < | σ | − 1 and σ, i + 1 | = ϕ ; – σ, i | = ♦ ϕ iff for s ome j s uc h that i ≤ j < | σ | , we have σ, j | = ϕ ; – σ, i | = ϕ iff for a ll j such that i ≤ j < | σ | , we hav e σ, j | = ϕ ; – σ, i | = ϕ 1 U ϕ 2 iff for some j such that i ≤ j < | σ | , we have σ, j | = ϕ 2 , a nd for all k s.t. i ≤ k < j , we hav e σ , k | = ϕ 1 . The formula ϕ is tr ue o n σ , denoted by σ | = ϕ , if and only if σ , 0 | = ϕ . W e denote the language of such finite traces a s sociated with L TL F formula ϕ by L ( ϕ ). Notice that in this case we a lso hav e the usual b oolea n equiv a le nc e s such as ϕ 1 ∨ ϕ 2 ≡ ¬ ( ¬ ϕ 1 ∧ ¬ ϕ 2 ), ϕ 1 = ⇒ ϕ 2 ≡ ¬ ϕ 1 ∨ ϕ 2 , ♦ ϕ ≡ true U ϕ , and ϕ ≡ ¬ ♦ ¬ ϕ . In this pap er, we consider only s afet y prop erties [1 2]. Hence, we use a subset of L TL F called safe L TL F as intro duced in [22] a nd defined as follows. Definition 1. A n L TL F formula is c al le d a safe L TL F formula if it c an b e r epr esente d in p ositive normal form, i.e., ne gatio ns only o c cur adjac ent to atomic pr op ositions, using the temp o r a l op er ators next ( ) and always ( ) . Next, we define deterministic finite automata which later serve as equiv alen t representations of L TL F formulae. Definition 2. A deterministic finite automaton ( DF A ) is a tuple A = ( Q, Q 0 , Σ , δ, F ) , wher e Q is a fin ite set of states, Q 0 ⊆ Q is a set of initial states, Σ is a finite set ( a.k.a. alphab et ) , δ : Q × Σ → Q is a tr ansition funct io n, and F ⊆ Q is a set of ac c epting states. W e use nota tion q σ − → q ′ to denote transition rela tion ( q , σ, q ′ ) ∈ δ . A finite word σ = ( σ 0 , σ 1 , . . . , σ n − 1 ) ∈ Σ n is a ccepted by a DF A A if there e x ists a finite state run q = ( q 0 , q 1 , . . . , q n ) ∈ Q n +1 such tha t q 0 ∈ Q 0 , q i σ i − → q i +1 for all 0 ≤ i < n a nd q n ∈ F . The accepted la nguage of A , deno ted by L ( A ), is the set of a ll words accepted by A . According to [5], every L TL F formula ϕ ca n be transla ted to a DF A A ϕ that ac c epts the same language as ϕ , i.e. , L ( ϕ ) = L ( A ϕ ). Suc h A ϕ can be co nstructed explicitly or symbolica lly using ex isting to ols, such as SPOT [7] a nd MONA [8]. R emark 1. F or a given L TL F formula ϕ ov er atomic prop ositions Π , the a ssocia ted DF A A ϕ is usually co nstructed ov er the alphab et Σ = 2 Π . Solution pro cess of a system S is also connected to the set of words by a la beling function L from the state s pace to the a lphabet Σ . Without loss o f gener a lit y , we w ork with the set of atomic prop ositions directly as the alphab et rather than its power set. Prop ert y satisfaction b y the s olution pro cess. F or a g iv en discrete-time sto c ha stic system S = ( X , V w , w , f ) with dynamics (1), finite-time s olution pro cesses x N are co nnected to L TL F formulae with the help of a measur a ble la beling function L : X → Π , where Π is the set o f ato mic pr opositions. Definition 3. F or a sto chastic system S = ( X , V w , w , f ) and lab eling function L : X → Π , a finite se quenc e σ x N = ( σ 0 , σ 1 , . . . , σ N − 1 ) ∈ Π N is a finite tra c e of the solution pr o c ess x N = x (0) , x (1) , . . . , x ( N − 1) of S if we have σ k = L ( x ( k )) for al l k ∈ { 0 , 1 , . . . , N − 1 } . Next, w e define the pr obabilit y that the discr ete-time sto ch astic system S satisfies safe L TL F formula ϕ ov er traces of length | σ | = N . Definition 4. L et T r ace N ( S ) b e the set of al l finite tr ac es of solution pr o c ess es of S with length | σ x N | = N and ϕ b e a s afe L TL F formula over Π . Then P { T r ace N ( S ) | = ϕ } is the pr ob ability t ha t ϕ is satisfie d by discr ete-t i me sto chastic system S over a fi nite t ime horizon [0 , N ) ⊂ N 0 . -10 -5 0 5 10 x 1 -10 -5 0 5 10 x 2 X 2 X 0 X 1 X 3 (a) q 2 q 0 q 1 q 3 q 4 p 0 p 2 : p 2 p 1 p 1 p 2 : p 1 p 1 _ p 3 p 2 p 0 _ p 3 (b) Fig. 1. ( a) State space and regions of in t erest for Example 1, (b) DF A A ¬ ϕ that accepts all traces satisfying ¬ ϕ where ϕ is given in (3 ). R emark 2. The set o f a to mic prop ositions Π = { p 0 , p 1 , . . . , p M } and the lab eling function L : X → Π provide a mea surable partition of the state s pace X = ∪ M i =1 X i as X i := L − 1 ( p i ). Without lo ss of generality , we ass umed that X i 6 = ∅ for any i . 2.4 Problem fo rmulation Pr oblem 1. Giv en a system S = ( X , V w , w , f ) with dyna mics (1), a safe L TL F sp ecification ϕ of length N ov er a set Π = { p 0 , p 1 , . . . , p M } of atomic prop ositions, and a lab eling function L : X → Π , compute a lower b ound o n the pro babilit y that the traces of s o lution pr ocess of S of length N satisfies ϕ , i.e. , a quantit y ϑ such that P { T r ace N ( S ) | = ϕ } ≥ ϑ . Note that ϑ = 0 is a trivial lower bound, but we a re lo oking at computation of low er b ounds that a r e as tight as p ossible. F or finding a solution to Problem 1, we first compute an upper bound on the proba bilit y P { T r ace N ( S ) | = ¬ ϕ } . This is done b y constructing a DF A A ¬ ϕ = ( Q, Q 0 , Π , δ, F ) that accepts all finite w o rds over Π that sa tisfies ¬ ϕ . Example 1. Consider a tw o-dimensio na l sto chastic system S = ( X , V w , w , f ) with X = V w = R 2 and dynamics x 1 ( k + 1) = x 1 ( k ) − 0 . 01 x 2 2 ( k ) + 0 . 1 w 1 ( k ) , x 2 ( k + 1) = x 2 ( k ) − 0 . 01 x 1 ( k ) x 2 ( k ) + 0 . 1 w 2 ( k ) , (2) where w 1 ( · ), w 2 ( · ) are independent standa rd normal r andom v a riables. Let the regions of int e r est be g iv en as X 0 = { ( x 1 , x 2 ) ∈ X | x 1 ≥ − 10 , − 10 ≤ x 2 ≤ 0 , and x 1 + x 2 ≤ 0 } , X 1 = { ( x 1 , x 2 ) ∈ X | 0 ≤ x 1 ≤ 10 , x 2 ≤ 10 , and x 1 + x 2 ≥ 0 } , X 2 = { ( x 1 , x 2 ) ∈ X | − 1 0 ≤ x 1 ≤ 0 a nd 0 ≤ x 2 ≤ 10 } , and X 3 = X \ ( X 0 ∪ X 1 ∪ X 2 ) . The sets X 0 , X 1 , X 2 , and X 3 are shown in Figur e 1(a). The set o f atomic pro positions is given by Π = { p 0 , p 1 , p 2 , p 3 } , with labeling function L ( x ) = p i for an y x ∈ X i , i ∈ { 0 , 1 , 2 , 3 } . W e a re interested in co mputing a lower b ound on the proba bilit y that T race N ( S ) of length N satisfies the following sp ecification: – Solution pro cess sho uld start in either X 0 or X 2 . If it star ts in X 0 , it will always stay aw ay fr o m X 1 or always stay aw ay from X 2 . If it star ts in X 2 , it will always stay awa y from X 1 within time hor izon [0 , N ) ⊂ N 0 . This prop ert y can b e ex pr essed by the safe L TL F formula ϕ = ( p 0 ∧ ( ¬ p 1 ∨ ¬ p 2 )) ∨ ( p 2 ∧ ¬ p 1 ) . (3) The DF A cor responding to the negation of the safe L TL F formula ϕ in (3) is shown in Fig ure 1(b). ⊓ ⊔ Next, we pro vide a systematic approa c h to solve Pr oblem 1 b y combining automata and bar- rier certificates introduce d in the next section. W e intro duce the notio n of barrier c e r tificate similar to the one used in [19] and show how to use it for s olving Pro blem 1 in Sections 4-5. 3 Barrier Cert ifica te W e r e c all that a function B : X → R is a sup ermartingale for system S = ( X , V w , w , f ) if E [ B ( x ( k + 1)) | x ( k )] ≤ B ( x ( k )) , ∀ x ( k ) ∈ X , k ∈ N 0 , where the exp ectation is with resp ect to w ( k ). This inequality requires that the exp ected v a lue of B ( x ( · )) doe s not increa ses as a function of time. T o provide results for finite time horizon, we instead use a relaxa tion of supe rmartingale condition called c-martingale . Definition 5. F unction B : X → R is a c-martingale for syst em S = ( X , V w , w , f ) if it satisfies E [ B ( x ( k + 1)) | x ( k )] ≤ B ( x ( k )) + c, ∀ x ( k ) ∈ X , k ∈ N 0 , with c ≥ 0 b eing a non- n e gative c onstant . W e provide the following lemma and use it in the seque l. This lemma is a direct consequence of [13, Theor em 1 ] and is also utilized in [27, Theor e m II.1 ]. Lemma 1. L et B : X → R + 0 b e a non-n e gative c-martingale for system S . Then for any c onstant λ > 0 and any initial c ondition x 0 ∈ X , P { sup 0 ≤ k ≤ T d B ( x ( k )) ≥ λ | x (0) = x 0 } ≤ B ( x 0 ) + cT d λ . (4) Next theor em provides inequalities o n a barr ier certifica te that gives an upp er b ound on reachabilit y pr obabilities. This theor em is inspired by the res ult of [19, Theo rem 1 5 ] that uses s upermartinga les for reachability analysis of contin uous-time sys tems. Theorem 1. Consider a discr ete-t ime st o chastic system S = ( X , V w , w , f ) and sets X 0 , X 1 ⊆ X . Supp ose t her e exist a non-n e gative function B : X → R + 0 and c onstants c ≥ 0 and γ ∈ [0 , 1] su ch t ha t B ( x ) ≤ γ ∀ x ∈ X 0 , (5) B ( x ) ≥ 1 ∀ x ∈ X 1 , (6) B ( x ) is c-martingale ∀ x ∈ X . (7) Then the pr ob ability t hat the solution pr o c ess x T d of S starts fr om initial state x (0) ∈ X 0 and r e aches X 1 within time horizon [0 , T d ] ⊂ N 0 is upp er b ounde d by γ + cT d . Pr o of. Since B ( x ( k )) is non-neg ativ e and c -martinga le , we conclude that (4) in Lemma 1 holds. Now using (5) a nd the fact that X 1 ⊆ { x ∈ X | B ( x ) ≥ 1 } , we hav e P { x ( k ) ∈ X 1 for s ome 0 ≤ k ≤ T d | x (0) = x 0 } ≤ P { sup 0 ≤ k ≤ T d B ( x ( k )) ≥ 1 | x (0) = x 0 } ≤ B ( x 0 ) + cT d ≤ γ + cT d . This concludes the pro of. ⊓ ⊔ Theorem 1 enables us to formulate a n optimization pro blem by minimizing the v alue of γ and c in or der to find an upp er bo und for finite-ho rizon reachabilit y that is as tight as po ssible. In the next section, we discuss how to tra nslate L TL F verification problem into the compu- tation of a c ollection o f barr ier certificates each satisfying inequalities o f the for m (5)-(7). Then w e show in Section 5 how to use Theor em 1 to pr o vide a low e r b ound on the probability of satisfying L TL F sp ecifications ov er finite time hor izon. 4 Decomp osition into Sequential Reac habilit y Consider a DF A A ¬ ϕ = ( Q, Q 0 , Π , δ, F ) that accepts a ll finite words o f length n ∈ [0 , N ] ⊂ N 0 ov er Π that sa tisfy ¬ ϕ . Self-lo ops in the DF A play a central ro le in our decomp osition. Let Q s ⊆ Q b e a se t of s tates of A ¬ ϕ having self-lo ops, i.e. , Q s := { q ∈ Q | ∃ p ∈ Π, q p − → q } . Accepting state run o f A ¬ ϕ . Sequence q = ( q 0 , q 1 , . . . , q n ) ∈ Q n +1 is ca lled an acc epting state run if q 0 ∈ Q 0 , q n ∈ F , and there exist a finite word σ = ( σ 0 , σ 1 , . . . , σ n − 1 ) ∈ Π n such that q i σ i − → q i +1 for a ll i ∈ { 0 , 1 , . . . , n − 1 } . W e denote the se t of such finite w o rds by σ ( q ) ⊆ Π n and the se t of accepting runs by R . W e als o indicate the length of q ∈ Q n +1 by | q | , which is n + 1. Let R ≤ N +1 be the set of all finite ac c epting state runs of lengths less than o r equal to N + 1 excluding s elf-loops, R ≤ N +1 := { q = ( q 0 , q 1 , . . . , q n ) ∈ R | n ≤ N , q i 6 = q i +1 , ∀ i < n } . (8) Computation of R ≤ N +1 can b e do ne efficiently us ing algor ithms in graph theory by viewing A ¬ ϕ as a directed gr aph. Consider G = ( V , E ) as a directed gra ph with vertices V = Q and edges E ⊆ V × V such that ( q , q ′ ) ∈ E if and only if q ′ 6 = q and ther e exist p ∈ Π such that q p − → q ′ . F rom the constr uction of the g raph, it is o b vious that the finite path in the g raph of leng th n + 1 star ting from vertices q 0 ∈ Q 0 and e nding at q F ∈ F is an ac c epting s ta te Algorithm 1 Computation of sets P ( q ), q ∈ R ≤ N +1 Require: G , Q s , N 1: Compute set R ≤ N +1 by depth fi rst searc h on G 2: for a ll q ∈ R ≤ N +1 and | q | ≥ 3 do 3: for i = 1 t o | q | − 3 do 4: P 1 ( q ) ← { ( q i , q i +1 , q i +2 ) } 5: if q i +1 ∈ Q s then 6: P ( q ) ← { ( q i , q i +1 , q i +2 , N + 2 − | q | ) } 7: else 8: P ( q ) ← { ( q i , q i +1 , q i +2 , 1) } return P ( q ) run q of A ¬ ϕ without a ny self-lo op thus b elongs to R ≤ N +1 . Then one can eas ily co mpute R ≤ N +1 using v ar ian ts of depth first sear c h algo rithm [21]. Decomp osition in to sequen tia l rea c hability is p erformed a s follows. F or any q = ( q 0 , q 1 , . . . , q n ) ∈ R ≤ N +1 , w e define P ( q ) as a set of all state runs of length 3 augmented with a horizon, P ( q ) := { ( q i , q i +1 , q i +2 , T ( q , q i +1 )) | 0 ≤ i ≤ n − 2 } , (9) where the hor izon is defined as T ( q , q i +1 ) = N + 2 − | q | for q i +1 ∈ Q s and 1 otherwise . R emark 3. Note that P ( q ) = ∅ for | q | = 2. In fa c t, a n y accepting state r un of length 2 sp ecifies a subset of the s tate space such that the system satisfies ¬ ϕ whenever it star ts from that subset. This gives trivial zer o probability fo r satisfying the s p ecification, thus neglected in the sequel. The computation of sets P ( q ), q ∈ R ≤ N +1 , is illustrated in Algorithm 1 and demonstrated below for our demo example. Example 1. (contin ued) F or s a fe L TL F formula ϕ given in (3 ), Figure 1(b) shows a DF A A ¬ ϕ that a c c epts all words that satisfy ¬ ϕ . F rom Figure 1(b), we ge t Q 0 = { q 0 } and F = { q 3 } . W e consider traces o f ma xim um leng th N = 5 . T he set of accepting state r uns of lengths a t most N + 1 without self-lo ops is R ≤ 6 = { ( q 0 , q 4 , q 3 ) , ( q 0 , q 1 , q 2 , q 3 ) , ( q 0 , q 1 , q 4 , q 3 ) , ( q 0 , q 3 ) } . The set o f states with self-lo ops is Q s = { q 1 , q 2 , q 4 } . Then the sets P ( q ) for q ∈ R ≤ 6 are as follows: P ( q 0 , q 3 ) = ∅ , P ( q 0 , q 4 , q 3 ) = { ( q 0 , q 4 , q 3 , 4) } , P ( q 0 , q 1 , q 2 , q 3 ) = { ( q 0 , q 1 , q 2 , 3) , ( q 1 , q 2 , q 3 , 3) } , P ( q 0 , q 1 , q 4 , q 3 ) = { ( q 0 , q 1 , q 4 , 3) , ( q 1 , q 4 , q 3 , 3) } . F or every q ∈ R ≤ 6 , the corr esponding finite words σ ( q ) a re listed as follows: σ ( q 0 , q 3 ) = { p 1 ∨ p 3 } , σ ( q 0 , q 4 , q 3 ) = { ( p 2 , p 1 ) } , σ ( q 0 , q 1 , q 2 , q 3 ) = { ( p 0 , p 1 , p 2 ) } , σ ( q 0 , q 1 , q 4 , q 3 ) = { ( p 0 , p 2 , p 1 ) } . ⊓ ⊔ 5 Computation of Probabilities Using Barrier Cert ificates Having the s et of state runs of length 3 augmented with horizon, in this section, we provide a systematic appr oac h to compute a lower b ound o n the probability that the solution proce s s of S satisfies ϕ . Given DF A A ¬ ϕ , our appr oac h relies on p erforming a rea c hability co mput a tion ov er each element of P ( q ), q ∈ R ≤ N +1 , whe r e reachability pr obabilit y is upp er bo unded using ba rrier certificates. Next theorem provides an upp er b ound o n the probability that the solution pro cess of the system s a tisfies the spe c ification ¬ ϕ . Theorem 2. F or a given safe L TL F sp e cific ation ϕ , let A ¬ ϕ b e a D F A c orr esp onding to its ne gation, R ≤ N +1 b e the set of ac c epting state runs of length at most N + 1 as define d in (8) , and P b e the set of runs of length 3 augmente d with horizon as define d in (9 ) . Then the pr ob ability t ha t the system satisfies ¬ ϕ within time horizon [0 , N ] ⊆ N 0 is u pp er b ounde d by P { T ra ce N ( S ) | = ¬ ϕ } ≤ X q ∈R ≤ N +1 Y { ( γ ν + c ν T ) | ν = ( q , q ′ , q ′′ , T ) ∈ P ( q ) } , (10) wher e γ ν + c ν T is the u pp er b ound on the pr ob ability of the tr aje ctories of S starting fr om X 0 := L − 1 ( σ ( q, q ′ )) and r e aching X 1 := L − 1 ( σ ( q ′ , q ′′ )) within time horizon [0 , T ] ⊆ N 0 c ompute d via The or em 1. Pr o of. Consider an a ccepting run q ∈ R ≤ N +1 and set P ( q ) as defined in (9). F or a n elemen t ν = ( q , q ′ , q ′′ , T ) ∈ P ( q ), the upp er b ound o n the probability of tr a jectories of S stating from L − 1 ( σ ( q, q ′ )) and reaching L − 1 ( σ ( q ′ , q ′′ )) within time horizon T is given by γ ν + c ν T . This fo llows from Theorem 1. Now the upp er b ound o n the probability of the trace of the solution pro cess rea c hing ac c epting state following tra ce cor responding to q is given by the pro duct of the probability b ounds corresp onding to all elements ν = ( q , q ′ , q ′′ , T ) ∈ P ( q ) and is given by P { σ x N ( q ) | = ¬ ϕ } ≤ Y { ( γ ν + c ν T ) | ν = ( q , q ′ , q ′′ , T ) ∈ P ( q ) } . (11) Note that, the wa y we computed time horizo n T d , we alwa ys get the upper bo und for the probabilities for all p ossible combinations of s e lf-loops for accepting state runs of length less than or e qual to N + 1. The upp er bound on the proba bilit y tha t the solution pro cesses of system S violate ϕ ca n be computed by summing the probability b ounds for all p ossible accepting runs a s computed in (11) and is given by P { T ra ce N ( S ) | = ¬ ϕ } ≤ X q ∈R ≤ N +1 Y { ( γ ν + c ν T ) | ν = ( q , q ′ , q ′′ , T ) ∈ P ( q ) } . ⊓ ⊔ Theorem 2 enables us to decomp ose the c o mputation int o a collection of sequential rea c ha- bilit y , c ompute bo unds on the rea c hability probabilities using Theorem 1 , and then combine the bounds in a sum-pro duct expres s ion. R emark 4. In case we ar e unable to find barrier certificates for some of the elemen ts ν ∈ P ( q ) in (10), we r eplace the rela ted term ( γ ν + c ν T ) b y the p essimistic b ound 1. In order to get a non-trivial b ound in (10), a t least one ba rrier certificate must b e found for each q ∈ R ≤ N +1 . Corollary 1. Give n the r esult of The or em 2, the pr ob ability t h at the tr aje ctories of S of length N satisfies safe L TL F sp e cific ation ϕ is lower-b ounde d by P { T ra ce N ( S ) | = ϕ } ≥ 1 − P { T r ace N ( S ) | = ¬ ϕ } . 5.1 Computation o f barrier certificate Proving existence of a barrie r certificate, finding one, or showing that a given function is in fact a bar rier certificate ar e in gener a l ha rd problems. But if we restrict the cla ss of systems a nd lab eling functions, we ca n construct c omputationally efficient techniques for searching barr ier certificates of sp ecific forms. One technique is to use sum-o f-squares (SOS) o ptimization [17], which relies on the fact that a p olynomial is non-neg ativ e if it can b e written as sum of squares of different p olynomials. Ther efore, we raise the following assumption. Assumption 1 System S has state set X ⊆ R n and its ve ctor fi eld f : X × V w → X is a p olynomial function of s t ate x for any w ∈ V w . Partition sets X i = L − 1 ( p i ) , i ∈ { 0 , 1 , 2 , . . . , M } , ar e b ounde d semi-algebr aic sets, i.e., t he y c an b e r epr esente d by p olynomial e qualities and ine qualities. Under Assumption 1, we ca n formulate (5)-(7 ) as an SOS optimizatio n pr oblem to se arc h for a p olynomial-type barr ier certificate B ( · ) and the tight est upp er bo und ( γ + cT d ). The following lemma provides a set of sufficient conditions for the existence of such a bar rier certificate required in The o rem 1, which can be s o lv ed as a n SO S optimization. Lemma 2. Su p p ose Assumption 1 holds and sets X 0 , X 1 , X c an b e define d by ve ctors of p olynomial ine qu a lities X 0 = { x ∈ R n | g 0 ( x ) ≥ 0 } , X 1 = { x ∈ R n | g 1 ( x ) ≥ 0 } , and X = { x ∈ R n | g ( x ) ≥ 0 } , wher e the ine qualities ar e define d element- wise . S upp ose ther e exists a sum-of-squar es p olynomial B(x), c onst ants γ ∈ [0 , 1] and c ≥ 0 , and ve ctors of sum-of-squar es p olynomials λ 0 ( x ) , λ 1 ( x ) , and λ ( x ) of appr opriate size such that fol lowing expr essions ar e sum-of-squar es p olynomials − B ( x ) − λ T 0 ( x ) g 0 ( x ) + γ (12) B ( x ) − λ T 1 ( x ) g 1 ( x ) − 1 (13) − E [ B ( f ( x, w )) | x ] + B ( x ) − λ T ( x ) g ( x ) + c. (14) Then B ( x ) satisfies c onditions (5) - (7) . Pr o of. The pr oof is similar to that of L e mma 7 in [33] and is o mitt e d due to lack of space. ⊓ ⊔ R emark 5. Assumption 1 is essential for applying the r esults of Lemma 2 to any L TL F sp ecification. F or a given sp ecification, we can relax this a ssumption and a llo w so me of the partition sets X i to b e unbounded. F or this, we require that the lab els corresp onding to un bo unded partition sets should only app ear either on self-lo ops or on ac c epting runs of length less than 3. F or instance, Example 1 has a n unbounded par tition s et X 3 and its corres p onding lab el p 3 satisfies this r equiremen t (see Figure 1 ), thus the results are still applicable for verifying the sp ecification. 5.2 Computational complexit y Based on Lemma 2 , a p olynomial ba rrier cer tificate B ( · ) satisfying (5)-(7) and minimizing constants γ and c ca n be a utomatically computed using SOSTOOL S [20] in conjunction with a s emidefinite progr amming solver such as SeDuMi [28]. W e refer the interested re a der to [27] and [19] for mor e discussions. Note that the v alue o f the upper bo und o f vio lating the prop ert y dep ends highly on the selectio n of degree o f p olynomials in Lemma 2. F rom the cons truction of directed gr aph G = ( V , E ), explained in Section 4, the n umber of triplets and hence the num b er of ba rrier certificates needed to b e computed a r e b ounded by |V | 3 = | Q | 3 , where |V | is the num b er of vertices in G . F urther, it is known [3] that | Q | is a t most |¬ ϕ | 2 |¬ ϕ | , where |¬ ϕ | is the length o f formula ¬ ϕ in terms of num b er of op erations, but in pra ctice, it is muc h smaller than this b ound [1 1 ]. Computational complexity of finding p olynomials B , λ 0 , λ 1 , λ in Lemma 2 depends on b o th the degree of p olynomials app earing in (12)- (1 4 ) and the n um b er of v ar iables. It is shown that for fixed degree s the required co mputatio ns grow po lynomially with resp ect to the dimension [33]. Hence we e x pect that this technique is more scalable in c o mparison with the discretization-ba sed appro ac hes esp ecially for lar ge-scale sy stems. 6 Case Studies In this sectio n, we demo nstrate the e ff ectiveness of the pro posed results o n several case studies. W e first showcase the res ults o n the running example, w hich has nonlinear dynamics with additive noise. W e then a pply the technique to a ten-dimensional linear s ystem with additive no ise to show its scala bilit y . The third case study is a three-dimens io nal nonlinea r system with multiplicativ e nois e. 6.1 Running example T o compute a n upp er b ound on reachabilit y pro babilities co rrespo nding to ea c h element of P ( q ) in Theo rem 2, w e use Lemma 2 to form ula te it as a SOS optimization prob- lem to minimize v alues of γ and c using bisection metho d. The optimization pr oblem is solved using SOSTOOLS and SeDuMi, to obtain upp er b ounds in Theore m 2. The com- puted upp er bo unds o n pro babilities cor r esponding to the elements of P ( · ), ( q 0 , q 4 , q 3 , 4), ( q 0 , q 1 , q 2 , 3), ( q 1 , q 2 , q 3 , 3), ( q 0 , q 1 , q 4 , 3), a nd ( q 1 , q 4 , q 3 , 3) a re res pectively 0 . 005 86, 0 . 0023 2, 0 . 0044 9, 0 . 003 91, and 0 . 0048 8. Using Theo rem 2, we get P { T ra ce N ( S ) | = ¬ ϕ } ≤ 0 . 00 586 + 0 . 00232 × 0 . 00449 + 0 . 0 0391 × 0 . 00488 = 0 . 005 89 . Thu s, a low er b ound on the probability tha t tra jectories of S satisfy safe L TL F prop ert y (3) ov er time horizo n N = 5 is given by 0 . 9941 1. The optimization finds po ly nomials of degree 5 for B , λ , λ 0 , a nd λ 1 . Hence 4 ba r rier certificates are co mputed each with 245 optimization co efficients, which takes 29 minutes in total. F or the sake of compariso n, we provide a proba bilis tic guar an tee from Monte-Carlo metho d using 5000 0 realizations, which results in the interv al P { T r ace N ( S ) | = ϕ } ∈ [0 . 9 959 , 0 . 997 9] with confidence 1 − 10 − 4 . Room1 Room 2 Room 3 Room 4 Room 5 Room 6 Room 8 Room 10 Room 7 Room 9 T e = 20 (a) q 1 : p 0 q 3 q 0 p 2 p 0 : p 1 p 1 p 1 p 0 q 2 (b) Fig. 2. (a) A schematic of t en-room building, (b) DF A A ¬ ϕ that accepts all traces satisfying ¬ ϕ where ϕ is given in (15). 6.2 Thermal mo del of a ten-ro om building Consider temp erature evolution in a ten-ro om building shown schematically in Figur e 2(a). W e use this mo del to demonstrate the effectiveness of the results o n large-dimensio nal state spaces. This mo del is a dapted from [1 0] b y dis c retizing it with s ampling time τ s = 5 minutes and without including heater s. The dyna mics o f S ar e given as follows: x 1 ( k + 1) = (1 − τ s ( α + α e 1 )) x 1 ( k ) + τ s αx 2 ( k ) + τ s α e 1 T e + 0 . 5 w 1 ( k ) , x 2 ( k + 1) = (1 − τ s (4 α + α e 2 )) x 2 ( k ) + τ s α ( x 1 ( k ) + x 3 ( k ) + x 7 ( k ) + x 9 ( k )) + τ s α e 2 T e + 0 . 5 w 2 ( k ) , x 3 ( k + 1) = (1 − τ s (2 α + α e 1 )) x 3 ( k ) + τ s α ( x 2 ( k ) + x 4 ( k ))+ τ s α e 1 T e + 0 . 5 w 3 ( k ) , x 4 ( k + 1) = (1 − τ s (2 α + α e 1 )) x 4 ( k ) + τ s α ( x 3 ( k ) + x 5 ( k ))+ τ s α e 1 T e + 0 . 5 w 4 ( k ) , x 5 ( k + 1) = (1 − τ s (4 α + α e 2 )) x 5 ( k ) + τ s α ( x 4 ( k ) + x 6 ( k ) + x 8 ( k ) + x 10 ( k )) + τ s α e 2 T e + 0 . 5 w 5 ( k ) , x 6 ( k + 1) = (1 − τ s ( α + α e 1 )) x 6 ( k ) + τ s αx 5 ( k ) + τ s α e 1 T e + 0 . 5 w 6 ( k ) , x 7 ( k + 1) = (1 − τ s ( α + α e 1 )) x 7 ( k ) + τ s αx 2 ( k ) + τ s α e 1 T e + 0 . 5 w 7 ( k ) , x 8 ( k + 1) = (1 − τ s ( α + α e 1 )) x 8 ( k ) + τ s αx 5 ( k ) + τ s α e 1 T e + 0 . 5 w 8 ( k ) , x 9 ( k + 1) = (1 − τ s ( α + α e 1 )) x 9 ( k ) + τ s αx 2 ( k ) + τ s α e 1 T e + 0 . 5 w 9 ( k ) , x 10 ( k + 1) = (1 − τ s ( α + α e 1 )) x 10 ( k ) + τ s αx 5 ( k ) + τ s α e 1 T e + 0 . 5 w 10 ( k ) , where x i , i ∈ { 1 , 2 , . . . , 10 } , denotes the temp erature in each roo m, T e = 20 ◦ C is the ambien t temper ature, and α = 5 × 1 0 − 2 , α e 1 = 5 × 10 − 3 , and α e 2 = 8 × 10 − 3 are heat exchange co efficien ts. Noise terms w i ( k ), i ∈ { 1 , 2 , . . . , 1 0 } , are indep enden t standard no rmal random v ar ia bles. The s ta te space of the system is X = R 10 . W e consider r e gions of interest X 0 = [18 , 19 . 75] 10 , X 1 = [20 . 25 , 22] 10 , X 2 = X \ ( X 0 ∪ X 1 ). The set of atomic prop ositions is given by Π = { p 0 , p 1 , p 2 } with lab eling function L ( x i ) = p i for all x i ∈ X i , i ∈ { 0 , 1 , 2 } . The ob jective is to compute a low er b ound on the probability that the solution pro cess of length N = 50 satisfies the s afe L TL F formula ϕ = ( p 0 ∧ ¬ p 1 ) ∨ ( p 1 ∧ ¬ p 0 ) . (15) The DF A A ¬ ϕ corres p onding to ¬ ϕ is shown in Fig ure 2 (b). W e use Algorithm 1 to get R ≤ 11 = { ( q 0 , q 3 ) , ( q 0 , q 1 , q 3 ) , ( q 0 , q 2 , q 3 ) } , P ( q 0 , q 1 , q 3 ) = { q 0 , q 1 , q 3 , 9 } , and P ( q 0 , q 2 , q 3 ) = q 2 q 0 p 0 : p 2 p 2 q 1 : p 0 Fig. 3. D F A A ¬ ϕ that accepts all traces satisfying ¬ ϕ where ϕ = p 0 ∧ ¬ p 2 . { q 0 , q 2 , q 3 , 9 } . As des cribed in Section 5, we compute tw o ba rrier cer tificates and SO S p oly- nomials satisfying inequalities of Le mma 2. The low er b ound P { T r ace N ( S ) | = ϕ } ≥ 0 . 98 2 0 is o btained using SOSTOO LS and SeDuMi for initial states starting fr om X 0 ∪ X 1 . The optimization finds B , λ , λ 0 , and λ 1 as quadr atic p olynomials. Hence tw o barr ier certificates are computed each with 2 55 optimization co efficients, which takes 1 8 minut es in total. F or the sake o f compariso n, we provide a pr obabilistic g uaran tee from Mont e - Carlo metho d us - ing 5 0000 realizatio ns, which r e s ults in the interv al P { T r ace N ( S ) | = ϕ } ∈ [0 . 99 84 , 0 . 9997 ] with c o nfidence 1 − 1 0 − 5 . 6.3 Lorenz mo del of a thermal conv ection lo op Our third c ase study is the Lore nz mode l o f a ther mal conv ection lo op a s used in [18] with m ultiplicative noise. The nonlinea r dynamics of S is given a s x 1 ( k + 1) = (1 − aT ) x 1 ( k ) + aT x 2 ( k ) + 0 . 02 5 x 1 ( k ) w 1 ( k ) , x 2 ( k + 1) = (1 − T ) x 2 ( k ) − T x 2 ( k ) x 3 ( k ) + 0 . 02 5 x 2 ( k ) w 2 ( k ) , x 3 ( k + 1) = (1 + bT ) x 3 ( k ) + T x 1 ( k ) x 2 ( k ) + 0 . 02 5 x 3 ( k ) w 3 ( k ) , (16) where a = 10, b = 8 / 3, and T = 0 . 0 1. Noise terms w 1 ( k ), w 2 ( k ), and w 3 ( k ) are indep e nden t standard normal ra ndom v a riables. W e re fer the interested r eaders to [3 1 ] for a detailed treatment of the mode l. The s tate space of the system is X = R 3 . W e define r egions of int e r est as X 0 = [ − 10 , 10] 2 × [2 , 10], X 1 = [ − 1 0 , 10] 2 × [ − 2 , 2], X 2 = [ − 10 , 10] 2 × [ − 10 , − 2], and X 3 = X \ ( X 0 ∪ X 1 ∪ X 2 ). The set of atomic pr opositions is giv e n by Π = { p 0 , p 1 , p 2 , p 3 } with labeling function L ( x i ) = p i for a ll x i ∈ X i , i ∈ { 0 , 1 , 2 , 3 } . W e consider safe L TL F prop ert y ϕ = p 0 ∧ ¬ p 2 and time horizon N = 10 . The DF A A ¬ ϕ corres p onding to the negation of ϕ is shown in Fig ure 3. One can readily see tha t R ≤ 11 = { ( q 0 , q 1 , q 2 ) } with P ( q 0 , q 1 , q 2 ) = ( q 0 , q 1 , q 2 , 9). Thus, we need to compute o nly o ne ba r rier certifica te. W e use inequalities of Lemma 2 a nd find a bar rier certificate that gives the lower b o und P { T r ace N ( S ) | = ϕ } ≥ 0 . 9 8 59. The optimizatio n finds B , λ , λ 0 , and λ 1 as p olynomials of degree 4. Hence only o ne ba rrier cer tificate is computed with 53 optimization co efficients, whic h takes 3 minutes. F or the s ak e of comparison, Mo n te- Carlo metho d res ults in the interv a l [0 . 9912 , 0 . 9972 ] for the true probability with confidence 1 − 1 0 − 4 using 1 0000 r ealizations. Remark that current implementations of discretizatio n-based approaches (e.g., [2 6 ]) a re not dir e c tly applicable to the mo del in Subsectio n 6.1 and to the mo del (16) due to the m ultiplicative noise in the latter and unbounded state space of the former. Application of these techniques to the mo del in Subsection 6.2 will also b e computationally mu ch more exp ensiv e than our appro ac h due to its exp onential c o mplexit y as a function o f state space dimension. 7 Conclusions In this pap er, we prop osed a discretization-free appr o ac h for for mal verification of discrete- time sto ch astic systems. The approa c h co mputes lower b ounds on the pr obabilit y of sat- isfying a s pecification enco ded as safe L TL ov er finite traces. It is based on computation of ba rrier certificates and us es sum-of-squa res optimization to find suc h b ounds. F rom the implemen tation pers pective, we pla n to g eneralize our co de and ma k e it publicly av ailable so tha t it can b e a pplied to systems a nd sp ecifications defined by users. References 1. A b ate, A., Kato en, J.P ., Mereacre, A .: Quantitative automata mo del chec king of autonomous stochastic hybrid systems. In: Pro ceed in g s of the 14th international conference on Hy brid sys- tems: compu tatio n and control . pp. 83–92. ACM (2011) 2. A yala, A .I.M ., And erss on, S .B., Belta, C.: Probabilistic control from time-b ounded temp o- ral logic sp ecifications in dynamic environments. In: 2012 IEEE International Conference on Rob otics and Automation. pp. 4705–4710 (2012) 3. Baier, C., Kato en, J.P ., Larsen, K.G.: Principles of mo del chec k ing. MIT press (2008) 4. De Giacomo, G., V ardi, M.Y.: Linear temp oral logic and linear dynamic logic on fin ite traces. In: I n ternational Joint Conference on Artificial Intelligence. vol. 13, pp. 854–860 (2013) 5. De Giacomo, G., V ardi, M.Y.: Synthesis for L TL and LDL on fin ite traces. In : International Join t Conference on Artificial Intell igence. vol. 15, p p . 1558–1564 (2015) 6. Dimitrov a, R., Ma jumdar, R.: Dedu ctiv e control synthesis for alternating-time logics. In: 2014 International Conference on Em b edded Softw are (EMSOFT). pp. 1–10 (2014) 7. Du ret-Lutz, A ., Lewko wicz, A., F auchille, A., Mic h au d , T., R enault, E., Xu, L.: Sp ot 2.0: A framew ork for L TL and \ omega -automata m an ip u lati on. In: I n ternational S ymposium on Automated T ec hnology for V erification and Analysis. pp. 122–129. Sp ringe r (2016) 8. H en riksen, J.G., Jensen, J., Jørgensen, M., K larlund , N., P aige, R., Rauh e, T., Sand holm, A.: Mona: Monadic second- order logic in practice. I n: Internatio nal W orkshop on T o ols and Algorithms for the Construction and Analysis of Sy stems. pp. 89–110. S pringer (1995) 9. H u ang, C., Chen, X ., Lin, W., Y ang, Z., Li, X .: Probabilistic safety verification of stochastic hybrid systems using barrier certificates. ACM T ransactions on Em b edded Computing Systems 16(5s), 186 (2017) 10. Jagtap, P ., Zamani, M.: QUEST: A to ol for state-space q uan tization-free synthesis of symbolic contro llers. I n: I nternational Conference on Qu an titative Ev aluation of Systems. pp. 309–313 . Springer (2017), http://www.hcs.ei .tum.de/softwa re/quest/ 11. Klein, J., Baier, C.: Exp eriments wi t h deterministic ω -automata for form u las of linear temp oral logic. Theoretical Computer Science 363(2), 182–195 (2006) 12. Kup fe rman, O., V ardi, M.: Mo del chec king of safet y prop erties. In: International Conference on Computer A ided V erification. pp. 172–183 . Springer (1999) 13. Kush ner, H.J.: On the stability of sto c hastic dynamical systems. Pro ceedings of the National Academy of S cie n ces 53(1), 8–12 (1965) 14. Lahijanian, M., A ndersson, S.B., Belta, C.: F ormal verification and synthesis for discrete-time stochastic systems. IEEE T ransactions on Automatic Control 60(8), 2031–2045 (2015) 15. Lav aei, A., Soudjani, S ., Zamani, M.: F rom dissipativity theory to comp ositional construction of finite Marko v d ecis ion pro cesses. In: Hybrid Sy stems: Computation and Contro l (H SCC ). pp. 21–30. AC M, New Y ork, N Y , U SA (2018) 16. Maity , D., Baras, J.S.: Motion planning in d ynamic environmen ts with b ounded time temp oral logic sp ecifications. In: 2015 23rd Mediterranean Conference on Control and Au tomatio n . pp . 940–946 ( 20 15) 17. Parrilo , P .A.: Semidefinite programming relaxations for semialgebraic p roblems . Mathematical programming 96(2), 293–320 (2003) 18. Posto yan, R ., Nesic, D.: Time-triggered con t ro l of nonlinear discrete-time systems. In: 2016 IEEE 55th Conference on Decision and Control. p p. 6814–6 819 (2016) 19. Pra jna, S ., Jadbabaie, A., Pappas, G.J.: A framew ork for w orst-case and sto c h as t ic safet y verificatio n using barrier certificates. IEEE T ransactions on Automatic Con trol 52(8), 1415– 1428 ( 20 07) 20. Pra jna, S., P apachristodoulou, A., P arrilo, P .A.: Introd ucing SOSTOOLS: a general purp ose sum of squares programming solv er. In: Pro ceedings of th e 41st IEEE Conference on Decision and Control. vol . 1, p p . 741–746 (2002), http://www.c ds.caltech.edu/sostools/ 21. Ru ss ell, S .J ., N orvig, P .: Art ificia l Intelligence: A Modern Ap proac h. P earson Education, 2 edn. (2003) 22. Saha, I., Ramaithitima, R ., Kumar, V ., P app as, G.J., S eshia , S .A .: Automated comp osition of motion primitives for multi-robot systems from safe L TL sp ecifications. In : 2014 I EEE /R SJ International Conference on Intell igen t Rob ots and Systems. pp. 1525–153 2 (2014) 23. Soud j ani, S., A b ate, A.: Precise approximations of th e probability distribution of a Marko v process in time: an application to probabilistic inv ariance. In : T AC AS, LNCS, vol. 8413, pp. 547–561 . Sp rin g er (2014) 24. Soud j ani, S., Abate, A., Ma jumdar, R.: D ynamic Bay esian netw orks as formal ab stractions of structured stochastic p rocesses. In: 26th International Conference on Concurrency Theory . pp. 1–14. D agstuh l Pu blis h ing, Madrid, Spain (2015) 25. Soud j ani, S ., Abate, A .: Adaptive and sequ en tial gridding pro cedures for the abstraction and verificatio n of sto c hastic pro cesse s. SIAM Journal on Ap plied Dyn ami cal Systems 12(2), 921– 956 (2013) 26. Soud j ani, S., Gev aerts, C., Abate, A.: F A U ST 2 : Formal Ab stracti ons of Uncountable-STate STochastic processes. In: Baier, C., Tinelli, C. (eds.) T o ols and Algorithms for the Construction and A nalysis of S ystems. pp. 272–286 . Springer Berlin Heidelb erg, Berlin, H eidelberg (2015) 27. Steinh ardt, J., T edrak e, R.: Finite-time regional verification of sto c h as t ic non-linear systems. The International Journal of R ob otics Research 31(7), 901–923 (2012) 28. Stu rm, J.F.: Using S eDuMi 1.02, a MA TLAB toolb o x for optimization ov er symmetric cones. Optimization metho ds and softw are 11(1-4), 625–653 (1999), http://sedumi.ie. lehigh.edu / 29. T abuada, P .: V erification and control of hybrid systems: a sy m b olic approach. Springer Science & Business Media (2009) 30. Tk achev, I., Abate, A .: F orm u la - free finite abstractions for linear temp oral verification of stochastic hybrid systems. In: Pro ceed in g s of the 16th international conference on Hy brid sys- tems: compu tatio n and control . pp. 283–292. ACM (2013) 31. Vincent, T.L., Y u, J.: Control of a chaotic system. Dy namics and Con t rol 1(1), 35–52 (1991) 32. Wisniewski, R ., Bujorianu, M.L.: Sto c hastic safety analysis of stochastic hybrid systems. In: 2017 I EEE 56th Annual Conference on Decision and Control . pp. 2390–2395 (2017) 33. W ongpiromsarn, T., T opcu , U ., Lamp erski, A.: Automata theory meets barrier certificates: T emp ora l logic verificati on of nonlinear systems. IEEE T ransactions on A utomatic Control 61(11), 3344–33 55 ( 2016)
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment