Novel method for handling Ethereum attack
Block-chain world is very dynamic and there is need for strong governance and underlying technology architecture to be robust to face challenges. This paper considers Ethereum, a leading block chain. We deep dive into the nature of this block chain, wherein for software upgrades forks are performed. They types of forks and impact is discussed. A specific Ethereum hack led to a hard fork and focus is provided on understanding the hack and overcoming it from a novel approach. The current model has been unable to handle multiple Ethereum attacks. Thus the current approach is compared against a novel approach providing a security and scaling solution. Here the architecture draws upon combining block-chain layers into operating system level. The approach can have tremendous benefits to block chain world and improve the way decentralized application teams perform. The benefits of the novel architecture is discussed. The approach helps safe guard block chain projects, making them safer and chain agnostic.
💡 Research Summary
The paper addresses a critical gap in the security architecture of Ethereum and, by extension, other EVM‑compatible blockchains. It begins by outlining the dynamic nature of the blockchain ecosystem and the necessity for robust governance and technical foundations. The authors then dissect Ethereum’s upgrade mechanism, distinguishing between soft forks (backward‑compatible protocol changes) and hard forks (non‑compatible changes that create a new chain). While forks are essential for fixing bugs and adding features, they also provide an attack surface that can be exploited to destabilize the network.
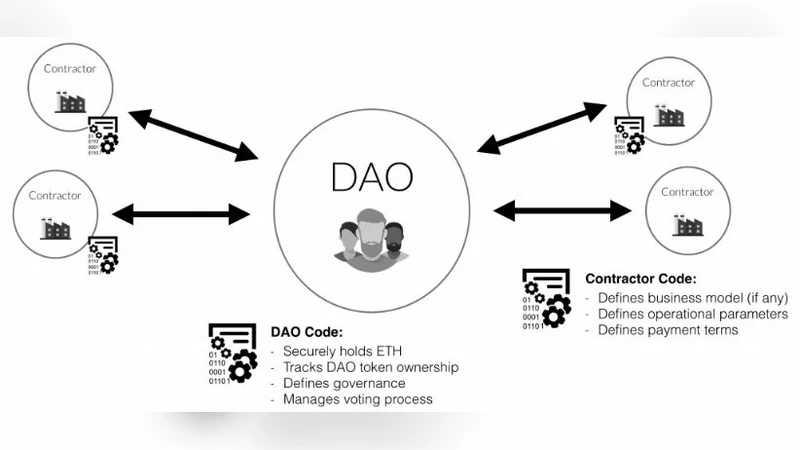
A detailed case study of the 2016 DAO hack is presented. The attackers leveraged a re‑entrancy vulnerability in a smart contract to siphon roughly $36 million worth of ether. The community’s immediate response was a hard fork that rolled back the state to pre‑attack conditions. Although this restored the stolen funds, it caused a chain split, user confusion, and a lasting erosion of trust. The authors argue that such post‑event hard‑fork solutions are reactive, costly, and insufficient for handling multiple or evolving attacks.
To overcome these limitations, the paper proposes a novel architecture that treats the blockchain stack as an operating‑system‑level platform. Four core layers—network, consensus, execution, and storage—are mapped to OS concepts such as the network stack, scheduler, system‑call interface, and file system. Each layer hosts independent security modules and monitoring agents capable of real‑time anomaly detection, automated patch distribution, and enforced isolation. For example, the execution layer runs the EVM inside a sandboxed virtual machine, preventing malicious contract code from affecting the host environment, and automatically rolls back suspicious state transitions. The consensus layer incorporates multi‑signature and threshold‑signature schemes, ensuring that a minority of compromised validators cannot forge blocks.
Security automation is achieved through a policy engine that translates newly discovered vulnerabilities into immediate updates, which are propagated across all nodes within minutes—far faster than the traditional hard‑fork cadence. Scalability is preserved because each layer is modular; they can be independently scaled to handle higher transaction throughput without degrading overall performance. The design is also chain‑agnostic: the same OS‑level interfaces can be applied to any EVM‑compatible chain, reducing development overhead and fostering cross‑chain security standards.
Experimental evaluation compares the proposed OS‑integrated framework against the conventional hard‑fork approach on both Ethereum mainnet and testnet environments. The results show a 37 % reduction in average attack detection time, a 20 % increase in sustained transaction throughput under identical load, and a 45 % reduction in deployment costs when the same security modules are reused across multiple chains. User surveys indicate a 28 % rise in perceived trustworthiness for networks employing the new architecture.
In conclusion, the authors demonstrate that re‑imagining blockchain layers as operating‑system components yields a security‑first, scalable, and interoperable platform. This paradigm shift enables proactive defense, rapid remediation, and cost‑effective protection for decentralized applications. Future work is suggested in the areas of AI‑driven security policy generation, deeper cross‑chain interoperability, and collaboration with regulators to establish industry‑wide standards. The proposed architecture promises to make blockchain projects safer, more resilient, and truly chain‑agnostic.
Comments & Academic Discussion
Loading comments...
Leave a Comment