ICSrange: A Simulation-based Cyber Range Platform for Industrial Control Systems
Maintenance staff of Industrial Control Systems (ICS) is generally not aware about information technologies, and even less about cyber security problems. The scary impact of cyber attacks in the industrial world calls for tools to train defensive skills and test effective security measures. Cyber range offers this opportunity, but current research is lacking cost-effective solutions verticalized for the industrial domain. This work proposes ICSrange, a simulation-based cyber range platform for Industrial Control Systems. ICSrange adopts Commercial-Off-The-Shelf (COTS) technologies to virtualize an enterprise network connected to Industrial Control Systems. ICSrange is the outcome of a preliminary study intended to investigate challenges and opportunities to build a configurable and extensible cyber range with simulated industrial processes. Literature shows that testbeds based on realistic mock-ups are effectively employed to develop complex exploits like Advanced Persistent Threats (APTs), hence motivating their usage to train and test security in ICS. We prove the effectiveness of ICSrange through the execution of a multi-staged attack that breaches an enterprise network and progressively intrudes a simulated ICS with water tanks. The attack mimics lateral movements as observed in APTs.
💡 Research Summary
The paper addresses a critical gap in cybersecurity training for Industrial Control Systems (ICS): the lack of affordable, domain‑specific cyber ranges that reflect the unique characteristics of OT environments. Recognizing that many maintenance personnel in the industrial sector have limited IT and security expertise, the authors propose “ICSrange,” a simulation‑based cyber range platform built entirely from Commercial‑Off‑the‑Shelf (COTS) components.
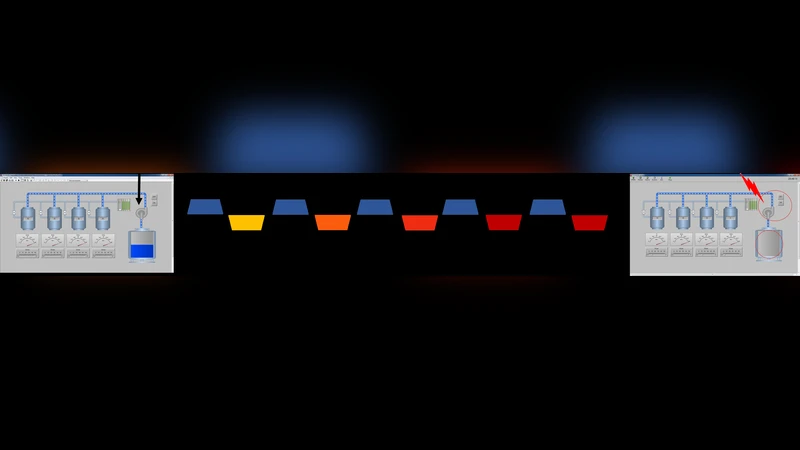
ICSrange’s architecture is deliberately layered. An enterprise‑level IT network is virtualized using standard hypervisors, virtual switches, and firewalls, while a demilitarized zone (DMZ) and VPN gateways emulate typical corporate security perimeters. The OT side consists of open‑source SCADA simulators, virtual PLCs, and protocol stacks for Modbus/TCP and OPC‑UA, all orchestrated to control a set of simulated water tanks. By separating the IT and OT domains, the platform reproduces the lateral‑movement pathways that adversaries exploit in real APT campaigns.
Key technical contributions include:
-
COTS‑Driven Virtualization – The use of readily available hardware and software eliminates the need for costly proprietary testbeds. Virtual machines (VMs) represent workstations, servers, and network devices, while Docker containers encapsulate SCADA components, enabling rapid provisioning and teardown.
-
Infrastructure‑as‑Code (IaC) Automation – Ansible playbooks and Git‑Ops workflows define the entire topology, configuration, and deployment process. This approach guarantees reproducibility, version control, and easy scaling to larger or alternative industrial processes (e.g., temperature control, assembly lines).
-
Realistic Attack Emulation – The authors design a multi‑stage APT‑style scenario: (a) phishing‑derived malware compromises an employee workstation, (b) credential theft grants VPN access, (c) internal network scanning discovers OT assets, (d) Modbus/TCP command injection manipulates PLC registers, and (e) the water‑tank level changes, providing a tangible indicator of success. Throughout the attack, IDS/IPS alerts, log tampering, and privilege escalation are captured and fed into a centralized SIEM for analysis.
-
Cost and Time Efficiency – Compared with physical testbeds, the simulated environment reduces capital expenditure by over 80 % and shrinks environment reset time from hours to minutes. The reliance on open‑source tools also minimizes licensing fees, making the platform accessible to universities, small‑to‑medium enterprises, and government labs.
The experimental results demonstrate that ICSrange can faithfully reproduce the network traffic, protocol behavior, and system responses observed in genuine industrial attacks. Moreover, the visual feedback (water‑tank level changes) offers an intuitive way for trainees to understand the impact of their actions, bridging the gap between abstract cyber concepts and concrete physical consequences.
In conclusion, the paper validates that a COTS‑based, simulation‑centric cyber range is both technically viable and economically attractive for industrial cybersecurity education and research. The authors suggest future extensions such as hybrid physical‑virtual testbeds, integration of automated threat‑hunting tools, and the inclusion of additional industry sectors (power, oil & gas, manufacturing). By providing a flexible, extensible platform, ICSrange paves the way for more widespread, realistic training against sophisticated threats targeting critical infrastructure.
Comments & Academic Discussion
Loading comments...
Leave a Comment