Defeating Opaque Predicates Statically through Machine Learning and Binary Analysis
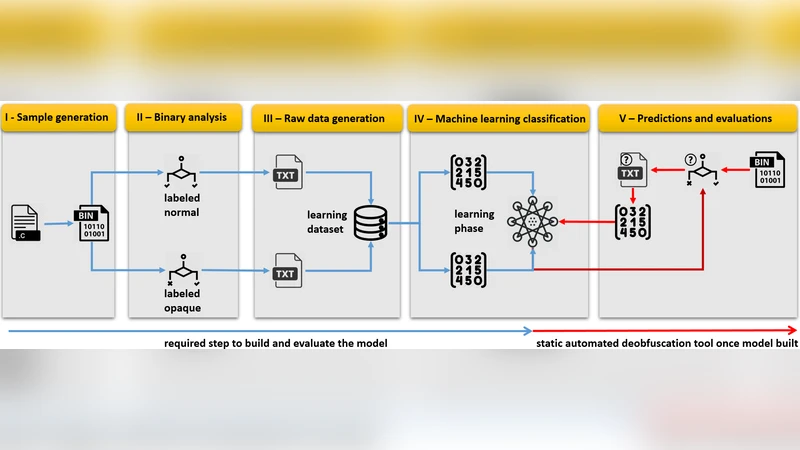
We present a new approach that bridges binary analysis techniques with machine learning classification for the purpose of providing a static and generic evaluation technique for opaque predicates, regardless of their constructions. We use this technique as a static automated deobfuscation tool to remove the opaque predicates introduced by obfuscation mechanisms. According to our experimental results, our models have up to 98% accuracy at detecting and deob-fuscating state-of-the-art opaque predicates patterns. By contrast, the leading edge deobfuscation methods based on symbolic execution show less accuracy mostly due to the SMT solvers constraints and the lack of scalability of dynamic symbolic analyses. Our approach underlines the efficiency of hybrid symbolic analysis and machine learning techniques for a static and generic deobfuscation methodology.
💡 Research Summary
The paper introduces a novel static de‑obfuscation framework that combines binary‑level static symbolic analysis with supervised machine learning to detect and resolve opaque predicates (OPs) in compiled code. Opaque predicates are constant‑value branch conditions deliberately hidden by obfuscators; they come in invariant forms (always true P_T or always false P_F) and two‑way forms (P_?). Existing de‑obfuscation tools largely rely on dynamic symbolic execution (DSE) or SMT‑based static analysis. While powerful for certain arithmetic‑based OPs, these approaches suffer from three major drawbacks: (1) specificity – they target only a subset of known constructions; (2) code coverage – DSE requires concrete execution traces and often fails to explore all paths, especially in trigger‑based malware; (3) scalability – path explosion and solver limitations (especially with MBA, alias‑based, or recent bi‑opaque constructions) make them impractical for large binaries.
To overcome these issues, the authors first collect a large corpus of opaque predicates generated by state‑of‑the‑art obfuscators such as Tigress and OLLVM. The corpus includes a wide variety of constructions: arithmetic‑based, mixed Boolean‑arithmetic (MBA), alias‑based, environment‑based, and the newer bi‑opaque patterns designed to defeat symbolic execution. Each predicate is labeled as “opaque” or “non‑opaque” and, when opaque, as P_T or P_F.
The static analysis pipeline extracts the disassembly of each conditional jump, along with auxiliary metadata (register usage, immediate constants, memory accesses, control‑flow context). These raw textual representations are transformed into numerical feature vectors using a bag‑of‑words model with term‑frequency and inverse‑document‑frequency weighting. The resulting feature space captures syntactic patterns that correlate with the underlying semantic invariance of the predicate.
A suite of supervised classifiers (Random Forest, Support Vector Machine, XGBoost, etc.) is trained and evaluated using 20‑fold cross‑validation. XGBoost consistently achieves the highest performance, reaching up to 98 % accuracy and a comparable F1‑score across all predicate types. Importantly, the model can predict not only the presence of an opaque predicate but also its invariant truth value, enabling direct code simplification without any execution.
The trained model is packaged as an IDA Pro plug‑in. When a binary is loaded, the plug‑in automatically enumerates all conditional jumps, extracts the same feature set, feeds it to the classifier, and, for predicates classified as invariant, rewrites the branch to the known target or removes the dead code. This process is purely static; no runtime traces or SMT queries are required, resulting in execution times on the order of seconds for thousands of predicates, a dramatic improvement over DSE‑based tools that may take minutes to hours.
Experimental evaluation compares the proposed static‑ML approach against several leading de‑obfuscation tools that rely on symbolic execution and SMT solving. The authors report three key findings: (1) Accuracy – the ML method outperforms DSE on all predicate families, especially on MBA and bi‑opaque cases where solvers exhibit high false‑negative/positive rates; (2) Speed – static analysis plus inference is orders of magnitude faster, making the technique suitable for large‑scale malware analysis pipelines; (3) Generalization – the model maintains high performance on unseen obfuscator versions and on custom‑crafted opaque predicates, demonstrating robustness to evolving obfuscation techniques.
The paper also discusses limitations. Feature extraction is based on textual tokenization, which may miss subtle semantic relationships in highly complex control‑flow graphs or in predicates that depend on runtime‑generated randomness. Moreover, the classifier’s performance degrades when encountering entirely novel constructions absent from the training set, potentially increasing false positives. The authors propose future work in three directions: (a) graph‑neural‑network representations to capture structural information; (b) deep sequence models (e.g., Transformers) for end‑to‑end feature learning; and (c) multimodal training that combines static features with lightweight dynamic traces to further improve resilience.
In summary, the study demonstrates that a hybrid static‑symbolic plus machine‑learning pipeline can reliably and efficiently identify and eliminate opaque predicates across a broad spectrum of obfuscation strategies. By removing the dependence on SMT solvers and exhaustive path exploration, the approach offers a scalable, accurate, and practical solution for modern reverse‑engineering challenges, establishing a new paradigm for static de‑obfuscation research.
Comments & Academic Discussion
Loading comments...
Leave a Comment