Maintenance staff of Industrial Control Systems (ICS) is generally not aware about information technologies, and even less about cyber security problems. The scary impact of cyber attacks in the industrial world calls for tools to train defensive skills and test effective security measures. Cyber range offers this opportunity, but current research is lacking cost-effective solutions verticalized for the industrial domain. This work proposes ICSrange, a simulation-based cyber range platform for Industrial Control Systems. ICSrange adopts Commercial-Off-The-Shelf (COTS) technologies to virtualize an enterprise network connected to Industrial Control Systems. ICSrange is the outcome of a preliminary study intended to investigate challenges and opportunities to build a configurable and extensible cyber range with simulated industrial processes. Literature shows that testbeds based on realistic mock-ups are effectively employed to develop complex exploits like Advanced Persistent Threats (APTs), hence motivating their usage to train and test security in ICS. We prove the effectiveness of ICSrange through the execution of a multi-staged attack that breaches an enterprise network and progressively intrudes a simulated ICS with water tanks. The attack mimics lateral movements as observed in APTs.
Deep Dive into ICSrange: A Simulation-based Cyber Range Platform for Industrial Control Systems.
Maintenance staff of Industrial Control Systems (ICS) is generally not aware about information technologies, and even less about cyber security problems. The scary impact of cyber attacks in the industrial world calls for tools to train defensive skills and test effective security measures. Cyber range offers this opportunity, but current research is lacking cost-effective solutions verticalized for the industrial domain. This work proposes ICSrange, a simulation-based cyber range platform for Industrial Control Systems. ICSrange adopts Commercial-Off-The-Shelf (COTS) technologies to virtualize an enterprise network connected to Industrial Control Systems. ICSrange is the outcome of a preliminary study intended to investigate challenges and opportunities to build a configurable and extensible cyber range with simulated industrial processes. Literature shows that testbeds based on realistic mock-ups are effectively employed to develop complex exploits like Advanced Persistent Threats (A
As industrial control systems (ICS) adopt information technologies, maintenance staff has to be more and more aware about cyber security. In an unprecedented way the consequences of a cyber-attack can be catastrophic for the physical world. This emergency calls for cost-effective and replicable methods to grow the expertise and skills of cyber-defense teams, and this is generally done using cyber testbeds or cyber ranges [1]. Cyber ranges are virtual hardware and software environments that recreate enterprise networks and interconnected systems 1,2 . The objective of a cyber range is to provide a legal and controlled environment for training and testing skills and methods for cyber-security [2]. In this work we present ICSrange, a simulation-based cyber range platform for Industrial Control Systems (ICS). ICSrange is the outcome of a preliminary study intended to investigate challenges and opportunities to build a cost-effective, configurable and extensible cyber range with simulated industrial processes. Literature shows that testbeds based on realistic mock-ups are effectively employed by hackers to develop complex exploits like Advanced Persistent Threats (APTs) 3 , hence motivating their usage to train and test security in ICS [3]. Even if not exhaustive, cyber training is extremely important in the process of maintaining a required level of security.
The prototype of ICSrange adopts Commercial-Off-The-Shelf (COTS) platforms and open-source technologies, to recreate 1) multiple servers connected in an enterprise network, i.e., gateways, web-servers, login nodes, 2) a production Industrial Control System based on a Supervisory Control And Data Acquisition (SCADA) system, 3) industrial network communications, i.e., Modbus communication among PLCs, 4) network segments such as a Demilitarized Zone (DMZ), an intermediate network, a SCADA network, 5) data sources from the ICS and from the enterprise nodes. ICSrange is deployed on virtual machines. Current version of ICSrange is partially configurable in terms of security features, e.g., the difficulty to breach some nodes based on patched vulnerabilities, the adjustable isolation of industrial network segments, the complexity of the simulated physical process. As compared to other works [4], ICSrange relies on the simulation and customization of variously complex SCADA processes -with real network communications,-which makes it extremely costeffective and portable. We prove the effectiveness of ICSrange through a multi-staged attack that breaches an enterprise network and progressively intrudes a simulated ICS with water tanks. The attack mimics lateral movements as observed in APTs.
ICSrange has to serve for the following objectives:
- Providing cyber training of penetration skills for Red Teams, i.e., professional hackers employed by organizations to challenge their own defensive capabilities by assuming an adversarial role on purpose. 2) Improving defensive methods and practices for Blue Teams. For example, the enterprise security team can test intrusion detection and prevention systems, server configurations, connections, access policies, and response and mitigation actions. 3) Researching for advanced methodologies for cybersecurity. As an example, installing security sensors and log collectors, researchers can develop data-driven methods to monitor the security posture of industrial networks. 4) Planning advanced reaction and risk mitigation plans for Industrial Control System, through the simulation of SCADA processes. Simulation of inter-dependent systems enable the assessment of the impact of attacks against physical controls, and allows to forecast cascading effects. Section 2 shows the architecture of ICSrange prototype and a validation through a multi-staged attack. Section 3 provides observations and describes future works.
Disclaimer The software used in this preliminary work is used under personal or academic license, and is not intended to be distributed. The vulnerabilities and exploits indicated in this work are public and known.
ICSrange emulates a segmented enterprise network and an Industrial Control System (ICS) based on SCADA.
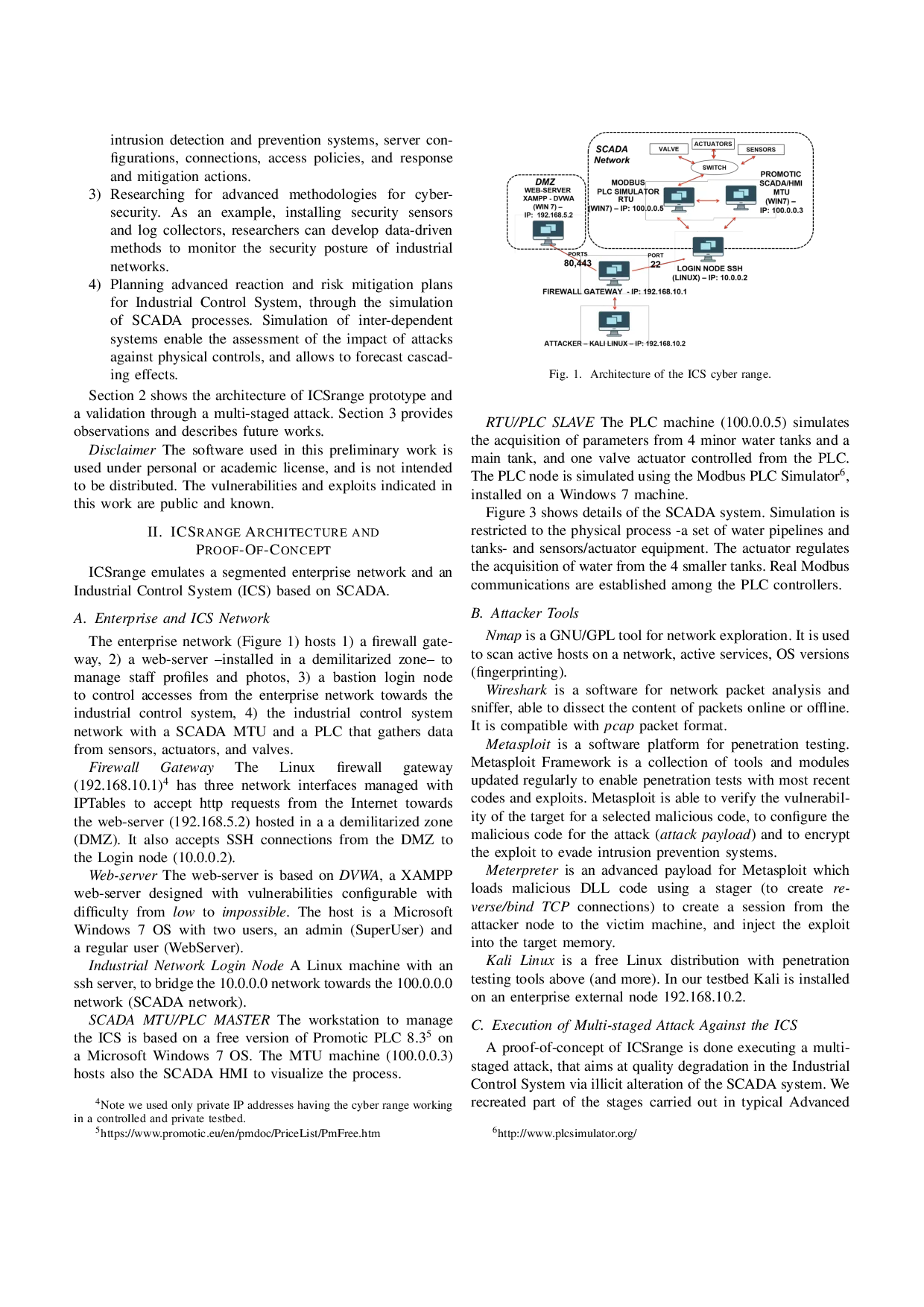
The enterprise network (Figure 1) hosts 1) a firewall gateway, 2) a web-server -installed in a demilitarized zone-to manage staff profiles and photos, 3) a bastion login node to control accesses from the enterprise network towards the industrial control system, 4) the industrial control system network with a SCADA MTU and a PLC that gathers data from sensors, actuators, and valves.
Firewall Gateway The Linux firewall gateway (192.168.10.1) 4 has three network interfaces managed with IPTables to accept http requests from the Internet towards the web-server (192.168.5.2) hosted in a a demilitarized zone (DMZ). It also accepts SSH connections from the DMZ to the Login node (10.0.0.2).
Web-server The web-server is based on DVWA, a XAMPP web-server designed with vulnerabilities configurable with difficulty fro
…(Full text truncated)…
This content is AI-processed based on ArXiv data.