Secure and Transparent Audit Logs with BlockAudit
Audit logs serve as a critical component in enterprise business systems and are used for auditing, storing, and tracking changes made to the data. However, audit logs are vulnerable to a series of attacks enabling adversaries to tamper data and corresponding audit logs without getting detected. Among them, two well-known attacks are “the physical access attack,” which exploits root privileges, and “the remote vulnerability attack,” which compromises known vulnerabilities in database systems. In this paper, we present BlockAudit: a scalable and tamper-proof system that leverages the design properties of audit logs and security guarantees of blockchain to enable secure and trustworthy audit logs. Towards that, we construct the design schema of BlockAudit and outline its functional and operational procedures. We implement our design on a custom-built Practical Byzantine Fault Tolerance (PBFT) blockchain system and evaluate the performance in terms of latency, network size, payload size, and transaction rate. Our results show that conventional audit logs can seamlessly transition into BlockAudit to achieve higher security and defend against the known attacks on audit logs.
💡 Research Summary
The paper “Secure and Transparent Audit Logs with BlockAudit” addresses a critical security gap in enterprise audit‑logging systems. Traditional audit logs are stored in a single database and therefore inherit the database’s single point of trust and single point of failure. An adversary with root access (physical access attack) or one who exploits software vulnerabilities (remote vulnerability attack) can simultaneously tamper with the underlying data and the corresponding audit entries, or even suppress the generation of logs altogether. Existing mitigations such as write‑once media or continuous printers assume the logging site itself cannot be compromised, an assumption that does not hold in practice.
To overcome these weaknesses, the authors propose BlockAudit, a blockchain‑based audit‑log framework that leverages the immutability, distributed replication, and consensus guarantees of a permissioned ledger. The design follows four logical steps: (1) capture system events generated by the data‑access layer of an enterprise application; (2) encode each event as a blockchain‑compatible transaction, attaching timestamps and cryptographic hashes; (3) disseminate the transactions to a peer‑to‑peer network of audit nodes that run a Practical Byzantine Fault Tolerance (PBFT) protocol; and (4) once a super‑majority (3f + 1 nodes) approves the transaction, it is appended to an immutable chain where each block contains the hash of its predecessor and a Merkle root of the contained transactions. This structure guarantees that any attempt to alter a past log entry would require compromising a majority of the peers, raising the cost of attack dramatically.
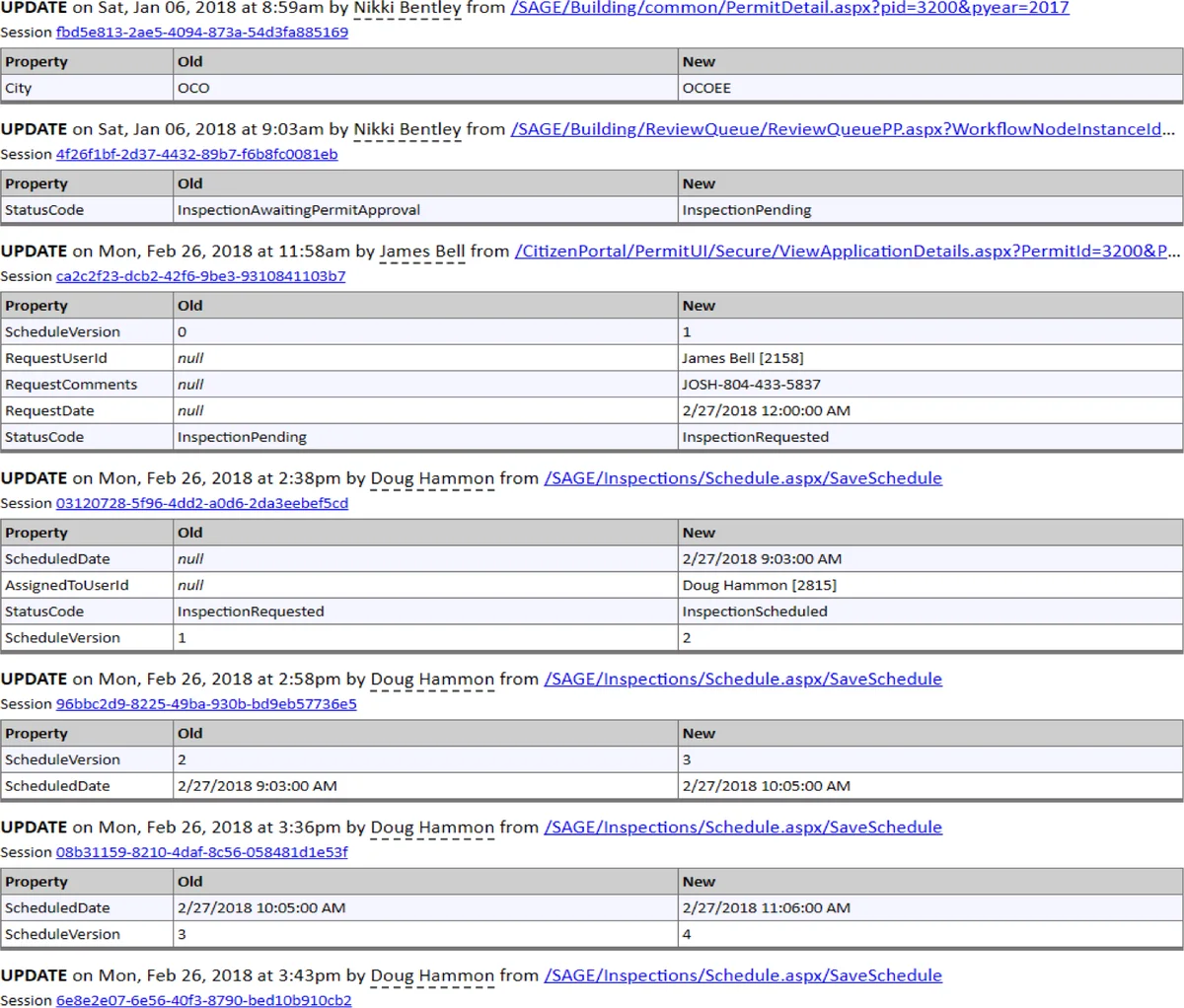
The authors implement BlockAudit on a custom PBFT blockchain and integrate it with a real‑world e‑government application supplied by Clearvillage Inc. They evaluate the system across several dimensions: latency, network size (number of peers), payload size (1 KB–10 KB per transaction), and transaction throughput (transactions per second). Experiments with 4, 8, 12, and 16 peers show average end‑to‑end latencies ranging from 30 ms to 70 ms, well within the bounds for real‑time auditing. Throughput scales linearly with payload size, achieving up to ~800 TPS for 10 KB payloads, while network bandwidth grows proportionally with the number of peers but remains manageable thanks to the efficient three‑phase PBFT message exchange. These results demonstrate that BlockAudit can replace conventional audit‑log stores without incurring prohibitive performance penalties.
In the related‑work discussion, the paper surveys cryptographic audit‑log schemes, trusted notary services, and cloud‑based secure logging frameworks. It points out that prior approaches either require pre‑generation of tamper‑evidence, cannot prevent log deletion, or rely on external notaries that become new single points of failure. BlockAudit’s decentralized consensus eliminates these drawbacks and provides continuous, post‑event tamper detection.
The threat model assumes a powerful adversary capable of both physical root‑level access and remote exploitation of software bugs. The model also acknowledges a weaker insider threat (a corrupt auditor) who already possesses privileged credentials. BlockAudit is designed to resist both scenarios by ensuring that any modification of the log would need to be reflected across the majority of the blockchain peers.
The authors acknowledge limitations: the current prototype is confined to a permissioned (private) blockchain, and scaling to public or consortium blockchains would introduce challenges such as higher latency, larger validator sets, and incentive mechanisms. Moreover, PBFT’s performance degrades in high‑latency or geographically dispersed networks, suggesting future work on hybrid consensus, sharding, or layer‑2 solutions.
In conclusion, BlockAudit presents a concrete, experimentally validated architecture that transforms audit logs from vulnerable, centrally stored records into tamper‑proof, transparent, and verifiable ledgers. It offers a practical migration path for enterprises and regulated industries seeking stronger guarantees of data provenance, compliance, and forensic integrity without sacrificing operational efficiency.
Comments & Academic Discussion
Loading comments...
Leave a Comment