Homomorphic Encryption for Speaker Recognition: Protection of Biometric Templates and Vendor Model Parameters
Data privacy is crucial when dealing with biometric data. Accounting for the latest European data privacy regulation and payment service directive, biometric template protection is essential for any commercial application. Ensuring unlinkability acro…
Authors: Andreas Nautsch, Sergey Isadskiy, Jascha Kolberg
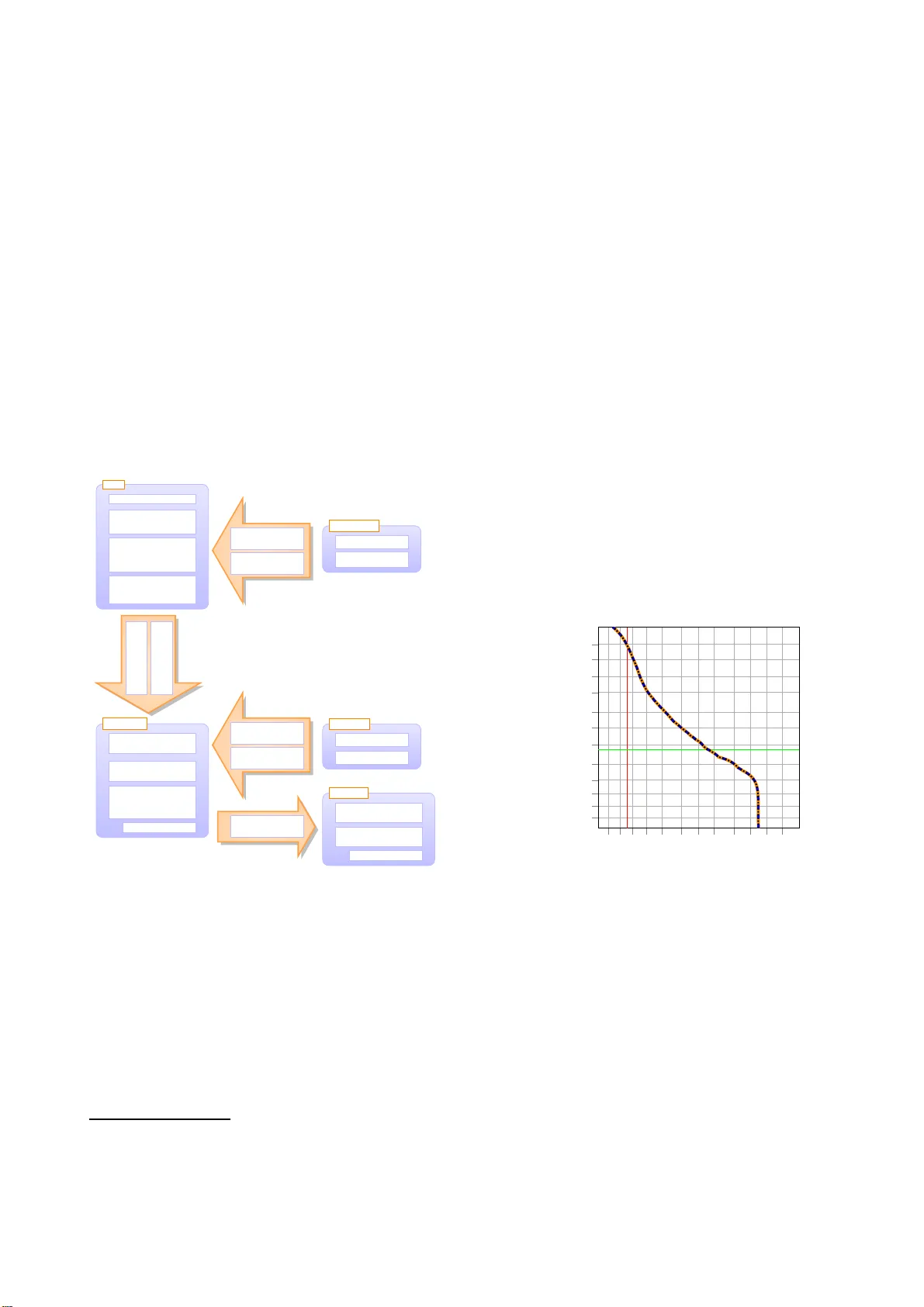
Homomorphic Encr yption f or Speak er Recognition: Pr otection of Biometric T emplates and V en dor Model Parameters Andr eas Nautsch, Ser ge y Isadskiy , J ascha K olber g, Marta Gomez-Barr er o, Christoph Busch da/sec – Biometri cs and Internet Security Research Group, Hochschu l e Darmstadt, Germany { andreas.nautsch ,sergey.isadsk iy,jascha.kolberg } @h-da.de { marta.gomez-bar rero,christoph .busch } @h-da.de Abstract Data pri v acy is crucial when dealing with biometric da ta. Ac- counting for the latest European data priv acy regulation and payment service directi v e, biometric template protection is es- sential for any commercial application. Ensu ring unlinkability across biometric service operators, irr eve rsibility of leaked en- crypted templates, and rene wability of e.g., voice models fol- lo wing the i-vector paradigm, biometric voice-based systems are prepared for the l at est EU data pri v acy leg islation. Employ- ing Paillier cryptosystems, Euclidean and cosine comparators are known to ensure data priv acy demands, without l oss of dis- crimination nor calibration performance. Bridging gaps from template protection to spea ker recognition, two architectures are proposed for the two-cov ariance comparator , serving as a gen- erativ e model in this study . The first architecture preserves pri- v acy of biometric data capture subjects. In the second architec- ture, model parameters of the comparator are encrypted as well, such that biometric service provid ers can supply the same com- parison modules emplo ying diffe rent ke y pairs to multiple bio- metric service operators. An experimental proof-of-concept and complex ity analysis i s carried out on the data from the 2013 – 2014 NIST i -v ector machine learning challenge. 1. Intr oduction The latest EU data priv acy regu lation [1] declares biometric in- formation as persona l data , i.e. highly sensitiv e and entitled to the r i ght of pri v acy preserv ation. Similarly , the current payment service directi ve [2] also requires biometric template protection to be employed in biometric systems uti l ized for banking ser- vices. T o that end, the ISO/IEC IS 24745 [3] on biometric in- formation protection provides guidance on ho w to preserv e the subject’ s pri v acy by defining the followin g three main proper- ties to be fulfilled by protected biometric templates: • unlinkability : stored biometric templates shall not be linkable across applications or databases, • irr ev ersibility : biometric samples cannot be recon- structed from protected biometric templates, • r ene wability : multiple biometric references can be inde- pendently transformed, when they are created from one or more samples of a biometric data capture subject. In addition to these properties, other performance metrics, such as recognition accuracy , should be preserved. Even if some works argu e that there i s no need for template protection depen ding on the feature extraction [4], sensiti ve in- formation can be derived from unprotected templates, as it has already been proved for other biometric characteristics [5, 6]. In particular , linkability of state-of-the-art speaker recognition fea- tures is demonstrated in [7] with the motiv ation of interchanging features among differen t voice biometric services. The inter- change of biometric data across services is recently addressed ethically in [ 8], especially when targeting forensic and in vesti- gatory scenarios. Accounting for latest data priv acy legislations, we moti v ate template protection, especially in commercial but also in other dual-use case application scenarios. Current approaches to biometric template protection can be broadly classifi ed into three categories [9], namely: i ) cance- lable biometrics [10 ], where irre versible transformations are ap- plied at sample or template lev el; ii ) cryptobiometric systems [11], where a ke y is either bound or extracted from t he bio- metric data; and iii ) biometrics in the encrypted domain [12], where techniques based on homomorphic encryption (HE ) and garbled circuits are used to protect the data. Whereas cancelable biometrics and cryptobio metric systems usually report some ac- curacy degrad ation [9], the use of H E schemes prev ents such loss, since the operations carried out in t he encrypted domain are equiv alent t o those performed with plaintext data. For this reason, we apply i n this work HE schemes simi l ar to t he ones proposed in [13 , 14, 15, 16] to speaker recognition relying on generati ve comparators, such as probabilistic linear discrimi- nant analysis (PLDA). W e thereby ensure data pri v acy f or data capture subjects for comparison models utilizing the t wo-co- v ariance (2Cov) approach [17, 18] (i.e. full subspa ce P LD A) as a prototype generativ e comparison algorithm. In contrast to con ventional discriminativ e comparators, generati ve models can emit features with associated l i kelihoo ds based on pre-trained models. Thus, comparison scores of gen- erativ e models represen t probabilistic similarit y . In this con- text, supplying model parameters to variou s service operators can arise pri v acy concerns regard ing the data protection of bio- metric service vendors, i.e. the pre-trained models. Therefore, we further propose a mutual encryption scheme granting subject and ve ndor data priv acy by employing well-established Pailli er homomorph ic cryptosystems [19, 20]. It should be finally noted that, while con ventional image based biometric systems employ non-genera tiv e comparators, operating either on binary or non- negati ve integers [15, 16, 21, 22], the generativ e comparators used in speaker recognition applications make assumptions on underlying distributions, such as normal distribution [23, 24], consequen tly operating on normal distributed fl oat values. In t he following , we make HE av ailable to speaker recog- nition, targe ting data priv acy for subjects and vendors. S ecs. 2, 3, 4 depict related wo rk on homomorphic cryptosystems and speak er recognition. Sec. 5 proposes two architectures for HE protected 2Cov comparators. A proof-of-concept study is dis- cussed in Sec. 6 with conclusions drawn i n Sec. 7 . 2. Related W ork In order to apply standardized biometric template protection schemes, binarization can be employed [3]. Related work on the binarization of traditional speak er recogn ition systems utili z- ing unive rsal backg round models (UBMs) targeting the GMM – UBM approach can be found in [25, 26, 27]. In addition, in our earlier work [28], we proposed a biometric template protection scheme for speaker r ecognition, based on binarized Gaussian mixture model (GMM) superv ectors. Ho we ver , due to t he binarization process, the biometric per- formance usually declines, and calibration properties are lost. Contrary to performance-l ossy template protection approaches as biometric cryptosystems and cancelable biometrics [9], HE completely preserves biometric accurac y . T herefore, we in ves- tigate on Paillier HE schemes, which are already introduced to other biometric modalities, such as signature [13], iris [21], and fingerprint [ 22] recognition, considering Hamming distances (XOR operator), dynamic time warping (DT W), the Euclidean distance, and the cosine similarity . W e thus focus on homomor - phic cryptosystems for the remainder of the article. In [29] and [30], the authors provide an ov ervie w of sev - eral biometric template protection schemes based on homomor- phic encryption and garbled circuits. Barni et al. [22] present a way to protect fixed-length fi ngercodes [31] using homomor- phic encryption. This system was modified in [32] to accelerate the process by reducing the size of t he fingercode. Howe ver , a reduction of i nformation also leads to a degradation of biomet- ric recognition performance. Y e et al . present an anonymo us biometric access control (AB A C) system [33] for iris recogni- tion. Their system setup verifies only whether a subject is en- rolled wi thout reve aling the identity and thus grants anonymity to wards the subjects. Another AB A C protocol is proposed in [34] by Luo et al. and a secure similarit y search algorithm is presented for anony mous authentication. Combining homomor - phic encryption with garbled circuits, Blanton and G asti [35] implement secure protocols for iris and fingerprint recognition. Among the existing cryptosystems in the lit erature, encryp - tion algorithms based on latti ces are assumed to be post- quan- tum secure [36, conjecture 2], which is a conv enient property for a public ke y encryption scheme. Usi ng ideal lattices in a some what homomorphic encryption (SHE) scheme, Y asuda et al. [37] compute the Hamming distance of encrypted templates in an efficient way by using a packing method before the en- cryption. By using binary feature vectors with a constant size of 2 048 bits for e very biometric data, again Y asuda et al. [38] present a new packing method in a SHE scheme for biometric authentication based on a special version of the ring learning with errors assumption. Another priv acy-preserving biometric authentication approach [39 ] splits a 2 048 bits iris code i nto 64 blocks with 32 b its each and encrypts these blocks using n-th degree truncated polyno mial ring (NTR U). As in the afore- mentioned works, scores are computed in the encrypted domain without disclosure of biometric information. 3. Homomorphic Cryptosystems Homomorphic encryption [40, 41, 42] has the property that computations on t he ciphertext are equi valent to those car- ried out on the plaintext. In particular , homomorphisms are functions which preserv e algebraic structures of groups [ 43]. The function f ∶ G → H is a homomorphism for groups ( G, ◇) , ( H, ) w i th sets G, H and operators ◇ , if: f ( g ◇ g ′ ) = f ( g ) f ( g ′ ) ∀ g , g ′ ∈ G. (1) Public-k ey cryptosystems ( K, M , C , enc , dec ) with sets of ke ys K , plaintexts M , ciphertexts C , and functions represent- ing encryption enc and decryption d ec are homomorphic i f : ∀ m 1 , m 2 ∈ M , ∀ pk ∈ K ∶ enc pk ( m 1 ) enc pk ( m 2 ) = enc pk ( m 1 ◇ m 2 ) , (2) where the public key pk is used for encryption and the secret ke y sk for the decryption functions, respecti ve ly: enc pk ∶ M → C , dec sk ∶ C → M . (3) 3.1. Paillier HE Scheme Moti v ated by asymmetric Paillier cryptosystems [19, 20], HE has been made av ailable to biometric template protection [13, 15, 16 ] . Paillier cryptosystems are homomorphic probabilistic encryption schemes based on the decisional composite residu- osity assumption (DCRA): for i ntegers n, z it is hard to decide, whether z is an n -residue modulo n 2 . Due to this assumption, the Pailli er cryptosystem is secure against honest but curious users conducting chosen cipherte xt attacks [19, 44, 45]. In the Paillier cryptosystem, the public key pk = ( n, g ) is defined by n = p q and g ∈ Z ∗ n 2 , where p, q are two large prime numbers, such that gcd ( p q , ( p − 1 ) ( q − 1 )) = 1 , and with Z ∗ n 2 as the set of module n 2 integers hav ing a modular multiplicativ e in v erse. The modular multiplicativ e in verse to is r equired with gcd ( , ) = 1 : ≡ 1 ( mod n 2 ) . Based on p, q , the secret ke y sk = ( λ, µ ) is defined by λ = lcm ( p − 1 , q − 1 ) and µ = mod n with = L ( g λ mod n 2 ) and L ( x ) = x − 1 n . During encryption c = enc pk ( m, s ) ∈ Z ∗ n 2 of a message m ∈ Z n with public ke y pk , a random numbe r s ∈ Z ∗ n provid es the probabilistic nature of the cryptosystem, i.e. enc pk ( m, s 1 ) ≠ enc pk ( m, s 2 ) for two dif ferent s 1 , s 2 ∈ Z ∗ n : c = enc pk ( m, s ) = g m s n mod n 2 , (4) which is abbreviated in the follo wing as enc pk ( m ) . Ciphertexts are decrypted as: m = d ec sk ( c ) = L c λ mod n 2 µ mod n. (5) Similarly t o [13, 15, 16, 20], we utilize the additi ve homo- morphic properties of the Paillier cryptosy stem regarding plain- texts m 1 , m 2 and corresponding ciphertexts c 1 , c 2 : dec sk ( c 1 c 2 ) = m 1 + m 2 mod n, dec sk c 1 l = m 1 l mo d n, with a constant l . (6) In other words, whereas the decrypted product of two cipher- texts is equiv alent to the sum of two plaintex ts, the correspond - ing expon entiation of a ciphertext results in the product of the correspondin g plaintext and constant as ex ponent. 3.2. Homomo rphic T emplate P rotection T argeting biometric template protection, data priv acy friendly comparison schemes are sought, i n which only encrypted refer- ences, i.e. no plaintexts, are stored in databases. As such, the Euclidean and cosine similarity comparison scores S Euc , S cos between t wo F -dimensiona l ve ctors X = { x 1 , . . . , x F } , Y = { y 1 , . . . , y F } are computationally deri v ed as [13, 15, 16]: S Euc ( X , Y ) = F f = 1 x 2 f + F f = 1 y 2 f − 2 F f = 1 x f y f , (7) and the correspon ding encryp ted score enc pk ( S Euc ( X , Y ) ) : enc pk ( S Euc ( X , Y )) = enc pk F f = 1 x 2 f enc pk F f = 1 y 2 f F f = 1 enc pk ( y f ) − 2 x f , (8) where the protected reference Y enc pk Euc is defined as: Y enc pk Euc = enc pk F f = 1 y 2 f , ( en c pk ( y f )) F f = 1 . (9) On t he other hand, the cosine comparison is deriv ed as [13, 15]: S cos ( X , Y ) = X ′ Y X Y = F f = 1 x f X y f Y , enc pk ( S cos ( X , Y ) ) = F f = 1 enc pk y f Y x f X , (10) where the protected reference Y enc pk cos is defined for length-nor- malized features as: Y enc pk cos = ( enc pk ( y f )) F f = 1 = enc pk ( Y ) . (11) In [13, 15], solely positi ve integers are considered. Accommo- dating a broader range of only positiv e float values, a 10 12 scal- ing factor is employ ed. Accoun ting for negati v e fl oat v alues, this study relies on an alternative float representation. Client DB controller AS operator 1. Ex tract probe: X 3. Com pute: enc pk ( S cos ) = 2 X enc pk ( Y ) 2. Send: enc pk ( Y ) 4. Send: enc pk ( S cos ) 5. Decrypt score: S cos = dec sk ( 4 ) 6. Decision: ( η ≤ 5 ) → yes / no pk , sk Figure 1: Architecture of homomorphic encrypted cosine simi- larity comparison for length-normalized features, cf. [13], with client, servers (blue) and commun ication channels (orange). Fig. 1 illustrates a distr ibuted client – server architecture employ ing HE with a cosine comparison: a client C extracts the probe feature vector X and requests the encrypted reference feature vector enc pk ( Y ) from the database DB contr oller . Then, scores are calculated on the client, and sent to the authentica- tion server AS operator , which holds the key pair ( pk , sk ) . Based on pre-defined threshold, AS operator outputs the decision D of whether the decrypted score S cos is greater or equal to a thresh- old η , or not. Ideally , DB contr oller is in the domain of an inde- pendent data controller , restricting access to operators among others. T ab. 1 prov ides an overvie w to the comple xity of t he en- crypted E uclidean and cosine comparison, where numbers di- ver ge from [ 13] as in the signature recognition scenario, fiv e reference templates are encrypted rather than e. g., an averaged template model. As references are encrypted during enrolment, cosine-based biometric comparisons require no additional en- cryptions, whereas in Euclidean-based comparisons, the probe templates need t o be encrypted. T able 1: Complex ity analysis for the Euclidean and cosine com- parators during verification, cf. [13], assuming F = 250 dimen- sional features, the size of an encrypted feature c = 0 . 5 KiB , and the plain feature size p = 64 b its . Euclidean Cosine N o encryptions F 0 N o decryptions 1 1 N o additions F − 1 0 N o products 2 F + 4 F − 1 N o exponentiations 2 F F Plain template size p F p F ≈ 2 . 0 Ki B ≈ 2 . 0 KiB Protected template size c ( F + 1 ) c F = 125 . 5 KiB = 125 . 0 KiB Channels: amount of c ( F + 2 ) c ( F + 1 ) protected data exchanged = 126 . 0 KiB = 125 . 5 KiB 4. Speak er Recognition: 2Cov Comparator Recent speak er recognition approaches rely on intermediate- sized vecto rs (i-vectors), representing the characteristic speak er of fset fr om an UBM, which models the distribution of acous- tic features, such as Mel-F requenc y Cepstral Coef ficients (MFCCs) [46]. UBM components’ mean vectors are concate- nated to a supervector µ UBM . Seeking non-sparse features, speak er superv ectors s are decompose d by a total v ariabil- ity matrix T into a lo wer-dimensional and higher-discriminant i-vectors i as an of fset to t he UBM supervector µ UBM : s = µ UBM + T i . (12) The total v ariability matrix is trained on a dev elopment set us- ing an expectation maximization algorithm [23, 24]. Then, i-vectors are projected onto a unit-spherical space by whit en- ing transform and length-normalization [47, 48]. State-of-the-art i-vector comparators belong t o the PLDA family [18, 48]. P LD A comparators conduct a likelihood ratio scoring comparing the probabilities of the hypotheses that ref- erence and probe i - vectors X , Y stem from (a) the same source or (b) dif ferent sources. Therefore, within and between speake r v ariabilities are examined in a latent feature subspace. In this work, emphasis is put on the 2Cov approach [17, 18], the full- subspace Gaussian PLDA. Notably , the 2Cov comparator can also be related to pairwise supp ort vector machines [17, 18]. For the sak e of tractability , this study focuses on the generativ e 2Cov model. Also, i-vectors are solely considered as point esti- mates, assuming ideal precision during feature extraction. The closed-form solution to the 2Cov scoring is denoted regarding within and between cov ariances W − 1 , B − 1 with mean µ [17]: S 2Cov ( X , Y ) = X ′ Λ Y + Y ′ Λ X + X ′ Γ X + Y ′ Γ Y + c ′ ( X + Y ) + k , Λ = 1 2 W ′ ˜ Λ W , Γ = 1 2 W ′ ˜ Λ − ˜ Γ W , c = W ′ ˜ Λ − ˜ Γ B µ , k = ˜ k + 1 2 ( B µ ) ′ ˜ Λ − 2 ˜ Γ B µ , ˜ Λ = ( B + 2 W ) − 1 , ˜ Γ = ( B + W ) − 1 , ˜ k = 2 log ˜ Γ − log ˜ Λ − log B + µ ′ B µ . (13) 5. Pr oposed Ar chitectur e In t he following, two discriminati ve HE schemes are propo sed. The fi rst puts emphasis on HE for i - vectors during 2Cov com- parison, seeking data priv ac y for end-users, whereas the sec- ond scheme focuses on the encryption of i-vectors as well as 2Cov model parameters, targeting data protection for subjects and vendo rs. An auxiliary float representation is implemented, encoding float v alues as nonn egati ve intege rs for the purpose of provid ing Paillier properties, cf. Eq. (6). 5.1. A uxiliary Float Representation: n onnegativ e Integers For the purpose of representing fl oat values of i-v ectors as nonne gati ve integer values, i.e. seeking conformance to Pail- lier cryptosystems, t he integer encoding scheme standardized in IE EE 754 is employed [49]. Fl oats are enco ded in terms of a sign S , a mantissa M times a base B = 16 raised to an expo nent E . Nonne gative integers are deri v ed by seeking con- gruent positi ve representations in modulo n 2 , i.e. regarding the public key domain. Accounting f or negati ve values [50], the plaintext integer domain is di vided into four interv als: [ 0 , n 3 ) for positi v e float representations, [ 2 n 3 , n ) for negati ve float r ep- resentations, and [ n 3 , 2 n 3 ) as well as [ n, ∞ ) for the purpose of detecting overflo ws resulting from pre vious Paillier HE oper- ations. T argeting Paillier HE, same expo nents of m 1 , m 2 are required, hence t he mantissa i s encrypted as a nonnegati v e in- teger representation. The plaintext exponent of the depending mantissa encoding is kept auxiliary . Security is satisfied due to the DCRA employing randomized mantissa obfuscation dur- ing encryption. In Paillier addition, encry pted mantissae are scaled for equi v alent addend exponents. In Paillier multi plica- tion, modular exponentiation of c = enc pk ( M , s ) is conducted, during which mantissae are kept rather small by it erative multi - plications than by right-aw ay exponentiation. 5.2. Data Priv acy: Protecting Subjects For the sake of tractability , we assume a zero mean, causing c = 0 , and neglect the normalization term, i. e. k = 0 , such that the following scheme solely holds for discrimi native 2Cov , ho we ve r calibrated scores can be easily achie v ed by adding the k term after score decryption : S 2Cov ( X , Y ) = X ′ Λ Y + Y ′ Λ X + X ′ Γ X + Y ′ Γ Y , = X ′ Λ Y + Y ′ ( Λ X ) + X ′ Γ X + Y ′ Γ Y . (14) For the discriminati ve 2Cov , HE is emplo yed motiv ated by the (symmetric) dot product for vector multiplication: enc pk ( Y ) X = F f = 1 enc pk ( y f ) x f = enc pk ( X ′ Y ) = enc pk ( Y ′ X ) = F f = 1 enc pk ( x f ) y f = enc pk ( X ) Y , enc pk ( S 2Cov ( X , Y )) = enc pk ( Y ) ( X ′ Λ ) enc pk ( Y ) ( Λ X ) enc pk ( X ′ Γ X ) enc pk ( Y ′ Γ Y ) , enc pk ( Y ) = ( enc pk ( y f )) F f = 1 , (15) with auxiliary vectors are denoted as ( X ′ Λ ) , ( Λ X ) , and the protected reference Y enc pk 2 C ov = ( enc pk ( Y ) , enc pk ( Y ′ Γ Y )) . Fig. 2 illustrates t he proposed HE architecture for a dis- tributed system. Similarly to the cosine comparison HE ap- proach, the scores are computed in t he encrypted domain on the cli ent, and decrypted on the authentication server . Thereby , the 2Cov score is compu ted in four parts. Client DB controller AS operator 1a. E xtract probe: X 1b. Encrypt: enc pk X ′ Γ X 3. Com pute: 2a ( Λ X ) 4. Com pute: 2a X ′ Λ 5. Com pute: enc pk S 2Cov = 1b × 2 b × 3 × 4 Γ , Λ enc pk ( Y ) enc pk ( Y ′ Γ Y ) Γ 2a. Send: enc pk ( Y ) 2b. Send: enc pk ( Y ′ Γ Y ) 7. Decrypt score: S 2Cov = dec sk ( 6 ) 8. Decision: ( η ≤ 7 ) → yes / no pk , sk 6. Send: enc pk S 2Cov Figure 2: Architecture of homomorphic encrypted 2Cov com- parison solely protecting subject data, with client, serv ers (blue) and communication channels (orange). 5.3. Data Priv acy: Protecting Subjects and V en dors Contrary to established biometric HE approaches employing non-generati ve comparators, generativ e comparators require trained hyper-parameters e.g., between and within cov ariance matrices in terms of the 2Cov comparator . For the purpose of protecting both subject and vendor data, two ke y sets are em- ployed ( pk 1 , sk 1 ) , ( pk 2 , sk 2 ) . Utilizing the F robenius inner product 1 , Eq. (13) can be reformulated [17]: S 2Cov ( X , Y ) = Λ , X Y ′ + Y X ′ + Γ , X X ′ + Y Y ′ + c ′ ( X + Y ) + k , = w ′ Λ ϕ Λ ( X , Y ) + w ′ Γ ϕ Γ ( X , Y ) + w ′ c ϕ c ( X , Y ) + w ′ k ϕ k ( X , Y ) , = w ′ ϕ ( X , Y ) , with: ϕ ( X , Y ) = vec ( X Y ′ + Y X ′ ) vec ( X X ′ + Y Y ′ ) X + Y 1 = ϕ Λ ( X , Y ) ϕ Γ ( X , Y ) ϕ c ( X , Y ) ϕ k ( X , Y ) , w = vec ( Λ ) vec ( Γ ) c k = w Λ w Γ w c w k . (16) For the si mplified 2Cov comparator , a mutual HE scheme sustaining data pri v acy for subjects and vendors can be em- ployed by extending t he inner product of vectors to the Frobe- nius inner product of matrices A , B , which can be reformulated via t he vec ( ⋅ ) operator as the inner product of (column-stacked) vectors, such that the dot product can be emplo yed as well with a public key pk : enc pk ( A ) ⟨⟩( B ) = enc pk ( vec ( A )) ve c ( B ) , (17) where the encryption of a matrix A is denoted as: enc pk ( A ) = ( enc pk ( a i,j )) F i = 1 F j = 1 . (18) 1 The inner Frobeniu s product denotes x ′ A y = ⟨ A , x y ′ ⟩ = v ec ( A ) ′ v ec ( x y ′ ) , where v ec ( ⋅ ) denotes the operator stacking ma- trices into a vect or and ⟨ A , B ⟩ is the dot product between matrices, cf. [17]. In the simplified 2Cov comparator , the encrypted vendor and operator communication takes the form: S 2Cov ( X , Y ) = w ′ Λ ϕ Λ ( X , Y ) + w ′ Γ ϕ Γ ( X , Y ) , enc pk2 ( S 2Cov ( X , Y )) = enc pk2 ( Λ ) ⟨⟩( c 1 ) enc pk2 ( Γ ) ⟨⟩( c 2 + c 3 ) , with: c 1 = X Y ′ + Y X ′ , c 2 = X X ′ , c 3 = Y Y ′ , (19) where the computation of c 1 , c 2 , c 3 is subdue to the encrypted operator , controller and end- user communication : enc pk1 ( c 1 ) = enc pk1 ( Y ) X ′ ○ enc pk1 ( Y ′ ) X , enc pk1 ( c 2 + c 3 ) = enc pk1 ( X X ′ ) ○ enc pk1 ( Y Y ′ ) , (20) where ○ denotes the Hadamard product 2 , and the terms enc pk1 ( Y ) X ′ , enc pk1 ( Y ′ ) X represent expo nentiations in an outer product fashion, resulting in t he matrices enc pk1 ( Y X ′ ) and enc pk1 ( X Y ′ ) , r espectively . Finally , the protected refer- ence is Y enc pk1 2Cov = ( enc pk1 ( Y ) , enc pk1 ( Y Y ′ )) . Client DB controller AS operator DB vendor AS vendor 1a. Extract probe: X 1b. Encrypt: enc pk1 X X ′ 3. Com pute: enc pk1 ( c 1 ) = 2a X ′ ○ 2a ′ X 4. Com pute: enc pk1 ( c 2 + c 3 ) = 1b ○ 2b enc pk1 ( Y ) enc pk1 Y Y ′ 2a. Send: enc pk1 ( Y ) 2b. Send: enc pk1 Y Y ′ 7. Decrypt: c 1 = dec sk1 ( 5a ) 8. Decrypt: c 2 + c 3 = dec sk1 ( 5b ) 9. Com pute: enc pk2 S 2Cov = 6a ( 7 ) 6b ( 8 ) pk1 , sk1 , pk2 5a. Send: enc pk1 c 1 5b. Send: enc pk1 c 2 + c 3 enc pk2 ( Λ ) enc pk2 ( Γ ) 6a. Send: enc pk2 ( Λ ) 6b. Send: enc pk2 ( Γ ) 11. Decrypt score: S 2Cov = dec sk2 ( 10 ) 12. Decision: ( η ≤ 11 ) → yes / n o pk2 , sk2 10. Send: enc pk2 S 2Cov Figure 3: Architecture of protected templates and hype r- parameters, with client, servers (blue) and communication channels (orange). Fig. 3 presents the proposed architecture. The prev iously proposed architecture is extende d by additional communication channels between operators and vendors. Applications employ two ke y pairs, such that template protection can be achiev ed dependen t on both: (a) dif ferent biometric services of an opera- tor , and (b) multiple pro visions of a biometric system to service operators by a vendor . Consequently , additional servers are nec- essary on the vendor site in terms of a database DB vendor and an authentication server AS vendor , respectiv ely . 2 The Hadamard product is an entrywise product of two matrices A , B havi ng the same dimension: A ○ B = ( A ) i,j ( B ) i,j . 6. Experimental Analysis and Discussion An experimental validation is conducted on the 2013 – 2014 NIST i-v ector machine learning challenge [51, 52] phase III database (i. e. with labeled de velo pment data), where 600 di- mensional i-ve ctors are supplied, comprising a de velop ment set of 36 572 i-vectors, 1 306 r eferences with each five enrolment i-vectors, and 9 634 probes, conducting 12 582 004 c ompar- isons on av eraged reference i-vectors as template models. The prototype system comprises a dimension reduction to F = 250 by linear discriminant analysis, within class cov ariance nor - malization, length normalization, and 2Cov comparison. For the Paillier cryptosystem, n = 2 048 bits keys are utilized, in accordance with the NIST recommendation [53]. In contrast, plaintext operations consider double floating-point precision, i.e. p = 64 bits per plain real feature value. Implementations are based on the freely av ailable sidekit [54] and Python P ail- lier [50]. Fig. 4 il l ustrates the DET performance of con ventional and HE 2Cov comparators on the ev aluation set i n terms of false non-match rate (FNMR) and false match rate (FMR): the base- line performance is preserved across all operating points. The DET is depicted in t erms of the con ve x hull of the r ecei ver oper- ating characteristic (R OCCH). For the exemplary 2Cov system, a 2 . 5% equal error rate (ROCCH-EER), a 0 . 050 minDCF (pa- rameterized according to [51]), and a 0 . 099 C min llr are preserved in the protected domain. As the k normalization term is ne- glected in this set-up, the baseline system yielded a 9 . 560 C llr . Calibration loss can be reduced by a post score re-bias, or by employ ing con vention al score calibration methods, cf. [55]. B y utilizing linear score calibration tr ained on the oracle dev elop- ment set, C llr is reduced to 0 . 284 . 0 . 00001 0 . 0001 0 . 001 0 . 01 0 . 1 1 5 15 40 65 85 95 0 . 00001 0 . 0001 0 . 001 0 . 01 0 . 1 1 5 15 40 65 85 95 FMR (in %) FNMR (in %) Figure 4: DE T comparison of the baseline 2Cov system ( or- ange), and t he proposed H E 2Cov schemes, focusing on subject data protection (blue, dashed), and the protection of subject and vend or data (black, dotted) wi th rule of 30 bound s (red, green). As the verification performance is preserved, the proposed schemes are further examined regarding requirements of the biometric template protection standard [3] in terms of [ 13 ]: i ) only the client can have access to the plain prob e template, ii ) the plain refer ence t emplate should not be seen by the client, and only its encryption should be stored or handled during ver- ification, and iii ) the scor e should also be pr otected in or der to pr event hill-cli mbing and in verse-biometrics attacks . Fi r stly , both employed homomorph ic Paillier cryptosystem pro vide se- mantic security: only secret keys are able to deri ve the plain probe after encryption, where the client solely communicates the encrypted score ( enc pk ( S 2Cov ( X , Y ) )) or auxiliary matri- ces ( enc pk 1 ( c 1 ) , enc pk 1 ( c 2 + c 3 )) . Secondly , biometric ref- erences are communicated from the controller database server to the cli ent i n the encrypted domain, assuming the authentica- tion server being able to protect the secret key sk 1 , no other entities will be able to r el ate the protected biometric informa- tion. Similarly , the vendor data is protected in the sense, t hat the vendor authentication server is assumed to be able to protect sk 2 . F inally , scores are computed in the protected domain, and can solely be decrypted utilizing secret key sk 2 . Thus, the i rre- versibility criterion is met. Rene wab ility is granted as depicted in [13]: if templates are lost, ne w ke y pairs can be generated for the purpose of re-encrypting the database, such that ( a) re- acquisitions of enrollment samples are avoided when rev oking corrupted templates, and (b) comparisons of corrupt to rene wed templates result in non-matches, granting security and data pri- v acy . Thus, templates can easily be revok ed, t hereby providing data priv acy . Unlinkability is granted due to the probabilistic nature of the Paillier cryptosystem, where random numbers are utilized for dif ferent encryptions, i.e. encrypting the same data Y t wice, two different random numbers s 1 , s 2 are drawn, such that: enc e ( Y , s 1 ) ≠ enc e ( Y , s 2 ) , cf. [13, 19]. T able 2: Complexity analysis for the proposed 2Cov HE schemes (verification) with the data sizes of the ex emplary em- ployed system ( p = 64 bits , ν = 0 . 5 KiB , F = 250 ). Comparator 2Cov 2Cov Protection subject subject & vendor N o encryptions 1 F 2 N o decryptions 1 2 F 2 + 1 N o additions 4 F ( F − 1 ) 0 N o products 4 F 2 + 2 F + 1 5 F 2 − 1 N o exponentiations 2 F 4 F 2 Plain template size p F p F ≈ 2 . 0 Ki B ≈ 2 . 0 Ki B Protected template size ν ( F + 1 ) ν ( F 2 + F ) = 125 . 5 KiB ≈ 30 . 6 MiB Plain model size 2 p F 2 2 p F 2 ≈ 1 . 0 MiB ≈ 1 . 0 M iB Protected model size 0 2 ν F 2 = 0 KiB ≈ 61 . 0 Mi B Channels: amount of ν ( F + 2 ) ν ( 5 F 2 + F + 1 ) protected data exchanged = 126 . 0 KiB ≈ 152 . 7 MiB In terms of complexity , each approach can be analyzed re- garding the amount of required resources, i.e. t he number of operations performed in the encrypted domain as well as the size of encrypted data sent ov er a channel. For a single veri- fication attempt, the chipertex t channel bandwidth is ν = 2 n due to the Paillier ciphertext length in modulo n 2 domain [ 13], i.e. ν = 4 096 bits 1 KiB 8 192 bits = 0 . 5 KiB for the examined sys- tem. T ab . 2 summarizes the proposed HE schemes’ complexity . Regarding to an i-vector dimension F = 250 , the cosine HE approach requires ν F = 125 KiB for storing a reference i -vec- tor . For transmitting the protected score to the authentication server , 0 . 5 KiB are necessary , i.e. a protected scalar . The sub- ject protectiv e 2Cov HE scheme stores a reference tuple with ν ( F + 1 ) = 125 . 5 KiB , communicating a protected scalar as well to the authentication serve r . Howe v er , the subject and ven- dor protective 2Cov HE scheme stores protected auxiliary ma- trices, requiring ν ( F 2 + F ) ≈ 30 . 6 MiB . T herefore, the chan- nel between client and authentication server considers two pro- tected matrices, requiring 2 ν F 2 ≈ 61 . 0 MiB , alike for t he ven- dor database to operator authentication server channel. Regard- ing the protected data exch anged ov er the commun ication chan- nels, the first proposed scheme comprises ν ( F + 2 ) = 126 KiB as the protected template and score are transmitted. The sec- ond proposed scheme demands higher requirements: as the model hyp er-parame ters are protected, the cli ent to authenti- cation server channel t r ansmits auxiliary matrices comprising 2 ν ( F 2 ) ≈ 61 . 0 MiB , whereas the same data amount is loaded for the protected model from the vendor database server . Fi- nally , a protected score is transmitted to the vendor authentica- tion server , making application decisions. Afterwards, con ve n- tional security protocols can be employed. 7. Conclusion Homomorphic template protection is made av ai l able to genera- tiv e comparators, i.e. comparators employing statistical models, where the related biometrics work solely considers non-genera- tiv e comparato rs, such as XOR, DTW , Euclidean distance, and cosine similarity . Extending the HE scheme for cosine simi- larity comparison, template protection is made av ailable to the 2Cov comparator in two architectures. The first proposed HE architecture solely puts emphasis on the protection of t emplates, which can be sustained under a fair complexity tradeoff. Con- trastiv ely , the second proposed HE 2Cov scheme provides sub- ject and vendor data protection. Howe v er , the required com- plexity increases by a quadratic term. By pre-loading both pro- tected model parameters the channel bottleneck is reduced to ν ( 3 F 2 + F + 1 ) ≈ 91 . 7 MiB for a si ngle verification attempt, which howe ver limits the app lication scope to well-equipped infrastructures e.g., call center and forensic scenarios. Depend- ing on the application scenario, protected templates may al so be pre-loaded, further reducing t he ov erall transmitted data amount to ν ( 2 F 2 + 1 ) ≈ 61 . 0 MiB . For mobile device voice biomet- rics, one may prefer to employ the fi rst proposed architecture. Both approaches ensure biometric template protection require- ments as of the IS O/IEC 24745 standard. For the sak e of repro- ducibility , we pro vide a reference implementation. As the proposed schemes target 2Cov as prototype gener- ativ e comparators, i.e. the full- subspace Gaussian P L D A spe- cial case, ex tensions to other members of the PLD A family and related comparators can be easily dev eloped. Accounting for i-vectors not only as si ngle point estimate features bu t also as latent v ariables, uncertainties associated to the single point esti- mation can be i ncorporated as well, e.g. targeting full-posterior PLD A. Also, HE schemes seem promising for end-to-end neu- ral network system architectures, as the inner Frobenius prod- uct is computable in the protected domain. Extensions of the proposed architectures and implementations of alt ernati ve HE schemes is left to future work. 8. Ackno wledgements This work was supported by the German Federal Ministry of Education and Research (BMBF) as well as by the H es- sen S tate Ministry for Higher Education, Research and the Arts within the C enter for Research in S ecurity and P riv acy ( www.crisp- da.de ), and the BioMobile II project (no. 518/16-30 ). 9. Refer ences [1] European C ouncil, “Dir ective 2016/68 0 of the European Parliament and of the Council on the protection of in- di viduals with regard to the processing of personal data by competent authorities for the purposes of t he pre ve n- tion, in vestigation, detection or prosecution of criminal of fences or the e xecu tion of criminal penalties, and on the free mo veme nt of such data, and repealing Counc il Framew ork Decision 2008/977/JHA, ” April 2016. [2] European Parliament and European Council, “Directiv e 2015/236 6 of the European Parliament and of the Council of 25 Nov ember 2015 on payment services in the internal market, ” Nov ember 2015. [3] ISO/IEC JT C 1 SC27 S ecurity T echnique s, ISO/IEC 24745:20 11. Information T echn ology - Secu rity T ech- niques - Biometric Information Pr otection , International Organization for Standardization, 2011. [4] C. V aquero and P . Rodr´ ıguez, “On the need of template protection for voice authentication, ” in Pr oc. Annual Conf. of the Intl. Speech Communication Association (IN TER- SPEECH) , 2015, pp. 219–2 23. [5] R. Cappelli, D. Maio, A. Lumini, and D . Maltoni, “Fi n- gerprint image reconstruction from standard templates, ” IEEE Tr ans. on P attern Analysis and Machine Intelli- gence , vo l. 29, no. 9, pp. 1489–1503, 2007. [6] J. Galbally , A. Ross, M. Gomez-Barrero, J. Fierrez, and J. Ortega-Garcia, “Iris image reconstruction from binary templates: An efficient probabilistic approach based on genetic algorithms, ” Computer V i si on and Image Under- standing , vol. 117, no. 10, pp. 1512–1525, 2013. [7] O. Glembek, P . Matejka, O. Plchot, J. Pesan, L. Burget, and P . S chwarz, “ Migrating i -vectors between speak er recognition systems using regression neural network s, ” in Pr oc. A nnual Conf. of the Intl. Speech Communication As- sociation (INT E RSPEECH) , 2015, pp. 2327–2331 . [8] E. Moyakine, C. Colonnello, J. Butler, and C. Jasserand, “Discussion panel: SIIP and INGRESS research projects: Dev eloping effe ctiv e and sustainable biometric systems with a global reach, ” 2017, EAB Research Projects Conference, [ Onli ne] https://www.e ab.org/upload/ documents/1279/08- eabrpc2017_SIIP_INGRESS.zip?ts=1517990107115 , last accessed: 2018-02-07. [9] C. Rathgeb and A. Uhl, “ A survey on biometric cryp- tosystems and cancelable biometrics, ” EURASIP J ournal on Information Security , vo l. 3, 2011. [10] V . M. Patel, N. Ratha, and R. Chellappa, “Cancelable biometrics: A revie w , ” IEEE Signal Pro c. Ma gazine , vo l. 32, no. 5, pp. 54–65, 2015. [11] P . Campisi, Ed., Security and Privacy in Biometrics , Springer , 2013. [12] C. Aguilar-Me lchor , S. Fau, C. Fontaine, et al., “Recent adv ances in homomorphic encryption: A possible future for signal processing in the encrypted domain, ” IE E E Signal Pr ocessing Magazine , vo l. 30, no. 2, pp. 108–117, 2013. [13] M. Gomez-Barrero, J. Fierrez, J. Galbally , E. Maiorana, and P . Campisi, “Implementation of fixed length template protection based on homomorphic encryption with appli- cation to signature biometrics, ” in Pr oc. Conf. on Com- puter V ision and P attern Recognition W orkshops (CVPR) , 2016, pp. 191–198. [14] M. Gomez-Barrero, C. Rathgeb, J. Galbally , C. Busch, and J. Fi err ez, “Unlinkable and irreversib le biometric tem- plate protection based on bloom filters, ” Information Sci- ences , vol. 370–371, pp. 18–32 , 2016. [15] M. Gomez-Barrero, E. Maiorana, J. Galbally , P . Campisi, and J. Fierrez, “Multi-biometric template protection based on Homomorphic E ncryption, ” P attern Recogn ition , vol. 67, pp. 149–163, 07 2017. [16] M. Gomez-Barrero, J. Galbally , A. Morales, and J. Fier- rez, “Priv acy-preserving comparison of variable-length data with application to biometric template protection, ” IEEE Access , vol. 5, no. 1, pp. 8606–8619, 12 2017. [17] S . Cumani, N. Br ¨ ummer , L. Burget, P . Laface, O. Pl chot, and V . V asilakakis, “Pairwise discriminati v e speak er ver- ification in the i-ve ctor space, ” IEEE T rans. on Aud io, Speec h, and Langua ge Pr ocessing (T ASLP) , vol. 21, no. 6, pp. 1217–1227, 2013 . [18] S . Cumani and P . Laface, “Generati ve pairwise models for speak er recogn ition, ” in Pro c. Odysse y 2014: T he Speaker and Languag e Recognition W orkshop , 2014, pp. 273–279. [19] P . Paillier , “Public-ke y cryptosystems based on composite degree residuosity classes, ” in P r oc. Advances in Cryptol- ogy — EUROCRYPT , 1999, pp. 223– 238. [20] H. Zhu, X. Meng, and G. Ko llios, “Pri v acy preserving similarity ev aluation of time series data, ” in Proc . Intl. Conf. on Ext ending Database T echnolo gy (EDBT) , 2014, pp. 499–510. [21] G. M. Penn, G. P ¨ otzelsberger , M. Rohde, and A. Uhl, “Customisation of paillier homomorphic encryption for efficien t binary biometric feature vec tor matching, ” in Pr oc. IEEE Intl. Conf. Biometrics Special Inter est Group (BIOSIG) , 2014, pp. 1–6. [22] M. B arni, T . Bianchi, D. Catalano, M. Di Raimondo, R. D. Labati, et al., “ A priv acy-compliant fingerprint recogni- tion system based on homomorphic encryp tion and fin- gercode templates, ” in Proc. Intl. Conf. on Biometrics: theory applications and systems (BT AS) . IE EE, 2010 , pp. 1–7. [23] N. Dehak, P . J. K enny , R. Dehak, P . Dumouch el, and P . Ouellet, “Front-end factor analysis for speak er verifi- cation, ” IEEE T ra ns. on Au dio, Speec h, and L angua g e Pr ocessing (T ASLP) , vol. 19, no. 4, pp. 788– 798, 2011. [24] P . Kenn y , “Joint f actor analysis of speaker and session v ariability: Theory and algorithms, ” T ech. Rep. CRIM- 06/08-13, CRIM, Montreal, 2005. [25] X. Anguera and J. F . B onastre, “ A novel speaker binary ke y deriv ed from anchor models, ” in Pr oc. Annual Conf. of the Intl. Speech Communication Association (IN TER- SPEECH) , 2010, pp. 2118– 2121. [26] J. F . Bonastre, P . M. Bousquet, D. Matrouf, and X. Anguera, “Discriminant binary data representation for speak er recogn ition, ” in Pr oc. IEEE Intl. Conf. on Acous- tics, Speech, and Signal Proce ssing (ICASSP) , 2011, pp. 5284–5 287. [27] G. Hern ´ andez-Sierra, J. F . Bonastre, and J. Calvo de Lara, “Speaker recognition using a binary representation and specificities models, ” in Pro c. Iber oamerican Congr ess on P attern Recognition (CIARP ) , 2012, pp. 732–739. [28] M. Paulini, C. Rathgeb, A. Nautsch, H. Reichau , H. Reininger , and C. Busch, “Multi-bit all ocation: Prepar- ing voice biometrics f or template protection, ” in Pr oc. Odysse y 2016: The Speaker and Langua ge Recognition W orkshop , 2016, pp. 291–296 . [29] M. Barni, G. Droandi, and R. Lazzeretti, “Priv ac y protec- tion in biometric-based recognition systems: A marriage between cryptography and signal processing, ” IEEE Sig- nal Pro cessing Maga zine , vol. 32, no. 5, pp. 66–76, 2015. [30] J. Bri nger , H. Chabanne, and A. Pate y , “Priv acy- preserving biometric identification using secure multi- party computation: An ov ervie w and recent trends, ” IEEE Signal Pro cessing Maga zine , vol. 30, no. 2, pp. 42–52, 2013. [31] A. K. Jain, L. Hong, S. Pankanti, and R. B olle, “ An identity-authentication system using fingerprints, ” Pr oc. of the I E EE , vol. 85, no. 9, pp. 1365–13 88, 1997. [32] T . B ianchi, S. Tu rchi, A. Piv a, R. D. Labati, V . P iuri, and F . S cotti, “Implementing fingercode-based identity match- ing in the encrypted domain, ” in IEEE W orkshop on Bio- metric Measur ements and Systems f or Security and Medi- cal Applications (BIOMS) , 2010, pp. 15–21. [33] S . Y e, Y . Luo, J. Zhao, and S. Cheung, “ Anonym ous bio- metric access control, ” EU R ASIP Jou rnal on Information Security , vol. 2009, no. 1, pp. 1–17, 2009. [34] Y . Luo, S. C. S en-ching, and S. Y e, “ Anonym ous biomet- ric access control based on homomorphic encryption, ” in Pr oc. Intl. Conf. on Multimedia and Expo (ICME) , 2009, pp. 1046–1049 . [35] M. Blanton and P . Gasti, Secur e and Efficient Pr oto- cols for Iris and Fing erprint Identification , pp. 190–209, Springer Berlin Heidelberg, 2011. [36] D. J. Bernstein, J. B uchmann, and E. Dahmen, P ost- Quantum Crypto grap hy , Springer Science & Business Media, 2009. [37] M. Y asuda, T . Shimoyama, J. K ogure, K. Y okoy ama, and T . K oshiba, “Packed homomorphic encryption based on ideal latt ices and it s application to biometrics, ” in Pr oc. Intl. Conf. on A vailability , Reliability , and Security , 2013, pp. 55–74. [38] M. Y asuda, T . Shimoyama, J. K ogure, K. Y okoy ama, and T . K oshiba, “New packing method i n somewhat homo- morphic encryption and its app lications, ” Security and Communication Netw orks , vol. 8, no. 13, pp. 2194–2213, 2015. [39] C. Patsakis, v an J. Rest, M. Chora ´ s, and M. Bouroch e, “Priv acy-preserving biometric authentication and match- ing via lattice-based encryption , ” in Pr oc. Intl. W orkshop on Data Privacy Mana gement , 2015, pp. 169–1 82. [40] R. L. Riv est, L. A dleman, and M. L. Dert ouzos, “On data banks and priv acy homomorphisms, ” F ound ations of se- cur e computation , vol. 4, no. 11, pp. 168–180, 1978. [41] C. Fontaine and F . Galand, “ A survey of homomorphic encryption for nonspecialists, ” EURASIP Journa l on In- formation Security , v ol. 2007, 2007. [42] J. Hof fstein, J. Pipher , and J. H. Silverman, An Intr oduc- tion to Mathematical Crypto grap hy , Springer , 2008. [43] T . W . Hungerford, Algebra , Springer Gr aduate T exts in Mathematics, 1974. [44] M. Bellare, A. Desai, D. Pointche v al, and P . R ogaway , “Relations among notions of security for public-ke y en- cryption schemes, ” in Pr oc. Advances in Cryptology (CRYPTO) , 1998, pp. 26–45 . [45] P . Paillier and D. Pointche v al, “Efficient public-ke y cryp- tosystems prov ably secure against active adv ersaries, ” in Pr oc. Advances in Cryptograp hy — ASIACRYPT , 1999, pp. 165–179. [46] D. A. Reynolds, T . F . Q uatieri , and R . B. Dunn, “Speaker verification using adapted gaussian mixture models, ” Con versational Speech, Digital Signal Pro cessing , vol. 10, pp. 19–41, 2000. [47] D. Garcia-Romero and C.Y . Epsy-Wilson, “ Analysis of i-vector length normalization in speaker recognition sys- tems, ” in Pr oc. Annual Conf. of the Intl. Speec h Communi- cation Association (INTE R SPEECH) , 2011, pp. 249–252. [48] P . -M. Bousquet, J.-F . Bonastre, and D. Matrouf, Iden- tify the Benefits of the Differ ent Steps in an i-V ector Based Speak er , chapter CIARP , Part II, pp. 278–285, Springer- V erlag Berlin Heidelberg, 2013. [49] IE EE Standards Association, 754-2008 IEE E standar d for Floating-P oint Arithmetic , 2008. [50] B. T horne, “Python Paillier , ” 2017, [Online] https://githu b.com/n1analyt ics/python- paillier/ , last accessed: 2018-01-11. [51] Nati onal Institute of Standards and T echnology (NIS T ), “The 2013-201 4 speaker recognition i- vector machine learning challenge, ” T ech. Rep., National Institute of Standards and T echno logy , 2014. [52] D. Bans ´ e, G. R. Doddington, D. Garcia-Romero, J. J. Godfrey , C. S. Greenberg , et al., “Summary and ini- tial results of the 2013-20 14 speaker recognition i-vector machine learning challenge, ” in P r oc. Annual Conf. of the Intl. Speech Communication Association (IN TER- SPEECH) , 2014, pp. 368–3 72. [53] E . Barker , L . Chen, A. R oginsk y , and M. S mi d, “Recom- mendation for pair-wise key establishment schemes using discrete logarithm cryptography , ” T ech. Rep. SP 800-56A Rev . 2, NIST , May 2013. [54] A. Larcher , K.A. Lee, and S. Meignier , “ An ex- tensible speake r identification S IDEKIT in Python, ” in P r oc. IEEE Intl. Conf. on Acoustics, Speech and Signal Processin g (ICASSP) , 2016, pp. 5095 –5099, http://lium.u niv- lemans.fr/side kit , last accessed: 2017-05 -15. [55] N. Br ¨ ummer and E. de V illiers, “The BOSARIS toolkit user guide: Theory , algorithms and code for binary clas- sifier score processing, ” T ech. Rep., A GNITIO Research, South Africa, December 2011.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment