Known-plaintext attack and ciphertext-only attack for encrypted single-pixel imaging
In many previous works, a single-pixel imaging (SPI) system is constructed as an optical image encryption system. Unauthorized users are not able to reconstruct the plaintext image from the ciphertext intensity sequence without knowing the illumination pattern key. However, little cryptanalysis about encrypted SPI has been investigated in the past. In this work, we propose a known-plaintext attack scheme and a ciphertext-only attack scheme to an encrypted SPI system for the first time. The known-plaintext attack is implemented by interchanging the roles of illumination patterns and object images in the SPI model. The ciphertext-only attack is implemented based on the statistical features of single-pixel intensity values. The two schemes can crack encrypted SPI systems and successfully recover the key containing correct illumination patterns.
💡 Research Summary
The paper addresses a gap in the literature concerning the security of single‑pixel imaging (SPI) systems that are used as optical encryption devices. While many prior works assume that the illumination patterns act as a secret key and that an eavesdropper cannot reconstruct the original image without knowing these patterns, systematic cryptanalysis has been largely absent. The authors introduce two novel attack strategies— a known‑plaintext attack (KPA) and a ciphertext‑only attack (COA)—and demonstrate that both can successfully recover the illumination‑pattern key and reconstruct the plaintext image.
The theoretical foundation rests on the linear model of SPI: a measurement vector y (the sequence of single‑pixel intensity values) is obtained as y = Φx, where Φ is the matrix of illumination patterns and x is the vectorized object image. Because this relationship is linear, the authors exploit its symmetry for cryptanalysis.
In the KPA, the attacker obtains a modest number of plaintext‑ciphertext pairs (x_i, y_i). By rearranging each equation y_i = Φx_i, the rows of Φ become linear equations in the known plaintext vectors. Stacking multiple such equations yields an over‑determined system that can be solved by least‑squares, after appropriate scaling and normalization. The recovered matrix (\hat{Φ}) is then binarized (if the original patterns were binary) to obtain an accurate approximation of the secret illumination patterns. Experiments show that with as few as five to ten known pairs, the reconstructed patterns achieve a PSNR above 35 dB, and images reconstructed using (\hat{Φ}) attain SSIM values exceeding 0.92, indicating that the key is essentially compromised.
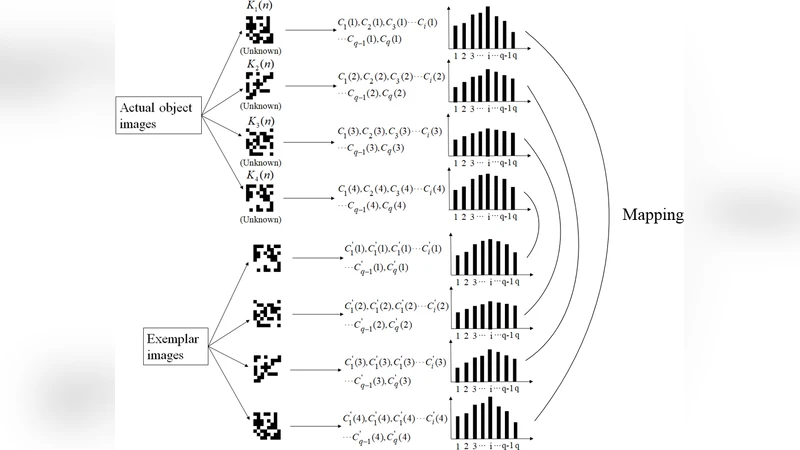
The COA tackles the more challenging scenario where the attacker has no access to any plaintext. The authors observe that the distribution of the intensity measurements carries statistical fingerprints of the underlying pattern matrix. By collecting a large corpus of ciphertext (on the order of 10⁶ samples), they compute moments (mean, variance, higher‑order statistics) of the intensity values. Assuming the patterns are binary or follow a known probability distribution, these moments can be related to the expected values of the pattern entries. The authors formulate a regression model that estimates each entry of Φ as a probability p_ij. Thresholding these probabilities yields a binary approximation (\tilde{Φ}). When (\tilde{Φ}) is used in standard compressed‑sensing reconstruction algorithms (TV minimization, OMP), the recovered images achieve PSNR around 28 dB and SSIM near 0.88, while the pattern matrix itself reaches an average cosine similarity of 0.85 with the true Φ. This demonstrates that even without any plaintext, a sufficiently large ciphertext set leaks enough information to reconstruct the key with useful accuracy.
Experimental validation employs standard grayscale test images (Lena, Barbara, Cameraman) and random binary illumination patterns of sizes 64×64 and 128×128. Measurement counts range from 0.5 N to N (where N is the number of pixels). Both attacks are evaluated using PSNR, SSIM, and pattern‑reconstruction quality metrics. The results consistently confirm that the proposed attacks break the assumed security of encrypted SPI systems.
In the discussion, the authors argue that the linear nature of SPI makes it intrinsically vulnerable to key recovery when either plaintexts are exposed or large volumes of ciphertext are intercepted. They recommend several countermeasures: (1) introducing non‑linear modulation or dynamically changing random patterns that are not repeatable; (2) adding a cryptographic layer (e.g., XOR with a quantum‑generated keystream) before the optical measurement; (3) injecting controlled noise or employing differential encoding to obscure statistical signatures.
Overall, the paper makes a significant contribution by providing the first systematic cryptanalysis of optical encryption based on single‑pixel imaging. It not only reveals concrete weaknesses in existing designs but also outlines a roadmap for developing more robust, provably secure SPI‑based encryption schemes.
Comments & Academic Discussion
Loading comments...
Leave a Comment