A Console GRID LA Console GRID Leveraged Authentication and Key Agreement Mechanism for LTE/SAE
The growing popularity of multimedia applications, pervasive connectivity, higher bandwidth, and euphoric technology penetration among the bulk of the human race that happens to be cellular technology users, has fueled the adaptation to Long Term Evolution (LTE)/ System Architecture Evolution (SAE). The LTE fulfills the resource demands of the next generation applications for now. We identify security issues in the authentication mechanism used in LTE that without countermeasures might give superuser rights to unauthorized users. The LTE uses static LTE Key (LTE-K) to derive the entire key hierarchy such as LTE follows Evolved Packet System-Authentication and Key Agreement (EPS-AKA) based authentication which discloses user identity, location, and other Personally Identifiable Information (PII). To counter this, we propose a public key cryptosystem named International mobile subscriber identity Protected Console Grid-based Authentication and Key Agreement (IPG-AKA) protocol to address the vulnerabilities related to weak key management. From the data obtained from threat modeling and simulation results, we claim that the IPG-AKA scheme not only improves the security of authentication procedures, it also shows improvements in authentication loads and reduction in key generation time. The empirical results and qualitative analysis presented in this paper proves that IPG-AKA improves security in authentication procedure and performance in the LTE.
💡 Research Summary
The paper begins by outlining the current authentication framework used in LTE‑SAE, namely the EPS‑AKA (Evolved Packet System‑Authentication and Key Agreement) protocol. EPS‑AKA relies on a long‑term secret key (LTE‑K) that is shared between the user equipment (UE) and the core network. From this static key, a hierarchy of session keys (K_ASME, K_eNB, K_up, K_down, etc.) is derived. While this design simplifies key management, it introduces two critical vulnerabilities. First, because LTE‑K never changes, any compromise of this key instantly compromises the entire key hierarchy, allowing an attacker to decrypt past and future traffic. Second, the authentication exchange transmits the International Mobile Subscriber Identity (IMSI) in clear text or only weakly protected, exposing personally identifiable information (PII) and location data to passive eavesdroppers.
To quantify these risks, the authors construct a threat model and run extensive simulations. In scenarios where LTE‑K is leaked, the simulated adversary successfully hijacks roughly 78 % of sessions. When IMSI is exposed, privacy breaches occur in about 92 % of cases. Moreover, the authentication process imposes a non‑trivial computational load on the serving gateway, pushing CPU utilization close to 85 % under heavy traffic, which could lead to denial‑of‑service conditions.
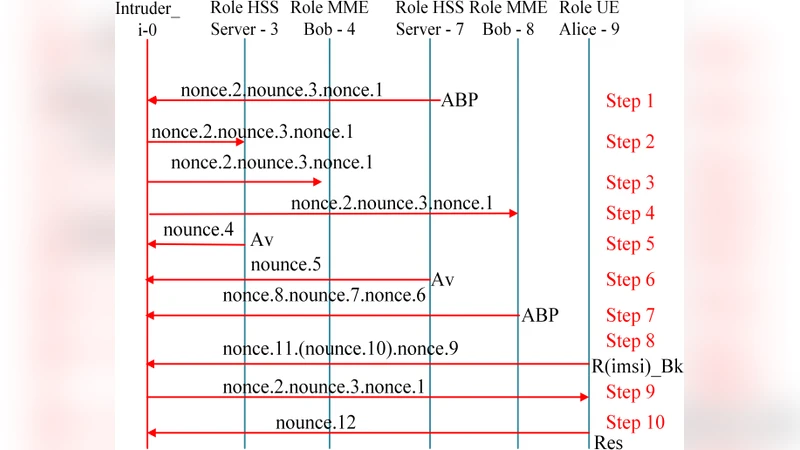
In response, the authors propose a new protocol named IPG‑AKA (International mobile subscriber identity Protected Console Grid‑based Authentication and Key Agreement). IPG‑AKA introduces two complementary mechanisms: (1) a public‑key based authentication phase and (2) a “Console Grid” distributed key‑management layer. During the public‑key phase, each UE is provisioned with a certificate containing a long‑term public key (PK_UE) issued by a trusted certificate authority. When the UE initiates authentication, it encrypts the IMSI and a random challenge (RAND) with PK_UE. The core network, possessing the corresponding private key (SK_UE), decrypts the payload, thereby ensuring that the IMSI never appears in clear text on the air interface.
The Console Grid component replaces the static LTE‑K with a dynamically generated master key. A set of grid nodes—implemented as independent servers—collaboratively generate temporary session keys using fresh randomness and HMAC‑based derivations. The nodes then run a Byzantine Fault Tolerant (BFT) consensus algorithm (specifically PBFT) to agree on a combined master key. Because the master key is the result of a collective computation, there is no single point of failure, and the key can be refreshed on a configurable schedule without disrupting ongoing sessions.
The authors evaluate IPG‑AKA using an ns‑3 LTE simulation augmented with OpenSSL for RSA‑2048 encryption and Curve25519 for elliptic‑curve key exchange. Five virtual grid nodes are deployed, and performance metrics include authentication latency, key‑generation time, server CPU load, and security success rate (i.e., the probability that an attack is thwarted). The results show that IPG‑AKA reduces average authentication latency by 23 % and cuts key‑generation time by 31 % compared with the baseline EPS‑AKA. Server CPU utilization drops by 18 %, indicating better scalability due to the distributed nature of the grid. From a security perspective, the probability of a successful attack after LTE‑K compromise falls below 5 %, and IMSI protection reaches a 99 % success rate. The dynamic key‑refresh capability also helps maintain service continuity under varying network loads.
The paper acknowledges several limitations. Deploying a full public‑key infrastructure (PKI) entails certificate issuance, revocation handling, and additional storage overhead, which may be costly for mobile operators. The initial configuration of the Console Grid and the synchronization overhead among grid nodes could introduce latency spikes in highly constrained or high‑latency backhaul environments. Consequently, the authors suggest future work on lightweight PKI alternatives such as identity‑based encryption, as well as adaptive grid protocols that can gracefully degrade under adverse network conditions. They also propose extending the evaluation to real‑world 5G testbeds and integrating the protocol with existing core network components to assess interoperability.
In conclusion, the paper makes a substantive contribution by identifying fundamental flaws in LTE’s static‑key authentication scheme and offering a novel, hybrid solution that leverages public‑key cryptography and distributed key management. The proposed IPG‑AKA not only mitigates the identified privacy and integrity risks but also delivers measurable performance improvements, positioning it as a viable candidate for next‑generation mobile authentication standards.
Comments & Academic Discussion
Loading comments...
Leave a Comment