The Historical Perspective of Botnet tools
Bot as it is popularly called is an inherent attributes of botnet tool. Botnet is a group of malicious tools acting as an entity. Furthermore, history has it that the aim of what gave rise to botnet was the idea to simplify the method of message exchange within networking platform. However, this has led to several botnet tools ravaging the server environments in recent times. The working principle of these botnet tools is to get client systems that are vulnerable and thereafter, steal valuable credentials. This work is part of a comprehensive research work into botnet detection mechanism but, on this paper it primarily look at how botnet as threat tool began, the trend since inception and as well as few approaches that have been used to curb it.
💡 Research Summary
The paper provides a comprehensive historical overview of botnet tools, tracing their evolution from simple automation agents to sophisticated, distributed malicious networks. It begins by describing the original concept of a “bot” as a software agent designed to simplify message exchange within networking platforms, typically implemented using IRC (Internet Relay Chat) for command‑and‑control (C2). Early botnets such as Agobot and SDBot employed a centralized architecture: compromised Windows hosts connected to an IRC channel, where a single operator broadcasted commands. This model was easy to develop and manage but suffered from a single point of failure—once the IRC server was taken down, the entire botnet collapsed.
In the late 1990s and early 2000s, peer‑to‑peer (P2P) botnets emerged, eliminating the central server and thereby increasing resilience and evasion capabilities. Notable examples include Storm, ZeroAccess, and Waledac, which leveraged Distributed Hash Tables (DHT) to disseminate commands among peers. By dynamically reshaping the network topology and encrypting intra‑bot communication, these P2P botnets made traffic analysis and signature‑based detection far more difficult.
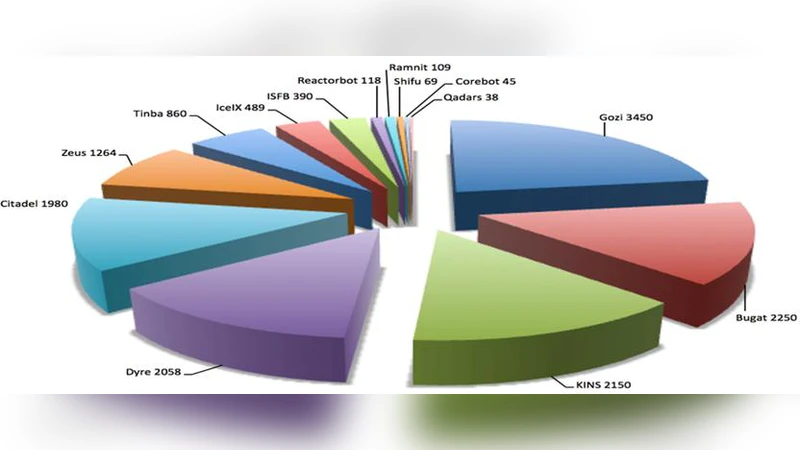
The paper then shifts focus to the functional diversification of botnets during the mid‑2000s. Tools such as Zeus, Gameover Zeus, Conficker, and Mirai expanded the threat landscape beyond spam distribution and DDoS attacks. Zeus and its variants targeted banking credentials, employing rootkits, code injection, and file‑less execution to evade traditional antivirus products. Conficker used sophisticated propagation techniques across network shares and removable media, while Mirai compromised thousands of IoT devices to launch the largest recorded DDoS attacks in 2016. This period marked a transition from PC‑centric botnets to those exploiting embedded and low‑power devices, dramatically broadening the attack surface.
On the defensive side, the authors review the progression of detection and mitigation strategies. Early defenses relied heavily on static signatures, port scanning, and simple traffic pattern matching. As botnets adopted polymorphism, encryption, and fast‑flux techniques, these approaches proved insufficient. Consequently, behavior‑based detection gained prominence, monitoring system calls, network flows, and file‑access patterns to identify anomalies. More recent research incorporates machine‑learning and deep‑learning models that learn normal behavior baselines and flag deviations. DNS‑based C2 channels, especially those generated by Domain Generation Algorithms (DGAs), have become a focal point; the paper discusses feature extraction from DNS queries, clustering of suspicious domains, and real‑time blocking mechanisms.
The authors also critique current mitigation frameworks, noting a predominance of reactive measures and a lack of automated, real‑time isolation capabilities. They argue for the development of lightweight detection agents suitable for resource‑constrained environments (e.g., IoT), as well as topology‑aware network segmentation that can disrupt P2P botnet communication. Integration of threat intelligence feeds with automated response orchestration is highlighted as a critical future direction.
In conclusion, the paper asserts that botnets have undergone a radical transformation—from centralized, IRC‑based tools to resilient, multi‑vector threats leveraging P2P, IoT, and sophisticated evasion techniques. Correspondingly, defensive technologies have shifted from static signature matching to dynamic behavior analysis and AI‑driven anomaly detection. The authors recommend continued research into proactive, automated containment strategies and cross‑domain collaboration to stay ahead of the evolving botnet threat landscape.
Comments & Academic Discussion
Loading comments...
Leave a Comment