Authentication schemes for Smart Mobile Devices: Threat Models, Countermeasures, and Open Research Issues
This paper presents a comprehensive investigation of authentication schemes for smart mobile devices. We start by providing an overview of existing survey articles published in the recent years that deal with security for mobile devices. Then, we describe and give a classification of threat models in smart mobile devices in five categories, including, identity-based attacks, eavesdropping-based attacks, combined eavesdropping and identity-based attacks, manipulation-based attacks, and service-based attacks. We also provide a classification of countermeasures into four types of categories, including, cryptographic functions, personal identification, classification algorithms, and channel characteristics. According to these, we categorize authentication schemes for smart mobile devices in four categories, namely, 1) biometric-based authentication schemes, 2) channel-based authentication schemes, 3) factor-based authentication schemes, and 4) ID-based authentication schemes. In addition, we provide a taxonomy and comparison of authentication schemes for smart mobile devices in the form of tables. Finally, we identify open challenges and future research directions.
💡 Research Summary
**
The paper offers a comprehensive survey of authentication schemes for smart mobile devices, focusing on three interrelated aspects: threat models, countermeasures, and the classification of existing authentication protocols. After reviewing ten recent survey articles on mobile security, the authors observe that few of them address authentication in depth, especially with respect to the full spectrum of attacks that modern smartphones face.
Threat‑model taxonomy – The authors identify 26 distinct attacks and group them into five high‑level categories: (1) identity‑based attacks (e.g., deposit‑key, impostor, impersonation, spoofing, replay), (2) eavesdropping‑based attacks (e.g., adaptive chosen‑message, traffic analysis, side‑channel), (3) combined eavesdropping‑and‑identity attacks (offline dictionary, MITM, parallel‑session, stolen‑verifier), (4) manipulation‑based attacks (trojan horse, biometric‑template tampering, DDoS), and (5) service‑based attacks (authentication‑server overload, denial‑of‑service). For each category, representative references are listed, and the underlying attack vectors are described in detail. This taxonomy provides a unified view that bridges the fragmented treatment of threats in earlier works.
Countermeasure classification – Countermeasures are organized into four families: (a) cryptographic functions (symmetric, public‑key, hash, elliptic‑curve), (b) personal identification (biometrics, PIN, passwords, patterns), (c) classification algorithms (machine‑learning based anomaly detection, clustering, decision trees), and (d) channel characteristics (exploitation of wireless channel randomness, RSSI, channel state information). The paper explicitly maps each countermeasure family to the threat categories it mitigates, illustrating, for example, that cryptographic signatures defend against identity‑based forgery, while channel‑based techniques are effective against eavesdropping and certain manipulation attacks.
Authentication‑scheme taxonomy – Building on the countermeasure view, the authors categorize existing mobile authentication protocols into four groups: (1) biometric‑based schemes (static traits such as fingerprint, iris; dynamic traits such as voice, gait, keystroke dynamics), (2) channel‑based schemes (physical‑layer key generation, proximity verification using radio‑channel fingerprints), (3) factor‑based (multi‑factor) schemes (combining “something you have”, “something you know”, and “something you are”), and (4) ID‑based schemes (traditional certificates, tokens, passwords). For each group, the paper lists representative protocols, the cryptographic primitives they employ, and the specific threats they claim to resist.
Comparative analysis – Table II (referenced in the text) provides a side‑by‑side comparison of recent protocols, reporting: (i) supported threat models, (ii) cryptographic primitives, (iii) computational complexity (e.g., number of exponentiations, elliptic‑curve operations), (iv) communication overhead (message count, size), (v) experimental platform (smartphone model, OS version), and (vi) identified limitations (e.g., high energy consumption, user‑perceived latency, lack of protection against service‑level attacks). The analysis reveals that while most schemes adequately address identity‑, eavesdropping‑, and manipulation‑based attacks, few provide systematic defenses against service‑based threats or combined multi‑vector attacks. Moreover, trade‑offs between security, usability, and battery consumption are often under‑explored, limiting practical deployment.
Open research challenges – The authors outline five major directions:
- Continuous, low‑power biometric authentication – Developing algorithms and hardware that can monitor physiological/behavioral traits in real time without draining the battery.
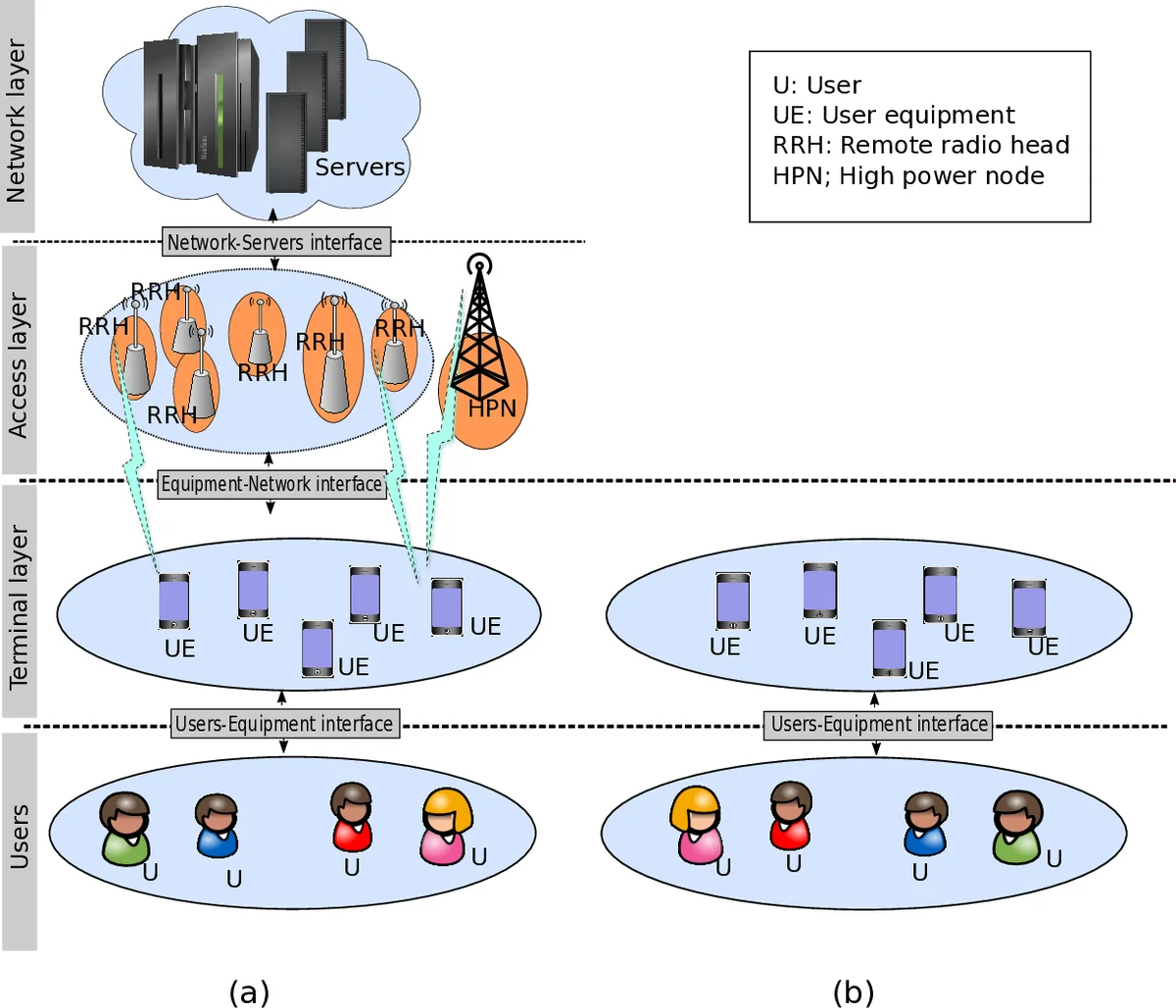
- Standardization of channel‑based authentication for 5G/edge environments – Defining interoperable protocols that exploit radio‑channel randomness while meeting latency requirements of ultra‑reliable low‑latency communications.
- Integration of AI‑driven anomaly detection into authentication flows – Leveraging deep learning to detect subtle deviations in user behavior or device telemetry and trigger adaptive authentication steps.
- Privacy‑preserving authentication using zero‑knowledge proofs – Designing schemes that prove possession of biometric or secret attributes without revealing the underlying data, thus reconciling privacy with security.
- Comprehensive benchmarking frameworks – Building simulation platforms that model combined attack scenarios (e.g., MITM + side‑channel + DDoS) and provide standardized metrics for computational, communication, and energy costs.
Conclusion – By unifying threat models, countermeasure families, and authentication scheme categories, the paper fills a gap in the literature and offers a clear roadmap for future work. The authors argue that next‑generation mobile authentication must combine multi‑factor biometrics, physical‑layer channel verification, and AI‑enhanced anomaly detection while preserving user privacy and maintaining low latency. Their taxonomy and identified research gaps provide a valuable reference for scholars, protocol designers, and industry practitioners aiming to secure the rapidly expanding ecosystem of smart mobile devices.
Comments & Academic Discussion
Loading comments...
Leave a Comment