Prospective Hybrid Consensus for Project PAI
PAI Coin’s Proof-of-Work (PoW) consensus mechanism utilizes the double SHA-256 hashing protocol– the same mechanism used by Bitcoin Core. This compatibility with classic Bitcoin-style mining provides low barrier to entry for PAI Coin mining, consequently rendering the PAI Coin network vulnerable to so-called 51% attacks, among others. To mitigate such risks, this paper proposes a hybrid Proof-of-Work, Proof-of-Stake (PoS) consensus mechanism and provides a detailed technical analysis of how such a mechanism would counter some of the PAI Coin network’s inherent vulnerabilities, if successfully implemented. A detailed technical outline of blockchain-based PoW & PoS consensus, including their advantages and disadvantages, when used both independently and in the context of the hybrid model, is provided. An economic analysis of attacking a hybrid-powered PAI Coin network is presented, and a final recommendation for future development of PAI Coin consensus is made.
💡 Research Summary
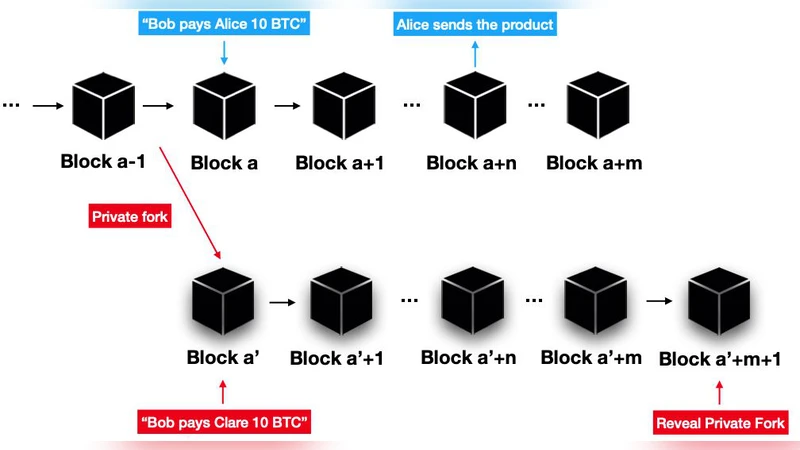
The paper begins by diagnosing the inherent vulnerability of the current PAI Coin consensus mechanism, which mirrors Bitcoin’s double‑SHA‑256 proof‑of‑work (PoW). While this design lowers the barrier to entry for miners—allowing anyone with commodity GPUs or ASICs to participate—it also makes the network susceptible to classic PoW attacks such as 51 % hash‑rate domination, chain re‑organizations, and double‑spending. Because PAI’s total hash power is relatively modest and its difficulty adjustment is permissive, an adversary could, in theory, acquire a controlling share of the network at a comparatively low cost.
To address these risks, the authors propose a hybrid PoW/Proof‑of‑Stake (PoS) consensus model. In the hybrid, block production is split into two sequential phases. Phase 1 follows the traditional PoW process: miners compete to find a nonce that satisfies the network’s difficulty target and broadcast a candidate block header. Phase 2 introduces a PoS checkpoint: a validator who has staked a predefined amount of PAI tokens is randomly (or via a coin‑age algorithm) selected to either approve or reject the candidate block. Only when both phases succeed does the block become final. This two‑layer approach forces an attacker to control both the majority of the network’s hash power and a majority of the token supply, dramatically raising the economic barrier to a successful attack.
The security analysis quantifies this barrier. Assuming current market prices and hardware costs, acquiring 51 % of the global hash power would require tens of billions of dollars in mining equipment and electricity. Simultaneously obtaining 51 % of the PAI token supply would demand a comparable capital outlay, especially given the liquidity constraints of the token. The combined cost is therefore orders of magnitude higher than attacking a pure PoW chain, rendering a 51 % attack practically infeasible. Moreover, the PoS component introduces a “skin‑in‑the‑game” incentive: validators earn staking rewards and a share of transaction fees, aligning their financial interests with network health and discouraging malicious behavior.
Economic modeling in the paper also explores the reward structure. The authors recommend an initial reward split of roughly 60 % PoW and 40 % PoS (or 70 %/30 % depending on network conditions) to avoid alienating existing miners while still attracting new stakers. This split can be dynamically adjusted based on observed hash‑rate and staking participation metrics. The hybrid model thus diversifies incentives, stabilizes token value, and mitigates the centralizing pressure that pure PoW can exert.
Implementation challenges are identified in four main areas: (1) synchronizing block times between PoW and PoS phases to minimize fork risk; (2) designing a validator selection algorithm that balances randomness, fairness, and resistance to stake‑grinding attacks; (3) defining clear fork‑resolution rules when the two layers disagree; and (4) continuously monitoring and tuning parameters such as minimum stake, selection probability, and reward ratios. The authors caution that an overly PoS‑biased reward schedule could cause miners to abandon the network, reducing overall hash power and inadvertently weakening security.
Simulation results presented in the paper demonstrate that, under realistic network conditions, the probability of a successful attack drops from roughly 30 % in a pure PoW scenario to under 0.1 % in the hybrid configuration when at least 30 % of tokens are staked. Additionally, the hybrid system maintains the same difficulty‑adjustment cadence as the original PoW chain, while the PoS checkpoint reduces block‑time variance and improves finality latency.
In conclusion, the paper argues that a PoW/PoS hybrid offers a balanced pathway for PAI Coin to enhance security without sacrificing decentralization or miner participation. The recommended development roadmap includes (1) detailed protocol specification and test‑net deployment, (2) community‑driven parameter tuning and governance processes, and (3) a phased migration plan to the mainnet. The authors’ final recommendation is for the PAI development team to adopt the hybrid consensus, implement robust monitoring mechanisms, and iterate on the design as the ecosystem evolves, thereby ensuring long‑term resilience and growth.
Comments & Academic Discussion
Loading comments...
Leave a Comment