BYOD, Personal Area Networks (PANs) and IOT: Threats to Patients Privacy
The passage of FISMA and HIPPA Acts have mandated various security controls that ensure the privacy of patients data. Hospitals and health-care organizations are required by law to ensure that patients data is stored and disseminated in a secure fashion. The advent of Bring Your Own Devices (BYOD), mobile devices, instant messaging (such as WhatsApp) and cloud technology however, have brought forth new challenges. The advent of Internet of Things (IOT) have complicated the matters further as organizations are not fully cognizant to the all facets of threats to data privacy. Physicians and health care practitioners need to be made aware of various new avenues of data storage and transmission that need to be secured and controlled. In this paper we look at various threats and challenges that IOT, Bring Your Own Device (BYOD) and Personal Area Networks (PANs) technologies pose to the patients privacy data. We conclude the paper by providing the results of a survey that gauge the depth of understanding of healthcare professionals regarding the emerging threats to patients privacy
💡 Research Summary
**
The paper “BYOD, Personal Area Networks (PANs) and IoT: Threats to Patients Privacy” examines how modern mobile and Internet‑of‑Things technologies undermine the privacy protections originally established by U.S. legislation such as HIPAA and FISMA. The authors begin by noting that while HIPAA (1996) and FISMA (2002) introduced a set of mandatory administrative, physical, and technical safeguards for electronic protected health information (ePHI), the rapid adoption of Bring‑Your‑Own‑Device (BYOD) policies, instant‑messaging platforms (e.g., WhatsApp), cloud storage, and pervasive sensor networks has created new attack surfaces that are not fully addressed by existing regulations.
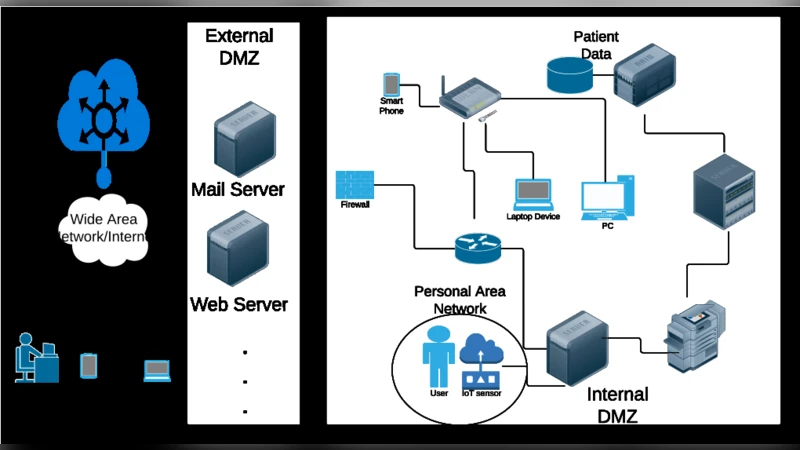
The paper structures its technical discussion around a three‑layer network model typical of a smart‑healthcare architecture: Local Area Network (LAN), Wide Area Network (WAN), and Personal Area Network (PAN). LANs are internal corporate networks protected by VPNs and conventional firewalls; WANs are essentially the public Internet, relying on ISP‑level security and external perimeter defenses. The authors focus on PANs because they are the smallest, most intimate networks—typically spanning 10‑20 meters and built on Bluetooth, IEEE 802.15.4 (low‑rate WPAN), IEEE 802.15.3 (high‑rate WPAN), and IEEE 802.15.6 (Body Area Networks). PANs connect medical sensors (e.g., heart‑rate monitors) and actuators (e.g., insulin pumps) directly to a clinician’s mobile device or to a bedside hub. This proximity and wireless nature make PANs especially vulnerable to three categories of risk identified in NIST SP 800‑46: (1) lack of physical security (devices can be stolen or lost), (2) insecure wireless channels that enable man‑in‑the‑middle (MITM) attacks, and (3) infection of the mobile device with malware that can then compromise the PAN and any downstream cloud services.
The regulatory landscape is reviewed next. HIPAA establishes privacy and security rules for covered entities, while FISMA extends federal information‑security requirements to government‑run health programs. The Cyber‑Enhancement Act of 2014 augments FISMA by emphasizing physical security and cyber‑physical systems, which are directly relevant to PANs and IoT medical devices. The FDA’s non‑binding guidance and MITRE’s medical‑device‑cybersecurity initiatives are mentioned as complementary efforts. The authors then summarize the relevant NIST publications (FIPS‑140, FIPS‑199, FIPS‑200, SP 800‑12, SP 800‑18, SP 800‑30, SP 800‑32, SP 800‑37, SP 800‑39, SP 800‑46, SP 800‑53, SP 800‑66, SP 800‑121, SP 800‑183, SP 800‑187) that collectively provide cryptographic standards, risk‑management frameworks, and specific guidance for BYOD, Bluetooth security, and “Internet of Things” networks.
To gauge real‑world awareness, the authors conducted an informal, anonymous SurveyMonkey poll of 50 healthcare professionals across multiple institutions. Key findings: only 6 % were aware of cloud‑related privacy risks; 69 % reported using WhatsApp to discuss patient information; and 82 % regularly used Bluetooth devices (e.g., wearables, bedside monitors). The authors interpret these results as evidence of a substantial gap between regulatory expectations and day‑to‑day practice, especially concerning unsecured messaging and the assumed safety of Bluetooth connections.
In the discussion, the paper proposes a set of technical and administrative countermeasures. For PANs, the authors recommend mandatory use of the latest Bluetooth Low Energy Secure Connections, device‑level authentication, and robust key‑management procedures. For BYOD, they advocate the deployment of Mobile Device Management (MDM) platforms that enforce remote wipe, full‑disk encryption, and application whitelisting, coupled with strict policy enforcement on acceptable use. Cloud services should be vetted for HIPAA‑compliance, with end‑to‑end encryption and data‑segregation enforced. Messaging should be limited to approved, encrypted healthcare communication tools rather than consumer apps. Finally, they call for continuous risk assessments using the NIST Risk Management Framework (RMF) and periodic updates to policies as new standards (e.g., upcoming NIST SP 800‑210 on IoT security) emerge.
The conclusion reiterates that while legacy regulations provide a solid foundation, the proliferation of BYOD, PAN, and IoT technologies introduces novel vulnerabilities that require updated technical controls, rigorous policy enforcement, and ongoing education of clinicians. The authors suggest future work involving larger, statistically powered surveys, penetration testing of real‑world PAN deployments, and the integration of AI‑driven anomaly detection to proactively identify malicious activity in smart‑health environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment