On Double-Sided QR-Codes
Due to the widespread adoption of the smart mobile devices, QR codes have become one of the most-known types of 2D codes around the world. However, the data capacity properties of modern QR codes are still not perfect. To address this issue, in this paper, we propose a novel approach to make double-sided QR codes, which could carry two different messages in a straight and mirrored position. To facilitate the process of creation of such codes we propose two methods of their construction: the brute-force method and the analytic solution.
💡 Research Summary
The paper addresses the well‑known limitation of QR‑code data capacity by proposing a “double‑sided” QR‑code that can convey two distinct messages depending on whether it is viewed in its normal orientation or as a mirror image reflected across the main diagonal. Focusing on the simplest QR‑code variant (Version 1‑L, a 21 × 21 matrix with the lowest error‑correction level), the authors dissect the code’s anatomy: fixed function patterns, the control‑code area, the payload data area, and the Reed‑Solomon error‑correction zone.
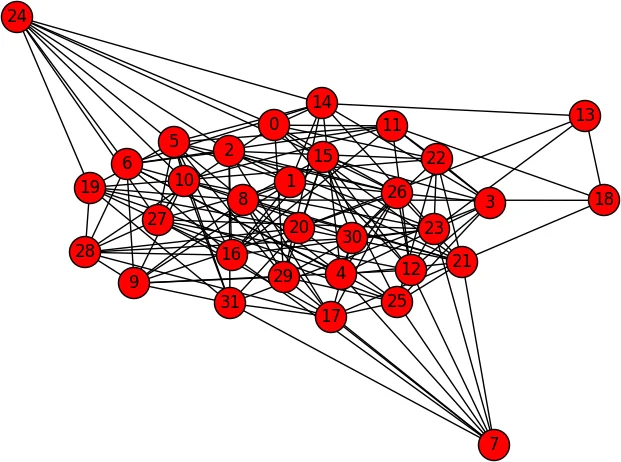
Key to the double‑sided concept is ensuring that the control code remains valid after diagonal mirroring. The control code consists of five informational bits (two for error‑correction level, three for the XOR mask) protected by a BCH(15,5) code. Because the control code appears twice in the matrix, a mirrored version reverses the order of the five bits. The authors therefore seek a palindromic 5‑bit pattern with a ‘1’ in the central position (to satisfy the “dark module” requirement). Using the BCH code’s ability to correct up to three bit errors, they search for a 15‑bit string that is within three bits of a valid control code and whose reversed version is also within three bits of another valid control code. A brute‑force enumeration of the 2⁵ = 32 possible control codes yields roughly 14 560 candidates; these are represented as a graph where nodes are valid codes and edges indicate a common 15‑bit string satisfying the dual‑radius condition. One suitable pair (e.g., 100101010100001 ↔ 100001010101001) fulfills the palindrome, central‑bit, and symmetric‑mask requirements.
The payload design is more delicate because the data areas of the two messages overlap by about 100 bits. The authors demonstrate that for very short messages (e.g., five alphanumeric characters, 41 bits each) the overlap shrinks to only four bits, which can be accommodated by careful selection of the encoding mode, length field, and data bits. However, the error‑correction zones (56 bits total) heavily intersect both payloads, creating four conflict zones (labelled a, c, e, i). Since each side can correct up to three padded bytes (24 bits) with Level‑L Reed‑Solomon codes, the authors propose to “hide” the conflicts inside the error‑correction data. By treating the overlapping bits as intentional errors, they rely on the code’s ability to recover the original payloads provided the total number of erroneous bytes per side does not exceed the correction capacity.
Two construction strategies are explored. The first, a brute‑force search, varies the free data bits (denoted g) until the resulting error‑correction bits (f on one side, h on the other) become sufficiently similar after mirroring. Empirical testing shows that with this method messages of up to eight characters on one side and eleven on the other can be encoded, but the combinatorial explosion makes the approach impractical for longer payloads.
The second, an analytic solution, models the Reed‑Solomon encoding as a system of linear Boolean equations. The payload bits, the generated error‑correction bits, and the mirroring constraints together form a large but sparse linear system with a modest number of free variables (the bits that can be chosen arbitrarily). By applying Gaussian elimination, the system can be solved in milliseconds, yielding a complete assignment of all bits that satisfies both orientations simultaneously. This method scales far better and opens the possibility of handling longer messages, limited only by the intrinsic capacity of the underlying QR‑code version.
The authors acknowledge several limitations. The current prototype works only with very short messages because the overlap between data and error‑correction zones becomes prohibitive as payload length grows. Extending the approach to higher error‑correction levels (M, Q, H) or larger QR‑code versions would increase the number of free variables but also introduce new compatibility challenges with existing scanning software. Moreover, the reliance on symmetric XOR masks restricts the set of usable masks to five out of eight.
In conclusion, the paper presents a novel exploitation of QR‑code structural symmetries to embed two independent messages in a single matrix, offering a software‑only solution that does not require changes to existing scanners. By combining careful control‑code selection, payload alignment, and the powerful error‑correction capabilities of Reed‑Solomon codes, the authors demonstrate both a brute‑force and an analytic pathway to generate double‑sided QR‑codes. While practical deployment is currently constrained by message length, the analytic framework provides a promising foundation for future research into higher‑capacity, robust, and backward‑compatible dual‑message QR‑codes.
Comments & Academic Discussion
Loading comments...
Leave a Comment