Improved Target Acquisition Rates with Feedback Codes
This paper considers the problem of acquiring an unknown target location (among a finite number of locations) via a sequence of measurements, where each measurement consists of simultaneously probing a group of locations. The resulting observation co…
Authors: Anusha Lalitha, Nancy Ronquillo, Tara Javidi
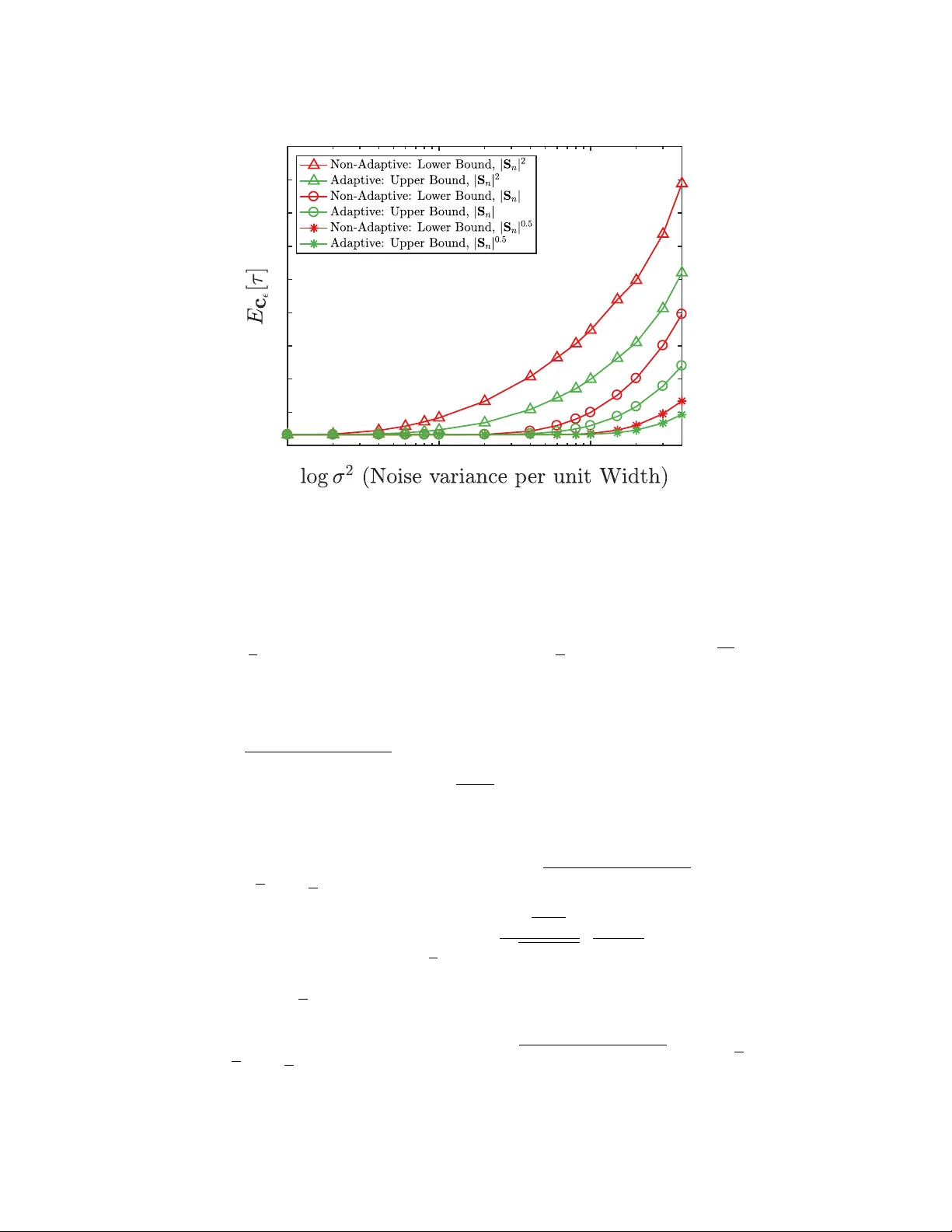
Impro v ed T ar get Acquisition Rates with Feedback Codes Anusha Lalitha, Nancy Ronquillo, and T ara Ja vidi, Senior Member , IEEE Abstract This paper considers the problem of acquiring an unkno wn target location (among a finite number of locations) via a sequence of measurements, where each measurement consists of simultaneously probing a group of locations. The resulting observation consists of a sum of an indicator of the target’ s presence in the probed region, and a zero mean Gaussian noise term whose variance is a function of the measurement vector . An equiv alence between the target acquisition problem and channel coding over a binary input additiv e white Gaussian noise (B A WGN) channel with state and feedback is established. Utilizing this information theoretic perspecti ve, a tw o-stage adaptiv e target search strategy based on the sorted Posterior Matching channel coding strate gy is proposed. Furthermore, using information theoretic con verses, the fundamental limits on the tar get acquisition rate for adapti ve and non-adaptiv e strategies are characterized. As a corollary to the non-asymptotic upper bound of the expected number of measurements under the proposed two-stage strategy , and to non-asymptotic lo wer bound of the expected number of measurements for optimal non-adaptive search strategy , a lower bound on the adaptivity gain is obtained. The adapti vity gain is further inv estigated in different asymptotic regimes of interest. I . I N T RO D U C T I O N Consider a single target acquisition ov er a search region of width B and resolution up to width δ . Mathematically , this is the problem of estimating a unit vector W ∈ { 0 , 1 } B δ via a sequence of noisy linear measurements Y n = h S n , W + Ξ n i , n = 1 , 2 , . . . , τ , (1) Preliminary versions of this work were presented at the 50th Asilomar Conference on Signals, Systems, and Computers, and at 2017 International Symposium on Information Theory . A. Lalitha N. Ronquillo, and T . Ja vidi are with the Department of Electrical and Computer Engineering, Univ ersity of California San Diego, La Jolla, CA 92093, USA. (e-mail: alalitha@ucsd.edu; nronquil@ucsd,edu; tjavidi@ucsd.edu). December 19, 2017 DRAFT 1 where a binary measurement vector S n ∈ { 0 , 1 } B δ denotes the locations inspected and the vector Ξ n ∈ R B δ denotes the additiv e measurement noise per location. More generally , the observation Y n at time n can be written as Y n = h S n , W i + Z n ( S n ) , (2) where Z n ( S n ) is a noise term whose statistics are a function of the measurement vector S n . The goal is to design the sequence of measurement vectors { S n } τ n =1 , such that the tar get location W is estimated with high reliability , while keeping the (expected) number of measurements τ as lo w as possible. In this paper, we first consider the linear model (1) when the elements of Ξ n are i.i.d Gaussian with zero mean and variance δ σ 2 . This means that Z n ( S n ) in (2) are distributed as N (0 , | S n | δ σ 2 ) , and sho w that the problem of searching for a target under measurement dependent Gaussian noise Z n ( S n ) is equi valent to channel coding over a binary additiv e white Gaussian noise (B A WGN) channel with state and feedback (in Section 4.6 [1]). This allo ws us not only to retrofit the known channel coding schemes based on sorted Posterior Matching (sort PM) [2] as adapti ve search strategies, but also to obtain information theoretic con verses to characterize fundamental limits on the tar get acquisition rate under both adaptiv e and non-adapti ve strategies. As a corollary to the non-asymptotic analysis of our sorted Posterior-Matching-based adapti ve strategy and our con verse for non-adaptiv e strategy , we obtain a lower bound on the adaptivity gain. A. Our Contributions Our main results are inspired by the analogy between target acquisition under measurement dependent noise and channel coding with state and feedback. This connection was utilized in [3] under a Bernoulli noise model. In this paper , in Proposition 1, we formalize the connection between our target acquisition problem with Gaussian measurement dependent noise and channel coding over a B A WGN channel with state. Here, the channel state denotes the v ariance of the measurement dependent noise | S n | δ σ 2 . Since feedback codes i.e., adapting the code word to the past channel outputs, are known to increase the capacity of a channel with state and feedback. This moti vates us to use adaptivity when searching, i.e., to utilize past observations { Y 1 , Y 2 , . . . , Y n − 1 } when selecting the ne xt measurement vector S n . Furthermore, this information theoretic perspectiv e allows us to quantify the increase in the adapti ve target acquisition rate. Our analysis of improvement in the tar get acquisition rate as well as the adapti vity g ain, measured December 19, 2017 DRAFT 2 as the reduction in e xpected number of measurements, while using an adapti ve strategy over a non-adaptive strategy has tw o components. Firstly , we utilize information theoretic con verse for an optimal non-adapti ve search strategy to obtain a non-asymptotic lower bound on the minimum expected number of measurements required while maintaining a desired reliability . As a consequence, this pro vides the best non-adaptive target acquisition rate. Secondly , we utilize a feedback code based on Posterior Matching as a two-stage adapti ve search strategy and obtain a non-asymptotic upper bound on the expected number of measurements while maintaining a desired reliability . These two components of our analysis allo w us to characterize a lower bound on the increased target acquisition rate due to adaptivity . Our non-asymptotic analysis of adapti vity gain re veals two qualitati vely dif ferent asymptotic regimes. In particular , we sho w that adapti vity gain depends on the manner in which the number of locations gro w . W e sho w that the adaptivity gro ws logarithmically in the number of locations, i.e., O log B δ when refining the search resolution δ ( δ going to zero) and while keeping total search width B fixed. On the other hand, we sho w that as the search width B expands while keeping search resolution δ fixed, the adapti vity gain grows in the number of locations as O B δ log B δ . The problem of searching for a target under a binary measurement dependent noise, whose crossov er probability increases with the weight of the measurement vector was studied by [3] and analyzed under sort PM strategy in [2]. In particular , [3] and [2] pro vide asymptotic analysis of the adapti vity gain for the case where B = 1 and δ approaches zero. Our prior work [4] by utilizing a (suboptimal) hard decoding of Gaussian observation Y n , strengthens [3] and [2] by also accounting for the re gime in which B grows. While the analysis in [4] strengthens the non- asymptotic bounds in [2] with Bernoulli noise it failed to provide tight analysis for our problem with Gaussian observ ations. In this paper , by strengthening our analysis in [4] we extend the prior work in three ways: (i) we consider the soft Gaussian observ ation Y n , (ii) we obtain non- asymptotic achiev ability and con verse analysis, and (iii) we characterize tight non-asymptotic adapti vity gain in the two asymptotically distinct regimes of B → ∞ and δ → 0 . B. Applications Our problem formulation addresses two challenging engineering problems which arise in the context of modern communication systems. W e will discuss the two problems in the following December 19, 2017 DRAFT 3 examples and then provide the details of the state of art. Example 1 (Establishing initial access in mm-W a ve communication) . Consider the problem of detecting the direction of arriv al for initial access in millimeter wav e (mmW av e) Communica- tions. In mmW av e communication, prior to data transmission the base station is tasked with aligning the transmitter and receiv er antennas in the angular space. In other words, the base station’ s antenna pattern can be vie wed as a measurement vector S n searching the angular space B ⊂ (0 , 360 ◦ ) . At each time n , the noise intensity depends on the base station’ s antenna pattern S n and the noisy observ ation Y n is a function of measurement dependent noise Z n ( S n ) . Here it is natural to characterize the fundamental limit on the measurement time as a function of asymptotically small δ . Example 2 (Spectrum Sensing for Cognitiv e Radio) . Consider the problem of opportunistically searching for a vacant subband of bandwidth δ ov er a total bandwidth of B . In this problem secondary user desires to locate the single stationary vacant subband quickly and reliably , by making measurements S n at ev ery time n . At each time instant n , the noise intensity depends on the number of subbands probed as dictated by S n and noisy observation Y n is is a function of measurement dependent noise Z n ( S n ) . Here it is natural to characterize fundamental limit of the measurement time required for a secondary user to acquire the v acant subband as a function of the asymptotically large bandwidth B . Giordani et al. [5] compare the exhausti ve search like the Sequential Beamspace Scanning considered by Barati et al. [6], where the base station sequentially searches through all angular sectors, against a two stage iterati ve hierarchical search strategy . In the first stage an e xhaustiv e search identifies a coarse sector by repeatedly probing each coarse re gion for a predetermined SNR to be achie ved. In the second stage an exhausti ve search o ver all locations identifies the target. Giordani et al. sho w that in general the adaptiv e iterati ve strategy reduces the number of measurements over exhausti ve search except when desired SNR is too high, forcing the number of measurements required at each stage to get too large. W e observe this in through our simulations in Section VI-A. In fact, as confirmed by our simulations random-coding-based non-adapti ve strategies including the Agile-Link protocol [7], outperform the repetition based adapti ve strategies. Past literature on spectrum sensing for cogniti ve radio [8]–[10] and support vector reco v- December 19, 2017 DRAFT 4 ery [11], [12] ha ve focused on the problem where S n can be real or complex, with measurement independent noise applying both exhausti ve search and multiple adapti ve search strategies. In contrast, our work considers a simple binary model, S n ∈ { 0 , 1 } B δ , b ut captures the implications of measurement dependence of the noise, which is kno wn in the spectrum sensing literature as noise folding. The problem of measurement dependent noise (kno wn as noise folding) has been in vestigated in [13] where non-adapti ve design of complex measurements matrix satisfying RIP condition has been in vestigated. Our work compliments this study by characterizing the gain associated with adaptiv ely addressing the measurement dependent noise (noise folding), albeit for the simpler case of binary measurements. W e note that the case of adpti vely finding a subset of a suf ficiently large v acant bandwidth with noise folding is considered in [14], where ideas from group testing and noisy binary search ha ve been utilized. The solutions ho wev er depend strongly on the a vailability of sufficiently lar ge consecti ve vacant band and does not apply to our setting. Notations: V ectors are denoted by boldface letters A and A ( j ) is the j th element of a vector . Matrices are denoted by overlined boldface letters. Let U M denote the set { u ∈ R M : u ( j ) ∈ { 0 , 1 }} . Bern ( p ) denotes the Bernoulli distrib ution with parameter p , h ( p ) = − p log p − (1 − p ) log (1 − p ) denotes the entropy of a Bernoulli random v ariable with parameter p . Let G ( x ; µ, σ 2 ) denote the pdf of Gaussian random variable with mean µ and variance σ 2 at x . Logarithms are to the base 2. Let [ g ] a = g if g ≥ a otherwise [ g ] a = 0 . I I . P RO B L E M S E T U P In this section, we describe the mathematical formulation of the target acquisition problem follo wed by the performance criteria. A. Pr oblem F ormulation W e consider a search agent interested in quickly and reliably finding the true location of a single stationary tar get by making measurements over time about the target’ s presence. In particular , we consider a total search re gion of width B that contains the target in a location of width δ . In other words, the search agent is searching for the target’ s location among B δ total locations. Let W ∈ U B δ denote the true location of the target, where W ( j ) = 1 if and only if target is located at location j . The tar get location W can take B δ possible values uniformly at December 19, 2017 DRAFT 5 random whose v alue remains fix ed during the search. A measurement at time n is given by a vector S n ∈ U B δ , where S n ( j ) = 1 if and only if location j is probed. Each measurement can be imagined to result in a clean observ ation X n = W | S n ∈ { 0 , 1 } indicating of the presence of the tar get in the measurement vector S n . Ho we ver , only a noisy version of the clean observation X n is av ailable to the agent. The resulting noisy observ ation Y n ∈ R is given by the follo wing linear model with additiv e measurement dependent noise Y n = X n + Z n ( S n ) . (3) Here, we assume Z n ∼ N (0 , | S n | δ σ 2 ) which corresponds to the case of i.i.d white Gaussian noise with σ 2 denotes the noise variance per unit width. Conditioned on the measurement vector S n , the noise Z n is independent ov er time. A search consisting of τ measurements can be represented by a measurement matrix S τ = [ S 1 , S 2 , . . . , S τ ] which yields the observation vector Y τ = [ Y 1 , Y 2 , . . . , Y τ ] . At any time instant n = 1 , 2 . . . , τ , the agent selects the measurement vector in general as a function of the past observ ations and measurements. Mathematically , S n = g n Y n − 1 , S n − 1 , (4) for some causal (possibly random) function g n : R n − 1 × U n − 1 B δ → U B δ . After observing the noisy observations Y τ and measurement matrix S τ , the agent estimates the target location W as follows ˆ W = d Y τ , S τ , (5) for some decision function d : R τ × U τ B δ → U B δ . The probability of error for a search is giv en by P e = P ( ˆ W 6 = W | Y , S ) and the av erage probability of error is gi ven by P e = P ( ˆ W 6 = W ) . No w we define the measurement strategy: Definition 1 ( -Reliable Search Strategy c ) . For some ∈ (0 , 1) , an -r eliable sear ch strate gy , denoted by c , is defined as a sequence of τ (possibly random) number of causal functions { g 1 , g 2 , . . . , g τ } , according to which the measurement matrix S τ is selected, and a decision function d which provides an estimate ˆ W of W , such that the av erage probability of error Pe is at most . December 19, 2017 DRAFT 6 Definition 2 (Achiev able T arget Acquisition Rate) . A target acquisition rate R is said to be an -achie vable , if for any small ξ > 0 and n large enough, there exists an -reliable search strategy c such the following holds E c [ τ ] ≤ n, (6) B δ ≥ 2 n ( R − ξ ) . (7) A targeting rate R is said to be achievable tar get acquisition rate if it is -achie v able for all ∈ (0 , 1) . The abov e definition is moti vated by information theoretic notion of transmission rate ov er a communication channel, which captures the exponential rate at which the number of messages gro w with the number of channel uses while the receiver can decode with a small av erage error probability . Similarly , the tar get acquisition rate captures the exponential rate at which the number of target locations gro w with the number of measurement vectors while a search strategy can still locate the target with a diminishing average error probability . Definition 3 (T ar get Acquisition Capacity) . The supremum of achie vable target acquisition rates is called the target acquisition capacity . B. T ypes of Sear ch Str ate gies and Adaptivity Gain Each measurement vector S n and the number of total measurements τ can be selected either based on the past observations Y n − 1 , or independent of them. Based on these two choices, strategies can be di vided into four types i) having fix ed length versus variable length number of the measurement matrix S , and ii) being adapti ve versus non-adapti ve. A fixed length -r eliable strate gy c uses a fixed number of measurements τ predetermined of fline independent of the observ ations, to obtain estimate ˆ W . On the other hand, a variable length -reliable strate gy c uses a random number of measurements τ (possibly determined as a function of the observations Y τ ) to obtain estimate, ˆ W . For example, τ can be selected such that agent achie ves P e ≤ in e very search and hence τ is a random variable which is a function of the past noisy observations. Under an adaptive strate gy c ∈ C A the agent designs the measurement vector S n as a function of the past observations Y n − 1 , i.e., g n is a function of both S n − 1 and Y n − 1 . Definition 4. Let C A be a class of all -reliable adapti ve strategies. December 19, 2017 DRAFT 7 Under a non-adaptive strate gy , the agent designs the measurement vector S n of fline indepen- dent of past observations, i.e., g n does not depend on S n − 1 or Y n − 1 . Definition 5. Let C N A be a class of all -reliable non-adapti ve strategies. For any -reliable strategy c , the performance is measured by the expected number of measurements E c [ τ ] . T o achie ve better reliability , i.e., smaller , in general the agent requires larger E c [ τ ] . Definition 6 (Adaptivity Gain) . The adapti vity gain is defined as the best reduction in the expected number of measurements when searching with an -reliable adapti ve strategy c 0 ∈ C A , ov er an -reliable non-adaptiv e strategy c ∈ C N A . Mathematically , it is giv en as min c ∈C N A E [ τ ] − min c 0 ∈C A E [ τ 0 ] . (8) Hence, characterizing adapti vity gain allows us to characterize the improv ement in target acquisition rate when using adaptiv e strategies ov er non-adapti ve strategies. I I I . P R E L I M I NA R I E S : C H A N N E L C O D I N G W I T H S TA T E A N D F E E D BA C K In this section, we revie w fundamentals of channel coding with state and feedback and relev ant literature to connect these information theoretic concepts to the problem of searching under measurement dependent noise discussed in the pre vious section. The aim is to formulate an equi valent model of channel coding with state and feedback for comparison to (3). Fig. 1. Transmission over a communication channel with state and feedback A communication channel is specified by a set of inputs ˜ X ∈ ˜ X , a set of outputs ˜ Y ∈ ˜ Y , and a channel transition probability measure P ( ˜ y | ˜ x ) for every ˜ x ∈ ˜ X and ˜ y ∈ ˜ Y that expresses the probability of observing a certain output ˜ y giv en that an input ˜ x was transmitted [15]. Throughout this work, we will concentrate on coding ov er a channel with state and feedback (section 4.6 December 19, 2017 DRAFT 8 in [1]). Formally , at time n the channel state, ˜ S n belongs to a discrete and finite set ˜ A . W e assume that the channel state is known at both the encoder and the decoder . For a channel with state, the transition probability at time n is specified by the conditional probability assignment P n ˜ Y n | ˜ X n , ˜ S n . T ransmission over such a channel is sho wn in Figure 1. In general, the channel state ˜ S n at time n ev olves as a function of all past outputs and all past states, ˜ S n = ˜ g n ( ˜ Y 1 , ˜ Y 2 , . . . , ˜ Y n − 1 , ˜ S 1 , ˜ S 2 , . . . , ˜ S n − 1 ) . (9) The goal is to encode and transmit a uniformly distrib uted message ˜ W ∈ [ M ] o ver the channel. The encoding function φ n at any time n depends on the message to be transmitted ˜ W , all past states, and all the past outputs. Thus the next symbol to be transmitted is given by ˜ X n = φ n ( ˜ Y 1 , ˜ Y 2 , . . . , ˜ Y n − 1 , ˜ S 1 , ˜ S 2 , ..., ˜ S n , ˜ W ) . (10) The encoder obtains the past outputs from the decoder due to the av ailability of a noiseless feedback channel from decoder to encoder . In this paper , we assume that both encoder and decoder kno w the ev olution of the channel state, i.e., the sequence { S n } n ≥ 1 . After τ channel uses, the decoder uses the noisy observations ˜ Y τ and state information { ˜ S 1 , ˜ S 2 , . . . , ˜ S τ } to find the best estimate ˜ W 0 , of the message ˜ W . The probability of error at the end of message transmission is gi ven by Pe = P ( ˜ W 0 6 = ˜ W | ˜ Y , { ˜ S 1 , ˜ S 2 , . . . , ˜ S τ } ) and the av erage probability of error is giv en by Pe = P ( ˜ W 0 6 = ˜ W ) . Example 3 (Binary Additi ve White Gaussian Noise channel with State and feedback) . Consider a Binary Additiv e White Gaussian Noise (B A WGN) channel with noisy output ˜ Y n gi ven as the sum of input ˜ X n ∈ { 0 , 1 } and Gaussian random variable ˜ Z n ∈ R whose distribution is a function of the channel state ˜ S n . Specifically , ˜ Z n is a Gaussian random variable with state dependent noise v ariance | ˜ S n | δ σ 2 for some δ > 0 . In other words, we have ˜ Y n = ˜ X n + ˜ Z n ( ˜ S n ) , (11) where ˜ Z n ∼ N (0 , | ˜ S n | δ σ 2 ) , and the state ev olves as ˜ S n = ˜ g n ( ˜ Y 1 , ˜ Y 2 , . . . , ˜ Y n − 1 , ˜ S 1 , ˜ S 2 , . . . , ˜ S n − 1 ) . T ransmission ov er a B A WGN channel is illustrated in Figure 2. Proposition 1. The pr oblem of sear ching under measur ement dependent Gaussian noise is equivalent to the pr oblem of channel coding over a BA WGN c hannel with state and feedbac k. Specifically , December 19, 2017 DRAFT 9 Y n Z n ~ (0, | S n | 2 ) X n ∈ {0,1} Fig. 2. Transmission over a BA WGN channel with binary input ˜ X n and Gaussian noise ˜ Z n . • The true location vector W can be cast as a message ˜ W to be transmitted over the BA WGN. Ther efore , ther e ar e B δ possible messages. • An -r eliable sear ch strate gy c pr ovides a sequence of { g 1 , g 2 , . . . , g τ } such that P ( ˜ W 0 6 = ˜ W ) ≤ . Hence, setting ˜ g i = g i for all i ∈ { 1 , 2 , . . . , τ } , the sear ch str ate gy dictates the evolution of channel states ˜ S n . • The measurement matrix S τ can be used as the codebook, i.e., by setting { ˜ S 1 , ˜ S 2 , . . . , ˜ S τ } = S . Specifically , codewor ds ar e obtained by setting ˜ X n = φ n ( ˜ Y n − 1 , ˜ S 1 , ˜ S 2 , . . . , ˜ S n , ˜ W ) = ˜ W | ˜ S n . • The measurement vector fixes the c hannel tr ansition pr obability measur e as P ( ˜ Y n | ˜ x n , ˜ S n ) = N ( ˜ x n , | ˜ S n | δ σ 2 ) since noise distribution is ˜ Z n ∼ N (0 , | ˜ S n | δ σ 2 ) for ˜ x n ∈ { 0 , 1 } . Hence, the channel state depends on measur ement vector . A coding scheme for a channel with state and feedback can double as a search strategy . This general approach of search using channel codes pro vides an efficient way to design and compare non-adapti ve and adapti ve search strate gies. This also implies that feedback can improve the capacity of a channel with state which is what we characterize as our adaptivity gain for the problem of searching under measurement dependent noise. Definition 7. The B A WGN capacity with input distrib ution Bern ( q ) and noise v ariance σ 2 is December 19, 2017 DRAFT 10 defined as C B A WGN q , σ 2 := − Z ∞ −∞ (1 − q ) G ( y ; 0 , σ 2 ) + q G ( y ; 1 , σ 2 ) × × log (1 − q ) G ( y ; 0 , σ 2 ) + q G ( y ; 1 , σ 2 ) − 1 2 log(2 π eσ 2 ) . (12) Corollary 1. F r om channel coding over a BA WGN channel with state and feedback, we obtain that for any small ξ > 0 and n lar ge enough, ther e exists an -r eliable sear ch strate gy c such the following holds E c [ τ ] ≤ n, (13) 2 n ( C BA WGN ( 1 2 , B σ 2 2 ) − ξ ) ( a ) ≤ B δ ( b ) < 2 nC BA WGN ( 1 2 ,δ σ 2 ) , (14) wher e ( a ) follows fr om Theor em 4.6.1 in [1] and ( b ) follows by combining the fact that the best channel is obtained when noise variance is the least, i.e., δ σ 2 , with the con verse of the noisy channel coding theor em [15]. I V . M A I N R E S U LT S In this section, we characterize a lower bound on the adaptivity gain min c ∈C N A E [ τ ] − min c 0 ∈C A E [ τ 0 ] ; the performance improvement measured in terms of reduction in the expected number of measurements for searching ov er a width B among B δ locations under measurement dependent Gaussian noise. Theorem 1. Let ∈ (0 , 1) . F or any -reliable non-adaptive strate gy c ∈ C N A sear ching over a sear ch re gion of width B among B δ locations with τ number of measur ements, ther e exists an -r eliable adaptive strate gy c 0 ∈ C A with τ 0 number of measur ements, such that for some small constant η > 0 the following holds E c [ τ ] − E c 0 [ τ 0 ] ≥ max α ∈I B δ log 1 α (1 − ) C BA WGN ( q ∗ , q ∗ B σ 2 ) − 1 C BA WGN ( q ∗ , q ∗ B σ 2 ) − η + log αB δ (1 − ) C BA WGN ( q ∗ , q ∗ B σ 2 ) − 1 C BA WGN 1 2 , αB σ 2 2 − η ! − h ( B , δ, σ 2 , α , , η ) , December 19, 2017 DRAFT 11 wher e h ( B , δ, σ 2 , α , , η ) = log 2 + log log 1 α + a η C BA WGN ( q ∗ , q ∗ B σ 2 ) − η + log 2 + log log αB δ + a η C BA WGN 1 2 , αB σ 2 2 − η + h ( ) C ( B ,δ,σ 2 ) BA WGN ( q ∗ , q ∗ B σ 2 ) , q ∗ = argmax q ∈I B δ C BA WGN ( q , q B σ 2 ) , and a η is the solution of the following equation η = a a − 3 max q ∈I B δ Z ∞ −∞ e − y 2 2 B q σ 2 p 2 π q B σ 2 2 y − 1 2 q B σ 2 ( a − 3) dy . (15) Proof of Theorem 1 is obtained by combining Lemma 1 and Lemma 2. Theorem 1 provides a non-asymptotic lower bound on adapti vity gain. The bound can be viewed as two parts corresponding to two stages. Intuitively , the first part corresponds to the initial stage of the search, where the agent narro ws down the target’ s location to some coarse α fractions of the total search region, i.e., narro ws to a section of width α B with high confidence. The second stage corresponds to refined the search within one of the coarse sections αB obtained from initial stage. This implies that an adaptiv e strategy can zoom in and confine the search to a smaller section to reduce the noise intensity . Whereas, a non adaptiv e strategy does not adapt to zoom in, and thus performs equally in both stages. W e formalize this intuition in Lemma 2. Optimizing ov er α fraction of the first search we obtain a bound on expected number of measurements. W e obtain the following corollary as a consequence of Theorem 1. Corollary 2. Let ∈ (0 , 1) . F or any -r eliable non-adaptive strate gy c ∈ C N A sear ching over a sear ch r e gion of width B among B δ with τ number of measur ements, there exists an -r eliable adaptive strate gy c 0 ∈ C A with τ 0 number of measurements, suc h that for a fixed B the asymptotic adaptivity gain gr ows logarithmically with the total number of locations, lim δ → 0 E c [ τ ] − E c 0 [ τ 0 ] log B δ ≥ 1 − C BA WGN ( q ∗ , q ∗ B σ 2 ) − 1 . (16) F or a fixed δ , the asymptotic adaptivity gain gr ows at least linearly with total number of locations, lim B →∞ E c [ τ ] − E c 0 [ τ 0 ] B δ log B δ ≥ (1 − ) σ 2 δ log e . (17) Furthermor e, we have lim B →∞ min c ∈C N A E c [ τ ] B δ log B δ ≥ (1 − ) σ 2 δ log e , (18) December 19, 2017 DRAFT 12 and lim B →∞ min c ∈C A E c 0 [ τ 0 ] B δ = 0 . (19) The proof of the above corollary is provided in Appendix-C. Remark 1. The above corollary characterizes the two qualitativ ely different regimes pre viously discussed. F or fix ed B , as δ goes to zero the asymptotic adapti vity gain scales as only log B δ , whereas for fixed δ , as B increases the asymptotic adapti vity gain scales as B δ log B δ . In other words, tar get acquisition rate improves by a constant for fixed B as δ decreases while it gro ws linearly with B for a fixed δ . In other words, adaptivity pro vides a larger gain in target acquisition rate for the regime where the total search width is growing than in the case where we fix the total width and shrink the location widths. In Section VI we related this phenomenon to the diminishing capacity of B A WGN channel when the total noise B σ 2 2 gro ws. Next we provide the main technical components of the proof of Theorem 1. A. Con verse: Non-Adaptive Sear ch Str ate gies Lemma 1. The minimum expected number of measur ements requir ed for any -r eliable non- adaptive sear ch strate gy can be lower bounded as min c ∈C N A E c [ τ ] ≥ (1 − ) log B δ − h ( ) C BA WGN ( q ∗ , q ∗ B σ 2 ) . Proof of the Lemma 1 is provided in Appendix-A. The proof follows from the fact that clean signal X i and noise Z i are independent ov er time and independent of past observ ations for i = 1 , 2 , . . . , n , due to the non-adapti ve nature of the search strategy . In the absence of information from past observ ation outcomes, the agent tries to maximize the mutual information I ( X i , Y i ) at ev ery measurement. Since X i ∼ Bern ( q i ) and Z i ∼ N (0 , q i B σ 2 ) , the mutual information I ( X i , Y i ) = C B A WGN ( q i , q i B σ 2 ) is maximized at q i = q ∗ . B. Achie vability: Adaptive Sear ch Strate gy Consider the following two stage search strategy . December 19, 2017 DRAFT 13 1) F irst Stage (F ixed Composition Strate gy c 1 2 ): W e group the B δ locations of width δ into 1 α sections of width αB . Let W 0 denote the true location of the tar get among the sections of width αB . Now , we use a non-adaptive strate gy to search for the target location among 1 α sections of width α B . In particular , we use a fixed composition strategy where at e very time instant n , the fraction of total locations probed is fixed to be q ∗ . In other words, the measurement vector S 0 n at ev ery instant n is picked uniformly randomly from the set of measurement vectors { S 0 ∈ U 1 α : | S 0 | = b q ∗ α c} . F or the ease of exposition, we assume that q ∗ α is an inte ger . Hence, for this strategy , at ev ery n , X n ∼ Bern ( q ∗ ) and Z n ∼ N (0 , q ∗ B σ 2 ) . For all i ∈ { 1 , 2 , . . . , 1 α } , let ρ 0 n ( i ) be the posterior probability of the estimate ˆ W 0 ( i ) = 1 after reception of Y n − 1 , i.e., ρ 0 n ( i ) := P ˆ W 0 ( i ) = 1 | Y n − 1 and let ρ 0 n := ρ 0 n (1) , ρ 0 n (2) , . . . , ρ 0 n 1 α . Assume that agent begins with a uniform probability ov er the 1 α sections, i.e., ρ 0 0 = { α , α, . . . , α } . The posterior probability ρ 0 n +1 ( i ) at time n + 1 when Y n = y is obtained by the following Bayesian update: ρ 0 n +1 ( i ) = ρ 0 n ( i ) G ( y ;1 ,q ∗ B σ 2 ) D 0 n if S 0 n ( i ) = 1 , ρ 0 n ( i ) G ( y ;0 ,q ∗ B σ 2 ) D 0 n if S 0 n ( i ) = 0 , (20) where D 0 n = X j : 1 { S n ( j )=1 } ρ 0 n ( j ) G ( y ; 1 , q ∗ B σ 2 ) + X j : 1 { S n ( j )=0 } ρ 0 n ( j ) G ( y ; 0 , q ∗ B σ 2 ) . (21) Let τ 1 := inf n : max i ρ 0 n ( i ) ≥ 1 − 2 be the number of measurements used under stage 1. Note that τ 1 is a random v ariable. Hence, first stage is a non-adapti ve variable length strategy . No w , the expected stopping time E c 1 2 [ τ 1 ] can be upper bounded using Lemma 3 from Appendix- B. 2) Second Stage (Sorted P osterior Matching Strate gy c 2 2 ): In the second stage, the agent zooms into the αB width section obtained from the first stage and uses an adapti ve strategy to search only within this αB section. The agent searches for the tar get location of width δ among the remaining αB δ locations. In particular , we use the sorted posterior matching strategy proposed in [2] which we describe next. Let W 00 denote the true target location of width δ . For all i ∈ { 1 , 2 , . . . , αB δ } , let ρ 00 n ( i ) be the posterior probability of the estimate ˆ W 00 ( i ) = 1 after reception of Y n − 1 , i.e., ρ 0 n ( i ) := P ˆ W 00 ( i ) = 1 | Y n − 1 and let ρ 00 ( n ) := { ρ 00 n (1) , ρ 00 n (2) , . . . , ρ 00 n αB δ } . Assume the agent begins with a uniform probability over the αB δ sections, i.e., ρ 00 0 = δ αB , δ αB , . . . , δ αB . At ev ery time instant n , we sort the posterior values in December 19, 2017 DRAFT 14 descending order to obtain the sorted posterior vector ρ ↓ n . Let vector I n denote the corresponding ordering of the location indices in the new sorted posterior . Define k ∗ n := argmin i i X j =1 ρ ↓ n ( j ) − 1 2 . (22) W e choose the measurement vector S 00 n such that S 00 n ( j ) = 1 if and only if j ∈ { I n (1) , I n (2) , . . . , I n ( k ∗ n ) } . Note that for this strategy , at e very n , the noise is Z n ∼ N (0 , | S 00 n | δ σ 2 ) and the worst noise intensity is N (0 , αB σ 2 2 ) . The posterior probability ρ 00 n +1 ( i ) at time n + 1 when Y n = y is obtained by the following Bayesian update: ρ 00 n +1 ( i ) = ρ 00 n ( i ) G ( y ;1 , | S 00 n | δ σ 2 ) D 00 n if S 00 n ( i ) = 1 , ρ 00 n ( i ) G ( y ;0 , | S 00 n | δ σ 2 ) D 00 n if S 00 n ( i ) = 0 , (23) where D 00 n = X j : 1 { S n ( j )=1 } ρ 00 n ( j ) G y ; 1 , | S 00 n | δ σ 2 + X j : 1 { S n ( j )=0 } ρ 00 n ( j ) G y ; 0 , | S 00 n | δ σ 2 . (24) Let τ 2 := inf n : max i ρ 2 n ( i ) ≥ 1 − 2 be the number of measurements used under stage 2. Note that τ 2 is a random v ariable. Hence, the second stage is an adaptiv e v ariable length strategy . The expected number of measurements E c 2 2 [ τ 00 ] can be upper bounded using Lemma 6 from Appendix-B. Noting that the total probability of error of the two stage search strategy is less than and that the e xpected stopping time is E c 0 [ τ 0 ] = E c 1 2 [ τ 1 ] + E c 2 2 [ τ 2 ] , we hav e the assertion of the follo wing lemma. Lemma 2. The minimum expected number of measur ements r equir ed for the above -r eliable adaptive sear ch strate gy c 0 can be upper bounded as E c 0 [ τ 0 ] ≤ min α ∈I B δ ( log 1 α + log 2 + log log 1 α + a η C BA WGN ( q ∗ , q ∗ B σ 2 ) − η + log αB δ + log 2 + log log αB δ + a η C BA WGN 1 2 , αB σ 2 2 − η ) . (25) Remark 2. For an -reliable adaptiv e search strategy c 0 ∈ C A using the two stage strategy , the non-asymptotic upper bound provided by Lemma 2 for min c 0 ∈C A E 0 c [ τ 0 ] is tighter than the upper bound provided in [2] using the sorted posterior matching strategy . In fact, for an y giv en α , our bound is significantly smaller than the upper bound in [2]. In the asymptotically dominating terms of the order log B δ , our upper bound closely follows the simulations as illustrated in Section VI. December 19, 2017 DRAFT 15 Remark 3. In the regime of fix ed B and diminishing δ , Lemma 2 together with Corollary 1 establishes the optimality of our proposed algorithm. Further , it characterizes a lo wer bound on the increase in targeting capacity when utilizing an adapti ve strategy ov er the non-adaptiv e strategies. V . E X T E N S I O N S A N D G E N E R A L I Z A T I O N S A. Generalization to other noise models The main results presented in this paper consider the setup where the noise Z n is distributed as N (0 , | S n | δ σ 2 ) . In other words, the variance of the noise gi ven by ( | S n | δ σ 2 ) is a linear function of the size of a measurement vector | S n | . This model assumption holds when each target location adds noise equally and independently of other locations when probed together . In general, due to correlation across locations the additi ve noise v ariance can be assumed to scale as a non- decreasing function f ( · ) of the measurement vector | S n | . In this section, we extend our model to a general formulation for the noise Z n ∼ N (0 , f ( | S n | ) δ σ 2 ) , where f ( · ) is a non-decreasing function of | S n | . For example, f ( S n ) = | S n | γ for some γ > 0 . Figure 3, sho ws that the ef fect of the noise function f ( | S n | ) on the capacity . 0 10 20 30 40 50 0 0.2 0.4 0.6 0.8 1 Fig. 3. Behavior of capacity of BA WGN channel with σ 2 = 0 . 25 over a total search region of width B = 10 , location width δ = 0 . 1 , as a function of the size of a measurement | S n | . December 19, 2017 DRAFT 16 Theorem 2. Let ∈ (0 , 1) and let f ( · ) be a non-decr easing function. F or any -r eliable non- adaptive strate gy c ∈ C N A sear ching over a searc h re gion of width B among B δ locations with τ number of measur ements, ther e exists an -reliable adaptive strate gy c 0 ∈ C A with τ 0 number of measur ements, such that for some small constant η > 0 the following holds E c [ τ ] − E c 0 [ τ 0 ] ≥ max α ∈I B δ ( log 1 α (1 − ) C BA WGN ( q ∗ , f ( q ∗ B δ ) δ σ 2 ) − 1 C BA WGN q ∗ , f ( q ∗ B δ ) δ σ 2 − η ! + log αB δ (1 − ) C BA WGN ( q ∗ , f ( q ∗ B δ ) δ σ 2 ) − 1 C BA WGN 1 2 , f ( αB 2 δ ) δ σ 2 − η !)! (1 + o (1)) , wher e q ∗ = argmax q ∈I B δ C BA WGN ( q , f ( q B δ ) δ σ 2 ) , and o (1) goes to 0 as B δ → ∞ . B. Multiple T ar gets The problem formulation and the main results of this paper consider the special case when there exists a single stationary tar get. Suppose instead the agent aims to find the true location of r unique targets quickly and reliably . Our problem formulation is easily e xtended to the general case where there may exist multiple targets. In our generalization to multiple tar gets under the linear noise model (3), the clean signal indicates the the number of tar gets present in the measurement vector S n . In particular , let W ( i ) ∈ U B δ be such that W ( i ) ( j ) = 1 if and only if j -th location contains the i -th target. Then, the noisy observation is given as Y n = r X i =1 ( W ( i ) ) | S n + Z n , (26) where Z n ∼ N (0 , | S n | δ σ 2 ) . Setting X ( i ) n = ( W ( i ) ) | S n for i ∈ [ r ] , we have Y n = r X i =1 X ( i ) n + Z n . (27) The problem of searching for multiple targets is equiv alent to the problem of channel coding over a Multiple Access Channel (MA C) with state and feedback [16]. In other words, we can extend the Proposition 1, to channel coding o ver a MA C with state and feedback with the following constraints: (i) W ( i ) can be vie wed as the message to be transmitted by the i -th transmitter , (ii) the measurement matrix S n can be vie wed as the common codebook shared by all the December 19, 2017 DRAFT 17 transmitters, and (iii) a search strategy dictates the e volution of the MA C state. The channel transition is then fixed by the channel state which is measurement dependent. Example 1 0 (Establishing initial access in mm-W a ve communications). In the deployment of mm-W a ve links into a cellular or 802.11 network, the base station needs to to quickly switch between users and accommodate multiple mobile clients. In this setup at time n the noisy observ ation, Y n , is a function of multiple users in the network, in addition to a measurement dependent noise. Example 2 0 (Spectrum Sensing for Cognitiv e Radio). Consider the problem of opportunisti- cally searching for r vacant subbands of bandwidth δ over a total bandwidth of B . In this problem we desire to locate r stationary v acant subbands quickly and reliably , by making measurements ov er time. Here again the noise intensity depends on the number of subbands probed, S n , at each time instant n . Searching for multiple targets with measurement dependent noise is a significantly harder problem compared to a single target case and achie vability strategies for this problem ev en in the absence of noise are far more complex [17], [18] . V I . N U M E R I C A L R E S U LT S In this section we provide numerical analysis. A. Comparing Sear ch Strate gies In this section, we numerically compare four strate gies proposed in the literature. Besides the sort PM strategy c 2 and the optimal variable length non-adapti ve strategy i.e., the fix ed composition strategy c 1 , we also consider two noisy variants of the binary search strategy . The noisy binary search applied to our search proceeds by selecting S n as half the width of the pre vious search region S n − 1 with higher posterior probability . The first v ariant we consider is fixed length noisy binary search, resembles the adaptiv e iterativ e hierarchical search strategy [5], where each measurement v ector S n is used α ( S n ) | S n | times where α ( S n ) is chosen such that entire search result in an -reliable search strategy . The second v ariant is v ariable length noisy binary search where each measurement v ector S n is used until in each search we obtain error probability less than p := log B /δ . T able I provides a quick summary of the search strategies. Figure 4, shows the performance of each -reliable search strategy , when considering fixed parameters B , δ , and . W e note that the fix ed length noisy binary strategy performs poorly December 19, 2017 DRAFT 18 T ABLE I C A N D I DA T E S E A R C H S T R A T E G I E S Strategies c ∈ C Description of S n selection V ariable Length Random • Select S n s.t. | S n | = q ∗ B δ as dictated by strategy c 1 Fixed Length Noisy Binary • Select S n as dictated by binary search strategy • Repeat α ( S n ) | S n | times V ariable Length Noisy Binary • Select S n as dictated by binary search strategy • Repeat τ times s.t. τ =min { n : k ρ n k ∞ ≥ 1 − p } Sorted Posterior Matching • Select S n as dictated by Sort PM strategy c 2 in comparison to the optimal non-adapti ve strategy . This sho ws that randomized non-adapti ve search strategies such as the one considered in [7] perform better than both exhausti ve search and iterativ e hierarchical search strategy . In particular , it performs better than variable length noisy binary search since when SNR is high since each measurement is repeated far too many times in order to be -reliable. The performance of the optimal fully adaptive variable length strategies sort PM [2] is superior to all strategies even in the non-asymptotic regime. B. T wo Distinct Re gimes of Operation In this section, for a fixed σ 2 we are interested in the expected number of measurements required E c [ τ ] by an -reliable strategy c , in the following two regimes: varying δ while keeping B fixed, and varying B while keeping δ fix ed. Figures 5 and 6 show the simulation results of E c [ τ ] as a function of width B and resolution δ respecti vely , for the fixed composition non adapti ve strate gy c ∈ C N A and for the sort PM adaptiv e strategy c ∈ C A , along with dominant terms of the lower bound of Lemma 1, and the upper bound of Lemma 2 for a fixed noise per unit width σ 2 = 0 . 25 . For both of these cases, we see that the adapti vity gain grows as the total number of locations increases; howe ver in distinctly different manner as seen in Corollary 2. December 19, 2017 DRAFT 19 10 -2 10 -1 0 50 100 150 Fixed Length Noisy Binary Variable Length Random Variable Length Noisy Binary Sorted Posterior Matching Fig. 4. E c [ τ ] with = 10 − 4 , B = 16 , and δ = 1 , as a function of σ 2 for various strategies. C. Relating the Re gimes of Operation to Capacity In this section, we attempt to relate these two regimes of operation to the manner in which the capacity of a BA WGN channel v aries. Let noise parameter Z n ∼ N (0 , 2 q σ 2 T otal ) , where q = | S n | δ B is the fraction of the search region measured and σ 2 T otal = B σ 2 2 is the half bandwidth v ariance. Figure 7 sho w the effects of the half bandwidth v ariance on the capacity of a search as a function of q . Intuiti vely , the target acquisition rate of the adaptiv e strategy relates to the time spent searching sets of size q as q varies from 1 2 to δ B . This means for sufficiently small σ 2 T otal ( ≤ 0 . 005 in this e xample), the adapti vity gain is negligible since C B A WGN ( 1 2 , 2 q σ 2 T otal ) is about 1 for all q . For medium range σ 2 T otal (for e.g., 0 . 05 in this example), the adapti vity ef fects the target acquisition rate from C B A WGN ( 1 2 , 2 q ∗ σ 2 T otal ) to C B A WGN ( 1 2 , 2 δ B σ 2 T otal ) . When σ 2 T otal gro ws significantly , howe ver , the capacity drops rather quickly to zero, forcing the non-adaptiv e strategies to operate close to exhausti ve search, whose measurement time increases linearly in B δ . This is the regime with most significant adaptivity gain as predicted by Corollary 2. December 19, 2017 DRAFT 20 0 200 400 600 0 2000 4000 6000 8000 10000 12000 14000 Non-Adaptive: Simulation Non-Adaptive: Lower Bound Adaptive: Upper Bound Adaptive: Simulation Fig. 5. E c [ τ ] with = 10 − 4 , σ 2 = 0 . 25 , and δ = 1 , as a function of B. D. Be yond i.i.d In this section, we analyze E c [ τ ] under a general noise model, as presented in section (VI-A). Recall, Y n ∼ N ( X n , f ( | S n | ) δ σ 2 ) , where f is a non-decreasing function of the measurement vector | S n | . Figure 3 sho ws that the behavior of the capacity range of a search with fixed parameters B , δ , S n can be significantly affected by the function f ( · ) . Let us consider the noise function f ( · ) to be of the form | S n | γ . Figure 8 shows the plot of dominant terms of the lo wer bound of Lemma 1, and the upper bound of Lemma 2 as a function of σ 2 for the v alues of γ ∈ { 0 . 5 , 1 , 2 } . The adaptivity gain is clearly more significant for larger values of gamma and hence, validates the need for generalizing the noise function. V I I . C O N C L U S I O N A N D F U T U R E W O R K W e considered the problem of searching for a target’ s unknown location under measurement dependent Gaussian noise. W e showed that this problem is equiv alent to channel coding o ver a B A WGN channel with state and feedback. W e used this connection to utilize feedback code based adaptiv e search strategies. W e obtained information theoretic con verses to characterize the fundamental limits on the target acquisition rate under both adaptiv e and non-adaptiv e strategies. December 19, 2017 DRAFT 21 0 200 400 600 0 5 10 15 20 25 Non-Adaptive: Simulation Non-Adaptive: Lower Bound Adaptive: Upper Bound Adaptive: Simulation Fig. 6. E c [ τ ] with = 10 − 4 , σ 2 = 0 . 25 and B = 1 , as a function of δ . As a corollary , we obtained a lower bound on the adaptivity gain. W e identified two asymptotic regimes with practical applications where our analysis shows that adapti ve strategies are far more critical when either noise intensity or the total search width is large. In contrast, in scenarios where neither the total width nor noise intensity is lar ge, non-adapti ve strategies might perform quite well. The immediate step is the extension of this work to a model with r > 1 target locations, where the problem has been sho wn to be equi v alent to MA C encoding with feedback [16]. December 19, 2017 DRAFT 22 0 0.1 0.2 0.3 0.4 0.5 0 0.2 0.4 0.6 0.8 1 Fig. 7. For arbitrary B and δ , and with = 10 − 4 , E c [ τ ] as a function of q for different values of total noise variance ( σ 2 T otal ) A P P E N D I X A. Pr oof of Lemma 1 Applying Fano’ s inequality [15] to any non-adapti ve search strategy that locates the target among B δ locations with P e ≤ , we hav e log B δ ( a ) ≤ 1 1 − sup X n n X i =1 I ( X i , Y i ) + h ( ) 1 − ( b ) ≤ 1 1 − n X i =1 C B A WGN q i , q i B σ 2 + h ( ) 1 − ≤ n 1 − max q ∈ I B δ C B A WGN ( q , q B σ 2 ) + h ( ) 1 − , (28) where ( a ) follo ws from the fact that X i and Z i for i = 1 , 2 , . . . , n are independent ov er time and independent of past observ ations due to the non-adapti ve nature of the search strategy . Since X i ∼ Bern ( q i ) and Z i ∼ N (0 , q i B σ 2 ) , ( b ) follows from the fact that I ( X i , Y i ) = C B A WGN ( q i , q i B σ 2 ) . Rearranging the abov e equation, we have the assertion of the lemma. December 19, 2017 DRAFT 23 10 -4 10 -3 10 -2 4 6 8 10 12 14 16 18 20 22 Fig. 8. E c [ τ ] with = 10 − 4 , σ 2 = 0 . 25 and B = 25 , δ = 1 , as a function of γ when Z n ∼ N (0 , | S n | γ δ σ 2 ) . B. Pr oof of Lemma 2 For any q ∈ I B δ and under any query vector S n ∈ U B δ such that | S n | = q B δ we hav e the follo wing log P ( y | S n , W ( i ) = 1) P ( y | S n , W ( j ) = 1) = 0 if S n ( i ) = 1 and S n ( j ) = 1 , 0 if S n ( i ) 6 = 1 and S n ( j ) 6 = 1 , 2 y − 1 2 q B σ 2 Otherwise . (29) Hence, we hav e max i,j ∈ [ B δ ] max S n ∈U B δ Z ∞ −∞ P ( y | S n , W ( i ) = 1) log P ( y | S n , W ( i ) = 1) P ( y | S n , W ( j ) = 1) 1+ γ = max q ∈I B δ Z ∞ −∞ e − y 2 2 qB σ 2 p 2 π q B σ 2 2 y − 1 2 q B σ 2 1+ γ dy . (30) Therefore, there exists ξ B δ < ∞ and γ > 0 such that max i,j ∈ [ B δ ] max S n ∈U B δ Z ∞ −∞ P ( y | S n , W ( i ) = 1) log P ( y | S n , W ( i ) = 1) P ( y | S n , W ( j ) = 1) 1+ γ ≤ ξ B δ . (31) December 19, 2017 DRAFT 24 Define ψ B δ ( a ) := max q ∈I B δ Z ∞ −∞ e − y 2 2 B q σ 2 p 2 π q B σ 2 2 y − 1 2 q B σ 2 a dy , (32) and recall that [ g ] a = g if g ≥ a , 0 if g < a . (33) Note that ψ B δ ( a ) is non-increasing in a, and we hav e ψ B δ ( a ) ≤ a − γ ξ B δ . Hence, ψ B δ ( a ) → 0 as a → ∞ . 1) Stage I: Lemma 3. Under the fixed composition sear ch strate gy while sear ching over a sear ch r e gion of width B among 1 α locations such that | S 0 n | α = q ∗ for n ≥ 1 , the following holds true for all n ≥ 1 E U ( ρ 0 n +1 ) − U ( ρ 0 n ) |F n , S 0 n ≥ C BA WGN q ∗ , q ∗ B σ 2 , (34) wher e define U ( ρ 0 n ) := P 1 α i =1 ρ 0 n ( i ) log ρ 0 n ( i ) 1 − ρ 0 n ( i ) . Pr oof. The proof follows closely the proof of inequality (9) in [19]. There are 1 α locations of length αB and hence query vector S 0 n ∈ U 1 α . At e very time instant under the fixed composition strategy K ∗ = | S n | = q ∗ α number of locations are searched. i.e., a re gion of length q ∗ B is searched. Let P K ∗ denote the collection of all partitions p of search locations 1 to 1 α into sets A 0 n and A 1 n such that | A 1 n | = K ∗ . The probability of picking a partition p ∈ P K ∗ is λ p = 1 α K ∗ − 1 . For simplicity of exposition let M = 1 α . Also, we hav e P p ∈P K ∗ λ p 1 { i ∈ A 0 n } = π ∗ 0 := M − K ∗ M , and P p ∈P K ∗ λ p 1 { i ∈ A 1 n } = π ∗ 1 := K ∗ M . Since a region of q ∗ B is searched at ev ery time instant, the noise variance is fixed at q ∗ B σ 2 . December 19, 2017 DRAFT 25 Hence, let P k = P ( Y | X = k , | A 1 n | = K ∗ ) = N ( k , q ∗ B σ 2 ) for k ∈ { 0 , 1 } . Consider E U ( ρ 0 n +1 ) − U ( ρ 0 n ) |F n , S n = X p ∈P K ∗ λ p M X i =1 1 X k =0 ρ 0 n ( i ) 1 { i ∈ A k n } D P k X j 6 = i 1 X l =1 ρ 0 n ( j ) 1 − ρ 0 n ( i ) 1 { i ∈ A l n } P l ! = M X i =1 ρ 0 n ( i ) 1 X k =0 π ∗ k X p ∈P K ∗ λ p π ∗ k 1 { i ∈ A k n } D P k X j 6 = i 1 X l =1 ρ 0 n ( j ) 1 − ρ 0 n ( i ) 1 { i ∈ A l n } P l ! ( a ) ≥ M X i =1 ρ 0 n ( i ) 1 X k =0 π ∗ k D P k X j 6 = i 1 X l =1 ρ 0 n ( j ) 1 − ρ 0 n ( i ) X p ∈P K ∗ λ p π ∗ k 1 { i ∈ A k t } 1 { i ∈ A l t } P l ( b ) = M X i =1 ρ 0 n ( i ) π ∗ 1 D P 1 K ∗ − 1 M − 1 P 1 + M − K ∗ M − 1 P 0 + π ∗ 0 D P 0 M − K ∗ − 1 M − 1 P 0 + K ∗ M − 1 P 1 ≥ M X i =1 ρ 0 n ( i ) π ∗ 1 D P 1 K ∗ M P 1 + M − K ∗ M P 0 π ∗ 0 D P 0 M − K ∗ M P 0 + K ∗ M P 1 ( c ) = C B A WGN q ∗ , q ∗ B σ 2 , (35) where ( a ) follo ws from Jensen’ s inequality ( b ) follo ws from the definition of π ∗ 0 , π ∗ 1 and P p ∈P K ∗ λ p 1 { i ∈ A 0 n } 1 { j ∈ A 1 n } = P p ∈P K ∗ λ p 1 { i ∈ A 1 n } 1 { j ∈ A 0 n } = K ∗ ( M − K ∗ ) M ( M − 1) , P p ∈P K ∗ λ p 1 { i ∈ A 0 n } 1 { j ∈ A 0 n } = π ∗ 0 ( M − K ∗ − 1) M − 1 , P p ∈P K ∗ λ p 1 { i ∈ A 1 n } 1 { j ∈ A 1 n } = π ∗ 1 ( K ∗ − 1) M − 1 , and ( c ) is the definition of non-adapti ve B A WGN channel capacity with input distribution Bern ( q ∗ ) and noise variance q ∗ B σ 2 . Lemma 4. Under the fixed composition sear ch strate gy while sear ching over a sear ch r e gion of width B among 1 α locations such that | S 0 n | α = q ∗ for n ≥ 1 , the following holds true for the expected number of queries while sear ching with P e ≤ 2 E c 1 [ τ 1 ] ≤ log 1 α + log 2 + log log B δ + a η C BA WGN ( q ∗ , q ∗ B σ 2 ) − η . (36) Proof is similar to the proof of Lemma 6. December 19, 2017 DRAFT 26 2) Stage II: Note that BA WGN capacity for all q ∈ I B δ C B A WGN 1 2 , q B σ 2 = D N (0 , q B σ 2 ) 1 2 N (0 , q B σ 2 ) + 1 2 N (1 , q B σ 2 ) = D N (1 , q B σ 2 ) 1 2 N (0 , q B σ 2 ) + 1 2 N (1 , q B σ 2 ) . (37) Hence, the following Lemma follo ws from Proposition 3 in [20]. Lemma 5. Under the sortPM sear ch strate gy while sear ching over a sear ch re gion of width α B among αB δ locations, the following holds true for all n ≥ 1 E U ( ρ 00 n +1 ) − U ( ρ 00 n ) |F n , S n ≥ C BA WGN 1 2 , αB σ 2 2 , (38) wher e define U ( ρ 00 n ) := P αB δ i =1 ρ 00 n ( i ) log ρ 00 n ( i ) 1 − ρ 00 n ( i ) . Lemma 6. Under the sortPM sear ch strate gy , the following holds true for the expected number of queries while sear ching over the sear ch width αB among αB δ locations with P e ≤ 2 E c 2 [ τ 2 ] ≤ log αB δ + log 2 + log log αB δ + a η C BA WGN 1 2 , αB σ 2 2 − η , (39) wher e a η is the solution of the following equation η = a a − 3 ψ B δ ( a − 3) . (40) Pr oof. Let M = αB δ . Let ˜ ρ 0 = 1 − 1 1+max { log M , 2 } . Now , define U 0 ( ρ 00 0 ) = U ( ρ 00 0 ) − log ˜ ρ 0 1 − ˜ ρ 0 and define U 0 ( ρ 00 n ) as follows: if U 0 ( ρ 00 n ) < 0 , then U 0 ( ρ 00 n +1 ) = U ( ρ 00 n +1 ) − U ( ρ 00 n ) + U 0 ( ρ 00 n ) if U ( ρ 00 n +1 ) − U ( ρ 00 n ) < a − U 0 ( ρ 00 n ) , a if U ( ρ 00 n +1 ) − U ( ρ 00 n ) ≥ a − U 0 ( ρ 00 n ) , (41) and if U 0 ( ρ 00 n ) ≥ 0 , then U 0 ( ρ 00 n +1 ) = U ( ρ 00 n +1 ) − U ( ρ 00 n ) + U 0 ( ρ 00 n ) if U ( ρ 00 n +1 ) − U ( ρ 00 n ) < a , a + U 0 ( ρ 00 n ) if U ( ρ 00 n +1 ) − U ( ρ 00 n ) ≥ a . (42) By induction we can show that log ˜ ρ 0 1 − ˜ ρ 0 ≤ U ( ρ 00 n ) − U 0 ( ρ 00 n ) . (43) December 19, 2017 DRAFT 27 W e hav e E U 0 ( ρ 00 n +1 ) − U 0 ( ρ 00 n ) |F n = E U ( ρ 00 n +1 ) − U ( ρ 00 n ) |F n + E h − b − U ( ρ 00 n +1 ) + U ( ρ 00 n ) − U 0 ( ρ 00 n ) 1 { U 0 ( ρ 00 n ) < 0 } + |F n i ( a ) ≥ E U ( ρ 00 n +1 ) − U ( ρ 00 n ) |F n − a a − 3 ψ B δ ( a − 3) ( b ) ≥ C B A WGN 1 2 , αB σ 2 2 − a a − 3 ψ B δ ( a − 3) , (44) where ( a ) follows from MN thesis eq (4.140) and ( b ) follows Lemma 5. Let τ 0 = min { n : U 0 ( ρ 00 n ) ≥ 0 } and τ = min { n : U ( ρ 00 n ) ≥ log ˜ ρ 1 − ˜ ρ } where ˜ ρ = 1 − 2 . From equation (43) and since ˜ ρ 0 > ˜ ρ , we ha ve E c 2 [ τ 2 ] ≤ E c 2 | ˜ τ 0 ] . (45) The sequence U 0 ( ρ 00 n ) C BA WGN 1 2 , αB σ 2 2 − a a − 3 ψ B δ ( a − 3) − n forms a submartingale with respect to filtration F n . Now by Doob’ s Stopping Theorem we hav e U 0 ( ρ 00 0 ) C B A WGN 1 2 , αB σ 2 2 − a a − 3 ψ B δ ( a − 3) ≤ E " U 0 ( ρ 00 ˜ τ 0 ) C B A WGN 1 2 , αB σ 2 2 − a a − 3 ψ B δ ( a − 3) − ˜ τ 0 # . (46) Hence, we hav e E c 2 [ ˜ τ 0 ] ≤ − U 0 ( ρ 00 0 ) + E [ U 0 ( ρ 00 ˜ τ 0 )] C B A WGN 1 2 , αB σ 2 2 − a a − 3 ψ B δ ( a − 3) = − U ( ρ 00 0 ) + log ˜ ρ 0 1 − ˜ ρ 0 + E [ U 0 ( ρ 00 ˜ τ 0 )] C B A WGN 1 2 , αB σ 2 2 − a a − 3 ψ B δ ( a − 3) ( a ) ≤ log αB δ + log log αB δ + log 2 + E [ U 0 ( ρ 00 ˜ τ 0 )] C B A WGN 1 2 , αB σ 2 2 − a a − 3 ψ B δ ( a − 3) ( b ) ≤ log αB δ + log log αB δ + log 2 + a C B A WGN 1 2 , αB σ 2 2 − a a − 3 ψ B δ ( a − 3) , (47) where ( a ) follows from the fact that U ( ρ 00 0 ) = − log( B δ − 1) and ( b ) follows from the fact that for all n < τ 0 , U 0 ( ρ 00 n ) < 0 and hence from equation (41) we have U 0 ( ρ 00 ˜ τ 0 ) < a . Let η > 0 such that η C B A WGN 1 2 , αB σ 2 2 . Choose a η such that η = a a − 3 ψ B δ ( a − 3) . (48) W e ha ve the assertion of the lemma by combining above equation with equations (45) and (47). December 19, 2017 DRAFT 28 C. Pr oof of Cor ollary 2 Choose a η = log log B δ so that η goes to zero as B δ → ∞ , and choose α ( B δ ) = 1 log B δ . Note that α ( B δ ) goes to 0 slower than δ goes to 0 . Combining this with Theorem 1 and using the fact lim δ → 0 C B A WGN 1 2 , 1 2 α B δ B σ 2 = 1 , we hav e equation (16). Similarly , note that α ( B δ ) goes to 0 slower than B goes to ∞ . Using loose approximations C B A WGN ( q ∗ , q ∗ B σ 2 ) ≤ log e B σ 2 and C B A WGN 1 2 , α ( B δ ) B σ 2 ≥ log( B δ ) 16 B σ 2 1 − log( B δ ) 16 B σ 2 with Theorem 1 we have equations (18–17). R E F E R E N C E S [1] R. G. Gallager, Information Theory and Reliable Communication . John W iley & Sons, Inc., 1968. [2] S. Chiu and T . Javidi, “Sequential measurement-dependent noisy search, ” in IEEE Information Theory W orkshop (ITW) , Sept. 2016. [Online]. A vailable: http://dx.doi.org/10.1109/ITW .2016.7606828 [3] Y . Kaspi, O. Shayevitz, and T . Javidi, “Searching with measurement dependent noise, ” CoRR , vol. abs/1611.08959, 2016. [Online]. A vailable: https://arxiv .org/abs/1611.08959 [4] A. Lalitha, N. Ronquillo, and T . Javidi, “Measurement dependent noisy search: The gaussian case, ” in Pr oceedings of the 2017 IEEE International Symposium on Information Theory (ISIT) , June 2017, pp. 3090–3094. [Online]. A vailable: http://dx.doi.org/10.1109/ISIT .2017.8007098 [5] M. Giordani, M. Mezzavilla, C. N. Barati, S. Rangan, and M. Zorzi, “Comparati ve analysis of initial access techniques in 5g mmwave cellular networks, ” in Proceedings of the 2016 Annual Confer ence on Information Science and Systems (CISS) , March 2016, pp. 268–273. [Online]. A vailable: http://dx.doi.org/10.1109/CISS.2016.7460513 [6] C. N. Barati, S. A. Hosseini, M. Mezzavilla, P . Amiri-Eliasi, S. Rangan, T . K orakis, S. S. Panwar , and M. Zorzi, “Directional initial access for millimeter wave cellular systems, ” in Proceedings of the 49th Asilomar Confer ence on Signals, Systems and Computers , Nov 2015, pp. 307–311. [Online]. A vailable: http://dx.doi.org/10.1109/A CSSC.2015.7421136 [7] O. Abari, H. Hassanieh, and D. Katabi, “Millimeter wave communications: From point-to-point links to agile network connections, ” in Proceedings of the 15th ACM W orkshop on Hot T opics in Networks , Nov ember 2016, pp. 169–175. [Online]. A vailable: http://dx.doi.org/10.1145/3005745.3005766 [8] Z. Quan, S.Cui, A. H. Sayed, and H. V . Poor , “Optimal Multiband Joint Detection for Spectrum Sensing in Cogniti ve Radio Networks, ” IEEE T ransactions Signal Pr ocess , vol. 57, no. 3, pp. 1128–1140, March 2009. [Online]. A vailable: http://dx.doi.org/10.1109/TSP .2008.2008540 [9] Y . Feng and X. W ang, “Adaptiv e Multiband Spectrum Sensing, ” IEEE W ireless Communications Letters , vol. 1, no. 2, pp. 121–124, April 2012. [Online]. A vailable: http://dx.doi.org/10.1109/WCL.2012.022012.110230 [10] A. T ajer , R. Castro, and X. W ang, “Adapti ve Spectrum Sensing for Agile Cognitiv e Radios, ” in Pr oceedings of the 2010 IEEE Conference on Acoustics Speec h and Signal Processing (ICASSP) , March 2010. [Online]. A vailable: http://dx.doi.org/10.1109/ICASSP .2010.5496137 [11] M. L. Malloy and R. D. Nowak, “Near-optimal adaptive compressed sensing, ” IEEE T ransactions on Information Theory , vol. 60, no. 7, pp. 4001–4012, May 2014. [Online]. A vailable: http://dx.doi.org/10.1109/TIT .2014.2321552 [12] Y . Jin, Y . Kim, and B. Rao, “Limits on support recovery of sparse signals via multiple-access communication techniques, ” IEEE T ransactions on Information Theory , vol. 57, no. 12, pp. 7877–7892, December 2011. [Online]. A vailable: http://dx.doi.org/10.1109/TIT .2011.2170116 December 19, 2017 DRAFT 29 [13] J. T reichler , M. Davenport, and R. Baraniuk, “ Application of compressive sensing to the design of wideband signal acquisition receivers, ” in Pr oceedings of the 6th US/Australia Joint W ork. Defense Applications of Signal Pr ocessing (D ASP) , September 2009, pp. 1–10. [Online]. A vailable: http://mdav .ece.gatech.edu/publications/tdb- dasp- 2009.pdf [14] A. Sharma and C. Murthy , “Group testing-based spectrum hole search for cognitiv e radios, ” IEEE T ransactions on V ehicular T echnology , vol. 63, no. 8, pp. 3794–3805, October 2014. [Online]. A vailable: http://dx.doi.org/10.1109/TVT .2014.2305978 [15] T . M. Cover and J. A. Thomas, Elements of information theory . John W iley & Sons, Inc., 2006. [16] N. Ronquillo and T . Javidi, “Multi-band Noisy Spectrum Sensing with Codebooks, ” in Pr oceedings of the 50th Asilomar Conference on Signals, Systems, and Computers , November 2016, pp. 1687–1691. [Online]. A vailable: http://dx.doi.org/10.1109/A CSSC.2016.7869669 [17] N. Bshouty , “Optimal algorithms for the coin weighing problem with a spring scale, ” in Proceedings of the 22nd Confer ence on Learning Theory (COLT) , June 2009, pp. 1–10. [Online]. A vailable: http://www .cs.mcgill.ca/ ∼ colt2009/papers/004.pdf [18] S. C. Chang and E. W eldon, “Coding for t-user multiple-access channels, ” IEEE T ransactions on Information Theory , vol. 25, no. 6, pp. 684–691, November 1979. [Online]. A vailable: http://dx.doi.org/10.1109/TIT .1979.1056109 [19] M. Naghshvar and T . Javidi, “Optimal reliability over a DMC with feedback via deterministic sequential coding, ” in Pr oceedings of the 2012 IEEE International Symposium on Information Theory and its Applications (ISIT A) , Oct 2012, pp. 51–55. [20] ——, “Extrinsic Jensen–Shannon Div ergence: Applications to V ariable-Length Coding, ” in IEEE T ransactions on Information Theory , July 2012, pp. 2191–2195. [Online]. A vailable: http://dx.doi.org/10.1109/ISIT .2012.6283840 December 19, 2017 DRAFT
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment