Preventing wireless deauthentication attacks over 802.11 Networks
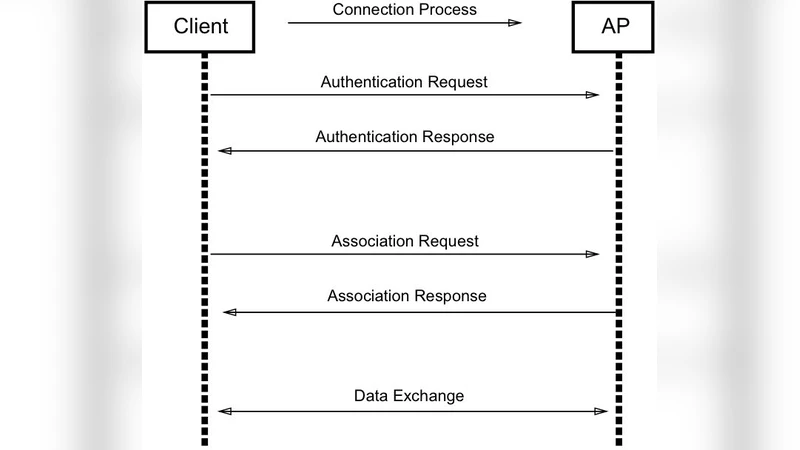
The objective of this paper is to investigate a special Denial of Service (DoS) attack against 802.11 wireless networks. This attack is known as the Deauthentication / Disassociation attack which is launched against 802.11-based wireless networks. When a client needs to disconnect from the wireless access point, it sends special frames known as deauthentication or disassociation frames. Due to being encrypted, these frames do not require an authenticated user. Hence, an attacker can craft these frames and send them to the access point in such a way that the access point assumes the frames to be coming from the client and not the attacker. In this paper, an efficient solution is proposed to prevent deauthentication attack by using a session management system used to then verify deauthentication frames.
💡 Research Summary
The paper addresses a fundamental weakness in IEEE 802.11 wireless networks: management frames used for deauthentication and disassociation are transmitted without encryption or authentication, allowing an attacker to spoof them and launch denial‑of‑service attacks. After reviewing existing counter‑measures—such as sequence‑number based detection, one‑bit authentication, R‑ARP, and cryptographic extensions—the authors propose a lightweight, backward‑compatible protocol that relies on universally unique identifiers (UUID v4) and the SHA‑512 hash function.
During the association phase, the client generates a random UUID (≈122 bits of entropy) and hashes it with SHA‑512. The resulting hash is placed in the Association Request frame. The access point (AP) checks whether this hash already exists in its memory; if not, the request is rejected as a replay. If the hash is new, the AP generates its own UUID, hashes it, and returns the hash in the Association Response. Both sides store the original UUIDs and the corresponding hashes.
When either side wishes to terminate the connection, it sends the original UUID inside the deauthentication frame. The receiver recomputes the SHA‑512 hash and compares it with the stored value. A match authorizes the deauthentication and causes both the token and its hash to be deleted; a mismatch results in the frame being ignored. Because the UUID space contains roughly 5.3 × 10³⁶ possible values, brute‑forcing a token is computationally infeasible.
The authors implemented the scheme on two low‑cost platforms: an ESP8266 Wi‑Fi chip (80 MHz, 64 KiB instruction RAM) and a Raspberry Pi 3 (1.2 GHz, 1 GB RAM). Micro‑benchmarks showed that generating a UUID takes about 0.05–0.08 seconds, while SHA‑512 hashing takes about 0.11–0.12 seconds, yielding a total overhead of roughly 0.18–0.20 seconds per association. These results demonstrate that the protocol can be deployed on resource‑constrained IoT devices without noticeable latency.
The paper also maps the proposed verification process onto all standard deauthentication reason codes, illustrating how legitimate frames are accepted and spoofed frames are rejected for each case.
In conclusion, the UUID‑SHA‑512 approach offers a simple, firmware‑upgradeable defense against deauthentication attacks that does not require new cryptographic primitives in legacy hardware. However, the authors acknowledge several practical concerns: memory consumption for storing tokens, potential denial‑of‑service via massive bogus association requests, the fact that tokens are transmitted in clear text (making capture and replay possible), and challenges in multi‑AP or roaming scenarios. Future work is suggested to encrypt token exchanges, integrate one‑time session keys, and address scalability in dense deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment