A Performance and Resource Consumption Assessment of Secure Multiparty Computation
In recent years, secure multiparty computation (SMC) advanced from a theoretical technique to a practically applicable technology. Several frameworks were proposed of which some are still actively developed. We perform a first comprehensive study of performance characteristics of SMC protocols using a promising implementation based on secret sharing, a common and state-of-the-art foundation. Therefor, we analyze its scalability with respect to environmental parameters as the number of peers, network properties – namely transmission rate, packet loss, network latency – and parallelization of computations as parameters and execution time, CPU cycles, memory consumption and amount of transmitted data as variables. Our insights on the resource consumption show that such a solution is practically applicable in intranet environments and – with limitations – in Internet settings.
💡 Research Summary
**
This paper presents a comprehensive performance and resource‑consumption evaluation of a secret‑sharing based Secure Multiparty Computation (SMC) framework, focusing on the open‑source system FRESCO. The authors first review existing SMC platforms (Sharemind, SPDZ‑2, and FRESCO) and select FRESCO because it supports an arbitrary number of parties, is actively maintained, and allows protocol substitution. Using the classic BGW round‑based model as a theoretical baseline, they identify that each computation round consists of local processing followed by a communication phase where every participant sends a share to every other participant, leading to O(n²) message traffic per round.
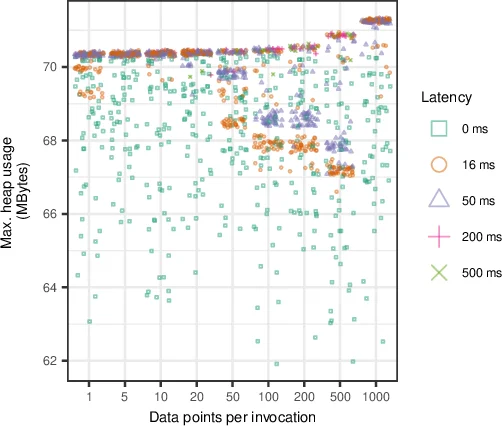
The experimental methodology varies five key environmental parameters: number of participants (3–15), network bandwidth (1 Mbps–100 Mbps), latency (10 ms–200 ms), packet‑loss rate (0 %–10 %), and the degree of parallelisation of independent computation sessions. For each configuration the authors measure total execution time, CPU cycles, heap memory usage, and total bytes transmitted.
Results show that execution time grows super‑linearly with the number of parties because of the quadratic increase in communication volume. Bandwidth below 10 Mbps or latency above 100 ms becomes the dominant bottleneck, dramatically inflating round‑trip delays. Packet loss up to 5 % has only a modest impact, but higher loss triggers retransmissions that add extra rounds and severely degrade performance. Memory consumption scales linearly with the number of parties, while CPU usage is dominated by communication handling rather than local arithmetic.
A second set of experiments investigates parallelising multiple independent SMC sessions. By splitting a workload into five concurrent sessions, the overall wall‑clock time drops to roughly one‑fifth of the sequential case, confirming that the cost of each round is bounded by the longest peer‑to‑peer link and can be amortised across parallel sessions.
The authors also compare SMC to a Trusted Third Party (TTP) baseline, where only two network round‑trips (input upload and result download) are required. In a well‑provisioned intranet, SMC incurs only a 2–3× latency penalty relative to TTP, whereas in typical Internet conditions the penalty exceeds an order of magnitude.
In conclusion, the study demonstrates that secret‑sharing based SMC is practically viable in low‑latency, high‑bandwidth intranet environments and can support dozens of participants with acceptable overhead. However, in wide‑area Internet settings the communication overhead limits real‑time applicability. The paper suggests future work on reducing round counts, employing compression and error‑correction, and exploring hybrid architectures that combine SMC with cloud‑based relays to mitigate network constraints.
Comments & Academic Discussion
Loading comments...
Leave a Comment