Quantum Differential Cryptanalysis
In this paper, we propose a quantum version of the differential cryptanalysis which offers a quadratic speedup over the existing classical one and show the quantum circuit implementing it. The quantum differential cryptanalysis is based on the quantum minimum/maximum-finding algorithm, where the values to be compared and filtered are obtained by calling the quantum counting algorithm. Any cipher which is vulnerable to the classical differential cryptanalysis based on counting procedures can be cracked more quickly under this quantum differential attack.
💡 Research Summary
The paper introduces a quantum version of differential cryptanalysis that achieves a quadratic speedup over its classical counterpart by leveraging quantum counting and quantum minimum/maximum‑finding algorithms. Classical differential cryptanalysis works in two stages: for each candidate sub‑key, count the number of “right pairs” (plaintext‑ciphertext pairs that satisfy a predefined differential characteristic) and then select the sub‑key with the largest count. This process is computationally intensive because it requires O(K·N) operations (K candidate sub‑keys, N chosen plaintext‑ciphertext pairs) or, with large memory, O(K+N) but still demands traversing all N pairs for each candidate.
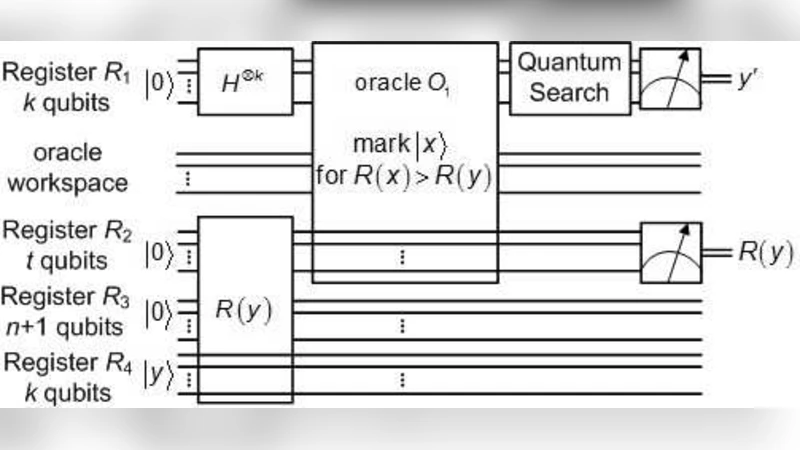
The authors propose to replace both stages with quantum procedures. They construct a quantum circuit that uses four registers: R1 holds a uniform superposition over all K candidate sub‑keys, R2 and R3 are ancilla registers for quantum counting, and R4 stores a threshold sub‑key y. The quantum counting sub‑routine is a modified version of the Brassard‑Høyer‑Mosca‑Tapp algorithm. For a given candidate x, an oracle O₂ marks those indices j (representing the N plaintext‑ciphertext pairs) that form a right pair with x by applying a phase flip. After applying the Grover iteration G a suitable number of times and an inverse quantum Fourier transform, the algorithm extracts an estimate R(x) of the number of right pairs for x. This estimation requires only O(√N) quantum operations regardless of K, because the superposition over all candidates allows simultaneous counting.
To find the sub‑key with the maximal count, the authors adapt the Durr‑Høyer quantum minimum/maximum‑finding algorithm. An oracle O₁ compares the current estimate R(x) with the estimate for the current threshold y and flips a flag qubit if R(x) > R(y). A Grover search then amplifies the marked states, yielding a new candidate y′ with a larger count. The process repeats, updating y each time, until the probability that y is the true maximum exceeds a chosen confidence level. The quantum maximum‑finding step costs O(√K) operations.
Complexity analysis shows that the total runtime is O(√K + √N). In terms of space, the classical part still needs to store the N chosen plaintext‑ciphertext pairs (O(N) memory), while the quantum registers require only O(log K + log N) qubits (approximately 2k + n + t + 1 qubits, with t ≈ ⌈n/2⌉+4). The success probability can be made arbitrarily high by selecting appropriate parameters for the counting accuracy ε and the constant c governing the number of Grover iterations; the authors demonstrate a 90 % success rate under realistic settings (e.g., ε = 0.1, m = ⌈n/2⌉+1).
The paper also discusses practical considerations. Implementing oracle O₂ requires a one‑round partial encryption of the candidate sub‑key and a comparison with the expected output difference defined by the characteristic; thus the complexity of the oracle depends on the underlying block cipher’s round function. Moreover, the attack assumes that the adversary can obtain N plaintext‑ciphertext pairs with a fixed input difference, which may be feasible only in chosen‑plaintext scenarios. Finally, the depth of the quantum circuit (proportional to k + t + n) poses challenges for near‑term noisy intermediate‑scale quantum (NISQ) devices, where decoherence and gate errors could degrade performance.
In conclusion, the authors present the first concrete quantum algorithm that accelerates differential cryptanalysis. By exploiting quantum parallelism, a single quantum counting procedure yields estimates for all candidate sub‑keys, and a quantum maximum‑finding routine identifies the correct sub‑key with √K speedup. Compared with classical approaches that may require O(K·N) time or large memory to avoid that cost, the quantum method offers a theoretically significant advantage. Future work is suggested in optimizing the oracle for specific ciphers, implementing the protocol on realistic quantum hardware, and extending the quantum‑enhanced methodology to other statistical cryptanalysis techniques such as linear cryptanalysis.
Comments & Academic Discussion
Loading comments...
Leave a Comment