Cooperative Authentication in Underwater Acoustic Sensor Networks
With the growing use of underwater acoustic communications (UWAC) for both industrial and military operations, there is a need to ensure communication security. A particular challenge is represented by underwater acoustic networks (UWANs), which are …
Authors: Roee Diamant, Paolo Casari, Stefano Tomasin
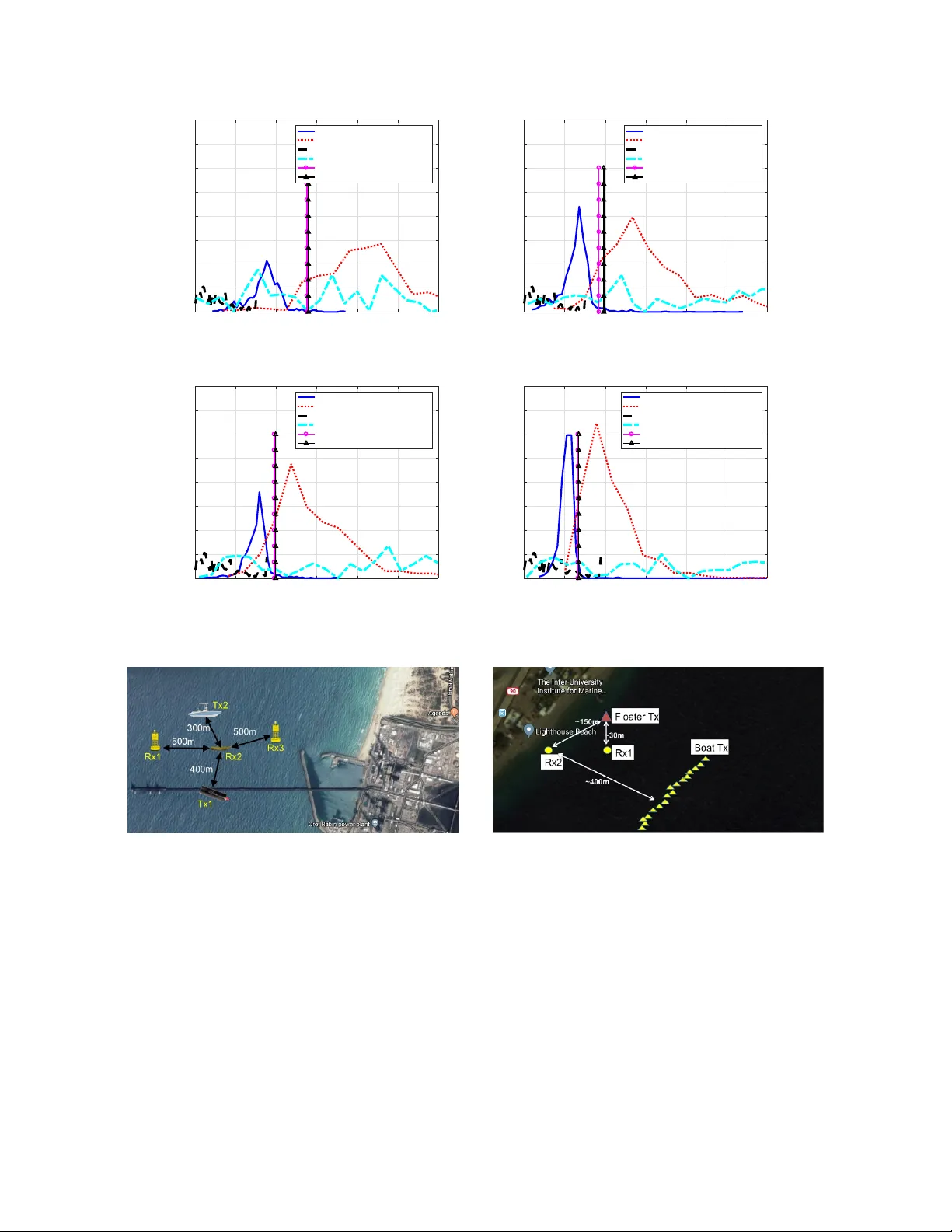
1 Cooperati v e Authentication in Underwater Acoustic Sensor Networks Roee Diamant, Senior Member , IEEE , Paolo Casari, Senior Member , IEEE , Stefano T omasin, Senior Member , IEEE Abstract —With the growing use of underwater acoustic com- munications (UW A C) for both industrial and military operations, there is a need to ensure communication security . A particu- lar challenge is repr esented by underwater acoustic networks (UW ANs), which are often left unattended over long periods of time. Currently , due to physical and performance limitations, UW A C packets rarely include encryption, leaving the UW AN exposed to external attacks faking legitimate messages. In this paper , we propose a new algorithm for message authentication in a UW AN setting. W e begin by observing that, due to the strong spatial dependency of the underwater acoustic channel, an attacker can attempt to mimic the channel associated with the legitimate transmitter only f or a small set of r eceivers, typically just f or a single one. T aking this into account, our scheme relies on trusted nodes that independently help a sink node in the authentication process. For each incoming packet, the sink fuses beliefs evaluated by the trusted nodes to reach an authentication decision. These beliefs are based on estimated statistical channel parameters, chosen to be the most sensiti ve to the transmitter - recei ver displacement. Our simulation results show accurate identification of an attacker’ s packet. W e also report results from a sea experiment demonstrating the effecti veness of our appr oach. Index T erms —Underwater acoustic communication, Underwa- ter acoustic communication networks, channel-based security , cooperative security , authentication, UW A C, sea experiment. I . I N T R O D U C T I O N Underwater acoustic networks (UW ANs) are increasingly being perceiv ed as a cost-effecti ve means of ocean exploration and monitoring. While carrying out these tasks, howe ver , UW ANs are left unattended ov er long periods of time, and may become vulnerable to external attacks. The recent intro- duction of standards for underw ater acoustic communications (UW A C) [1] makes these attacks more probable. For this reason, the in vestigation of security mechanisms tailored to the specific UW AC characteristics is currently gaining mo- mentum. In particular , it has been observed that only in very specific cases the same security techniques dev eloped for Manuscript recei ved February 21, 2018; re vised August 14, 2018; accepted December 10, 2018. The associate editor coordinating the revie w of this paper and approving it for publication was S. Y ang. ( Corresponding author: Roee Diamant.) . This research has been sponsored in part by the N A TO Science for Peace and Security Programme under grant G5293. R. Diamant is with the Department of Marine T echnologies, Univ ersity of Haifa, Haifa 3498838, Israel (e-mail: roeed@univ .haifa.ac.il). P . Casari is with the IMDEA Networks Institute, 28918 Madrid, Spain (e- mail: paolo.casari@imdea.org). S. T omasin is with the Department of Information Engineering, Univ ersity of Padov a, 35122 Padov a, Italy (e-mail: tomasin@dei.unipd.it). Color versions of one or more of the figures in this paper are available online at http://ieeexplore.ieee.org. Digital Object Identifier 10.1109/TWC.2018.2886896 terrestrial wireless radio networks can be directly applicable in underwater scenarios. F or example, this is the case of well-known elliptic-curve cryptography schemes, which hav e been e v aluated for underwater applications in [2]. In most other cases, a systematic re-thinking of security schemes and strategies has to be carried out [3]. The focus of this paper is the authentication of a packet receiv ed by a sink node with the support of trusted nodes. Authentication mechanisms allo w a node to prov e that it is a legitimate member of a network, so that controller nodes or sinks can trust the data sent by the node. This step is of great importance, especially in underwater monitoring tasks and tactical scenarios. The sink’ s objecti ve is to determine whether the packet is coming from either the le gitimate node or the attacker . Conv ersely , the attacker’ s objectiv e is to let its o wn packet be recognized as authentic by the sink. The authentication process is based on the acoustic communication channel features, rather than on cryptographic techniques. T rusted nodes cooperate to the authentication process without knowing its outcome: each trusted node independently sends authentication data to the sink, which does not broadcast the authenticity decision, in order to increase the system’ s spectral efficienc y and avoid additional security risks. W e remark that the trusted nodes do not need to exchange data in order to complete the authentication process. Our approach is based on channel features that mildly vary ov er time and space, slo w enough such that their distribution can be approximated as constant during the authentication process. W e choose these features by examining a data set from more than a hundred sea experiments, and by showing that the distributions of dif ferent channel features –such as the number of channel taps, the relative delay spread, and the receiv ed po wer lev el– are sufficiently stable over time and sufficiently div erse for different transmitter -receiv er pairs. This makes such features amenable for authentication purposes. For incoming packets receiv ed by different trusted nodes, we lev erage this div ersity by systematically measuring the distribution of the e valuated channel’ s characteristics, and by calculating beliefs that are then transmitted to and processed by a sink node. The outcome is a measure to discriminate between packets sent by a le gitimate transmitter and packets receiv ed from an attacker . W e hav e tested the performance of our authentication method both in simulations based on established acoustic propagation models and in two sea ex- periments. A comparison with existing approaches and a theoretical bound are also provided. The results sho w a very good trade-of f between the probability of detecting an attack 2 and the probability of a f alse alarm. In the following, we survey the state of the art in UW AC authentication (Section II), and describe our system model, in- cluding the features we use for authentication (Section III). W e discuss our authentication method (Section IV) and ev aluate it through simulations (Section V) and two sea experiments (Section VI), before drawing conclusions in Section VII. I I . R E L A T E D W O R K Comprehensiv e revie ws of security approaches for underwa- ter networks are provided in [3], [4], which discuss approaches for anti-jamming, priv acy securing, and covertness. As this paper focuses on authentication, in this section we consider only authentication approaches. In [2], an end-to-end authen- tication scheme has been proposed using the elliptic curv e digital signature algorithm (ECDSA). Secret keys can also be used for authentication, and in this respect a robust secret key generation scheme is proposed in [5]. The survey in [6] cov ers several forms of cooperation and their application to underwater networks. Game theory is advocated as a means to foster cooperation among the nodes. In a security context, this concept is applied to motiv ate nodes to beha ve cooperativ ely , and to impro ve the effecti veness of end-to-end authentication schemes, which are seen as an important aspect of future underwater network dev elopments [7]. User authentication has been addressed by the so-called physical layer security by exploiting the channel coherence, i.e., messages going from the same source to the same des- tination are subject to the same channel, whereas a message coming from a fake source located in a different position will be subject to a different channel, which can be estimated at the destination (see [8] for a survey). V arious channel features hav e been considered in this context. For example, in wireless radio systems, the power le vel was considered in [9]–[11], the impulse response of a wideband channel in [12]–[16], the frequency response of an orthogonal frequency division multiplexing (OFDM) transmission in [17], the power spectral densities in [18], and the time series of the received signal strength in a data/ackno wledgment packet exchange in [19]. When multiple nodes are available, the authentication pro- cess can be further enhanced. In [20], a distributed authen- tication in wireless networks was considered where multiple sensors report their correlated measurements to a fusion center , which makes the ultimate authentication decision. In [21], a similar solution using compressed sensing is studied. All these works typically assume a giv en channel statistic, which is used to formulate the authentication hypothesis testing problem. In [22], this assumption is removed by using logistic regression techniques, which is applied to the received signal power . Different from the literature presented so far , our authenti- cation approach relies on the estimation of the distribution of selected underwater channel features instead of their instanta- neous realizations, as opposed to, e.g., [9]–[19]. Unlike [5], we do not explicitly generate keys starting from channel features; we do not base our scheme on cryptography (unlike [2]); and in order to save ener gy we do not require the transmission of structured jamming signals, unlike some approaches in [3]. Moreov er , most of the existing literature on physical layer authentication is based on the comparison of a reference channel with the estimated channel, in a mean square error (MSE) sense. This approach is optimal when the estimate is only subject to Gaussian noise but is not adequate in a UW A C context, where instantaneous channel variations and noise requires a more elaborate description of the PDF of the channel estimate (and its variations with respect to the reference channel). Therefore, we deriv e the distribution of the channel features directly from packets receiv ed by trusted nodes, and fuse their beliefs at a sink to make a decision on the authenticity of the message. Our approach proves valid both in simulations, where we realistically model the underwater acoustic channels via ray tracing [23], and in a sea experiment, proving that the assumptions behind our scheme are v alid in practice. I I I . S Y S T E M M O D E L W e consider an underwater acoustic network with a sink node assisted by N trusted nodes, one legitimate transmitter , and one attacker . The extension to deployments consisting of multiple attackers is straightforward. T ransmissions are orga- nized in packets of T symbols. W e assume that the first packet always comes from the legitimate node. Then, the following packets can arri ve from the legitimate transmitter or from the attacker . Each packet is labeled with a unique identification (ID) number that pre vents replay attacks. Moreo ver , the trusted nodes are assumed to be roughly time-synchronized such that the times at which the trusted nodes receive a packet with a specific ID (according to their own clock) are within a reasonable time span of up to one maximum propagation delay in the network. This prev ents the retransmission of the same packet by the attacker with beamforming/channel modification techniques aimed at bypassing the authentication procedure. A. Assumptions about the channel features In the UW AC channel, the transmitted signal is reflected both by the sea boundaries and by volume scatterers, such as plankton and sediments. Moreover , due to the continual motion of the wav es, signals are affected by a Doppler shift varying up to tens of Hz [24]. The channel is modeled as a tapped delay line, whose delay spread is in the order of hundreds of milliseconds [25], with significant variations for different transmitter-receiv er locations. The po wer attenuation of the UW A C channel is governed by the propagation loss and the absorption loss. The propagation loss is a function of the channel structure and entails a highly non-linear pro- cess [26]. Moreov er , the sound propagation between layers, characterized by different sound speed (mostly due to water pressure or temperature changes), leads to both refraction and additional attenuation. The absorption loss is a function of the carrier frequency , and is mainly affected by water temperature, salinity , and pressure [26]. Since propagation and absorption losses cannot be separated at the recei ver , we consider the ov erall attenuation lev el. Our proposed authentication method relies on features ex- tracted from the underwater acoustic channel, such as the 3 number of channel taps, the channel’ s delay spread, and the receiv ed power lev el. These features are typically location- dependent, such that the channel realization observed by a trusted node for packets receiv ed from the legitimate node is different than that observed by an attacker located far from the legitimate node. Even if underw ater channels are time-varying, we assume that the feature statistics do not change, as long as the locations of the transmitter and receiver remain relatively stable. In Section III-C, we will validate this assumption based on more than 100 sea experiments conducted at various times and in div erse en vironments over a four-year period. Let I be the set of channel features used for authentication, and x i,n ( t ) , i ∈ I , be the estimated channel feature extracted at time t ∈ T φ at trusted node n ∈ [1 , N ] , where T φ is the set of time epochs when a feature x i,n ( t ) has been estimated for packet φ . Each random variable x i,n ( t ) is modeled as a generalized Gaussian (GG), whose statistics is determined by the three parameters ω i,n = ( µ i,n , σ i,n , β i,n ) , (1) where µ i,n = E [ x i,n ( t )] is the mean, E [ x 2 i,n ( t ) − µ 2 i,n ] = σ 2 i,n Γ(3 /β i,n ) Γ(1 /β i,n ) is the v ariance, and β i,n is a shape parameter . The GG distribution is chosen to provide flexibility . In particular , it models the Laplace distrib ution ( β i,n = 1 ), the Gaussian distri- bution ( β i,n = 2 ) and the uniform distrib ution ( β i,n → ∞ ). W e will provide more details on how to obtain these parameters for authentication purposes both in Section IV -B and in the Appendix. Then the conditional probability density function (PDF) of x i,n ( t ) (for a specific set of parameters ω i,n ) is [27] p x | ω ( a | ω i,n ) = β i,n 2 σ i,n Γ 1 β i,n e − | a − µ i,n | σ i,n β i,n . (2) As anticipated above, we assume that the feature statistics ω i,n are static during the authentication process, i.e., they do not change over time, or across different packets for fixed nominal locations of the transmitter and receiv er . The validity of this assumption is confirmed by more than one hundred sea experiments, as described in Section III-B. W e also carried out two sea experiments (Section VI) where we successfully tested the authentication scheme. This further confirms that the stability assumption is appropriate in practice. B. F eatur es for physical layer authentication The ke y features we use to determine the integrity of an underwater acoustic transmission are the number of channel taps, the tap power , the coherence time, the root mean square (RMS) of the relativ e delay experienced by the channel taps with respect to the first tap, and a smoothed version of the received power . The ef fecti veness of the authentication features is provided by the fact that they are relativ ely stable ov er time, so their distribution can be approximated as static, but v arying considerably in space, so that an attacker located in a dif ferent position can be distinguished from the authentic transmitter . In this section, we discuss the rationale behind our choice of channel features. Consider a measured channel power -delay profile H n ( t, τ ) for time t , delay τ , and node n . Define the relev ant tap set S n ( t ) = { τ : | H n ( t, τ ) | > T h } , where T h is a threshold chosen to achieve a probability of false alarm of 10 − 4 in the identification of relev ant channel taps at the output of a nor- malized matched filter , according to the analysis in [28]. The following channel features are considered for authentication by trusted node n : 1—Number of channel taps. The estimated number of significant taps is x 1 ,n ( t ) = |S n ( t ) | . (3) While the number of channel taps could be limited or location- independent in specific scenarios (e.g., deep water), there exists a broad class of shallow-water scenarios where the number of taps can vary widely , depending not only on the location of the transmitter and receiver , but also on their depth. For this reason, we consider the number of taps a relev ant authentication feature. 2—A verage tap power . From the power -delay profile H n ( t, τ ) , we measure this metric as x 2 ,n ( t ) = 1 |S n ( t ) | X τ ∈S n ( t ) | H n ( t, τ ) | . (4) 3—Coherence Time. This metric con ve ys the amount of time when the channel can be approximated as stationary . Formally , we define x 3 ,n ( t ) = argmax(∆) s.t. NC H n ( t, τ ) , H n ( t − ∆ , τ ) > 0 . 9 , (5) where NC ( α, β ) is the normalized correlation between α and β . 4—Relative RMS delay spread. Call τ 0 = min { τ : τ ∈ S n ( t ) } the delay of the first tap. The estimate of the relativ e RMS delay spread is computed as x 4 ,n ( t ) = 1 |S n ( t ) | − 1 X τ ∈S n ( t ) ,τ 6 = τ 0 ( τ − τ 0 ) 2 1 / 2 . (6) 5—A verage path delay . The av erage path arriv al delay , relativ e to the arriv al of the first tap, is x 5 ,n ( t ) = 1 |S n ( t ) | − 1 X τ ∈S n ( t ) ,τ 6 = τ 0 ( τ − τ 0 ) . (7) 6—Smoothed received power . Since we expect the receiv ed power to change, we consider the difference between the current po wer measurement and a smoothed version of the previous measurements. Formally , let q n,t be the po wer of a symbol receiv ed at time t by node n , call t 0 the time when the previous feature measurement was performed, and let 0 ≤ α ≤ 1 be a user-defined parameter . The smoothed receiv ed power is recursively defined as x 6 ,n ( t ) = α q n,t + (1 − α ) x 6 ,n ( t 0 ) . (8) Other channel features can also be used for authentication. For example, the Doppler shift would seem a good candidate, since it inherently changes for different transmitter/recei ver locations. Howe ver , relying on the Doppler shift for authen- tication requires the legitimate node to notify others of its mobility plans. In addition, the attacker can easily impress a 4 # of taps Tap power Coherence time Delay spread Path delay Received power 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 c n Fig. 1. Spatial and time dependency of some acoustic channel features: the red line on each histogram element conve ys the 10th and the 90th percentile for each metric. giv en Doppler shift on its packets by resampling its transmitted signals. These aspects make Doppler shift a comparativ ely less robust channel feature, hence in this work we do not consider it for authentication. Similarly , the time of arriv al of a packet transmission would also be a good channel feature for authentication purposes. Howe ver , the trusted node would need to cooperate with the transmitter in order to determine the transmission time: this makes the time of arriv al vulnerable to attacks, and therefore we av oid using it. C. Statistical analysis of the channel featur es In order to assess the sensitivity of the channel features to the transmitter and receiver locations, we performed a statistical analysis using time-based channel impulse responses recorded during more than 100 sea experiments at different locations, water depths, and times of the year . All experiments were performed along the Israeli coast between 2001 and 2005, and included the use of various acoustic equipment at different carrier frequencies. The channels were recorded for at least 10 s with a resolution of 50 ms. The database format is reported in [29]. From the database in [29], we selected the experiments that included more than two nodes, so that we could compare the differences between the considered channel features in space at the same time. T o capture fluctuations due to environmental changes on a small time scale, this comparison is performed for the time series rather than for av erage values. As the re- ceiv ers used similar hydrophones for reception, in this section we drop the node index n from the notation. For the same transmitter and a pair of recei vers i and j within the set of receiv er pairs R in the same sea experiment, we ev aluate the difference between the time series of the estimated channel features x j and x i with elements x j ( t ) and x i ( t ) , respectiv ely , obtained at the same time instances t = 0 , . . . , T N − 1 . The difference between the two time series provides a measure of the spatial dependency of the estimated feature. Y et, to be used as authentication metrics, -5 0 5 10 15 20 25 0 0.05 0.1 0.15 0.2 Estimated: =10.27, = 4.28, = 2 Measured (a) Receiv er 1 -0.5 0 0.5 1 1.5 2 2.5 0 0.05 0.1 0.15 0.2 0.25 Estimated: =0.94, = 0.78, = 4 Measured (b) Receiv er 2 Fig. 2. Empirical and theoretical pdf of the number of channel taps from one of our sea experiments. the chosen features must also not change significantly during the acquisition time. As a metric for the comparison, we used ρ c = 1 |R| X ( i,j ) ∈R ,i 6 = j P T N − 1 t =0 x j ( t ) x i ( t ) q P T N − 1 t =0 x 2 j ( t ) P T N − 1 t =0 x 2 i ( t ) · × 1 − ρ diff ( x j ) 1 − ρ diff ( x i ) , (9) where | · | is the cardinality of · , and ρ diff ( x j ) is Jain’ s fairness index [30] ρ diff ( x j ) = T N − 1 X t =0 x j ( t ) 2 T N T N − 1 X t =0 x 2 j ( t ) − 1 , (10) used to estimate the v ariation of the considered channel feature ov er time. The value of ρ c decreases if a giv en metric varies as a function of a node’ s location, but remains otherwise stable ov er time. Hence, for authentication, those features yielding a small ρ c are preferred. Fig. 1 sho ws the average ρ c for the dif ferent channel features considered in Section III-B. All features were measured by estimating the channel impulse response ov er time (see full description in [29]), and by processing it to extract the feature values. While there is a considerable difference between features estimated at dif ferent locations, we observe that the most significant differences are obtained for the number of 5 taps and the relativ e delay spread, and that such differences hold in a variety of experiments, as can be inferred from their small confidence intervals. Finally , the results confirm that the flexibility offered by the generalized Gaussian distribution in (2) is indeed required in practical settings. Figs. 2a and 2b show the empirical and theoretical PDFs of the number of taps, estimated in our sea experiment, as observed by two receiv ers. W e observe that the shape of the distributions is different for each receiv er . This demonstrates why obtaining a specific distribution for the channel is challenging. Still, due to its fle xibility , our estimated GG distribution (2) is able to capture the empirical PDF quit well. D. Assumptions on the Attacker Model W e assume that the attacker is a single malicious node, able to perform any kind of signal processing on its transmitted packet. In particular, it has unlimited transmission po wer capabilities, it can filter the transmitted signal in order to let the trusted node estimate a different channel, and it can superimpose signals onto the message. W e also assume that the attacker knows: 1) the position of both the trusted nodes and the legitimate node; 2) the training signals used for channel estimation by the trusted nodes; 3) the instantaneous acoustic channel realization observed ov er the link from itself to all of the trusted nodes plus the legitimate node; 4) the statistical correlation of the abov e channels with the channel realizations observed over the links from the legitimate node to each of the trusted nodes. I V . A U T H E N T I C A T I O N M E T H O D In this section, we outline the details of our authentication method. Our scheme aims at establishing the authenticity of a receiv ed packet. This is a hypothesis-testing problem, where for a packet φ the two hypotheses are • H 0 : packet φ is authentic, and • H 1 : packet φ is not authentic. By false alarm (F A) we mean the case where an authentic packet is classified as not authentic; by missed detection (MD) the case where a non-authentic packet is classified as authentic. For a giv en testing strategy , the F A and MD probabilities are the probabilities that a F A or a MD occur . Our authentication is based on the set of features X ( φ ) = { x i,n ( t ) , t ∈ T φ , ∀ i, n } associated with packet φ . The deci- sion on X ( φ ) is made using alternativ e distributions with parameters estimated from previously recei ved packets. Let p X |H ( X ( φ ) |H m ) be the joint PDF of X ( φ ) conditional upon hypothesis H m . Then, for packet φ , the optimal hypothesis testing strategy is obtained by using the log-likelihood ratio (LLR) [31] as decision index: Ψ φ = Ψ 0 φ − Ψ 1 φ , (11) where ( m = { 0 , 1 } ) Ψ m φ = log p X |H X ( φ ) |H m . (12) The decision procedure for the hypothesis testing problem therefore becomes b H = ( H 0 Ψ φ < λ , H 1 Ψ φ ≥ λ , (13) where λ is a threshold that trades off between the F A and MD probabilities. A. Distributed Authentication Our authentication method is distributed, as each trusted node pre-processes each receiv ed packet to reduce the amount of data exchanged with the sink node. In turn, the sink will determine the authenticity of each packet. 1 In the following, we deriv e both the data provided by the trusted nodes and the fusion procedure at the sink. W e assume that a set I of channel features has been prelim- inarily selected to be used for authentication purposes. In fact, the chosen set of features matches the characteristics of a gi ven en vironment, and is usually designed to extract the maximum div ersity from that en vironment. W e consider (2) as the PDF of the channel features used for authentication; howe ver , we do not know the parameters ω m i,n a priori. Instead, we estimate ω m i,n using all received packets up to packet φ , and we indicate this estimate as ˆ ω m i,n ( φ ) = ˆ µ i,n ( φ ) , ˆ σ i,n ( φ ) , ˆ β i,n ( φ ) . As analyzed in [33] and discussed in [34], we rely on the spatial di versity of the UW AC channel to assume that channel variations from the transmitter to each of the trusted nodes are independent. Under this assumption, we use the estimated parameters to compute the conditional probability ( m = { 0 , 1 } ) p X |H X ( φ ) |H m = Y i,n,τ ∈T φ p x | ω x i,n ( τ ) | ˆ ω m i,n ( φ ) , (14) where m = 0 and m = 1 denote the classification of legitimate and fake , respectively . The details about the estimate of the parameters ˆ ω m i,n ( φ ) are provided in the next subsections. Plugging (14) into (12), the LLR (11) is written as Ψ φ = X n R φ,n (15) where R φ,n = Ψ 0 φ,n − Ψ 1 φ,n , (16) Ψ m φ,n = X i, τ ∈T φ log ˆ β m i,n ( φ ) 2 ˆ σ m i,n ( φ )Γ 1 ˆ β m i,n ( φ ) × e − | x i,n ( τ ) − ˆ µ m i,n ( φ ) | ˆ σ m i,n ( φ ) ˆ β m i,n ( φ ) . (17) From (15)–(17), we observe that the computation of the LLR can be split among the N trusted nodes: each trusted node 1 W e remark that this requires both error control (to ensure reliable trans- mission from the trusted nodes to the sink) and medium access control (to regulate the access of the trusted nodes to the UW A C channel). Since the amount of information exchanged from the trusted nodes to the sink is small and limited to the value R φ,n in (16), the above controls can be implemented using reliable communication schemes [32]. 6 estimates the parameter set ˆ ω m i,n ( φ ) , computes the two LLRs for m = 0 , 1 , and forwards R φ,n to the sink. Then, at the sink, (15) is used to compute the packet LLR. A bound for the system’ s performance, in terms of the F A and MD probabilities P F A ( φ ) and P MD ( φ ) for a giv en attack strategy can be obtained by applying the data process- ing inequality [35]. By defining the Kullback-Leibler (KL) div ergence as D ( p X |H X ( φ ) |H 0 ) || p X |H ( X ( φ ) |H 1 ) = Z p X |H ( X |H 0 ) log p X |H ( X |H 0 ) p X |H ( X |H 1 ) d X , (18) the bound is f P MD ( φ ) ,P F A ( φ ) ≤ D p X |H ( X ( φ ) |H 0 ) || p X |H ( X ( φ ) |H 1 ) , (19) where f P MD ( φ ) , P F A ( φ ) = P MD ( φ ) log P MD ( φ ) 1 − P F A ( φ ) + 1 − P MD ( φ ) log 1 − P MD ( φ ) P F A ( φ ) . (20) Under the assumption of independent errors, the KL di ver - gence can be written as D p X |H ( X ( φ ) |H 0 ) || p X |H ( X ( φ ) |H 1 ) = |T φ | X i,n D p x | ω ( x i,n ( τ ) | ω 0 i,n ( φ )) || p x | ω ( x i,n ( τ ) | ω 1 i,n ( φ )) (21) The closed-form expression of the KL diver gence for two GG random v ariables is available [36] for either β 0 i,n ( φ ) = β 1 i,n ( φ ) = 2 , i.e., for Gaussian distributions as D p X |H ( X ( φ ) |H 0 ) || p X |H ( X ( φ ) |H 1 ) = |T φ | X i,n log σ 1 i,n ( φ ) σ 0 i,n ( φ ) − 1 2 + σ 0 i,n ( φ ) σ 1 i,n ( φ ) ! 2 + µ 1 i,n ( φ ) − µ 0 i,n ( φ ) 2 2 σ 1 i,n ( φ ) 2 (22) or for µ 0 i,n ( φ ) = µ 1 i,n ( φ ) = µ , a special case of the generalized Gamma distribution, where [37] D p X |H ( X ( φ ) |H 0 ) || p X |H ( X ( φ ) |H 1 ) = − 1 β 0 i,n ( φ ) + log β 0 i,n ( φ ) σ 1 i,n ( φ )Γ 1 β 1 i,n ( φ ) β 1 i,n ( φ ) σ 0 i,n ( φ )Γ 1 β 0 i,n ( φ ) + Γ β 1 i,n ( φ ) β 0 i,n ( φ ) Γ 1 β 0 i,n ( φ ) σ 0 i,n ( φ ) σ 1 i,n ( φ ) ! β 1 i,n ( φ ) . (23) The computation of the KL di ver gence for GG distribution with general parameters requires the numerical integration of (18). B. Estimation of the PDF P arameters at the T rusted Nodes In order to compute (15) and (16), each trusted node n must estimate the set of PDF parameters, ˆ ω m i,n ( φ ) , for the two hypotheses m = 0 and m = 1 . Note that the procedure to classify the packets as authentic or not authentic should not imply feedback from the sink to the trusted nodes, as this would increase the authentication overhead, would also have to be secured against, e.g., forging or jamming attacks on the feedback packet. For this reason, no consensus procedures can be implemented. Instead, here we do not employ any feedback, but rather propose that each trusted node estimates all parameters and associates them with the two hypotheses. P arameter Estimation — As the estimation criterion, we con- sider the maximum likelihood approach, wherein parameters are selected in order to maximize the probability of the observations. Given the parameters, we employ the mixture model P X i,n ( φ ) | ˆ ω 0 i,n ( φ ) , ˆ ω 1 i,n ( φ ) = Y t ∈T f 1 X m =0 k m i,n p x | ω x i,n ( t ) | ˆ ω m i,n ( φ ) , (24) where X i,n ( φ ) = { x i,n ( t ) , t ∈ T f , f ≤ φ } (i.e., we use all observ ations collected so far), and k m i,n is the prior on parameter i at node n about hypothesis m (which is also unknown and must be estimated). W e let each trusted node estimate the set θ m i,n = ( ω m i,n , k m i,n ) . Let us now define the set Θ i,n = { θ m i,n , m = 0 , 1 } and similarly the corresponding set of estimated parameters at packet φ as ˆ Θ i,n ( φ ) . Note that θ m i,n is not packet-dependent, in accordance with our assumption that the feature statistics for both the legitimate node and the attacker do not change significantly across different packets. Ho wev er, the estimate ˆ θ m i,n ( φ ) is updated after each packet. The estimated parame- ters ˆ Θ i,n ( φ ) maximize the likelihood of observing X i,n ( φ ) . T aking into account the fact that the observations x i,n ( t ) are independent for different t (even when belonging to the same packet), we have ˆ Θ i,n ( φ ) = arg max ¯ Θ=( ω m i,n ,k m i,n ) P ( X i,n ( φ ) | Θ i,n = ¯ Θ) . (25) W e find the solution of the maximization problem (25) via the expectation maximization (EM) algorithm [31], as detailed in the Appendix. P arameter Association — The EM algorithm provides the esti- mated parameter sets ˆ θ m i,n ( φ ) , for m = 0 and m = 1 . Howe ver , without further information about the expected values for each of the two classes m = { 0 , 1 } , the association of ˆ θ m i,n ( φ ) to hypothesis H 0 or H 1 is ambiguous. In other words, we do not know if m = 0 is actually associated with hypothesis H 0 or hypothesis H 1 . Therefore, when fusing all data at the sink, we must synchronize m across the trusted nodes to ensure that the same value of m refers to the same hypothesis for all the trusted nodes. According to our assumption that the first packet always originates from the legitimate transmitter , all trusted nodes assign hypothesis m = 0 to the first packet with index φ = 0 . Then, the labeling m is chosen by matching the 7 current estimated variables ˆ θ m i,n ( φ ) to the measurements from the first packet, X i,n (0) . Formally , we associate ˆ θ 0 i,n ( φ ) with hypothesis H 0 if P X i,n (0) | ˆ θ 0 i,n ( φ ) ≥ P X i,n 0) | ˆ θ 1 i,n ( φ ) , (26) and from (2), condition (26) becomes Y t ∈T 0 p x | ω x i,n ( t ) | ˆ ω 0 i,n ( φ ) ≥ Y t ∈T 0 p x | ω x i,n ( t ) | ˆ ω 1 i,n ( φ ) . (27) After this association procedure, for m = 0 , trusted node n calculates (17) and then the decision index R φ,n in (10), according to the ˆ θ m i,n ( φ ) tuples associated with hypotheses H 0 , and H 1 . C. Refined Data Fusion W e observe that in the above distributed procedure, two possible errors may occur: a) a hypothesis association error , and b) a parameter estimation error . The first error occurs when m is assigned different values for the same hypothesis by different nodes, i.e., when test (26) fails. The probability of occurrence of this error P e can not be obtained in closed form. Howe ver , when the number of samples goes to infinity (i.e., the products in (27) have a large number of terms) we can resort to the Chernoff-Stein lemma [38, Theorem 11.8.3], which states that the error probability goes exponentially to zero as a function of |T 0 | , with exponent gi ven by the KL div ergence (21) computed for φ = 0 , i.e., lim |T 0 |→∞ 1 |T 0 | log P e = − D p X |H ( X (0) |H 0 ) || p X |H ( X (0) |H 1 ) , (28) provided that the parameters ˆ ω m i,n hav e been correctly esti- mated. T o address the hypothesis association error , since the sink node collects more information than each single trusted node, we let the sink correct the association by flipping the sign of the reported R φ,n as follows. The parameter estimation error occurs when the observed data is noisy and does not represent the full feature statistics, or when the attacker manages to confuse a trusted node. The sink node can still make a robust decision by weighing the values R φ,n . The two refinements are jointly obtained by replacing (15) with Ψ φ = X n g n ( φ ) s n ( φ ) R φ,n , (29) where g n ( φ ) > 0 is a weight to correct PDF parameter estimation errors, and s n ( φ ) ∈ {− 1 , 1 } is the binary correction factor for the hypothesis association. Choice of g n ( φ ) — The weighting mechanism reflects the fact that the physical location of the trusted node matters in two respects: if a trusted node n is closer to the packet source, be it the legitimate transmitter or the attacker , the estimate ˆ ω m i,n is more reliable. Moreover , if the trusted nodes are spread around the network area, instead of being clustered close to one another , it becomes easier to detect that the attacker is imitating a certain transmitter-trusted node channel. This is because for each fake packet sent, the attacker can realistically attempt to mimic the channel only within a limited area. W e use channel feature i ? = 6 (the smoothed receiv ed power in Section III-B) as a measure of physical proximity to the packet source, and formalize the weighing function as g n ( φ ) = ¯ x i ? ,n ( φ ) max n 0 ( ¯ x i ? ,n 0 ( φ )) ! − 2 (1 + ζ n ) , (30) where ¯ x i ? ,n ( φ ) is the mean of the set { x i ? ,n ( t ) , t ∈ T φ } . The first term of (30) is the normalized weighting function, while ζ n ensures that isolated trusted nodes are giv en higher weights than clustered nodes, as they contrib ute with more information. T o that end, we choose ζ n to reflect the variance of the UTM locations of the trusted nodes, normalized to the closeness to the packet source. Specifically , ζ n = P k 6 = n ζ n,k , where ζ n,k = 1 P j 6 = k ,n ¯ x i ? ,j ( φ ) · X j 6 = k ,n 1 ¯ x i ? ,j ( φ ) × 1 − p ( k ) − p ( n ) T p ( j ) − p ( n ) ¯ x i ? ,n ( φ ) ¯ x i ? ,k ( φ ) ! (31) is a normalized distribution measure between nodes n and k , and p ( ` ) is the set of UTM coordinates of node ` . Choice of s n ( φ ) — W e choose s n ( φ ) at the sink node so as to maximize the agreement among the trusted nodes. W e adopt a majority rule, i.e., let ¯ s φ ∈ {− 1 , 1 } be the sign of the majority of reports R φ,n , then s n ( φ ) = sgn( R φ,n ) ¯ s φ , (32) so that sgn( s n ( φ ) R φ,n ) = ¯ s φ for all n . Also in this case an analysis of the probability of error in the sign change does not yield closed-form expressions. Assuming that the choice of the majority sign ¯ s φ is correct (i.e., it corresponds to the true hy- pothesis), and that both the parameters and the assignment (26) are correct, we consider the probability that any of the N signs of R φ,n is not correct. Let π n = P [sgn( R φ,n ) 6 = ¯ s φ ] . In this case, since the parameters and the assignment are correct, we should not change the sign, and the probability that this error occurs for at least one n is P e,s = 1 − Y n (1 − π n ) . (33) Now , for small values of π n we hav e P e,s ≈ max π n . Therefore, resorting again to the Chernof f-Stein lemma, we can conclude that P e,s goes to zero as |T φ | → ∞ exponentially with exponent lim |T φ |→∞ 1 |T φ | log P e,s ≈ − min n |T φ | X i D p x | ω ( x i,n ( τ ) | ω 0 i,n ( φ )) || || p x | ω ( x i,n ( τ ) | ω 1 i,n ( φ )) , (34) where the approximation comes from having considered only the error probability of the least reliable node n , i.e., the one having the minimum KL diver gence. Algorithm 1 summarizes the proposed authentication pro- cedure. The trusted nodes act first (lines 3–7), and the sink makes the final decision (lines 9–16). The complexity of the EM algorithm is O ( N sym N EM ) [31], where N sym is 8 Algorithm 1 Cooperativ e Authentication Algorithm Require: Set of channel measurements { x i,n ( t ) , t ∈ T φ } , i ∈ I , for each trusted node n and for each current and previous packets φ ; Ensure: Authentication decision for a packet φ ; Begin 1: Calculate ω m i,n , m = 0 , 1 (see Section V); 2: for each received packet φ do 3: for each trusted node n do 4: Associate hypothesis m = { 0 , 1 } by (27); 5: Calculate Ψ m φ,n from (17); 6: Calculate local decision index R φ,n by (16); 7: Forward R φ,n to sink; 8: end for At the sink: 9: Calculate hypothesis correction s n ( φ ) by (32); 10: Calculate trusted nodes’ weights g n ( φ ) by (30); 11: Calculate decision index Ψ φ by (29); 12: if Ψ φ ≥ λ then 13: packet is authentic; 14: else 15: packet is false; 16: end if 17: end for End the number of elements in X ( φ ) and N EM is the number of EM iterations. The numerical solution to (39)–(41) is obtained through the alternating optimization approach [39], whose complexity is O N 3 sym + N 2 sym + N sym . The EM procedure is performed for each of the four estimated channel feature, and for each trusted node. Finally , the authenti- cation decision has complexity O (1) . Thus, the complex- ity of our algorithm for authenticating a single packet is O 4 N ( N sym + N 3 sym + N 2 sym ) N EM . W e also note that the EM algorithm, as well as the alternate maximization process, prov ably con verge to a local maximum of the log-likelihood function (35). W e explore this conv ergence numerically in the following. V . N U M E R I C A L R E S U LT S W e ev aluate our authentication approach using realistic channel simulations obtained through the Bellhop frame- work [23], an established ray-tracing tool to simulate acoustic propagation under water . W e set our simulations in the Bay Area of San Diego, CA, between the latitude/longitude co- ordinates [32 . 6 ◦ , − 117 . 8 ◦ ] and [33 . 3 ◦ , − 117 . 2 ◦ ] . The setting is characterized by a continental shelf zone with a quasi- flat bottom, of a depth between 50 and 100 m, followed by a ridge, which plunges to lo wer depths. Here we consider a portion of this area, whose bathymetry map is shown in Fig. 3. In this portion, the depth ranges from about 10 m in the top-right corner of the map, to about 450 m in the bottom-left corner . W e assume that the bottom sediments are mostly sandy and that the sound speed profile decreases almost linearly from 1520 m/s (sea lev el) to 1480 m/s (depth 450 m), which corresponds to an actual measurement taken in the area Fig. 3. Bathymetry map of the area, showing the location of Alice and the trusted node deployment area. during the summer season. Furthermore, we assume a flat ocean surface. Fig. 3 also provides a view of our simulation setup. The locations of the legitimate transmitter (Alice) and the attacker (Eve) are shown as a red diamond and a black cross, re- spectiv ely . The distance between the legitimate node and the attacker is about 1500 m. The trusted nodes are deployed within the area enclosed in the white frame, which has a size of about 2 km × 2 km (notice that the scale is different on the x-axis and y-axis in Fig. 3). As the focus of this e v aluation is on the authentication model itself and not on the design of the communication between the trusted node and the sink, we do not explicitly model the links between the sink and the trusted nodes in the following. W e collect a Monte-Carlo set of 500 simulation runs. In each run, the location and depth of the trusted nodes are uniformly drawn at random, whereas the locations of the legitimate node and the attacker remain fix ed. Each simulation run corresponds to the transmission of a total of six packets from the legitimate transmitter to all trusted nodes, and of one packet from the attacker , also directed to all trusted nodes. Each packet includes 100 symbols, out of which each trusted node produces 100 estimates of the channels’ number of taps (3), relative RMS delay spread (6), and the smoothed received power (8), which have been found to offer sufficient diversity to enable our authentication scheme. Since the transmitted signals were wideband (relativ e to the carrier frequency) and transmitted with high SNR, channel estimates were obtained by processing the receiv ed signals through a normalized matched filter . Relev ant channel taps were determined by identifying the peaks exceeding a threshold corresponding to a probability of false alarm of 10 − 4 according to the analysis of [28]. For each packet, we obtain a different channel estimate by simulating the oscillation of the nodes around their mooring location. For each symbol, we perform a separate Bellhop run where the transmitter and the receiv er are randomly displaced by a short distance from their nominal location. Assuming a realistic transmission system with 10 kHz of bandwidth, the power -delay profiles have been filtered such that no two 9 arriv als exist whose delays are less than 100 µ s apart. The correlation among different channel realizations is ensured by the fact that the displacement of each node is small. W e compare our scheme with a typical approach for au- thentication that is also aligned with our proposal, referred to as benchmark . This approach compares the 2-norm dif ference between a feature of a giv en impulse response and the same feature of a reference impulse response. Follo wing [40], [41], we choose the receiv ed power as the compared channel feature, and the reference channel to be that of the first packet of the legitimate transmitter . A. Attack Strate gy T o implement the attacker model in Section III-D, we consider different attacker capabilities which, in turn, enable increasingly comple x attack strategies. The most typical case is a straightforward impersonation attack, where the attacker tries to disguise himself as the legitimate transmitter by sending packets to all trusted nodes. This na ¨ ıve attack can succeed if, e.g., the attacker is close to the legitimate node. W e model this attack by using the Bellhop software [23] to estimate the channel impulse response from the legitimate node or the attacker to all of the trusted nodes. A more powerful attack, referred to as TN-1 , is enabled if the attacker can estimate the channel impulse response between the legitimate node and one of the trusted nodes, and can leverage an array of transducers in order to approach this channel response. T o compute the channel estimate, we assume the attacker knows the exact sound speed profile and the location of both the legitimate and the trusted nodes, but has an imperfect bathymetry map. Specifically , the attacker stores the value of the bathymetry for the same set of latitude and longitude coordinates used in the simulation, but each bathymetry sample is affected by a constant offset ∆ z equal to 5% of the maximum depth, and by an error drawn at random in the interval [ − 0 . 1∆ z , 0 . 1∆ z ] . The attacker runs the same acoustic propagation model provided by Bellhop to estimate the channel impulse response and then pre-processes its transmission, such that it will be received as having gone through the estimated channel between the legitimate node and the trusted node. An even more complex attack is obtained by assuming that the attacker can approximate the channel response between the legitimate node and multiple trusted nodes, ultimately all of them. This attack is referred to as TN- x , and makes it possible for the attacker to disguise itself as the legitimate node, limited only by its capability to estimate the channels between the legitimate node and the trusted nodes. W e stress that trying to fool a single trusted node in TN-1 requires sev eral complex steps, including channel estimation, channel in version and pre-coding, but may still be possible for an underwater attacker endowed with a large transceiver array and sufficient computational power . Instead, fooling multiple cluster nodes at the same time in TN- x , x > 1 , would require the deployment of multiple, perfectly coordinated transceiv er array elements at different locations in the network area. This is orders of magnitude less realistic in any practical underwater scenario. 0 2 4 6 8 10 Iteration number 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 Normalized Convergence ( ) numTaps AveTaps delayRMS rxPowerSmoothed Fig. 4. A verage conv ergence of the EM algorithm for parameter µ . B. Determining the Threshold level In order to make the authentication decision in (13), we need to determine the decision threshold λ . W e offer two approaches. The first is to determine the receiver operating characteristic (R OC) curve as a function of the threshold ( R OC test ), either theoretically using the relation in 19 or numerically . The second method is based on a support vector machine (SVM) to classify the two hypotheses based on the decision index ( SVM-test ). For both methods, we divide the simulation data into a training part and a test part. The threshold computation is performed only on the training data set, whereas the data analysis is performed only on the test set. In the ROC test, we try a set of threshold values over the training data and draw the TP rate against the FN rate. W e then determine a desirable w orking point that trades of f between the values of these two metrics. In the SVM test, we av oid setting such a trade-off, and instead seek the threshold that yields the best classification solution. T o this end, we perform a K -fold test to determine the classifier’ s parameters, and train the SVM model based on the training set. Classification is performed on the test set, and the threshold is determined based on the minimum decision index from all packets classified as belonging to the attacker . C. Simulation Results W e first describe the simulation results for the na ¨ ıve at- tacker , which transmits its packets directly , without any pre- processing. Fig. 4 shows the normalized con vergence of the EM algorithm for the mean parameter µ , averaged ov er the trusted nodes and the number of simulations for all estimated parameters. W e observe that, for all estimated parameters, the EM procedure con verges after only 6 iterations on av erage. Similar results are obtained for the conv ergence of σ and β . In Fig. 5a we assess the average R OC from a) bound (19) on GG signals with estimated parameters (KL Bound), b) LLR thresholding on GG signals with estimated parameters (GG Model), c) LLR thresholding on Bellhop simulations (Actual). In particular , for a) and b), the bound and R OC are 10 obtained using signals generated according to the GG model and the estimated parameters, respectively . For c) we apply the detection technique described in the pre vious subsection for the estimated parameters from Bellhop simulations. For all scenarios, we obtain a R OC curve for each parameter estimation, then for each misdetection probability we average the false alarm probability to obtain average ROC and bound curves. As expected, the bound provides the highest true positiv e ( 1 − P MD ) probability for the same false alarm probability , while the R OC obtained from the GG model has a slightly reduced true positiv e probability . The effecti ve ROC shows worse performance due to estimation errors affecting the GG parameters and to a slight model mismatch between the Bellhop simulations and the GG model. Fig. 5b shows the histogram of the decision index, nor- malized within the [ − 1 , 1] range, for 1,000 simulated test scenarios, together with the performance of the benchmark scheme, the SVM test-based threshold, and the R OC test- based threshold. The latter was set based on the R OC curve in Fig. 5a, and we choose as a best practice (at least under the assumption that the channel does not v ary significantly) the knee point in the R OC curv e to yield a desired FN probability of 0.1 and a TP probability of 0.98. The SVM test-based threshold was obtained from a radial basis function (RBF) kernel SVM with a K = 5 -fold training procedure. The procedure achiev ed an excellent authentication accuracy of 97% . W e observe that the decision index v alues for the legitimate packets (Alice) and the attacker’ s packets (Eve) are well distinguished. While a similar trend is also obtained for the benchmark scheme, here the difference between Alice and Eve is less dominant. Although they hav e been obtained through different procedures, the threshold based on the SVM test is close to the one based on the R OC test. Howe ver , the SVM-based threshold yields a slightly better performance (the same TP , but lower FN probability). Next, we explore the performance of our authentication method against the more advanced TN- x attacker models. Recall that this requires the attacker to accurately estimate the bathymetry as well as the location of the legitimate node and the trusted node. W e recall that we fav or the attacker by assuming that it possesses perfect knowledge of the legitimate nodes and the trusted nodes’ location, knowledge of the sound speed profile and of the sediments on the bottom (as is necessary to run the Bellhop propagation model), and slightly erroneous knowledge of the bathymetry . W e illustrate the authentication algorithm performance for the case where the attacker attempts to imitate the channel to a single trusted node (TN-1, Fig. 6a); to two (TN-2, Fig. 6b); to three (TN-3, Fig. 6c); and to all four trusted nodes (TN- 4, Fig. 6d). Since the packets arrive almost simultaneously to all of the trusted nodes, the last three cases of TN-2, TN- 3, and TN-4 are infeasible without an advanced and lar ge transmission array . Still, we ev aluate them to show that our approach remains rob ust ev en under lar gely unrealistic attacker models. For all cases, we also give the R OC performance as obtained by the statistical approach and by the SVM approach. In each caption, we provide the accuracy obtained through the SVM approach. By comparing the empirical distribution 10 -6 10 -4 10 -2 P FA 0.6 0.65 0.7 0.75 0.8 0.85 0.9 0.95 1 1-P MD KL Bound GG Model Actual Trade-off point (a) ROC curve for the KL bound (19), GG signals with estimated parameters (GG Model), and Bellhop signals (Actual). -1 -0.9 -0.8 -0.7 -0.6 -0.5 Decision Index 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 Histogram for Decision Index Alice Eve Benchmark-Alice Benchmark-Eve SVM Th. TP=0.97781, FN=0.091358 ROC Th. TP=0.97226, FN=0.081481 (b) Empirical distribution of the decision index for our method and the benchmark. Fig. 5. Simulation results of LLR Ψ φ from (13) for a na ¨ ıve attacker . The obtained authentication accuracy is 97% . curves of the decision index for the two classes in Figs. 5b and 5b, we observe that the two classes become expectedly less distinct if the attacker imitates the channel to a higher number of trusted nodes. A similar , but less distinctiv e trend, is also observed for the benchmark scheme. For our approach , the results show that, ev en for the advanced TN-4 attacker , 92% of the packets are still classified correctly . An ev en better authentication accuracy of 96% is achiev ed for the more realistic TN-1 case. V I . S E A E X P E R I M E N T In this section, we describe the setup and results obtained from two sea experiments aimed at demonstrating the effec- tiv eness of our authentication method under real sea condi- tions. In particular , we show the validity of our assumptions regarding the distrib ution model, and measure the ef fecti veness to separate the legitimate and the attacker through the decision index (13). One experiment, Exp1 , w as conducted in May 2017 near the Hadera coal pier in northern Israel, and the second, Exp2 , at the Inter-Uni versity Institute for marine sciences in Eilat, Israel. Exp1 enabled performance ev aluation in a larger 11 -1 -0.9 -0.8 -0.7 -0.6 -0.5 Decision Index 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 Histogram for Decision Index Alice Eve Benchmark-Alice Benchmark-Eve SVM Th. TP=0.98705, FN=0.11852 ROC Th. TP=0.98705, FN=0.12593 (a) TN-1, Accuracy 96%. -1 -0.9 -0.8 -0.7 -0.6 -0.5 Decision Index 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 Histogram for Decision Index Alice Eve Benchmark-Alice Benchmark-Eve SVM Th. TP=0.96856, FN=0.10617 ROC Th. TP=0.97904, FN=0.15556 (b) TN-2, Accuracy 96%. -1 -0.9 -0.8 -0.7 -0.6 -0.5 Decision Index 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 Histogram for Decision Index Alice Eve Benchmark-Alice Benchmark-Eve SVM Th. TP=0.96239, FN=0.13086 ROC Th. TP=0.96856, FN=0.14321 (c) TN-3, Accuracy 94%. -1 -0.9 -0.8 -0.7 -0.6 -0.5 Decision Index 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 Histogram for Decision Index Alice Eve Benchmark-Alice Benchmark-Eve SVM Th. TP=0.98397, FN=0.074074 ROC Th. TP=0.9889, FN=0.079012 (d) TN-4, Accuracy 92%. Fig. 6. Simulation results of decision index Ψ φ from (13) for an advanced attacker . Fig. 7. Setup of the Hadera (left) and Eilat (right) sea experiments. network, whereas Exp2 had a longer duration, and thus better reflects the variations of the UW A C channel ov er time. A. Setup The setup of the sea experiments is illustrated in Fig. 7. Exp1 included two transmitters (station Tx1 on a pier that stretches 2 km into the sea, and station Tx2 on the larger boat), and three receivers (station Rx2 on the smaller boat, and stations Rx1 and Rx3 on floating buo ys). The transmitters were placed roughly 1000 m apart, and the three receivers were deployed along a line with spacing of roughly 500 m. The distances between the receiver on the smaller boat and the boat and pier transmitters were roughly 300 m and 400 m, respectively . Due to the pier’ s thick stone columns, the transmissions of Tx1 were not receiv ed by Rx1. Exp2 included two transmitters, one on a buoy and one deployed from a boat, and two recei vers, both deplo yed from anchored b uoys. In both experiments, the water depth was about 25 m, and the modems and receivers were deployed at a depth of about 10 m. Since the area in Exp2 is a protected reef, all except the Boat Tx nodes were moored by scuba divers. During both experiments, the sea was rough, with a sea level of 3 and waves rising to ov er 1.5 m. In both experiments, we used EvoLogics software-defined S2CR 7/17 modems to transmit from both transmitters packets of 100 (Exp1) and 60 (Exp2) chirp-modulated symbols of 10 ms in the frequency band between 7 kHz and 17 kHz at the source lev el of roughly 175 dB re 1 µ Pa@1m. The 12 P1 (AL) P2 (AL) P3 (AL) P4 (AL) P5 (AL) P6 (AL) P7 (AL) P8 (Eve) P9 (Eve) 0 0.002 0.004 0.006 0.008 0.01 0.012 0.014 Delay spread [sec] Rx 1 Rx 2 Rx 3 (a) Relativ e RMS delay spread. P1 (AL) P2 (AL) P3 (AL) P4 (AL) P5 (AL) P6 (AL) P7 (AL) P8 (Eve) P9 (Eve) 0 5 10 15 20 25 30 35 Average number of paths Rx 1 Rx 2 Rx 3 (b) Number of taps. P1 (AL) P2 (AL) P3 (AL) P4 (AL) P5 (AL) P6 (AL) P7 (AL) P8 (Eve) P9 (Eve) 0 0.005 0.01 0.015 0.02 0.025 0.03 Average Path power attenuation Rx 1 Rx 2 Rx 3 (c) A verage tap’s power . P1 (AL) P2 (AL) P3 (AL) P4 (AL) P5 (AL) P6 (AL) P7 (AL) P8 (Eve) P9 (Eve) 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 Average normalized smoothed received level Rx 1 Rx 2 Rx 3 (d) Smoothed received power level, α = 0 . 5 . Fig. 8. A verage per-packet values of the authentication features from sea experiment Exp1 (Legitimate node: Tx 1). receiv ers employed a Cetacean CR1 hydrophone, and recorded continuously throughout the experiment. Analysis was per- formed off-line. In Exp1, we tested two configurations: one where node 1 served as the legitimate node and transmitted sev en packets followed by the transmission of two packets from node 5, which served as the attacker , and vice versa in the second configuration. Exp2 was longer, as we let both the legitimate node (Floater Tx) and the attacker (Boat Tx) transmit sequences of 10 packets one after the other, for a total of 50 packets each. T o allow accurate channel estimation, we used a guard interval of 0.1 s between each symbol, and set a gap that stretched from 10 s to 60 s between consecutive packets from the same transmitter . Exp1 lasted for 5 min for each configurations, while Exp2 lasted for 70 min. This long time span allowed capturing instantaneous channel variations, and testing our assumption in the realistic scenario of drifting nodes. As in the simulation discussed in Section V -C where we did not consider the channels between nodes and sink, also in the experiments we collect data directly from the trusted nodes and process it off-line. The choice of channel features used for authentication is based on our preliminary analysis in Section III-B, and includes the number of taps (3), the relative RMS delay spread (6), and the smoothed receiv ed power lev el (8). Our results show that, to extract the largest degree of div ersity from this scenario, including the average tap’ s power (4) is beneficial due to the different link attenuations. Similar to our simulations, we estimated those channel features by thresholding the output of a normalized matched filter . B. Results W e start by showing the estimated values of the four authentication features from Exp1. In Fig. 8a, we sho w the av erage per-pack et relativ e delay spread values from the three receiv ers. W e observe that packets 8 and 9 from the attacker (Eve) are well distinguished from packets 1-7 from the le- gitimate node (AL). A similar effect is shown in Figs. 8b and 8c for the av erage per-packet number of taps and the av erage tap power . Instead, Fig. 8d shows the per -packet smoothed receiv ed po wer lev el, and we observ e that at Rx3 little difference is sensed between Alice’ s and Eve’ s. Howe ver , at Rx2 the same metric results in very dif ferent v alues for Alice and Eve, hence the effect on performance is limited. Figs. 9a and 9b show the LLR Ψ φ obtained in Exp1 and Exp2 for all recei ved packets. For Exp1, the LLRs from the legitimate transmitter are stable, whereas for Exp2 we observe 13 a variation over time. This is because the longer duration of the experiment induces slow variations in the stability of the parameters ˆ ω m i,n ( φ ) . For both experiments Ψ φ for the legiti- mate node’ s packets are well distinguished from the attacker’ s packets. In Fig. 9b we also compare our results with those of the benchmark scheme. As expected, in realistic conditions the underwater channel changes ov er time, hence the decision index computed by the benchmark cannot distinguish between the legitimate node’ s and the attacker’ s packets. Still, as the distribution of the channel features remains relativ ely stable, our approach successfully discriminates authentic packets. In Fig. 10, we show the difference (or gain), ρ Gain , between the av erage Ψ φ for the legitimate node’ s packets and the av erage Ψ φ for the attacker’ s packets. For Exp1, the average was calculated for all packets, while for Exp2, due to the time variation observed in Fig. 9b, we averaged groups of packets receiv ed over time windo ws of 10 minutes. T o explore the contribution of each channel feature to the decision index, we show ρ Gain when using each of the channel features alone and all the features together . For both experiments, the results of our method suggest that the conjunction of all features achieves higher gains and that, although the smoothed receiv ed power showed high gains, no single channel feature yields significantly higher benefits than the others. Fig. 10 also shows ρ Gain for the benchmark scheme applied to the smoothed receiv ed power . The small and sometimes negati ve gain reflects that, due to the channel’ s time variation, the benchmark is unable to le verage the diversity offered by the channel features and authentication fails. By way of contrast, the results of our method show a significant gain, and thus good authentication performance, e ven after 70 min of consecutiv e transmissions. Finally , we remark that, as shown in Fig. 9b, ρ Gain decreases ov er time, which implies on the need to re-estimate the distribution parameters of each features periodically , although this is only needed once ev ery sev eral tens of minutes, confirming the robustness of our scheme. V I I . C O N C L U S I O N S In this paper, we presented a new cooperati ve message au- thentication method for underwater acoustic networks, where a set of trusted nodes helps a sink node determine whether a receiv ed message was sent by a legitimate transmitter or by an attacker . Our method leverages the strong spatial dependency and time-in variance of the distribution of the underwater acoustic channel features in order to perform authentication based on the computation of a decision index. This operation is performed by a set of trusted nodes acting in a distributed fashion, whereas a sink node fuses the beliefs of the trusted nodes and makes a final decision. No feedback to the trusted nodes is required for this. Extensiv e model-based numerical simulations, as well as demonstrations in two sea experiments prov e the effecti veness of our scheme. Further work will extend our approach to intruder detection. A P P E N D I X In the following, we focus on a single channel feature i and a single node n , and therefore drop the indices i, n from all notation. T o estimate θ ( p ) , we use the expectation maximiza- tion (EM) algorithm [31, Ch. 17] to update the estimate of θ iterativ ely . Denote ˜ θ ( p + 1) = ˜ ω m ( p + 1) , ˜ k m ( p + 1) as the estimate obtained at the end of iteration p . W ith the constraint that all estimates within one of the previously received packets f = 1 , . . . , φ must be assigned to the same hypothesis ( m = 0 , 1 ), we define y ( f ) ∈ { 0 , 1 } as the label assigned to packet f . Let Y ( φ ) = { y ( t ) , t ∈ T f } be the set of estimated labels for feature i at node n up to packet φ , and Y ( f ) = { y ( t ) , t ∈ T f , f ≤ φ } . Let ¯ X ( f ) be a subset of X ( φ ) including only those measurements x that are obtained from packet f = { 0 , . . . , φ } . The expectation of the log-likelihood function at iteration p , is L θ | ˜ θ ( p ) = E h log P ( X ( φ ) , Y ( φ ) | θ ) | ¯ X ( φ ) , ˜ θ ( p ) i = = 1 X m =0 F X f =1 P y ( f ) = m | X ( f ) , ˜ θ ( p ) · log ˜ k m ( p ) + X x ∈ ¯ X ( f ) log p x | ω m x | ˜ ω m ( p ) , (35) where log x is the natural logarithm of x and the posterior is P y ( f ) = m | ¯ X ( f ) , ˜ θ ( p ) = ˜ k m ( p ) P X ( f ) | ˜ ω m ( p ) P ¯ X ( f ) | ˜ θ ( p ) = ˜ k m ( p ) Q x ∈ ¯ X ( f ) p x | ω m x | ˜ ω m ( p ) P 2 j =1 ˜ k j ( p ) Q x ∈ ¯ X ( f ) p x | ω m x | ˜ ω j ( p ) . (36) W e maximize the second term of (35) to yield [42], ˜ k m ( p + 1) = 1 φ φ X f =1 P ( y ( f ) = m | ¯ X ( f ) , ˜ θ ( p )) . (37) T o obtain ˜ ω m ( p + 1) , we maximize the first term of (35) φ X f =1 P y ( f ) = m | ¯ X ( f ) , ˜ θ ( p ) · log P ¯ X ( f ) | ˜ ω m ( p + 1) = = φ X f =1 P y ( f ) = m | ¯ X ( f ) , ˜ θ ( p ) · · X x ∈ ¯ X ( f ) log ˜ β m ( p + 1) − log 2 ˜ σ m ( p + 1) − − log Γ 1 ˜ β m ( p + 1) − | x − ˜ µ m ( p + 1) | ˜ σ m ( p + 1) ˜ β m ( p +1) . (38) The result is obtained numerically by solving the follo wing equation for ˜ µ m ( p + 1) : 0 = φ X f =1 P y ( f ) = m | ¯ X ( f ) , ˜ θ ( p ) × × X x ∈ ¯ X ( f ) x − ˜ µ m ( p + 1) | x − ˜ µ m ( p + 1) | ˜ β m ( p ) − 2 , (39) 14 Legitimate node: Tx 1 Legitimate node: Tx 2 -1 -0.8 -0.6 -0.4 -0.2 0 0.2 0.4 Decision index Pck 1 Pck 2 Pck 3 Pck 4 Pck 5 Pck 6 Pck 7 Pck 8 (eve) Pck 9 (eve) (a) Hadera experiment 0 10 20 30 40 50 60 70 Time [min] -0.8 -0.6 -0.4 -0.2 0 0.2 0.4 Decision Index Floater (Alice) Boat (Eve) Benchmark (Alice) Benchmark (Eve) (b) Eilat experiment Fig. 9. LLR Ψ φ from the sea experiments, showing significant differences between Alice and Eve. Legitimate node: Tx 1 Legitimate node: Tx 2 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 Gain All Delay spread Num taps Ave Tap's power Smoothed Rx power Benchmark (Smoothed Rx power) (a) Hadera experiment. 0 10 20 30 40 50 60 70 Time [min] -0.1 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 Gain All Delay spread Num taps Ave Tap's power Smoothed Rx power Benchmark (Smoothed Rx) (b) Eilat experiment. Fig. 10. Importance of each channel feature used for authentication in (a) the Hadera experiment and (b) the Eilat experiment. and then by solving, for ˜ σ m ( p + 1) , 0 = φ X f =1 P y ( f ) = m | ¯ X ( f ) , ˜ θ ( p ) X x ∈ ¯ X ( f ) − 1 ˜ σ m ( p + 1) + ˜ β m ( p ) | x − ˜ µ m ( p + 1) | ˜ β m ( p ) ( ˜ σ m ( p + 1)) ˜ β m ( p ) − 1 . (40) Finally , for ˜ β m ( p + 1) , we solve ( d ( · ) is the digamma function) 0 = φ X f =1 P y ( f ) = m | ¯ X ( f ) , θ ( p ) 1 ˜ β m ( p + 1) + d 1 ˜ β m ( p +1) ( ˜ β m ( p + 1)) 2 + X x ∈ ¯ X ( f ) log | x − ˜ µ m ( p + 1) | ˜ σ m ( p + 1) · | x − ˜ µ m ( p + 1) | ˜ σ m ( p + 1) ˜ β m ( p +1) # . (41) After the conv ergence of the EM procedure, we calculate the posterior P y ( f ) = m | ¯ X ( f ) , ˜ θ ( p + 1) , and use it as a soft decision parameter to assign packet f with set m . T o consistently identify sets m = { 0 , 1 } between the different trusted nodes, for the first received packet, we determine m = 1 as the set m that yields the highest posterior . T o initialize the EM, we use the k-means algorithm [43, Section 33.7] to cluster X ( φ ) into two groups. For each group m , we ev aluate ˜ ω m (0) using the following statistics for PDF (2) E [ X ( φ )] = ˜ µ m (0) (42a) E |X ( φ ) − ˜ µ m (0) | 2 = ˜ σ m (0) 2 Γ 3 ˜ β m (0) Γ 1 ˜ β m (0) (42b) Kurtosis = E [( X ( φ ) − ˜ µ m (0)) 2 ] ( E [( X ( φ ) − ˜ µ m (0)) 2 ]) 2 = = Γ 5 ˜ β m (0) Γ 1 ˜ β m (0) Γ 3 ˜ β m (0) 2 − 3 . (42c) where the above mean, variance, and Kurtosis are calculated using standard methods. Similarly , the prior ˜ k m (0) is estimated 15 as the fraction of the elements of X ( φ ) , which is part of the m th cluster after the k-means algorithm. R E F E R E N C E S [1] J. Potter , J. Alves, D. Green, G. Zappa, I. Nissen, and K. McCoy , “The J ANUS underwater communications standard, ” in Pr oc. UComms , Sestri Lev ante, Italy , Sep. 2014. [2] E. Souza, H. C. W ong, I. Cunha, . Cunha, L. F . M. V ieira, and L. B. Oliv eira, “End-to-end authentication in under-water sensor networks, ” in Pr oc. IEEE ISCC , Split, Croatia, Jul. 2013. [3] G. Han, J. Jiang, N. Sun, and L. Shu, “Secure communication for underwater acoustic sensor networks, ” IEEE Tr ans. Mobile Comput. , vol. 53, no. 8, pp. 54–60, Aug. 2015. [4] C. Lal, R. Petroccia, M. Conti, and J. Alves, “Secure underwater acoustic networks: Current and future research directions, ” in Pr oc. IEEE UComms , Lerici, Italy , Aug. 2016. [5] Y . Liu, J. Jing, and J. Y ang, “Secure underwater acoustic communication based on a robust ke y generation scheme, ” in Pr oc. ICSP , Beijing, China, Oct. 2008. [6] D. Muhammed, M. H. Anisi, M. Zareei, and A. Khan, “Game theory- based cooperation for underwater acoustic sensor networks: T axonomy , revie w , research challenges and directions, ” MDPI Sensors , vol. 18, no. 2, Feb. 2018, art. 425. [7] M. Sharif-Y azd, M. R. Khosrav , and M. K. Moghimi, “ A survey on underwater acoustic sensor networks: Perspectives on protocol design for signaling, MAC and routing, ” SciRP J. of Computer and Commun. , vol. 5, no. 5, pp. 12–23, Feb. 2017. [8] E. Jorswieck, S. T omasin, and A. Sezgin, “Broadcasting into the uncer- tainty: Authentication and confidentiality by physical-layer processing, ” Pr oc. IEEE , vol. 103, no. 10, pp. 1702–1724, Oct. 2015. [9] D. Faria and D. Cheriton, “Detecting identity-based attacks in wireless networks using signalprints, ” in Proc. ACM W iSe , Los Angeles, CA, Sep. 2006. [10] M. Demirbas and Y . Song, “ An RSSI-based scheme for sybil attack detection in wireless sensor networks, ” in Proc. IEEE W oWMoM) , Buff alo, NY), Jun. 2006. [11] Y . Chen, W . Trappe, and R. Martin, “Detecting and localizing wireless spoofing attacks, ” in Proc. IEEE SECON , San Diego, CA, Jun. 2007. [12] L. Xiao, L. Greenstein, N. Mandayam, and W . Trappe, “Fingerprints in the ether: using the physical layer for wireless authentication, ” in Pr oc. IEEE ICC , Glasgow , UK, Jun. 2007. [13] ——, “ A physical-layer technique to enhance authentication for mobile terminals, ” in Proc. IEEE ICC , Beijing, China, May 2008. [14] L. Xiao, L. J. Greenstein, N. Mandayam, and W . Trappe, “Channel- based spoofing detection in frequency-selecti ve Rayleigh channels, ” IEEE Tr ans. W ir eless Commun. , vol. 8, no. 12, pp. 5948–5956, Dec. 2009. [15] L. Xiao, A. Reznik, W . Trappe, Y . S. C. Y e, and L. Greenstein, “PHY- authentication protocol for spoofing detection in wireless networks, ” in Pr oc. IEEE GLOBECOM , Miami, FL, Dec. 2010. [16] F . He, W . W ang, and H. Man, “REAM: rake receiver enhanced authen- tication method, ” in Proc. IEEE MILCOM , Oct. 2010, pp. 2205–2210. [17] F . He, H. Man, D. Kiv anc, and B. McNair, “EPSON: enhanced physical security in OFDM networks, ” in Proc. IEEE ICC , 2009, pp. 1–5. [18] J. K. T ugnait, “Wireless user authentication via comparison of power spectral densities, ” IEEE J. Sel. Areas Commun. , vol. 31, no. 9, pp. 1791–1802, Sep. 2013. [19] Q. W ang, “ A novel physical layer assisted authentication scheme for mobile wireless sensor networks, ” MDPI Sensors , vol. 17, no. 2, Feb . 2017, art. 289. [20] G. Caparra, M. Centenaro, N. Laurenti, S. T omasin, and L. V angelista, “Energy-based anchor node selection for iot physical layer authentica- tion, ” in Proc. IEEE ICC , Kuala Lumpur , Malaysia, May 2016. [21] A. Mahmood, W . Aman, M. O. Iqbal, M. M. U. Rahman, and Q. H. Abbasi, “Channel impulse response-based distributed physical layer authentication, ” in Proc. IEEE VTC , Sydney , Australia, Jun. 2017. [22] L. Xiao, X. W an, and Z. Han, “Phy-layer authentication with multiple landmarks with reduced ov erhead, ” IEEE T rans. W ireless Commun. , vol. 17, no. 3, pp. 1676–1687, Mar . 2017. [23] M. Porter et al. , “Bellhop code, ” http://oalib .hlsresearch.com/Rays/index. html. Last time accessed: Aug. 2018. [24] K. G. Kebkal, O. Kebkal, and R. Petroccia, “ Assessment of underwater acoustic channel during payload data exchange with hydro-acoustic modems of the S2C series, ” in Proc. MTS/IEEE OCEANS , Geno va, Italy , May 2015. [25] M. Stojanovic and J. Preisig, “Underwater acoustic communication channels: Propagation models and statistical characterization, ” IEEE Commun. Mag. , vol. 47, no. 1, pp. 84–89, 2009. [26] B. Katsnelson, V . Petniko v , and J. L ynch, Fundamentals of shallow water acoustics . Springer Science & Business Media, 2012, ch. 3, 4. [27] M. Nove y , T . Adali, and A. Roy , “ A complex generalized Gaussian distribution: Characterization, generation, and estimation, ” IEEE T rans. Signal Pr ocess. , vol. 58, pp. 1427–1433, Mar . 2010. [28] R. Diamant, “Closed form analysis of the normalized matched filter with a test case for detection of underwater acoustic signals, ” IEEE Access , vol. 4, pp. 8225–8235, 2016. [29] R. Diamant and L. Chorev , “Emulation system for underwater acoustic channel, ” in Proc. UDT , Amsterdam, the Netherlands, Jun. 2005. [30] R. Jain, W . Hawe, and D. Chiu, “ A quantitative measure of fairness and discrimination for resource allocation in shared computer systems, ” Eastern Research Lab, T ech. Rep. DEC-TR-301, 1984. [31] T . K. Moon and W . C. Stirling, Mathematical Methods and Algorithms . Upper Saddle River , NJ: Prentice Hall, 2000. [32] P . van W alree, H. Buen, and R. Otnes, “ A performance comparison between DSSS, M-FSK, and frequency-division multiplexing in under- water acoustic channels, ” in Proc. UComms , Sestri Lev ante, Italy , Sep. 2014. [33] M. Porter and H. Bucker, “Gaussian beam tracing for computing ocean acoustic fields, ” Journal of Acoustical Society of America , vol. 82, no. 4, pp. 1349–1359, Oct. 1987. [34] W . Burdic, Underwater Acoustic System Analysis . Los Altos, CA, USA: Peninsula Publishing, 2002. [35] A. Ferrante, N. Laurenti, C. Masiero, M. Pa von, and S. T omasin, “On the error region for channel estimation-based physical layer authentication over Rayleigh fading, ” IEEE T rans. Inf . F or ensics Security , vol. 10, no. 5, pp. 941–952, May 2015. [36] C. P . Kitsos and T . L. T oulias, “New information measures for the generalized normal distribution, ” MDPI Information , vol. 1, no. 1, pp. 13–27, 2010. [Online]. A vailable: http://www .mdpi.com/2078- 2489/1/ 1/13 [37] C. Bauckhage, “Computing the Kullback-Leibler diver gence between two generalized gamma distributions, ” 2014, http://arxiv .org/abs/1401. 6853. Last time accessed: Aug 2018. [38] T . M. Cover and J. A. Thomas, Elements of Information Theory . New Y ork, NY , USA: W iley-Interscience, 2006. [39] T . W ang, R. C. De Lamare, and A. Schmeink, “ Alternating optimization algorithms for po wer adjustment and receive filter design in multihop wireless sensor networks, ” IEEE T rans. V eh. T echnol. , vol. 64, no. 1, pp. 173–184, Jan. 2015. [40] P . Hao, X. W ang, and A. Refaey , “ An enhanced cross-layer authentica- tion mechanism for wireless communications based on per and rssi, ” in 2013 13th Canadian W orkshop on Information Theory , June 2013, pp. 44–48. [41] L. Xiao, Y . Li, G. Liu, Q. Li, and W . Zhuang, “Spoofing detection with reinforcement learning in wireless networks, ” in Pr oc. IEEE GLOBECOM , San Diego, CA, Dec. 2015. [42] R. Diamant, H. T an, and L. Lampe, “LOS and NLOS classification for underwater acoustic localization, ” IEEE T rans. Mobile Comput. , vol. 13, no. 2, pp. 311–323, Feb. 2014. [43] D. J. MacKay , Information Theory , Inference , and Learning Algorithms , 4th ed. Cambridge, UK: Cambridge Univ ersity Press, Mar . 2005. 16 Roee Diamant (S’09–M’15–SM’17) recei ved the B.Sc. and M.Sc. degrees from T echnion–Israel Insti- tute of T echnology , in 2002 and 2007, respectiv ely , and the Ph.D. degree from the Department of Elec- trical and Computer Engineering, The Univ ersity of British Columbia, in 2013. From 2001 to 2009, he was with Rafael Advanced Defense Systems, Israel, as the Project Manager and Systems Engineer , where he developed a commercial underwater modem with network capabilities. In 2015 and 2016, he was a V isiting Professor with the University of Padova, Italy . He leads the underwater Acoustic and Navigation Laboratory as an Assistant Professor at the Department of Marine T echnologies, University of Haifa. His research interests include underwater acoustic communication, un- derwater navigation, object detection, and classification. He is the Coordinator of the EU H2020 Project SYMBIOSIS (BG-14 track). In 2009, he received the Israel Excellent W orker First Place A ward from the Israeli Presidential Institute. In 2010, he receiv ed the NSERC V anier Canada Graduate Schol- arship. He has received three best paper awards, and serves as an Associate Editor for the I E E E J O U R NA L O F O C E A N I C E N G I N E E R I N G . Paolo Casari (S’05–M’08–SM’13) received the PhD in Information Engineering in 2008 from the Univ ersity of Padov a, Italy . After being on leave at the Massachusetts Institute of T echnology in 2007, his research progressively focused on underwater communications and networks. He collaborated to sev eral funded projects including CLAM (EU-FP7), RA CUN (ED A), and several US ARO, ONR and NSF initiati ves. He is the PI of the N A TO SPS project ThreatDetect, and the scientific coordinator of the EU H2020 RECAP and SYMBIOSIS projects. Previously , he was appointed T echnical Manager of the N AUTILUS and WISEW AI projects. In 2015, he joined the IMDEA Networks Institute, Madrid, Spain, where he leads the Ubiquitous W ireless Networks group. His research interests include many aspects of underwater communications, such as channel modeling and simulation, network protocol design and ev aluation, localization, and field experiments. He was a co-recipient of the IEEE WPNC 2017 best paper award. He serves on the editorial boards of the I E E E T R A N S AC T I O N S O N M O B I L E C O M P U T I N G and of the I E E E T R A N S AC T I O N S O N W I R E L E S S C O M M U N I C AT I O N S , and regularly collaborates with the or- ganizing committee of sev eral conferences. He has been guest editor of a special section of I E E E A C C E S S on Underwater Wireless Communications and Networking, and of a special issue of the Hindawi Journal of Electrical and Computer Engineering on Underwater Communications and Networking. Stefano T omasin (S’99–M’03–SM’11) was born in V enice, Italy . He received the Ph.D. degree in telecommunications engineering from the University of Padov a, Italy , in 2003. In 2002, he joined the Univ ersity of Padov a, where he is currently an As- sociate Professor . He was on leave with Philips Re- search, Eindhoven, Netherlands, in 2002, Qualcomm Research Laboratories, San Diego, CA, USA, in 2004, Polytechnic University , Brooklyn, NY , USA, in 2007, and the Huawei Mathematical and Algo- rithmic Sciences Laboratory , Boulogne-Billancourt, France, in 2014. His current research interests include physical layer security and signal processing for wireless communications, with application to 5th generation cellular systems. Since 2011, he has been an Editor of the EURASIP Journal of W ireless Communications and Networking . From 2011 to 2017, he was an Editor of the I E E E T R A N S AC T I O N S O N V E H I C U L A R T E C H N O L O G Y , and has been the Editor of the I E E E T R A N S A C T I O N S O N S I G N A L P R O C E S S I N G since 2016.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment