Machine Learning DDoS Detection for Consumer Internet of Things Devices
An increasing number of Internet of Things (IoT) devices are connecting to the Internet, yet many of these devices are fundamentally insecure, exposing the Internet to a variety of attacks. Botnets such as Mirai have used insecure consumer IoT devices to conduct distributed denial of service (DDoS) attacks on critical Internet infrastructure. This motivates the development of new techniques to automatically detect consumer IoT attack traffic. In this paper, we demonstrate that using IoT-specific network behaviors (e.g. limited number of endpoints and regular time intervals between packets) to inform feature selection can result in high accuracy DDoS detection in IoT network traffic with a variety of machine learning algorithms, including neural networks. These results indicate that home gateway routers or other network middleboxes could automatically detect local IoT device sources of DDoS attacks using low-cost machine learning algorithms and traffic data that is flow-based and protocol-agnostic.
💡 Research Summary
The paper addresses the growing security problem posed by insecure consumer Internet‑of‑Things (IoT) devices that can be hijacked into botnets such as Mirai and used for distributed denial‑of‑service (DDoS) attacks. The authors propose a lightweight, flow‑based machine‑learning pipeline that can run on a home gateway router or other on‑path middleboxes to detect DDoS traffic originating from local IoT devices.
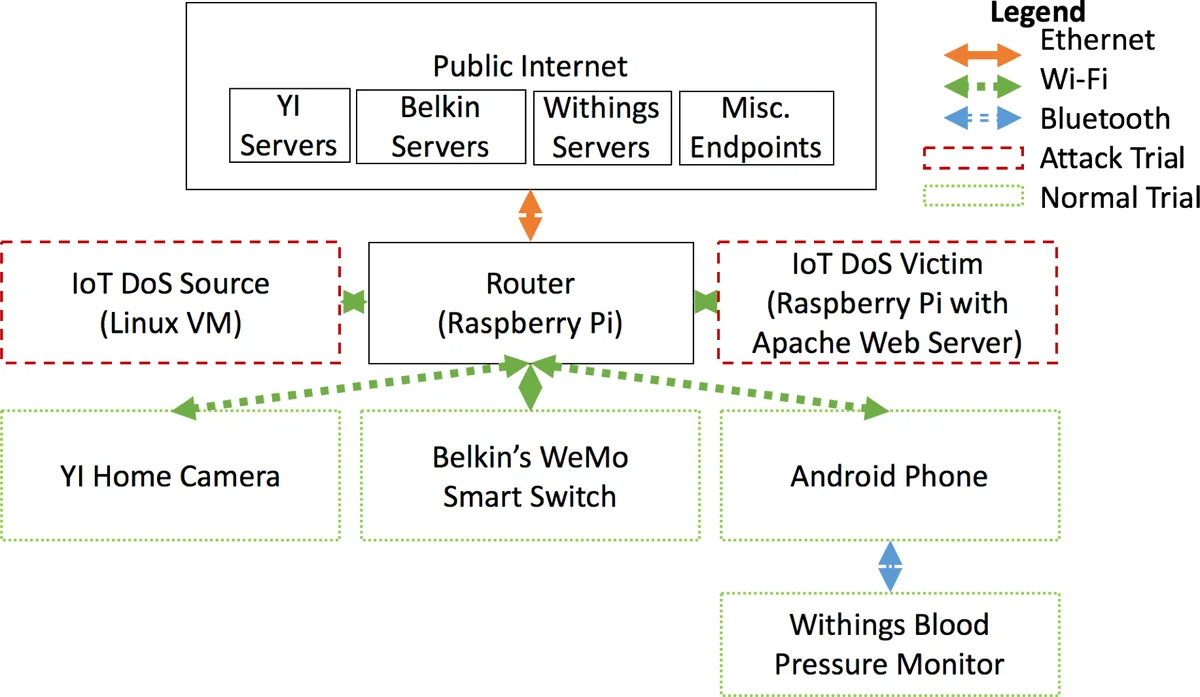
First, they construct a realistic testbed: a Raspberry Pi acting as a Wi‑Fi access point and middlebox, three popular consumer IoT devices (a YI camera, a Belkin smart switch, and a Withings blood‑pressure monitor) for benign traffic, and a Kali‑Linux VM to generate three typical Mirai‑style attacks (TCP SYN flood, UDP flood, HTTP GET flood) against a Raspberry Pi web server. By spoofing source IP/MAC addresses and interleaving attacks with normal device activity, they create a dataset of 491,855 packets (≈459 k malicious, 32 k benign).
Feature engineering is the core contribution. Two classes of features are defined:
-
Stateless features extracted per packet without any flow context: packet size, inter‑packet interval ΔT and its first and second derivatives, and a one‑hot encoding of the protocol (TCP, UDP, HTTP, other). These capture the observation that attack packets are typically very small, sent back‑to‑back, and use a different protocol mix than normal IoT traffic.
-
Stateful features computed over short (10‑second) windows per device: average bandwidth, count of distinct destination IP addresses, and the change in that count between successive windows. These exploit the IoT characteristic of communicating with a limited, stable set of endpoints.
The authors evaluate five classifiers—K‑Nearest Neighbors (KD‑Tree), linear SVM, decision tree, random forest, and a deep neural network. All achieve >0.999 accuracy, with random forest, K‑NN, and the neural net delivering the highest F1 scores. The results demonstrate that the selected IoT‑specific features are highly discriminative and that the models are lightweight enough for on‑router deployment.
Limitations are acknowledged: the dataset is simulated, includes only three device types and three flood attacks, and the 10‑second window may miss ultra‑short bursts. Real‑world deployment on ISP‑scale switches or with more diverse botnet behaviors remains untested.
In conclusion, the study shows that by tailoring features to IoT traffic patterns and using modest machine‑learning models, home routers can autonomously detect and potentially block DDoS traffic from compromised IoT devices. Future work should expand the dataset with real botnet captures, explore adaptive windowing, and integrate the pipeline into actual router firmware for field validation.
Comments & Academic Discussion
Loading comments...
Leave a Comment