Privacy-preserving data aggregation in resource-constrained sensor nodes in Internet of Things: A review
Privacy problems are lethal and getting more attention than any other issue with the notion of the Internet of Things (IoT). Since IoT has many application areas including smart home, smart grids, smart healthcare system, smart and intelligent transportation and many more. Most of these applications are fueled by the resource-constrained sensor network, such as Smart healthcare system is powered by Wireless Body Area Network (WBAN) and Smart home and weather monitoring systems are fueled by Wireless Sensor Networks (WSN). In the mentioned application areas sensor node life is a very important aspect of these technologies as it explicitly effects the network life and performance. Data aggregation techniques are used to increase sensor node life by decreasing communication overhead. However, when the data is aggregated at intermediate nodes to reduce communication overhead, data privacy problems becomes more vulnerable. Different Privacy-Preserving Data Aggregation (PPDA) techniques have been proposed to ensure data privacy during data aggregation in resource-constrained sensor nodes. We provide a review and comparative analysis of the state of the art PPDA techniques in this paper. The comparative analysis is based on Computation Cost, Communication overhead, Privacy Level, resistance against malicious aggregator, sensor node life and energy consumption by the sensor node. We have studied the most recent techniques and provide in-depth analysis of the minute steps involved in these techniques. To the best of our knowledge, this survey is the most recent and comprehensive study of PPDA techniques.
💡 Research Summary
The paper presents a comprehensive survey of privacy‑preserving data aggregation (PPDA) techniques tailored for resource‑constrained sensor nodes in the Internet of Things (IoT). Recognizing that many IoT applications—such as smart homes, smart grids, and especially health‑monitoring systems based on Wireless Body Area Networks (WBAN) and Wireless Sensor Networks (WSN)—rely on battery‑powered devices, the authors emphasize the dual challenge: reducing communication overhead to extend node lifetime while simultaneously protecting the confidentiality of sensed data during aggregation.
The authors first outline the importance of privacy in two flagship domains. In e‑health, patient data collected by WBAN sensors is highly sensitive and subject to strict regulations (e.g., HIPAA). In smart grids, fine‑grained electricity consumption data can reveal personal habits and must be shielded from profiling attacks. Both scenarios illustrate that intermediate aggregators, if compromised, become a critical privacy breach point.
To address this, the survey categorizes recent PPDA schemes into five representative families and examines each in depth:
-
Complex‑number masking (Bista et al.) – Sensors add a shared random secret to their reading, embed the result in a complex number, encrypt with a symmetric key, and forward it. The sink extracts the real part after successive decrypt‑aggregate‑encrypt steps. The scheme reduces communication cost compared with CPDA and SMART, but the authors note that the analysis omits the energy impact of repeated encryption/decryption and key‑exchange overhead.
-
Incremental Hash Function (IHF) based scheme (Yip et al.) – Smart meters hash their instantaneous cost using an IHF, send the hash to an operation center, which aggregates hashes and forwards the sum to the utility. The utility validates integrity by comparing the aggregated hash with a hash of the total generated power. The method is O(N) in computation, uses fixed‑size hashes, and offers strong pre‑image resistance, yet it does not protect the link between appliances and the meter, leaving a vulnerable segment.
-
SMART‑ER (Finster & Baumgart) – An extension of the SMART protocol that introduces randomized slicing, dependency tracking, node grouping, and extrapolation to handle communication errors and node failures. By slicing each reading into N + 1 parts and mixing them across nodes, the sink receives an irreversible sum. SMART‑ER improves valid submission rates dramatically (≈85 % vs. 10 % for SMART) while keeping overhead modest. However, the extrapolation of missing data is heuristic and may degrade accuracy.
-
SMPC/VSS/ZK architecture (Callegari et al.) – A distributed privacy‑aware framework where smart meters generate a random vector, subtract it from the true data vector, split the result into n shares, and send each share to a set of “privacy peers”. The peers aggregate shares and forward them to the utility, which combines them with the directly transmitted random vectors to reconstruct high‑frequency neighborhood consumption using homomorphic properties. This approach offers strong anonymity and integrity but incurs significant communication and computation due to multi‑party computation and zero‑knowledge proof generation, and it assumes privacy peers are semi‑trusted.
-
Homomorphic MAC (Hayouni et al.) – Each encrypted payload carries two MACs: a data‑integrity MAC and an “EMAC” that protects the MAC itself. The protocol consists of key distribution, encryption, MAC generation, and combination phases. It enables verification of aggregated data without revealing individual readings. While security is robust, generating and verifying two MACs per message may strain the limited CPU and memory of typical sensor platforms.
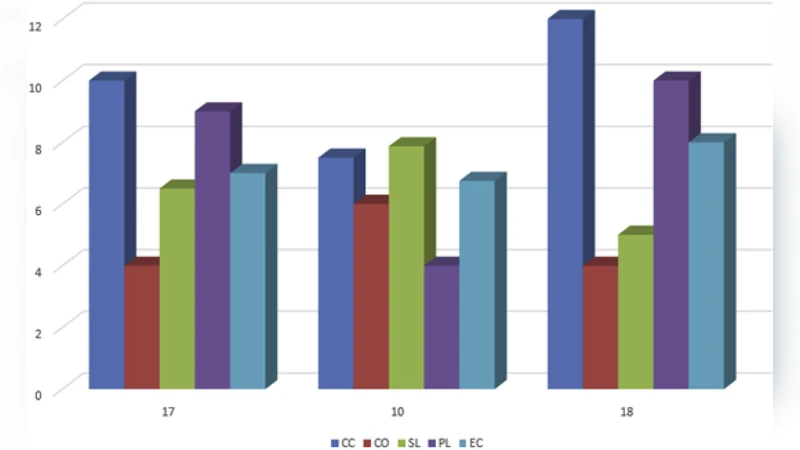
The survey evaluates all listed techniques against five criteria: (i) computational cost, (ii) communication overhead, (iii) privacy level (confidentiality, anonymity, resistance to inference), (iv) resistance to a malicious aggregator, and (v) impact on node lifetime/energy consumption. A comparative table (Table 1) summarizes the findings, highlighting that lightweight schemes (complex‑number masking, IHF) excel in efficiency but provide limited privacy guarantees, whereas heavyweight cryptographic solutions (SMPC/VSS, homomorphic MAC) deliver stronger guarantees at the expense of higher resource consumption.
Beyond the taxonomy, the authors critique the current state of research. Most evaluations rely on simulation or analytical models rather than real‑world hardware benchmarks (e.g., ARM Cortex‑M, ESP32). Key management, especially secure distribution and periodic refresh of symmetric keys, is often glossed over. Moreover, emerging paradigms such as blockchain‑based audit trails, federated learning for distributed analytics, and lattice‑based lightweight homomorphic encryption are not yet integrated into the surveyed literature.
In the concluding section, the paper outlines future research directions: (1) development of ultra‑lightweight homomorphic primitives and hardware‑assisted security modules (Trusted Execution Environments, Physically Unclonable Functions) for efficient key handling; (2) adaptive aggregation protocols that react to dynamic network topology, node failures, and varying privacy policies; (3) incorporation of anomaly detection and machine‑learning‑driven intrusion detection to complement cryptographic safeguards; and (4) establishment of standardized, reproducible benchmarks on actual IoT platforms to quantify trade‑offs between privacy, latency, and energy consumption.
Overall, this survey provides a valuable, up‑to‑date synthesis of PPDA mechanisms for constrained IoT nodes, clarifies the inherent trade‑offs between privacy strength and resource usage, and offers a roadmap for researchers aiming to design next‑generation, energy‑aware, privacy‑preserving aggregation solutions.
Comments & Academic Discussion
Loading comments...
Leave a Comment