Performance Evaluation of Cryptographic Ciphers on IoT Devices
With the advent of Internet of Things (IoT) and the increasing use of application-based processors, security infrastructure needs to be examined on some widely-used IoT hardware architectures. Applications in today’s world are moving towards IoT concepts as this makes them fast, efficient, modular and future-proof. However, this leads to a greater security risk as IoT devices thrive in an ecosystem of co-existence and interconnection. As a result of these security risks, it is of utmost importance to test the existing cryptographic ciphers on such devices and determine if they are viable in terms of swiftness of execution time and memory consumption efficiency. It is also important to determine if there is a requirement to develop new lightweight cryptographic ciphers for these devices. This paper hopes to accomplish the above-mentioned objective by testing various encryption-decryption techniques on different IoT based devices and creating a comparison of execution speeds between these devices for a variety of different data sizes. Keywords-Internet of things(IoT), application-based processors, security, encryption-decryption, speed, efficiency
💡 Research Summary
The paper conducts a systematic performance evaluation of several widely‑used cryptographic ciphers on representative Internet‑of‑Things (IoT) hardware platforms. The authors select three device classes that span the typical resource spectrum of IoT deployments: an 8‑bit AVR microcontroller (Atmega328P) representing ultra‑low‑power sensor nodes, a 32‑bit Cortex‑M4 microcontroller (STM32F407) as a mid‑range embedded processor, and an ARM Cortex‑A53 based single‑board computer (Raspberry Pi 3 Model B+) serving as a more capable edge gateway. For each platform the same C implementation is compiled with -O2 optimization and, where appropriate, the CMSIS‑DSP library to exploit any available hardware acceleration.
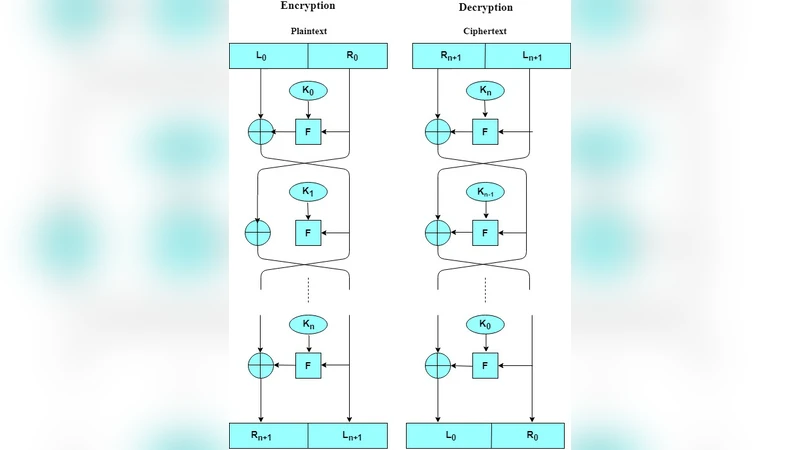
The cipher suite includes AES‑128 (ECB and CBC modes), DES, Triple‑DES, Blowfish, ChaCha20, and two lightweight block ciphers, SPECK‑64/128 and SIMON‑64/128. All algorithms follow their standard key lengths and round counts; key‑schedule and encryption/decryption phases are measured separately. Input data sizes range from 64 bytes to 16 kilobytes (64 B, 256 B, 1 KB, 4 KB, 16 KB), and each configuration is executed 100 times to obtain average execution time (milliseconds) and memory footprint (kilobytes).
Results reveal a pronounced performance gap between the high‑end SoC and the constrained microcontrollers. On the Cortex‑A53, every cipher processes 1 KB or less of data in under 0.1 ms and consumes less than 0.5 KB of RAM, indicating that, for edge devices, algorithm choice is less critical from a speed perspective. Conversely, on the AVR, AES‑CBC requires roughly 45 ms and 3.2 KB of RAM for a 16 KB payload, while ChaCha20 completes the same workload in about 38 ms using 2.8 KB of RAM, making the stream cipher modestly faster and more memory‑efficient. The lightweight ciphers SPECK and SIMON achieve sub‑5 ms encryption for 1 KB inputs on the AVR, but their key‑schedule routines inflate overall memory usage, negating some of the anticipated savings. Traditional DES and Triple‑DES, despite their small code size on low‑end MCUs, suffer from high computational cost and known security weaknesses, rendering them unsuitable for modern IoT security.
The discussion emphasizes several practical take‑aways. First, for severely resource‑constrained nodes, algorithms that minimize arithmetic operations and memory accesses—such as ChaCha20—outperform block ciphers in both latency and energy consumption. Second, implementation details (software‑only vs hardware‑assisted, choice of block mode) have a larger impact than the abstract algorithmic strength, underscoring the need for early profiling in the design cycle. Third, lightweight ciphers can reduce CPU cycles but may still demand non‑trivial RAM for key expansion; designers must balance code size, RAM usage, and security margins. Finally, the authors call for future work that integrates hardware cryptographic accelerators, evaluates mixed‑mode schemes (e.g., encrypt‑then‑authenticate), and explores post‑quantum lightweight primitives on IoT platforms.
In conclusion, the study demonstrates that security mechanisms for IoT cannot be selected solely on theoretical cryptographic robustness. Real‑world constraints—execution time, memory consumption, and power budget—must be quantified for each target device. The comprehensive benchmark data presented here provide developers and system architects with concrete guidance for choosing or designing ciphers that meet both security and performance requirements in the diverse IoT ecosystem.
Comments & Academic Discussion
Loading comments...
Leave a Comment