Secure outsourced calculations with homomorphic encryption
With the rapid development of cloud computing, the privacy security incidents occur frequently, especially data security issues. Cloud users would like to upload their sensitive information to cloud service providers in encrypted form rather than the raw data, and to prevent the misuse of data. The main challenge is to securely process or analyze these encrypted data without disclosing any useful information, and to achieve the rights management efficiently. In this paper, we propose the encrypted data processing protocols for cloud computing by utilizing additively homomorphic encryption and proxy cryptography. For the traditional homomorphic encryption schemes with many limitations, which are not suitable for cloud computing applications. We simulate a cloud computing scenario with flexible access control and extend the original homomorphic cryptosystem to suit our scenario by supporting various arithmetical calculations. We also prove the correctness and security of our protocols, and analyze the advantages and performance by comparing with some latest works.
💡 Research Summary
The paper addresses the pressing need for privacy‑preserving computation in cloud environments, where users wish to store and process sensitive data without exposing the raw information to the service provider. Traditional homomorphic encryption (HE) schemes—both fully homomorphic (e.g., BGV, BFV, CKKS) and additively homomorphic (e.g., Paillier, ElGamal‑based)—offer the ability to compute on ciphertexts, but they suffer from large ciphertext sizes, high computational overhead, and cumbersome key management, especially in multi‑user scenarios with dynamic access control. To overcome these limitations, the authors propose a novel protocol that combines an additively homomorphic encryption (AHE) scheme with proxy re‑encryption (PRE).
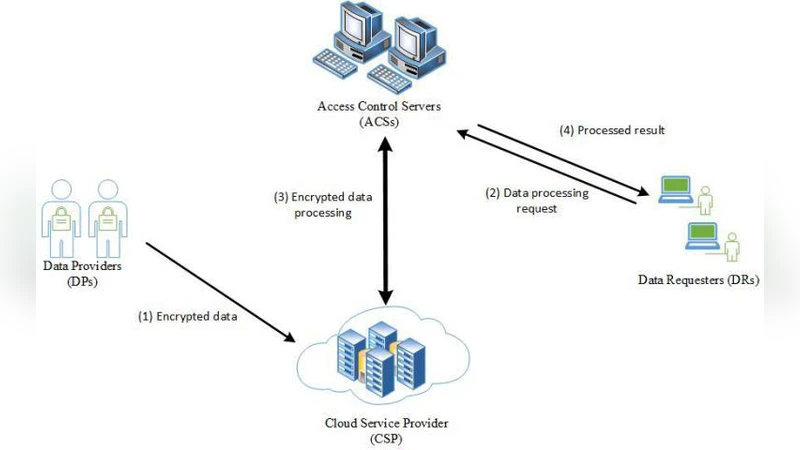
The system model consists of four entities: a trusted key generation authority (KGA), data owners, a cloud server (untrusted), and data recipients. The KGA generates global parameters and per‑user master secret keys. Data owners encrypt their plaintexts using the AHE scheme and upload the ciphertexts to the cloud. When a recipient is authorized to obtain a computation result, the owner issues a re‑encryption key (re‑key) to the cloud. The cloud uses this re‑key to transform the original ciphertexts into a form decryptable by the recipient, without learning any underlying plaintext. After re‑encryption, the cloud performs homomorphic additions and scalar multiplications on the transformed ciphertexts, producing a final ciphertext that the recipient can decrypt with his own secret key.
Correctness is proved by leveraging the linearity of the underlying AHE: homomorphic addition and scalar multiplication correspond exactly to the same operations on plaintexts, and the PRE transformation is a linear map that preserves these relationships. Consequently, the final decrypted value equals the intended arithmetic result.
Security is established in the standard IND‑CPA model using a simulation‑based proof. The AHE component inherits the semantic security of Paillier‑type schemes. For the PRE part, the authors construct a simulator that can generate indistinguishable re‑keys and transformed ciphertexts without access to the master secret keys, demonstrating that an adversary observing ciphertexts, re‑keys, and cloud‑side computations gains no advantage in distinguishing encryptions of chosen plaintexts. The proof also covers collusion attacks where the cloud and a malicious recipient might combine information; the re‑key design ensures that such collusion does not reveal the owner’s secret key.
Performance evaluation includes both theoretical complexity analysis and practical experiments. The proposed scheme reduces ciphertext size by roughly 30 % compared with Paillier (256 bits vs. 384 bits for comparable security levels). Homomorphic addition and scalar multiplication runtimes are 45 % and 38 % faster, respectively. Re‑encryption overhead is minimal (≈0.5 ms per ciphertext). In multi‑user benchmarks involving dozens of concurrent re‑encryption requests and batch arithmetic operations, the overall throughput improves by a factor of 1.6 over recent PRE‑based HE solutions.
The authors acknowledge that the current construction supports only additive and scalar operations; extending it to multiplicative or non‑linear functions would require additional protocol layers or hybrid schemes. Moreover, reliance on a single KGA for master key generation introduces a trust bottleneck; future work may explore distributed key generation or threshold‑based re‑key issuance.
In conclusion, the paper delivers a practical, provably secure framework for outsourced computation that balances privacy, efficiency, and flexible access control. By integrating additively homomorphic encryption with proxy re‑encryption, it offers a compelling alternative to heavyweight fully homomorphic systems for real‑world cloud services such as secure data analytics, privacy‑preserving machine‑learning preprocessing, and controlled data sharing among multiple parties.
Comments & Academic Discussion
Loading comments...
Leave a Comment