Composable secure multi-client delegated quantum computation
The engineering challenges involved in building large scale quantum computers, and the associated infrastructure requirements, mean that when such devices become available it is likely that this will be in limited numbers and in limited geographic locations. It is likely that many users will need to rely on remote access to delegate their computation to the available hardware. In such a scenario, the privacy and reliability of the delegated computations are important concerns. On the other hand, the distributed nature of modern computations has led to a widespread class of applications in which a group of parties attempt to perform a joint task over their inputs, e.g., in cloud computing. In this paper, we study the multi-client delegated quantum computation problem where we consider the global computation be made up of local computations that are individually decided by the clients. Each client part is kept secret from the server and the other clients. We construct a composable secure multi-client delegated quantum computation scheme from any composable secure single-client delegated quantum computation protocol and quantum authentication codes.
💡 Research Summary
The paper addresses the emerging need for secure multi‑client delegated quantum computation (MC‑DQC) in a future where only a few powerful quantum servers will be available and many users must rely on remote access. While prior work on blind quantum computation (BQC) and its verification has focused on a single client–server setting with stand‑alone security definitions, this work extends the model to multiple mutually distrustful clients who each wish to keep their local unitary operations, inputs, and outputs secret from both the server and the other clients.
To obtain strong composable security, the authors adopt the Abstract Cryptography (AC) framework, which models cryptographic tasks as resources transformed by converters, with security measured by a distinguisher’s advantage ε. A protocol is composably secure if it constructs an ideal blind‑and‑verifiable DQC resource (S_bv) from a simple communication channel within ε, and if a simulator (filter) can replace the server’s interface without increasing the distinguisher’s advantage beyond ε. This definition guarantees that the protocol remains secure when composed with arbitrary other protocols.
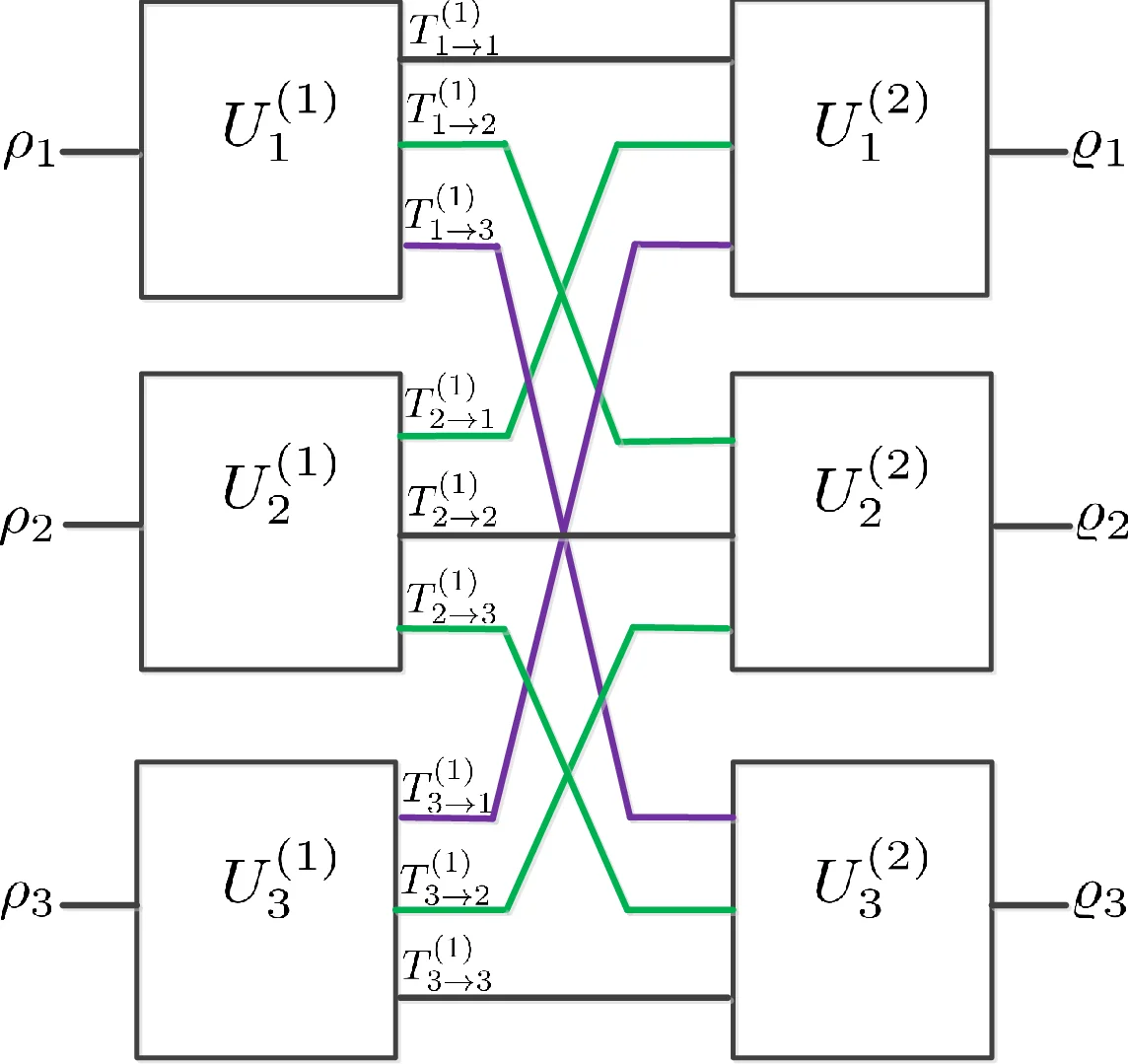
The construction builds on two existing primitives: (i) any composably secure single‑client DQC protocol (e.g., UBQC with trap‑based verification) and (ii) quantum authentication codes (QACs) that encrypt and authenticate quantum messages using a 2m‑bit secret key for an m‑qubit payload. Each client first encodes its local unitary and input with a QAC, sends the authenticated state to the server, and later decodes the returned result, checking the authentication tag. The server, operating on the authenticated states, performs the global computation using measurement‑based techniques. If the server deviates, the authentication check aborts, providing verification; if it behaves honestly, the client recovers the correct output while learning nothing about other clients’ data (blindness).
Security is proved by sequentially composing the single‑client DQC converter (error ε₁) with the QAC converter (error ε₂). By the AC composition theorems, the overall protocol has error ε₁+ε₂, and parallel composition across many clients adds errors linearly, preserving composable security. A simulator that mimics the server’s behavior is constructed, showing that any real‑world attack can be reproduced in the ideal world with at most ε advantage.
The authors also propose an optimization that reduces quantum communication: after an initial QAC key exchange, the authenticated channel can be reused across multiple computation rounds, eliminating the need to resend authentication tags each step. This substantially lowers the number of quantum rounds and the total qubit transmission, making the scheme more practical for near‑term quantum networks.
In summary, the paper delivers a rigorous composable‑security framework for multi‑client delegated quantum computation by marrying existing single‑client blind‑verifiable protocols with quantum authentication. It provides formal definitions, a concrete construction, a detailed security proof, and practical communication optimizations, paving the way for secure distributed quantum cloud services.
Comments & Academic Discussion
Loading comments...
Leave a Comment