State-of-the-Art Survey on In-Vehicle Network Communication (CAN-Bus) Security and Vulnerabilities
Nowadays with the help of advanced technology, modern vehicles are not only made up of mechanical devices but also consist of highly complex electronic devices and connections to the outside world. There are around 70 Electronic Control Units (ECUs) in modern vehicle which are communicating with each other over the standard communication protocol known as Controller Area Network (CAN-Bus) that provides the communication rate up to 1Mbps. There are different types of in-vehicle network protocol and bus system namely Controlled Area Network (CAN), Local Interconnected Network (LIN), Media Oriented System Transport (MOST), and FlexRay. Even though CAN-Bus is considered as de-facto standard for in-vehicle network communication, it inherently lacks the fundamental security features by design like message authentication. This security limitation has paved the way for adversaries to penetrate into the vehicle network and do malicious activities which can pose a dangerous situation for both driver and passengers. In particular, nowadays vehicular networks are not only closed systems, but also they are open to different external interfaces namely Bluetooth, GPS, to the outside world. Therefore, it creates new opportunities for attackers to remotely take full control of the vehicle. The objective of this research is to survey the current limitations of CAN-Bus protocol in terms of secure communication and different solutions that researchers in the society of automotive have provided to overcome the CAN-Bus limitation on different layers.
💡 Research Summary
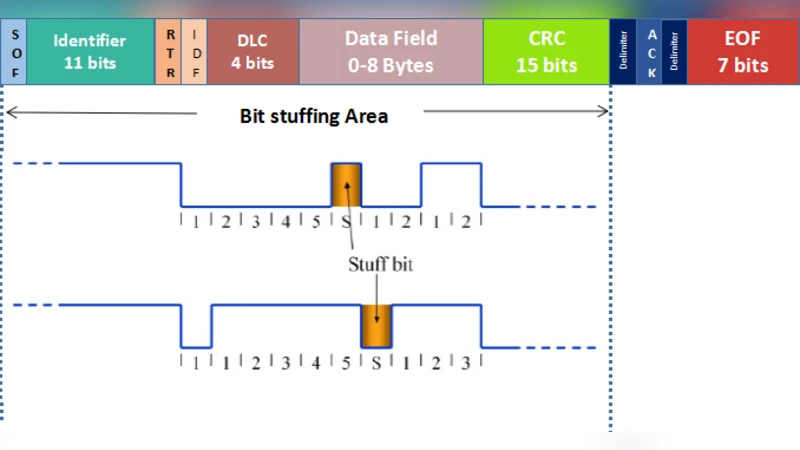
The paper provides a comprehensive survey of the security shortcomings of the Controller Area Network (CAN‑Bus) that underpins modern automotive communication and reviews state‑of‑the‑art countermeasures across protocol layers. It begins with a technical overview of CAN‑Bus, describing its broadcast‑oriented arbitration, 11‑bit and 29‑bit identifiers, bit‑stuffing, and differential signaling (recessive 2.5 V, dominant 3.5 V/1.5 V). While these features deliver low cost, high reliability, and deterministic real‑time behavior, the protocol was designed without any built‑in authentication, confidentiality, or integrity mechanisms.
The authors enumerate five fundamental security objectives—data integrity, authentication, confidentiality, non‑repudiation, and availability—and illustrate how CAN‑Bus fails to meet any of them. Specific attack vectors are detailed: (1) spoofing and replay attacks, where an adversary mimics a legitimate ECU’s identifier to inject malicious frames; (2) passive eavesdropping, enabled by the unencrypted, plain‑text traffic that can be captured with inexpensive hardware; (3) denial‑of‑service (DoS) via priority abuse, where a low‑ID (high‑priority) frame is transmitted continuously to monopolize the bus; and (4) exploitation of external interfaces such as Bluetooth, GPS, OBD‑II, and infotainment systems that provide remote footholds.
The survey then categorizes existing mitigation strategies into three layers. At the physical/transfer layer, clock‑skew based ECU fingerprinting (Cho & Shin) leverages the minute timing errors inherent to each microcontroller. By modeling each ECU’s clock behavior with a Recursive Least Squares algorithm, deviations are flagged as intrusions, achieving a false‑positive rate of only 0.055 % in tests on multiple vehicle models.
At the network/application layer, the VeCure framework (Wang et al.) introduces a two‑tier trust model (high‑trust vs. low‑trust ECUs) and augments every CAN frame with an 8‑byte Message Authentication Code (MAC) derived from SHA‑3. To keep latency low, the heavy hash computation is performed offline, reducing the on‑board cost to an additional 2 000 CPU cycles (≈50 µs on a 40 MHz processor), a twenty‑fold speed improvement over naïve implementations.
Empirical attack studies by Koscher et al. demonstrate real‑world exploitation paths: physical access via the OBD‑II port, malware injection through malicious audio files in infotainment units, and wireless attacks using Bluetooth, RFID (Keeloq), and GPS. Paar et al. further expose the vulnerability of remote keyless entry systems based on Keeloq, showing that they can be compromised from a distance.
While these works significantly raise the security bar, the authors stress the inherent trade‑off between added cryptographic overhead and the stringent timing constraints of automotive control loops. Extra MAC bytes consume bus bandwidth, and cryptographic processing taxes limited ECU resources. Consequently, the paper calls for future research on lightweight cryptography, hardware‑accelerated security modules, and multi‑layer collaborative IDS/IPS architectures that can deliver robust protection without jeopardizing real‑time performance. The authors conclude that automotive manufacturers must embed security considerations early in the design phase and pursue standardized, OTA‑compatible security frameworks to safeguard the increasingly connected vehicle ecosystem.
Comments & Academic Discussion
Loading comments...
Leave a Comment