SD-WAN Threat Landscape
Software Defined Wide Area Network (SD-WAN or SDWAN) is a modern conception and an attractive trend in network technologies. SD-WAN is defined as a specific application of software-defined networking (SDN) to WAN connections. There is growing recognition that SDN and SD-WAN technologies not only expand features, but also expose new vulnerabilities. Unfortunately, at the present time, most vendors say that SD-WAN are perfectly safe, hardened, and fully protected. The goal of this paper is to understand SD-WAN threats using practical approach. We describe basic SD-WAN features and components, investigate an attack surface, explore various vendor features and their security, explain threats and vulnerabilities found in SD-WAN products. We also extend existing SDN threat models by describing new potential threats and attack vectors, provide examples, and consider high-level approaches for their mitigations. The provided results may be used by SD-WAN developers as a part of Secure Software Development Life Cycle (SSDLC), security researchers for penetration testing and vulnerability assessment, system integrators for secure design of SD-WAN solutions, and finally customers for secure deployment operations and configurations of SD-WAN enabled network. The main idea of this work is that SD-WAN threat model involves all traditional network and SDN threats, as well as new product-specific threats, appended by vendors which reinvent or introduce proprietary technologies immature from a security perspective.
💡 Research Summary
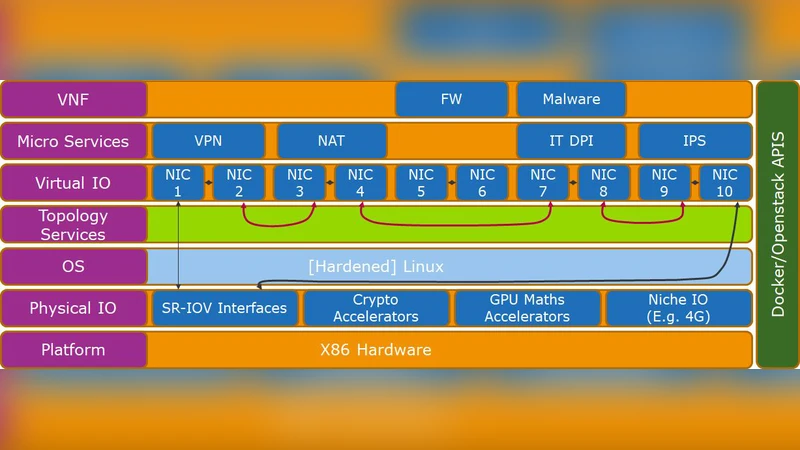
The paper presents a comprehensive examination of the security threat landscape surrounding Software‑Defined Wide Area Networks (SD‑WAN). It begins by defining SD‑WAN as an application of Software‑Defined Networking (SDN) principles to WAN connectivity, describing its core components: a centralized orchestration platform (often cloud‑based), SD‑WAN controllers, edge appliances (virtual routers or hardware boxes), and the underlying transport links to traditional routers and switches. This architecture introduces three distinct attack surfaces—management, control, and data planes—each with its own set of vulnerabilities.
In the management plane, administrators interact with the system via web consoles, RESTful APIs, CLI, and mobile apps. Weak authentication, inadequate session handling, and insufficient role‑based access control can allow an adversary to enumerate the entire network topology, modify routing policies, or exfiltrate configuration data. Multi‑tenant SaaS orchestrators are especially prone to classic web‑application flaws such as CSRF, XSS, insecure cookies, and API rate‑limit bypasses.
The control plane mirrors the SDN controller’s responsibilities, making decisions about routing, policy enforcement, and traffic steering. Communication between the controller and edge devices typically relies on TLS/DTLS, yet many vendors implement proprietary encryption schemes or allow encryption to be disabled for performance reasons. This opens the door to man‑in‑the‑middle attacks, packet tampering, and the injection of malicious policies that can reroute or sniff traffic. Moreover, the controller’s plugin architecture can expose additional CVEs when third‑party modules are used without rigorous vetting.
The data plane carries user traffic and inherits traditional threats such as DDoS, packet sniffing, and IP spoofing. SD‑WAN adds new vectors: distributed traffic‑optimisation engines can be subverted to create “stealth tunnels” that bypass security controls, and compromised edge devices can leak tunnel configuration files, enabling attackers to craft arbitrary paths that traverse internal networks undetected. Mis‑implemented load‑balancing or path‑selection algorithms can also be abused to concentrate traffic on a single link, causing a denial‑of‑service condition.
Vendor‑specific implementations further diversify the risk profile. Some vendors ship hardware‑based cryptographic modules but provide cumbersome firmware‑update mechanisms that lack proper signature verification, making them vulnerable to supply‑chain attacks. Others promote “zero‑touch provisioning” while transmitting initial authentication tokens in clear text or leaving default admin credentials unchanged, creating low‑effort footholds for attackers. These proprietary weaknesses are not captured by generic SDN threat models and therefore require a dedicated “proprietary‑risk” category.
Building on this analysis, the authors extend existing SDN threat frameworks with five novel SD‑WAN‑specific vectors: (1) misuse or abuse of orchestration APIs, (2) cross‑tenant policy contamination in multi‑tenant deployments, (3) theft of automated provisioning scripts or templates, (4) firmware supply‑chain compromises of edge appliances, and (5) privilege‑escalation scenarios arising from integration with cloud‑native services. For each vector, concrete attack scenarios, impact assessments, and likelihood ratings are provided.
Mitigation recommendations are organized into four pillars. First, strong authentication and authorization: enforce multi‑factor authentication, adopt least‑privilege principles, implement role‑based access control, and rotate signed API tokens regularly. Second, mandatory encryption and integrity verification: require TLS 1.3 or higher for all inter‑plane traffic, and replace proprietary crypto with standards‑compliant protocols where possible. Third, secure supply‑chain practices: enforce digitally signed firmware, enable secure boot, and verify image integrity during over‑the‑air updates. Fourth, continuous monitoring and threat detection: centralize logs, employ behavior‑based anomaly detection, and integrate zero‑trust network access (ZTNA) to enforce dynamic, context‑aware policies.
Finally, the paper advocates embedding these controls within a Secure Software Development Life Cycle (SSDLC) for SD‑WAN products. Threat modeling should be performed early, static and dynamic code analyses applied during development, and rigorous penetration testing conducted before deployment. Post‑deployment, organizations must maintain a regular patching cadence, conduct periodic red‑team exercises, and have an incident‑response playbook tailored to SD‑WAN environments. By following this holistic approach, operators can reap the agility and cost benefits of SD‑WAN while mitigating both traditional network threats and the emerging, product‑specific vulnerabilities identified in this study.
Comments & Academic Discussion
Loading comments...
Leave a Comment