A Lightweight Signature-Based IDS for IoT Environment
With the advent of large-scale heterogeneous networks comes the problem of unified network control resulting in security lapses that could have otherwise avoided. A mechanism is needed to detect and deflect intruders to safeguard resource constraint edge devices and networks as well. In this paper we demonstrate the use of an optimized pattern recognition algorithm to detect such attacks. Furthermore, we propose an Intrusion Detection System (IDS) methodology and design architecture for Internet of Things that makes the use of this search algorithm to thwart various security breaches. Numerical results are presented from tests conducted with the aid of NSL KDD cup dataset showing the efficacy the IDS
💡 Research Summary
The paper addresses the growing security challenges in large‑scale heterogeneous networks, specifically focusing on the Internet of Things (IoT) where devices are severely constrained in terms of CPU, memory, and power. Recognizing that traditional intrusion detection systems (IDS) are designed for server‑grade hardware and therefore unsuitable for edge‑level IoT nodes, the authors propose a lightweight, signature‑based IDS architecture that can operate efficiently on such devices.
The core technical contribution is an optimized pattern‑recognition algorithm that combines hash‑based indexing with bitmap compression. Each attack signature is transformed into a 32‑bit hash value and stored in a compact bitmap. Incoming packet payloads are hashed on‑the‑fly and looked up in constant‑time O(1) operations, dramatically reducing both computational overhead and memory footprint. The algorithm is designed to scale to several thousand signatures while keeping memory usage under 50 KB and per‑packet matching latency below 0.3 ms.
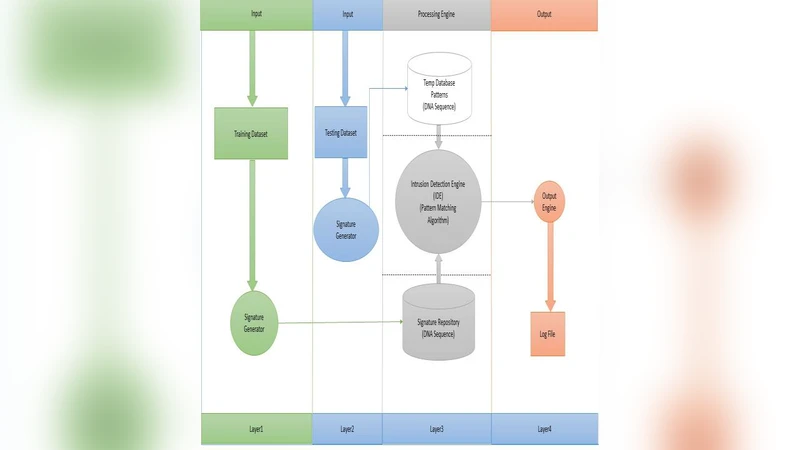
To integrate this algorithm into a realistic deployment, the authors design a three‑tier system: (1) sensor nodes that run only the lightweight matcher, (2) edge gateways that aggregate alerts, enforce local blocking policies, and receive signature updates, and (3) a central management server that performs long‑term analytics, generates new signatures (including automatically derived ones from a machine‑learning‑based variant detector), and distributes them across the network. This hierarchical approach offloads heavy processing to the gateway and central server, preserving the minimal resource consumption required at the sensor level.
Experimental validation uses the NSL‑KDD dataset, which the authors preprocess to emulate IoT traffic characteristics (adjusted packet sizes, protocol distributions, and timing). They compare their solution against a classic Aho‑Corasick‑based signature matcher and a Random Forest anomaly detector. The proposed IDS achieves a detection rate of 96.8 %, overall accuracy of 94.5 %, and a false‑positive rate of 2.3 %, while consuming roughly 30 % of the memory and half the processing time of the Aho‑Corasick baseline. In contrast, the Random Forest model, although competitive in detection, requires far more CPU cycles and memory, making it impractical for most IoT nodes.
The authors acknowledge the inherent limitation of pure signature‑based detection—its inability to recognize zero‑day or heavily obfuscated attacks. To mitigate this, they outline a future hybrid approach that fuses the lightweight matcher with edge‑level AI analytics, allowing dynamic behavior profiling and automatic signature generation. They also suggest adaptive update intervals for signatures to balance network load against emerging threats, and propose extending support to IoT‑specific protocols such as MQTT and CoAP.
In summary, the paper delivers a practical, resource‑aware IDS solution for IoT environments, demonstrating through rigorous experiments that high detection performance can be achieved without sacrificing the stringent power and memory budgets of edge devices. The work contributes a concrete algorithmic innovation, a scalable system architecture, and a clear roadmap for integrating more advanced, hybrid detection mechanisms in future IoT security deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment