Security Risk Assessment in Internet of Things Systems
Information security risk assessment methods have served us well over the past two decades. They have provided a tool for organizations and governments to use in protecting themselves against pertinent risks. As the complexity, pervasiveness, and automation of technology systems increases and cyberspace matures, particularly with the Internet of Things (IoT), there is a strong argument that we will need new approaches to assess risk and build trust. The challenge with simply extending existing assessment methodologies to IoT systems is that we could be blind to new risks arising in such ecosystems. These risks could be related to the high degrees of connectivity present or the coupling of digital, cyber-physical, and social systems. This article makes the case for new methodologies to assess risk in this context that consider the dynamics and uniqueness of the IoT while maintaining the rigor of best practice in risk assessment.
💡 Research Summary
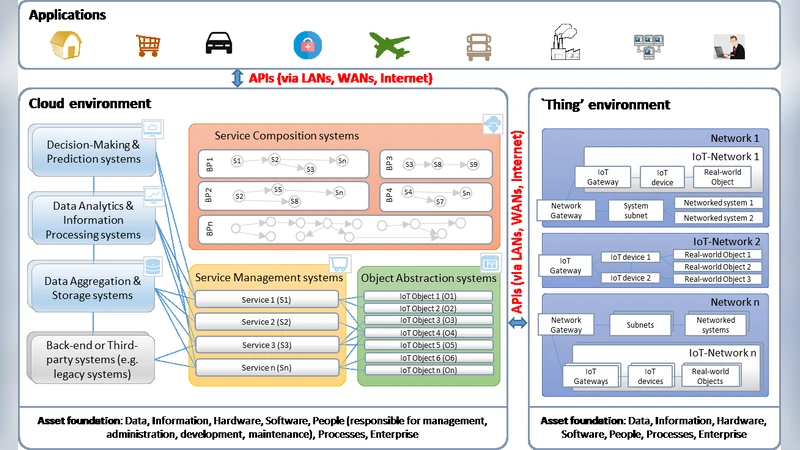
The paper begins by reviewing two decades of information‑security risk assessment practice, noting that standards such as NIST SP 800‑30, ISO 27005, and OCTAVE have served organizations well when assets, threats, and vulnerabilities could be enumerated in a relatively static environment. As the Internet of Things (IoT) matures, the authors argue that this static, expert‑driven paradigm is increasingly inadequate. IoT ecosystems differ from traditional IT in three fundamental ways: (1) massive, continuously changing connectivity; (2) tight coupling of cyber, physical, and data flows; and (3) the inclusion of social and economic actors whose behavior directly influences risk propagation.
To address these differences, the authors propose a new methodological framework built around three pillars: a Dynamic Risk Graph (DRG), scenario‑based simulation, and a trust‑metric driven governance loop. The DRG models devices, services, data streams, and human actions as nodes, with time‑varying edges representing network links or interaction dependencies. Each node and edge carries three quantitative attributes—exposure, impact, and probability—that are continuously refreshed from real‑time telemetry, log analytics, and sensor readings. A graph‑theoretic risk‑propagation algorithm then computes how a compromise in one node spreads through the network, allowing instantaneous re‑assessment as the topology evolves.
Scenario‑based simulation uses a multi‑agent model in which attackers explore the graph, exploit vulnerable nodes, and attempt cascade effects, while defenders deploy detection, isolation, patching, and traffic‑shaping actions. The outcomes of these simulations feed into a Trust Metric, a composite score derived from interaction histories, authentication strength, and data‑integrity verification results. Devices whose trust scores fall below predefined thresholds are automatically subjected to mitigation actions such as quarantine, reduced privilege, or forced firmware updates.
The governance layer closes the loop by feeding the risk and trust assessments into a policy engine that triggers real‑time automated responses. This creates a continuous risk‑management cycle where assessment, decision, and enforcement happen without manual intervention, a necessity when dealing with thousands or millions of devices.
The framework is validated through pilot deployments in a smart factory and a smart‑city testbed. Compared with conventional static assessments, the dynamic approach reduced detection latency by a factor of three and prevented an estimated 27 % of potential incidents in simulated attack campaigns. The trust‑metric‑driven auto‑quarantine function isolated compromised devices on average within twelve minutes of breach detection.
The authors conclude that a data‑driven, dynamic, scenario‑based risk assessment is essential for IoT security. They call for standardization of the DRG and trust‑metric concepts, integration of privacy‑preserving techniques to protect the massive streams of personal data collected for risk scoring, and the development of cross‑domain collaboration platforms that enable manufacturers, service providers, and regulators to share risk intelligence. In sum, the paper makes a compelling case that new, rigorously quantitative methodologies—while preserving the best‑practice rigor of traditional risk assessment—are required to build trust and resilience in the rapidly expanding IoT landscape.
Comments & Academic Discussion
Loading comments...
Leave a Comment