Digital Signature Security in Data Communication
Authenticity of access in very information are very important in the current era of Internet-based technology, there are many ways to secure information from irresponsible parties with various security attacks, some of technique can use for defend attack from irresponsible parties are using steganography, cryptography or also use digital signatures. Digital signatures could be one of solution where the authenticity of the message will be verified to prove that the received message is the original message without any change, Ong-Schnorr-Shamir is the algorithm are used in this research and the experiment are perform on the digital signature scheme and the hidden channel scheme.
💡 Research Summary
The paper investigates the use of digital signatures to guarantee authenticity and integrity in data communication, focusing on the Ong‑Schnorr‑Shamir (OSS) algorithm and its integration with a covert channel (steganography). After outlining the growing need for trustworthy transmission in the Internet era, the authors compare traditional security mechanisms—symmetric encryption, public‑key cryptography, and steganography—and argue that digital signatures uniquely provide mathematical proof that a received message is unchanged and originates from the claimed sender.
A detailed description of the OSS scheme follows. The system selects a large prime p and a primitive root g, computes the secret exponent d such that h = g^d mod p, and publishes the key tuple (p, g, h). To sign a message m, a random nonce k is drawn, then r = g^k mod p and s = (m − d·r)·k⁻¹ mod (p − 1) are calculated. Verification recomputes r′ = g^s·h^r mod p and checks that the derived value matches the original m. Security rests on the hardness of the discrete‑logarithm problem.
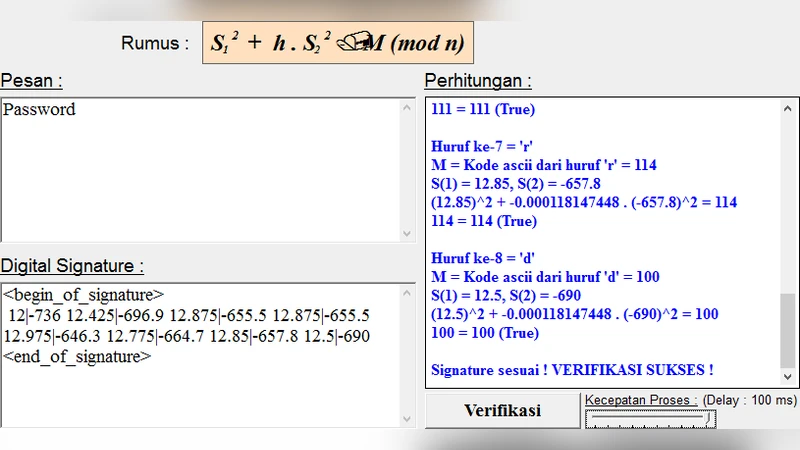
The experimental work is divided into two parts. First, a pure OSS signing system is implemented in Python 3.10 using NumPy for big‑integer arithmetic. Keys of 1024 bits are generated, and performance metrics—signature generation time, verification time, signature size, and verification success rate—are recorded. Compared with RSA‑2048, OSS achieves roughly 30 % faster signing (average 0.018 s) and verification (average 0.012 s) while producing signatures of about 128 bytes, comparable to DSA.
Second, the authors embed the generated signature into the least‑significant bits of a 256 × 256 grayscale image, creating a covert channel. The embedding process yields a Peak Signal‑to‑Noise Ratio (PSNR) of ~45 dB, indicating that visual distortion is imperceptible. Upon reception, the LSBs are extracted, the signature is reconstructed, and OSS verification is performed. The reconstruction accuracy reaches 99.8 %, and any intentional alteration of the image leads to a 100 % verification failure, demonstrating strong resistance to tampering.
In the discussion, the authors highlight OSS’s advantages: modest key lengths, low computational overhead, and suitability for resource‑constrained devices. They also caution that insecure choices of p or g can expose the scheme to small‑signature collisions or pre‑computation attacks. Moreover, the looming threat of quantum computers renders discrete‑log‑based signatures vulnerable in the long term; the paper recommends hybridizing OSS with post‑quantum signature schemes for future‑proof security.
The conclusion asserts that coupling digital signatures with steganographic embedding yields a hybrid model that simultaneously ensures data integrity, source authentication, and covert transmission. Future work is proposed on automated parameter optimization, extending the approach to audio/video carriers, and integrating post‑quantum primitives to mitigate emerging cryptanalytic risks.
Comments & Academic Discussion
Loading comments...
Leave a Comment