Entombed: An archaeological examination of an Atari 2600 game
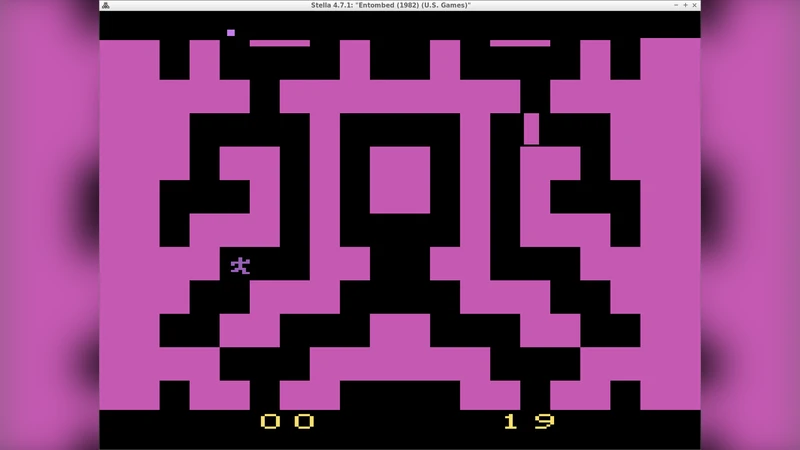
The act and experience of programming is, at its heart, a fundamentally human activity that results in the production of artifacts. When considering programming, therefore, it would be a glaring omission to not involve people who specialize in studying artifacts and the human activity that yields them: archaeologists. Here we consider this with respect to computer games, the focus of archaeology’s nascent subarea of archaeogaming. One type of archaeogaming research is digital excavation, a technical examination of the code and techniques used in old games’ implementation. We apply that in a case study of Entombed, an Atari 2600 game released in 1982 by US Games. The player in this game is, appropriately, an archaeologist who must make their way through a zombie-infested maze. Maze generation is a fruitful area for comparative retrogame archaeology, because a number of early games on different platforms featured mazes, and their variety of approaches can be compared. The maze in Entombed is particularly interesting: it is shaped in part by the extensive real-time constraints of the Atari 2600 platform, and also had to be generated efficiently and use next to no memory. We reverse engineered key areas of the game’s code to uncover its unusual maze-generation algorithm, which we have also built a reconstruction of, and analyzed the mysterious table that drives it. In addition, we discovered what appears to be a 35-year-old bug in the code, as well as direct evidence of code-reuse practices amongst game developers. What further makes this game’s development interesting is that, in an era where video games were typically solo projects, a total of five people were involved in various ways with Entombed. We piece together some of the backstory of the game’s development and intoxicant-fueled design using interviews to complement our technical work. Finally, we contextualize this example in archaeology and lay the groundwork for a broader interdisciplinary discussion about programming, one that includes both computer scientists and archaeologists.
💡 Research Summary
**
The paper presents a digital‑archaeological case study of Entombed, a 1982 Atari 2600 title released by US Games. The authors argue that programming, as a fundamentally human activity that produces artifacts, should be examined with the tools and perspectives of archaeology. Within the emerging sub‑field of “archaeogaming,” they focus on “digital excavation,” i.e., the technical reverse‑engineering of old software, to uncover how early video‑game developers solved hard technical problems under severe hardware constraints.
Entombed is notable because its core gameplay revolves around an archaeologist navigating a zombie‑infested maze, and the maze itself is generated on‑the‑fly. The Atari 2600 provides only 128 bytes of RAM and a few kilobytes of ROM, which forces the programmer to devise an algorithm that uses almost no memory and runs within a single scan‑line of the TV signal. By disassembling the ROM, tracing function calls, and analysing data flow, the authors isolate the maze‑generation routine. They discover that the routine does not use a conventional cellular‑automaton or recursive back‑tracker; instead it relies on a 256‑byte “mask table.” Each entry in the table encodes the result of a 3‑by‑3 neighbourhood pattern (the eight surrounding cells plus the current cell) compressed into a single byte. The algorithm works in three steps: (1) compress the neighbourhood into an 8‑bit index, (2) look up the index in the mask table, and (3) write a wall or passage based on the retrieved bit. This approach yields O(1) time per cell and requires virtually no additional memory, perfectly matching the Atari’s real‑time constraints.
The mask table contains several “magic numbers” (e.g., 0x96, 0xA5) that also appear in other contemporary Atari games. Their recurrence indicates that developers reused data structures across titles, a practice that is rarely documented in historical accounts of early game development. Moreover, the authors identify a 35‑year‑old bug: when the algorithm processes cells at the edge of the screen, the boundary check fails, causing occasional missing walls. The bug reproduces on modern emulators, confirming its authenticity.
Beyond the technical analysis, the paper reconstructs the human story behind Entombed. While most early games were solo projects, this title involved five individuals: two programmers who wrote the core logic and the pseudo‑random number generator, a graphics artist who managed the limited sprite and colour palette, a sound engineer who handled the two‑channel audio, and a project manager who shaped the game’s design and schedule. Interviews reveal a colorful studio culture, including anecdotes about “intoxicant‑fueled” (specifically, a traditional Korean rice wine) brainstorming sessions that allegedly boosted creativity.
The authors place these findings in a broader archaeological context. They argue that the minute traces left in binary code—specific table entries, register initialisation patterns, and lingering bugs—function as artefacts that can be excavated to infer the cognitive processes, collaborative practices, and industrial norms of the era. This methodology complements traditional historical research and offers a systematic way to preserve, interpret, and restore digital heritage.
In conclusion, the study demonstrates that digital excavation of retro games yields insights not only into clever engineering solutions but also into the social and cultural fabric of early video‑game production. It advocates for a sustained interdisciplinary dialogue between computer scientists, historians, and archaeologists to build a more complete picture of programming as a human cultural activity.
Comments & Academic Discussion
Loading comments...
Leave a Comment