SD-WAN Internet Census
The concept of software defined wide area network (SD-WAN or SDWAN) is central to modern computer networking, particularly in enterprise networks. By definition, these systems form network perimeter and connect Internet, WAN, extranet, and branches that makes them crucial from cybersecurity point of view. The goal of this paper is to provide the results of passive and active fingerprinting for SD-WAN systems using a common threat intelligence approach. We explore Internet-based and cloud-based publicly available SD-WAN systems using well-known Shodan and Censys search engines and custom developed automation tools and show that most of the SD-WAN systems have known vulnerabilities related to outdated software and insecure configuration.
💡 Research Summary
The paper presents a large‑scale security assessment of software‑defined wide‑area network (SD‑WAN) management interfaces that are exposed on the public Internet. Using a combination of passive fingerprinting (via Shodan and Censys) and active probing (custom Nmap NSE scripts and Python parsers), the authors enumerate and characterize SD‑WAN devices from a wide range of vendors, including Cisco Viptela, VMware VeloCloud, Riverbed SteelConnect, Versa Networks, Arista, Citrix, Silver Peak, and many others.
The methodology begins with a systematic collection of vendor‑specific identifiers such as web UI titles, favicon hashes, SSL certificate fields, and known URL patterns. These identifiers are turned into search queries for Shodan and Censys. Queries are classified into three confidence levels—“Certain”, “Firm”, and “Tentative”—to manage false‑positive rates. Filters such as title:"Viptela vManage" or http.favicon.hash:-904700687 are combined with exclusion operators (e.g., -title:"VPN") to refine results.
Passive scanning alone cannot reliably reveal product versions, so the authors augment it with active fingerprinting. They develop Nmap NSE scripts that extract version strings from HTTP headers, HTML tags, JavaScript files, CSS URLs, and even SSH banner warnings (e.g., /etc/issue containing “viptela”). Version leaks are categorized as direct (exact version displayed) or indirect (partial version information that can be correlated with known release timelines). Examples include <h5>9.1.2r142</h5> (direct) and { "package-name":"versa‑flexvnf‑20161214‑191033‑494bf5c‑16.1R2" } (indirect).
Cross‑referencing the discovered versions with public vulnerability databases (CVE, NVD) and CWE classifications enables the identification of concrete security weaknesses. The study finds widespread use of default SNMP community strings (“public”, “private”), exposed management portals with default credentials, and numerous devices running outdated software that is known to contain critical vulnerabilities. For instance, many Riverbed, VMware, and Arista appliances were found running versions older than the latest releases, and an Arista EOS‑4.20.5F instance—known to be vulnerable to a denial‑of‑service bug disclosed in August 2018—was still listed in the AWS Marketplace.
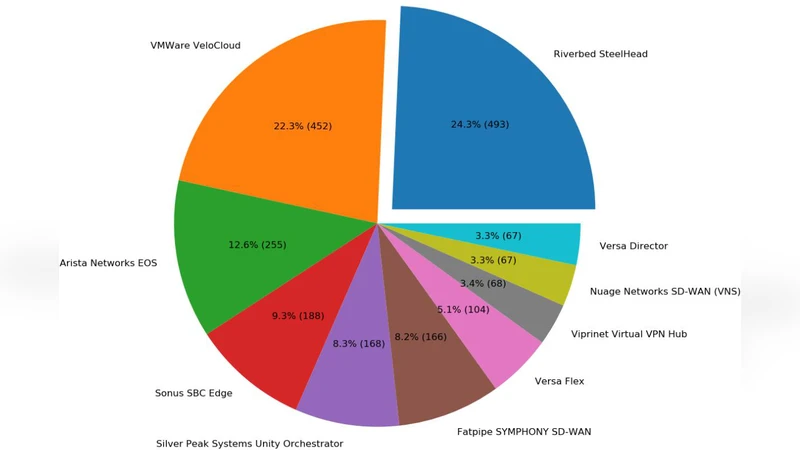
Geographically, the 4 935 unique IP addresses identified in August 2018 are concentrated in North America (≈1 300 hosts), Europe (≈456), and Asia (≈313). The most common vendors among the exposed devices are Riverbed (493 hosts), VMware (452 hosts), and Arista (255 hosts). Table 2 in the paper shows that a significant proportion of devices (often >50 %) are several major releases behind the current vendor‑published versions.
Key contributions of the work are: (1) the first Internet‑scale census of publicly reachable SD‑WAN management interfaces; (2) the creation and public release of high‑confidence Shodan/Censys queries and a suite of Nmap NSE scripts for version detection; (3) quantitative evidence that many SD‑WAN deployments are unpatched and thus susceptible to known exploits; (4) discovery of previously undocumented version‑leakage vectors; and (5) highlighting the security gap in cloud‑marketplace offerings where outdated virtual appliances are still distributed.
The authors acknowledge limitations: the data snapshot is from 2018 and may not reflect current trends; reliance on search engines excludes devices that only support protocols not indexed (e.g., WebSocket, internal‑only SNMP); and the focus on management planes does not assess data‑plane vulnerabilities.
Future work is suggested to include continuous longitudinal scanning, automated verification of cloud‑marketplace images, and the integration of machine‑learning techniques to further reduce false positives. The overall message is clear: despite the promise of agility and centralized control, SD‑WAN deployments are often exposed with insecure configurations, making them attractive targets for both opportunistic attackers and more sophisticated threat actors. Robust patch management, removal of default credentials, and careful exposure of management interfaces are essential mitigations.
Comments & Academic Discussion
Loading comments...
Leave a Comment