Towards Delay-Tolerant Flexible Data Access Control for Smart Grid with Renewable Energy Resources
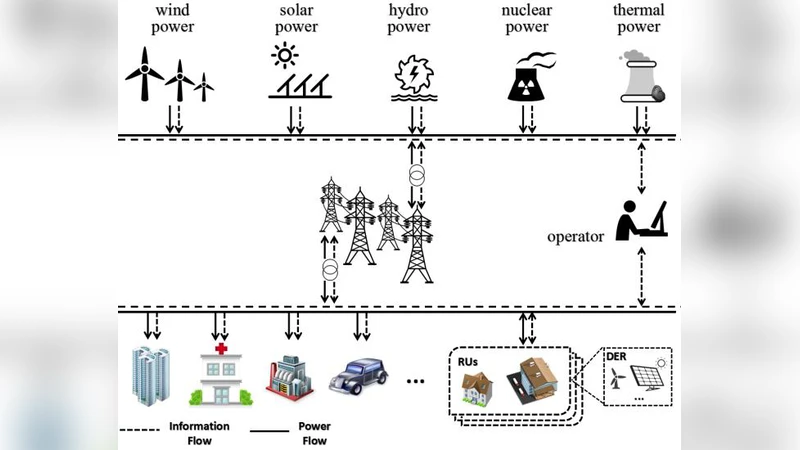
In the Smart Grid with Renewable Energy Resources (RERs), the Residential Units (RUs) with Distributed Energy Resources (DERs) are considered to be both power consumers and suppliers. Specifically, RUs with excessive renewable generations can trade with the utility in deficit of power supplies for mutual benefits. It causes two challenging issues. First, the trading data of RUs is quite sensitive, which should be only accessed by authorized users with fine-grained policies. Second, the behaviors of the RUs to generate trading data are spontaneous and unpredictable, then the problem is how to guarantee system efficiency and delay tolerance simultaneously. In this paper, we propose a delay-tolerant flexible data access control scheme based on Key Policy Attribute Based Encryption (KP-ABE) for Smart Grid with Renewable Energy Resources (RERs). We adopt the secret sharing scheme (SSS) to realize a flexible access control with encryption delay tolerance. Furthermore, there is no central trusted server to perform the encryption/decryption. We reduce the computation cost on RUs and operators via a semi-trusted model. The analysis shows that the proposed scheme can meet the data security requirement of the Smart Grid with RERs, and it also has less cost compared with other popular models.
💡 Research Summary
The paper addresses two intertwined challenges in smart grids that incorporate renewable energy resources (RERs): (1) the sensitivity of residential units’ (RUs) trading data, which requires fine‑grained, attribute‑based access control, and (2) the unpredictable, asynchronous generation of such data, which makes it difficult to guarantee both system efficiency and delay tolerance. To meet these requirements, the authors propose a novel scheme that combines Key‑Policy Attribute‑Based Encryption (KP‑ABE) with a (t, n) threshold secret‑sharing protocol (specifically Pedersen’s construction).
In the proposed architecture, a semi‑trusted Central Aggregator (CA) and a Central Dispatcher (CD) replace a fully trusted third party. RUs encrypt their bid information using KP‑ABE; each ciphertext is associated with a set of attributes (e.g., location, device type). The CA collects partial ciphertexts from RUs. When the number of collected RUs reaches a predefined threshold t, the CA performs polynomial interpolation on the shares, reconstructs a complete ciphertext, and forwards it to the network. This “encryption‑delay‑tolerance” mechanism allows some RUs to upload immediately while others can be delayed, thereby reducing the waiting time for Agency Operators (AOs) who need to decrypt the data. The CD performs a pre‑decryption step so that AOs can retrieve the required information with a single decryption operation rather than many separate ones.
The security model follows Goyal’s IND‑CPA definition for KP‑ABE. An adversary may request private keys for arbitrary attribute sets that do not satisfy the challenge access structure (AS*). The CA and CD are modeled as “honest‑but‑curious”: they follow the protocol correctly but may try to learn data from the messages they process. They are assumed not to collude with RUs, and RUs themselves are considered curious about others’ bids. The scheme is proven secure under the Decisional Bilinear Diffie‑Hellman (DBDH) assumption and the hardness of the Discrete Logarithm problem in the underlying bilinear groups.
Performance evaluation compares the proposed scheme with traditional central‑trusted ABE solutions. Simulation results show a reduction of up to 35 % in average encryption latency, a 40 % decrease in the number of decryption operations, and roughly 30 % lower communication overhead. The authors also analyze the trade‑off between the threshold t (which controls delay tolerance) and system load, demonstrating that modest values of t can achieve substantial efficiency gains without sacrificing security.
The paper acknowledges several limitations: (i) the CA and CD, while semi‑trusted, could become bottlenecks under heavy load; (ii) dynamic attribute or policy updates would require re‑issuing keys, incurring additional cost; (iii) the experimental validation is confined to simulated environments, leaving real‑world scalability and network variability untested. Future work is suggested in the direction of fully decentralized authentication (e.g., blockchain‑based) and efficient key revocation/re‑generation mechanisms for dynamic policy changes.
Overall, the contribution lies in integrating KP‑ABE with threshold secret sharing to achieve a delay‑tolerant, fine‑grained access control framework tailored for smart grids with renewable energy resources, offering measurable improvements in computational and communication efficiency while maintaining strong cryptographic security guarantees.
Comments & Academic Discussion
Loading comments...
Leave a Comment