Security Services Using Blockchains: A State of the Art Survey
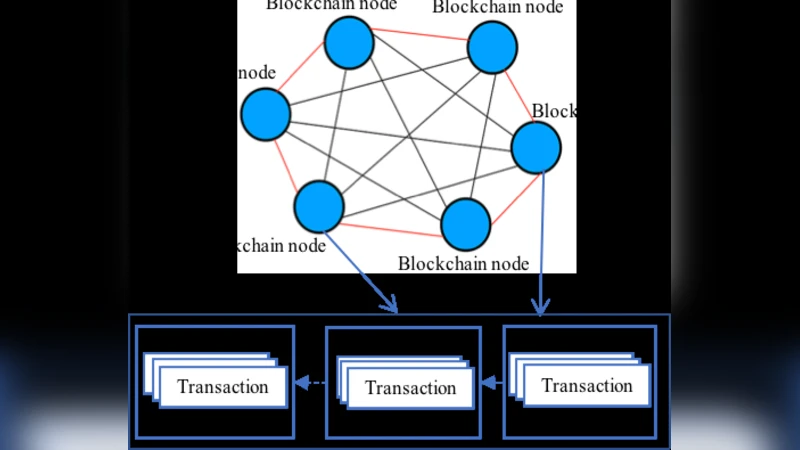
This article surveys blockchain-based approaches for several security services. These services include authentication, confidentiality, privacy, and access control list (ACL), data and resource provenance, and integrity assurance. All these services are critical for the current distributed applications, especially due to the large amount of data being processed over the networks and the use of cloud computing. Authentication ensures that the user is who he/she claims to be. Confidentiality guarantees that data cannot be read by unauthorized users. Privacy provides the users the ability to control who can access their data. Provenance allows an efficient tracking of the data and resources along with their ownership and utilization over the network. Integrity helps in verifying that the data has not been modified or altered. These services are currently managed by centralized controllers, for example, a certificate authority. Therefore, the services are prone to attacks on the centralized controller. On the other hand, blockchain is a secured and distributed ledger that can help resolve many of the problems with centralization. The objectives of this paper are to give insights on the use of security services for current applications, to highlight the state of the art techniques that are currently used to provide these services, to describe their challenges, and to discuss how the blockchain technology can resolve these challenges. Further, several blockchain-based approaches providing such security services are compared thoroughly. Challenges associated with using blockchain-based security services are also discussed to spur further research in this area.
💡 Research Summary
The surveyed paper provides a comprehensive review of how blockchain technology can be employed to deliver core security services—authentication, confidentiality, privacy, access‑control lists (ACL), provenance, and integrity assurance—in modern distributed environments such as cloud, IoT, and big‑data platforms. It begins by outlining the shortcomings of traditional centralized security infrastructures, notably single points of failure, certificate authority compromises, and limited auditability. The authors then categorize blockchain‑based approaches into six functional groups.
For authentication, the paper highlights decentralized identity (DID) frameworks and zero‑knowledge proof (ZKP) schemes that let users self‑manage credentials on an immutable ledger, eliminating reliance on a central certificate authority. Confidentiality solutions typically combine strong encryption with off‑chain storage (e.g., IPFS) and store only cryptographic hashes or pointers on the chain; access rights are enforced by smart contracts that reject unauthorized requests. Privacy‑preserving techniques include ring signatures, mixnets, and ZKPs, which enable “prove‑only‑what‑is‑necessary” interactions without revealing user identities or transaction details. ACL mechanisms are re‑implemented as on‑chain smart contracts supporting role‑based (RBAC) and attribute‑based (ABAC) policies; policy updates are automatically propagated and can trigger on‑chain penalties. Provenance is achieved by recording metadata and hash digests for every data creation, modification, and transfer event, thereby providing an immutable audit trail that clarifies ownership and usage history. Integrity assurance leverages Merkle trees and chain‑linked verification to ensure that stored data has not been tampered with, with the blockchain itself serving as the ground truth.
The authors compare each blockchain‑based solution with its conventional counterpart across dimensions such as consensus algorithm (PoW, PoS, BFT), network type (public, private, consortium), throughput, cost, privacy level, and regulatory compliance. They note that public blockchains offer maximal transparency and security but suffer from limited scalability and higher transaction fees, whereas private or consortium chains improve performance and privacy at the expense of a more complex trust model.
A substantial portion of the paper is devoted to open challenges. Scalability remains a critical bottleneck for high‑frequency authentication or ACL updates; smart‑contract vulnerabilities introduce new attack vectors; advanced cryptographic primitives (e.g., ZKPs) lack mature standards and interoperability; immutable ledgers clash with legal “right‑to‑be‑forgotten” requirements such as GDPR; and the impending threat of quantum computers calls for post‑quantum cryptography integration.
To address these issues, the authors propose future research directions including hybrid on‑chain/off‑chain architectures, formal verification of smart contracts, differential privacy mechanisms that balance transparency with data minimization, and designs that support reversible or redactable entries to satisfy regulatory mandates. In conclusion, while blockchain offers a powerful foundation for enhancing trust, auditability, and decentralization of security services, its practical adoption will depend on solving the identified technical, legal, and operational hurdles.
Comments & Academic Discussion
Loading comments...
Leave a Comment