Detecting Bot Activity in the Ethereum Blockchain Network
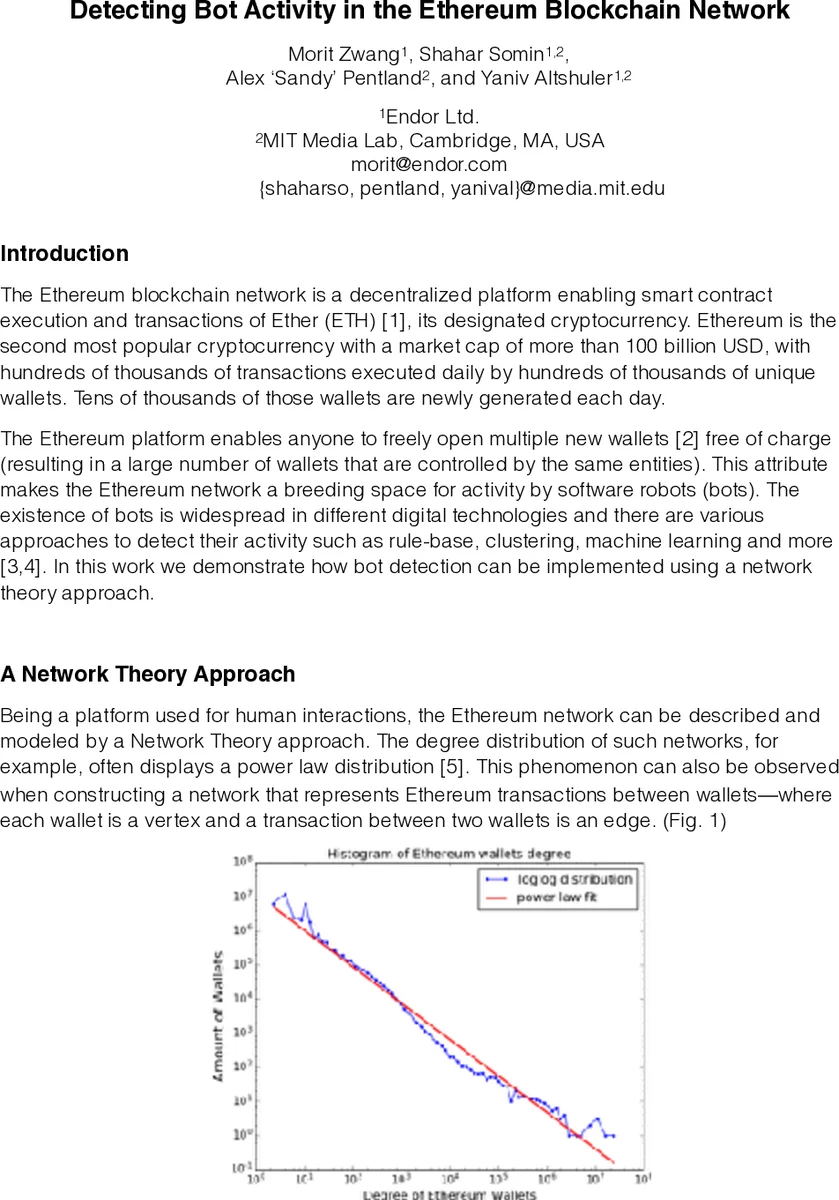
The Ethereum blockchain network is a decentralized platform enabling smart contract execution and transactions of Ether (ETH) [1], its designated cryptocurrency. Ethereum is the second most popular cryptocurrency with a market cap of more than 100 billion USD, with hundreds of thousands of transactions executed daily by hundreds of thousands of unique wallets. Tens of thousands of those wallets are newly generated each day. The Ethereum platform enables anyone to freely open multiple new wallets [2] free of charge (resulting in a large number of wallets that are controlled by the same entities). This attribute makes the Ethereum network a breeding space for activity by software robots (bots). The existence of bots is widespread in different digital technologies and there are various approaches to detect their activity such as rule-base, clustering, machine learning and more [3,4]. In this work we demonstrate how bot detection can be implemented using a network theory approach.
💡 Research Summary
The paper presents a novel, network‑theory‑driven method for detecting automated bot activity on the Ethereum blockchain. Recognizing that Ethereum’s open‑access wallet creation allows a single entity to control many addresses, the authors argue that this environment is fertile ground for software bots that execute transactions without human intervention. While prior bot‑detection work has largely relied on rule‑based systems, clustering, or machine learning, the authors exploit a unique property of blockchain data: every transaction is publicly recorded with precise timestamps, enabling a straightforward statistical analysis of temporal patterns.
Methodologically, the authors construct an undirected graph where vertices represent wallets and edges represent transactions. For each wallet they compute the time difference, in minutes, between consecutive transactions, then aggregate these differences across all wallets to produce a global histogram. The bulk of the distribution follows a power‑law (heavy‑tailed) shape, consistent with prior findings on human‑driven activity such as email communication and call‑center logs. This confirms that ordinary human users generate bursts of activity that decay according to a power‑law.
Crucially, the histogram exhibits several pronounced spikes that deviate from the smooth power‑law curve. The authors categorize these spikes into two types. “Periodic anomalies” appear at regular intervals (24 h, 48 h, 72 h, etc.) regardless of the sampling window. By extracting the transactions responsible for these spikes, the authors discover that they correspond to mining‑pool reward distributions. Mining pools schedule payouts at fixed times, sending identical amounts to many participant wallets, thereby creating a deterministic temporal pattern that stands out against the stochastic human background.
“Irregular anomalies” are spikes that occur only during a specific time window. The paper highlights a spike at a 1,032‑minute interval (≈17 h) observed exclusively on May 18 2018. Transactions underlying this spike belong to a large set of newly created wallets that participated in a token airdrop. Airdrops are commonly executed by bots that generate many fresh addresses to claim free tokens, resulting in a burst of transactions with identical timing and value.
From these observations the authors draw several key insights. First, while human‑driven activity conforms to a power‑law, bot‑driven activity introduces deterministic, highly correlated transaction bursts that manifest as outliers in the temporal distribution. Second, detecting these outliers does not require sophisticated machine‑learning pipelines; a simple statistical test for deviations from the expected power‑law suffices to flag suspicious clusters of wallets. Third, the network‑theory framework is extensible: incorporating additional dimensions such as transaction value, recipient address clustering, or smart‑contract interaction patterns can refine detection and reduce false positives.
The paper’s contribution lies in demonstrating that the inherent transparency of blockchain data can be leveraged for lightweight, yet effective, bot detection. By interpreting deviations from a power‑law as signatures of non‑human behavior, the authors provide a practical tool for analysts, regulators, and platform operators to monitor and mitigate malicious automation. The authors suggest future work that integrates multi‑feature anomaly detection, applies the methodology to other blockchains (e.g., Bitcoin, Polkadot), and explores real‑time monitoring pipelines. Overall, the study bridges network science and blockchain analytics, offering a parsimonious alternative to existing complex bot‑identification systems while highlighting the security implications of automated activity in decentralized finance ecosystems.
Comments & Academic Discussion
Loading comments...
Leave a Comment