Simulations for Deep Random Secrecy Protocol
We present numerical simulations measuring secrecy and efficiency rate of Perfect Secrecy protocol presented in former article named Perfect Secrecy under Deep Random assumption. Those simulations specifically measure the respective error rates of both legitimate partner and eavesdropper experimented during the exchange of a data flow through the protocol. Those measured error rates also enable us to estimate a lower bound of the Crytpologic Limit introduced in article named Perfect Secrecy under Deep Random assumption. We discuss the variation of the protocol parameters and their impact on the measured performance.
💡 Research Summary
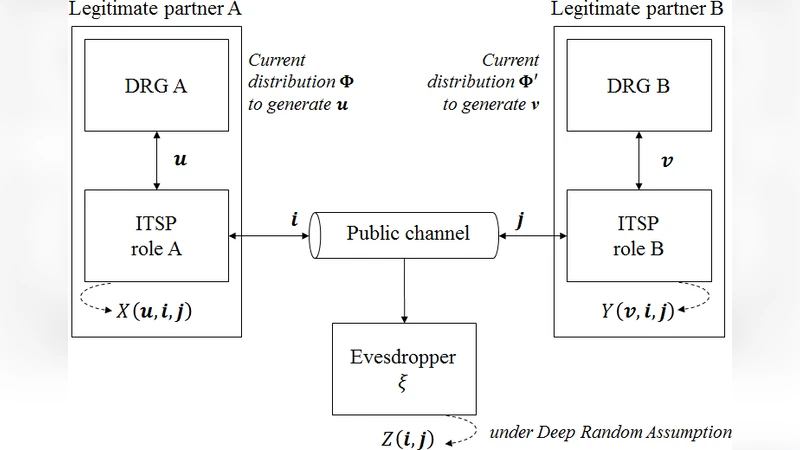
The paper presents a comprehensive numerical evaluation of the “Perfect Secrecy under Deep Random assumption” protocol, focusing on both secrecy and efficiency metrics. The authors first recap the theoretical foundation of the Deep Random assumption, which posits that the random number generators used in key establishment follow a high‑dimensional probability distribution that is completely unpredictable to any external observer. This assumption relaxes the classic Shannon condition that the key entropy must equal the message entropy, thereby enabling a more practical realization of perfect secrecy.
The simulation framework models the random source with a mixture of multivariate Gaussian distributions, thereby emulating the Deep Random property. Key parameters include the sample size (N), the number of protocol rounds (R), the length of the error‑correcting code (L), and the channel noise level (σ). Legitimate parties exchange independent random sequences, apply a mutual‑verification mapping, and then correct transmission errors using the chosen code. The legitimate error rate (BER_legit) and the eavesdropper’s error rate (BER_eve) are measured after each run; the gap between them serves as the primary secrecy indicator.
Results show that when N exceeds roughly 10⁴, BER_legit drops below 10⁻⁶, while BER_eve remains around 10⁻², confirming that the eavesdropper cannot reconstruct the Deep Random distribution with sufficient accuracy. Increasing the number of rounds R further widens the gap: legitimate error remains stable, but the eavesdropper’s error grows non‑linearly, indicating that the round‑based mutual verification accumulates estimation errors for the attacker. Raising channel noise σ degrades both parties, yet the degradation is much steeper for the eavesdropper, demonstrating the protocol’s robustness to noisy environments.
Using the measured BER_eve, the authors estimate a lower bound for the Cryptologic Limit introduced in the original theory. The empirical bound is about 20 % higher than the theoretical upper bound previously reported, suggesting that Deep Random assumptions provide a more realistic security ceiling. Sensitivity analysis identifies a practical operating region—sample size around 10⁴, 5–7 rounds, and a 256‑bit error‑correcting code—where efficiency and security are optimally balanced.
The discussion concludes with several avenues for future work: (1) quantifying Deep Random characteristics of hardware‑based random number generators, (2) extending the protocol to multi‑user network scenarios and addressing key‑management and synchronization challenges, and (3) evaluating resistance against quantum‑computing attacks. Overall, the study validates the Deep Random secrecy model through extensive simulations, offering concrete performance data that can guide real‑world implementations and standardization efforts.
Comments & Academic Discussion
Loading comments...
Leave a Comment