Sharing Information with Competitors
We study the mechanism design problem in the setting where agents are rewarded using information only. This problem is motivated by the increasing interest in secure multiparty computation techniques. More specifically, we consider the setting of a joint computation where different agents have inputs of different quality and each agent is interested in learning as much as possible while maintaining exclusivity for information. Our high level question is to design mechanisms that motivate all agents (even those with high-quality input) to participate in the computation and we formally study problems such as set union, intersection, and average.
💡 Research Summary
The paper tackles a novel mechanism design problem in which agents are rewarded solely with information rather than money. This setting is motivated by the rapid advances in secure multiparty computation (SMPC) that enable parties to jointly compute functions on private inputs, yet the question of why rational agents would voluntarily participate has received little attention. The authors model each participant’s utility as a combination of two competing preferences: (i) correctness, i.e., the desire to acquire as much new information as possible, and (ii) exclusivity, i.e., the desire to keep the information they obtain from being widely shared. Formally, for agent i the information gain after a mechanism M is denoted v_i, and the utility is defined as u_i = v_i − max_{j≠i} v_j. This captures the “envy” an agent feels toward the best‑informed peer and reflects the tension between learning and protecting one’s informational advantage.
The authors focus on three concrete joint‑computation tasks: (1) multiparty set union, (2) interval intersection, and (3) point‑average. In each case the goal is to compute a non‑boolean function (the union of sets, a common point in intervals, or the arithmetic mean) while respecting the agents’ informational preferences. The analysis is primarily carried out in an “all‑or‑nothing” model: each agent either submits its entire private input or refuses to participate. The model assumes that inputs cannot be forged (e.g., via digital signatures) and that a trusted mediator (or a cryptographic protocol that emulates one) runs the mechanism.
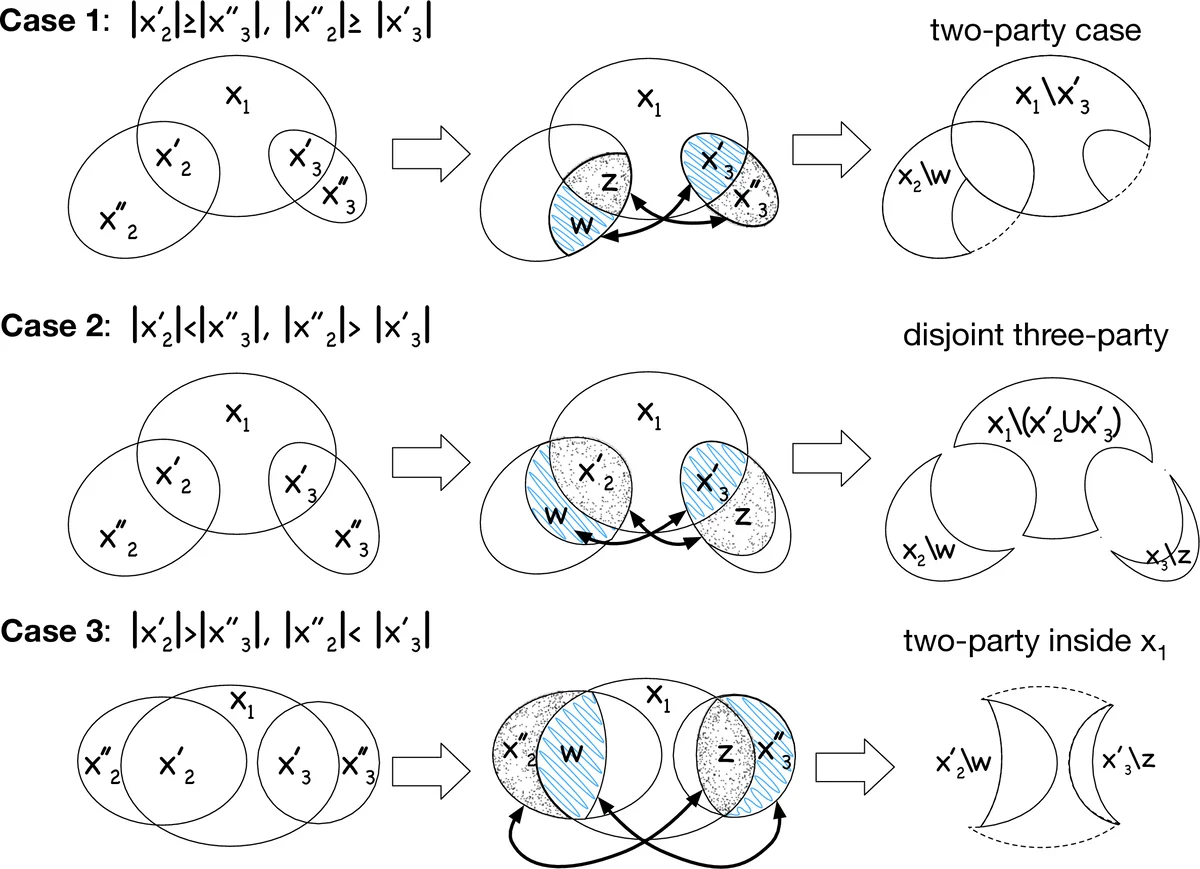
Key contributions are encapsulated in four theorems. Theorem 1.1 presents a truthful, Pareto‑efficient mechanism for set union among three agents, using a round‑by‑round exchange where each round guarantees that every participant receives more new elements than it contributes. Theorem 1.2 extends this to any fixed number n of all‑or‑nothing agents, delivering a mechanism that is truthful, Pareto‑efficient, welfare‑maximizing, treats equally‑contributing agents identically, and rewards higher contributors more. Theorem 1.3 addresses interval intersection: each agent holds a connected interval on the real line, and the mechanism finds a point in the common intersection while preserving truthfulness and Pareto efficiency. Theorem 1.4 handles the point‑average problem, again achieving truthfulness and efficiency for any number of all‑or‑nothing participants. An additional general result (Appendix C) shows how to handle arbitrary value functions beyond simple set cardinalities.
The technical core lies in quantifying each agent’s marginal contribution to the collective information pool and designing allocation rules that compensate agents at least as much as the loss they would impose on others by abstaining. This “no‑regret” condition ensures that no rational agent has an incentive to deviate, thereby guaranteeing truthfulness. Because information can be duplicated at negligible cost, the total surplus is not fixed, distinguishing the setting from classic cooperative game solutions such as the Shapley value, which assume a fixed pie. Consequently, the mechanisms must explicitly specify which pieces of information are transferred, not merely how much “value” is distributed.
The paper situates its work relative to several strands of literature. It extends the non‑cooperative computation (NCC) and informational mechanism design (IMD) frameworks, which previously focused on Boolean functions and monetary or binary correctness utilities. It also differs from works on information as substitutes/complements in prediction markets, and from rational secret‑sharing protocols that rely on cryptographic tricks to enforce participation. By incorporating exclusivity directly into the utility, the authors capture realistic competitive scenarios such as firms sharing overlapping training data, stock‑prediction models, or social‑media influencers exchanging follower lists.
Limitations are acknowledged. The reliance on the all‑or‑nothing model sidesteps the more intricate strategic choices agents could make when they can partially reveal information. The existence of a trusted mediator is assumed, and cryptographic implementation details are left for future work. Moreover, the simple linear utility u_i = v_i − max_j v_j may not fully capture nuanced real‑world preferences for privacy or strategic withholding.
In summary, the paper pioneers the study of non‑monetary mechanism design where information itself is the currency. It provides concrete, polynomial‑time mechanisms for several natural joint‑computation tasks that are truthful, Pareto‑efficient, and welfare‑optimal under the all‑or‑nothing assumption. By formalizing the trade‑off between learning and exclusivity, it opens a new avenue for designing incentive‑compatible protocols that could make SMPC technologies practically viable in competitive environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment