BLAG: Bandit On Large Action Set Graph
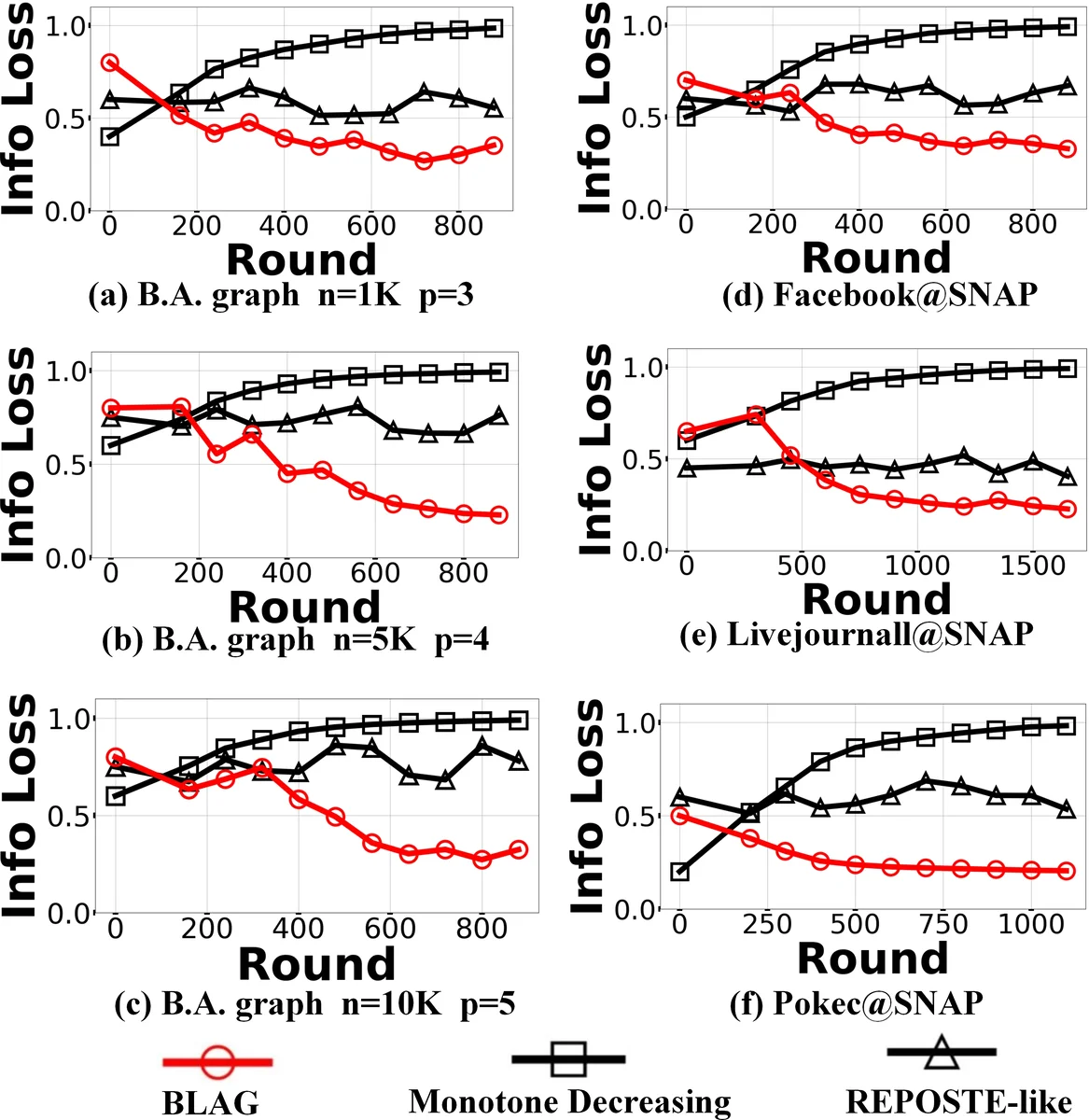
Information diffusion in social networks facilitates rapid and large-scale propagation of content. However, spontaneous diffusion behavior could also lead to the cascading of sensitive information, which is neglected in prior arts. In this paper, we present the first look into adaptive diffusion of sensitive information, which we aim to prevent from widely spreading without incurring much information loss. We undertake the investigation in networks with partially known topology, meaning that some users’ ability of forwarding information is unknown. Formulating the problem into a bandit model, we propose BLAG (Bandit on Large Action set Graph), which adaptively diffuses sensitive information towards users with weak forwarding ability that is learnt from tentative transmissions and corresponding feedbacks. BLAG enjoys a low complexity of O(n), and is provably more efficient in the sense of half regret bound compared with prior learning method. Experiments on synthetic and three real datasets further demonstrate the superiority of BLAG in terms of adaptive diffusion of sensitive information over several baselines, with at least 40 percent less information loss, at least 10 times of learning efficiency given limited learning rounds and significantly postponed cascading of sensitive information.
💡 Research Summary
The paper tackles the problem of preventing the uncontrolled spread of sensitive information in large social networks where the topology is only partially known. In many real‑world platforms, the one‑hop neighborhoods of a substantial fraction of users are unknown, making it impossible to directly apply diffusion control methods that assume full network knowledge. The authors model each user’s forwarding ability by its degree (higher degree implies stronger forwarding) and aim to steer the diffusion so that low‑degree (weak‑forwarding) users receive more sensitive content while high‑degree users receive less, thereby reducing the overall cascade of sensitive information without sacrificing too much non‑sensitive traffic.
To formalize this adaptive diffusion, the authors map the problem onto a constrained combinatorial multi‑arm bandit (CCMAB). In each round a “trial” corresponds to a transmission policy represented by a probability‑adjustment vector Δβ applied to the edges that connect sensitive nodes to uninformed non‑sensitive nodes. The objective is to minimize the inner product D·(β₀ + Δβ), where D is the (unknown) degree vector of the target nodes and β₀ is the baseline transmission probability. The bandit formulation includes:
- Base‑actions – vectors that simultaneously decrease the probability on one edge and increase it on another by the same amount, keeping the total probability mass unchanged. Each base‑action has exactly two non‑zero components that sum to zero.
- Super‑actions – feasible combinations of base‑actions. A combination is valid only if, after applying all adjustments, every edge’s probability stays within the
Comments & Academic Discussion
Loading comments...
Leave a Comment