Cyber-Security in Smart Grid: Survey and Challenges
Smart grid uses the power of information technology to intelligently deliver energy to customers by using a two-way communication, and wisely meet the environmental requirements by facilitating the integration of green technologies. Although smart grid addresses several problems of the traditional grid, it faces a number of security challenges. Because communication has been incorporated into the electrical power with its inherent weaknesses, it has exposed the system to numerous risks. Several research papers have discussed these problems. However, most of them classified attacks based on confidentiality, integrity, and availability, and they excluded attacks which compromise other security criteria such as accountability. In addition, the existed security countermeasures focus on countering some specific attacks or protecting some specific components, but there is no global approach which combines these solutions to secure the entire system. The purpose of this paper is to provide a comprehensive overview of the relevant published works. First, we review the security requirements. Then, we investigate in depth a number of important cyber-attacks in smart grid to diagnose the potential vulnerabilities along with their impact. In addition, we proposed a cyber security strategy as a solution to address breaches, counter attacks, and deploy appropriate countermeasures. Finally, we provide some future research directions.
💡 Research Summary
The paper provides a comprehensive survey of cyber‑security issues in the modern smart grid, emphasizing that while the integration of information‑technology (IT) and two‑way communication brings unprecedented flexibility, efficiency, and renewable‑energy integration, it also introduces significant cyber‑risk due to the inherent weaknesses of communication infrastructures. The authors first review the security requirements defined by the National Institute of Standards and Technology (NIST), namely confidentiality, integrity, and availability (the classic CIA triad), and argue that accountability (or non‑repudiation) must be added as a fourth essential criterion because sophisticated attacks often aim to hide their footprints and impede forensic analysis.
The survey then examines the smart‑grid architecture as defined by NIST, which consists of seven logical domains (bulk generation, transmission, distribution, customer, markets, service provider, and operations). Within this framework, the paper focuses on three critical subsystems—Advanced Metering Infrastructure (AMI), Supervisory Control and Data Acquisition (SCADA), and substation automation—detailing their components, communication protocols, and typical deployment scenarios. For AMI, the authors note that smart meters, head‑end servers, and the underlying wireless links (ZigBee, Z‑Wave, etc.) often lack authentication and encryption, making them vulnerable to eavesdropping, spoofing, and data manipulation. In SCADA, the reliance on legacy industrial protocols such as Modbus and Distributed Network Protocol 3.0 (DNP3) is highlighted; both were originally designed without security features, exposing the system to session hijacking, command injection, and replay attacks. The paper also discusses IEC 61850, the standard for substation communication, pointing out that while it offers rich data models, many implementations omit mandatory integrity checks, creating exploitable gaps.
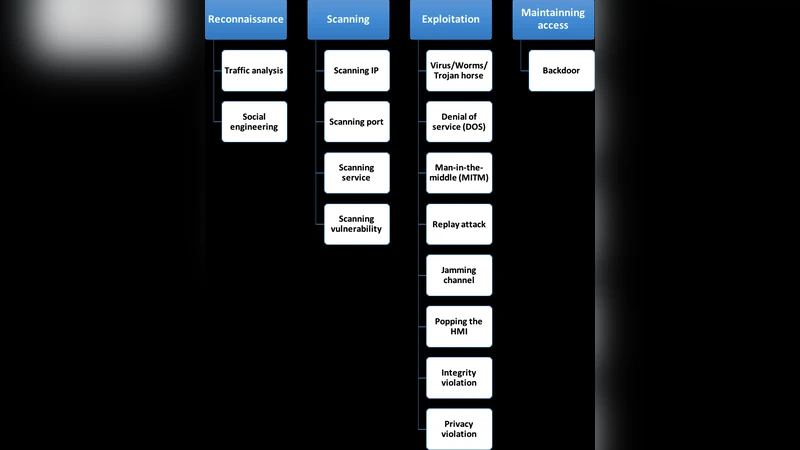
A major contribution of the work is the analysis of cyber‑attacks that target these components. The authors categorize attacks not only by the CIA impact but also by the attacker’s methodology: reconnaissance, infiltration, control, and destruction. Using this taxonomy, they illustrate how blended threats such as Stuxnet, Duqu, and Flame can simultaneously compromise confidentiality, integrity, and availability, thereby escaping detection by traditional CIA‑centric classification schemes. Specific attack vectors discussed include power‑injection attacks that corrupt state‑estimator measurements, denial‑of‑service (DoS) attacks that disrupt real‑time control traffic, and malware that propagates through insecure Modbus/TCP sessions.
In response to the identified gaps, the paper proposes a holistic, multi‑layered security framework. At the network layer, it recommends intrusion detection and prevention systems (IDS/IPS), encrypted tunnels (TLS/VPN), and secure routing protocols. At the host and system layer, it advocates for rigorous patch management, hardened operating systems, and the principle of least privilege. At the application layer, the authors suggest the deployment of digital signatures, hash‑based integrity verification, robust key‑management, and certificate‑based authentication. To achieve accountability, they emphasize comprehensive logging, secure log storage, and the potential use of blockchain‑based immutable ledgers for tamper‑evident audit trails.
Finally, the paper outlines future research directions: (1) the development of AI/ML‑driven anomaly detection with higher precision and lower false‑positive rates; (2) exploration of quantum‑resistant cryptographic schemes for next‑generation grid communications; (3) creation of large‑scale testbeds that emulate the full smart‑grid stack for realistic security testing; and (4) continuous evolution of standards and regulatory frameworks through international collaboration. By integrating these recommendations, the authors aim to move the smart‑grid security paradigm from fragmented, component‑specific solutions toward a unified, end‑to‑end protection strategy capable of withstanding both current and emerging cyber threats.
Comments & Academic Discussion
Loading comments...
Leave a Comment