Comments On "A New Transient Attack On The Kish Key Distribution System"
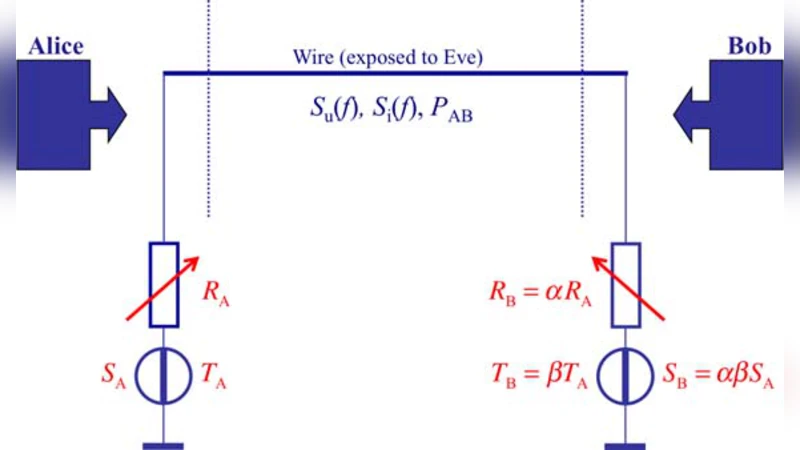
A recent IEEE Access Paper by Gunn, Allison and Abbott (GAA) proposed a new transient attack against the Kirchhoff-law-Johnson-noise (KLJN) secure key exchange system. The attack is valid, but it is easy to build a defense for the KLJN system. Here we note that GAA’s paper contains several invalid statements regarding security measures and the continuity of functions in classical physics. These deficiencies are clarified in our present paper, wherein we also emphasize that a new version of the KLJN system is immune against all existing attacks, including the one by GAA.
💡 Research Summary
The paper under review is a critical commentary on the recent IEEE Access article by Gunn, Allison, and Abbott (hereafter referred to as GAA) that introduced a “new transient attack” against the Kirchhoff‑law‑Johnson‑noise (KLJN) secure key exchange system. The authors of the commentary acknowledge that the attack described by GAA is theoretically sound: by capturing the brief voltage and current transients that occur at the very beginning of a KLJN exchange, an eavesdropper equipped with ultra‑fast oscilloscopes and low‑noise amplifiers could, in principle, infer which resistance (and thus which binary value) each party has selected. However, the commentary proceeds to demonstrate that the attack overlooks several essential defensive features that are already part of, or can be easily added to, a robust KLJN implementation.
First, the authors point out that a properly engineered KLJN system continuously monitors the instantaneous voltage and current at both ends and employs a high‑speed feedback loop to keep the two quantities balanced. Any sudden deviation from the expected equilibrium—such as the spike that GAA’s attack seeks to exploit—is immediately countered by either adjusting the switching state of the resistors or by temporarily boosting the noise power. This active control dramatically reduces the amplitude of the exploitable transient.
Second, the system incorporates wide‑band low‑pass filtering and statistical averaging stages. These components smooth out short‑duration fluctuations, effectively burying any residual transient beneath the thermal‑noise background. As a result, the signal‑to‑noise ratio (SNR) available to an eavesdropper drops to a level where reliable bit extraction becomes practically impossible, even with state‑of‑the‑art measurement equipment.
Third, the commentary highlights a newer variant of the KLJN protocol that combines dynamic resistor switching with simultaneous multi‑channel operation. In this configuration, any transient that might appear on one channel is counterbalanced by the complementary behavior of the other channels, yielding an overall voltage‑current waveform that is essentially flat. This “dual‑channel cancellation” technique eliminates the very signature that the GAA attack relies upon.
Beyond the technical countermeasures, the authors address a conceptual error in GAA’s paper concerning the continuity of physical functions. GAA argues that abrupt changes in system parameters (resistance, temperature, noise spectral density) would cause discontinuities in voltage, current, or temperature, thereby opening a security loophole. The commentary refutes this by invoking the fundamental principle of continuity in classical physics: when external parameters vary infinitesimally, the dependent physical quantities also vary infinitesimally, provided the system is described by well‑behaved differential equations. In a KLJN circuit, resistance values, temperatures, and noise spectra are all controlled continuously; any rapid change is filtered out by the same low‑pass and averaging stages mentioned earlier. Consequently, the alleged “discontinuities” simply do not arise in a realistic implementation.
The paper then proceeds to a comprehensive description of the modern KLJN architecture that is claimed to be immune to all known attacks, including the transient attack of GAA. Key elements of this architecture include:
-
Dynamic Resistor Switching – Resistances are not held constant for the entire bit‑exchange interval; they are switched according to a pseudo‑random schedule that is synchronized between the two legitimate parties. This prevents an eavesdropper from correlating a specific transient with a particular resistance value.
-
Multi‑Channel Parallelism – Two or more independent KLJN channels operate in parallel, with their noise sources and resistors coordinated such that any transient on one channel is statistically cancelled by the others.
-
Real‑Time Integrity Monitoring – Both ends continuously compute statistical metrics (e.g., variance, autocorrelation) of the measured voltage and current. Deviations beyond a pre‑defined threshold trigger an immediate abort of the key‑exchange session.
-
Adaptive Noise Power Control – The noise power spectral density can be dynamically increased during periods of heightened vulnerability (e.g., right after a switching event) to mask any residual transients.
-
Error‑Detection Coding – After the raw key bits are generated, a classical error‑detecting code (e.g., a cyclic redundancy check) is applied, ensuring that any tampering that subtly alters the statistical properties of the exchanged signals is detected before the key is used.
By integrating these mechanisms, the authors argue that the KLJN system regains its original claim of unconditional security based on classical physics, without reliance on computational hardness assumptions. The commentary concludes that while GAA’s transient attack is an intellectually interesting contribution, it does not constitute a practical threat to a correctly designed KLJN system, especially one that adopts the newer defensive enhancements described above. The paper thus serves both as a rebuttal to the specific criticisms raised by GAA and as a concise guide to the state‑of‑the‑art KLJN design principles that guarantee immunity against all currently known attack vectors.
Comments & Academic Discussion
Loading comments...
Leave a Comment