An Entropy Analysis based Intrusion Detection System for Controller Area Network in Vehicles
Dozens of Electronic Control Units (ECUs) can be found on modern vehicles for safety and driving assistance. These ECUs also introduce new security vulnerabilities as recent attacks have been reported by plugging the in-vehicle system or through wireless access. In this paper, we focus on the security of the Controller Area Network (CAN), which is a standard for communication among ECUs. CAN bus by design does not have sufficient security features to protect it from insider or outsider attacks. Intrusion detection system (IDS) is one of the most effective ways to enhance vehicle security on the insecure CAN bus protocol. We propose a new IDS based on the entropy of the identifier bits in CAN messages. The key observation is that all the known CAN message injection attacks need to alter the CAN ID bits and analyzing the entropy of such bits can be an effective way to detect those attacks. We collected real CAN messages from a vehicle (2016 Ford Fusion) and performed simulated message injection attacks. The experimental results showed that our entropy based IDS can successfully detect all the injection attacks without disrupting the communication on CAN.
💡 Research Summary
The paper addresses the well‑known security shortcomings of the Controller Area Network (CAN) used in modern vehicles, where the protocol provides no authentication or encryption and relies solely on a priority‑based bit‑arbitration mechanism. Because every CAN frame’s identifier (ID) determines its priority, any successful message‑injection attack must manipulate the ID bits. Leveraging this observation, the authors propose an intrusion detection system (IDS) that monitors the Shannon entropy of each bit in the 11‑bit CAN identifier.
First, a “golden template” of normal entropy is built by collecting CAN traffic from a 2016 Ford Fusion under diverse driving conditions. For each bit i, the probability p_i of observing a ‘1’ is estimated, and the binary entropy H(p_i)=‑p_i·log₂p_i‑(1‑p_i)·log₂(1‑p_i) is computed. Averaging 35 independent measurements yields a stable 11‑dimensional entropy vector. The detection threshold for each bit is set as Th = κ·(max(H_i) – min(H_i)), where κ is an empirically chosen multiplier (the authors use κ = 5).
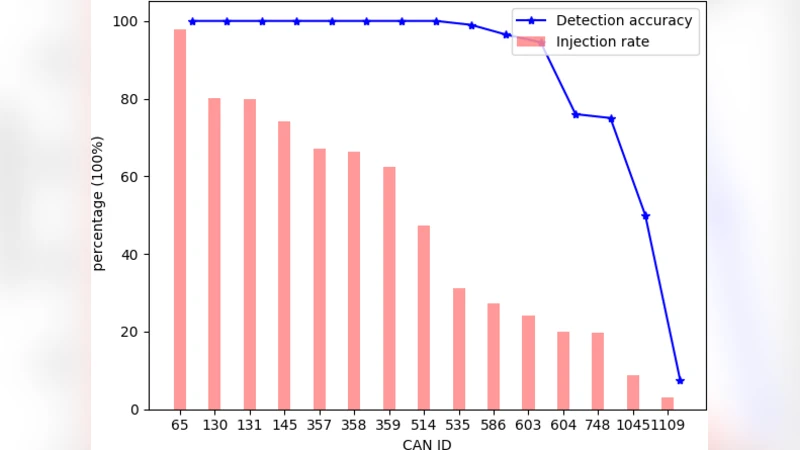
Two adversary models are defined. A “strong” attacker can transmit any ID, allowing high‑priority (dominant‑0) messages to dominate the bus, either by flooding, by using a single malicious ID, or by employing multiple IDs simultaneously. A “weak” attacker is constrained by ECU‑level filters and can only send messages with a fixed, pre‑assigned ID. Four concrete attack scenarios—strong flooding, strong single‑ID injection, strong multi‑ID injection, and weak fixed‑ID injection—are implemented using an Arduino UNO and a CAN Shield attached to the real vehicle bus.
Experimental results show that any of these attacks produce a measurable shift in the per‑bit entropy, often a sharp decrease because dominant‑0 bits become more frequent. All four scenarios exceed the predefined thresholds, yielding a 100 % detection rate with zero false positives. Moreover, because the IDS is passive—it does not modify CAN frames—it can be deployed alongside existing or future MAC‑based security extensions without compatibility issues.
The contributions are threefold: (1) a novel, non‑intrusive IDS based solely on ID‑bit entropy that covers all known CAN injection attacks; (2) a thorough validation on real vehicle data, demonstrating robustness across multiple attack models; and (3) an argument that entropy‑based detection can coexist with cryptographic solutions, offering a lightweight, real‑time complement to MAC‑based authentication.
Limitations include the focus on identifier bits only; attacks that manipulate payload data without changing IDs, or sophisticated timing attacks, may evade detection. The threshold parameter κ is chosen empirically and may need recalibration for different vehicle models or network loads. Future work is suggested to combine entropy monitoring with payload statistics and clock‑skew analysis, creating a multi‑layer IDS capable of detecting a broader class of threats while maintaining real‑time performance.
Comments & Academic Discussion
Loading comments...
Leave a Comment